Risk Assessment Overview & Heatmap
Learn how to effectively identify, mitigate, and manage risk in your organization.
The number of OAuth applications and Browser Extensions organizations manage constantly increases, making it more difficult to get an understanding of insights and trends in order to be able to take action.
SpinOne’s Risk Assessment Overview is designed to give you a breakdown of ALL applications and extensions and provide insightful recommendations on applications that may impose risk.
Overview
Head to the Risk Assessment Overview section from the left panel to uncover insights on all your applications.
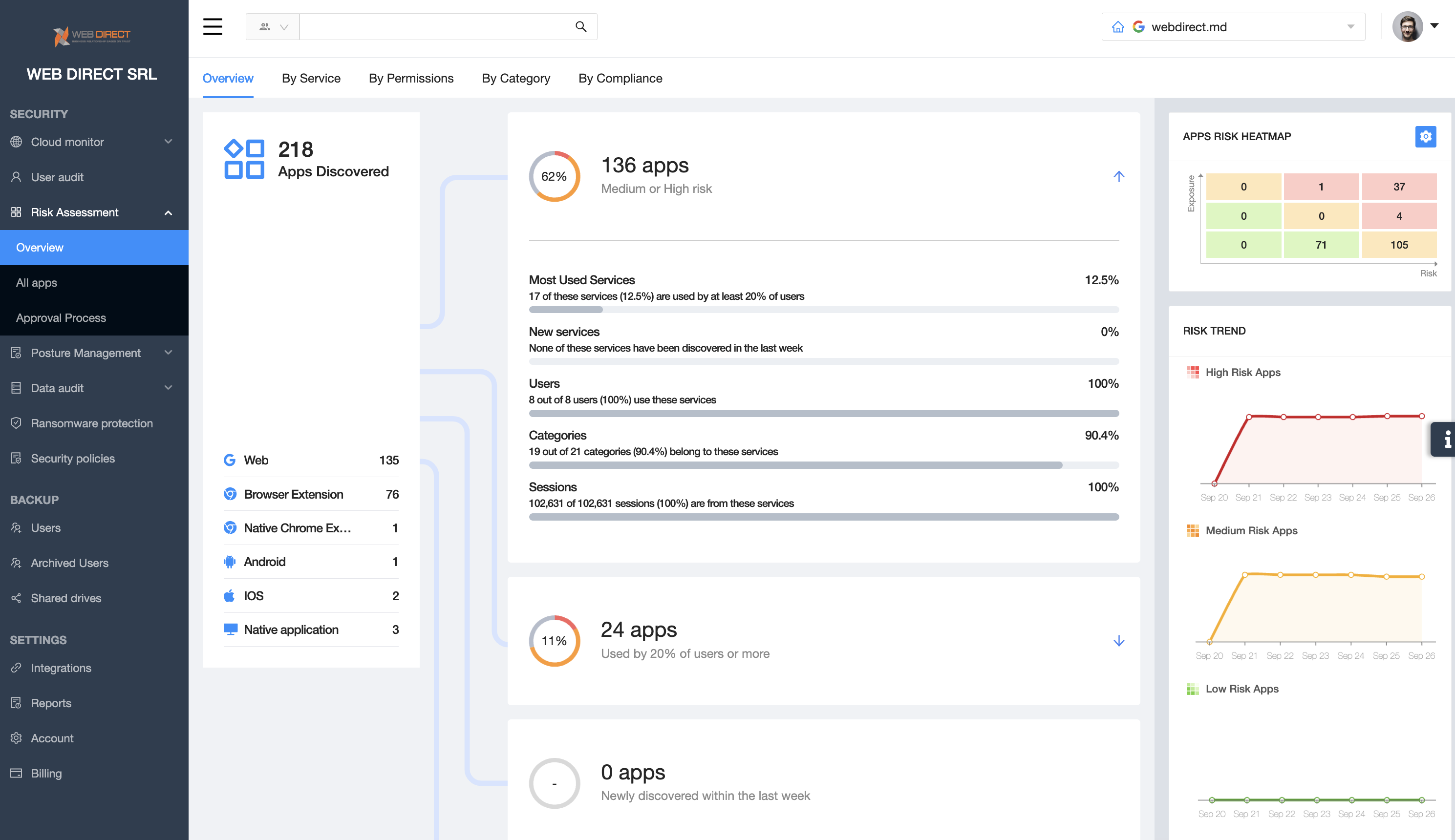
The Risk Assessment Overview is broken down into 5 tabs:
- Overview – general summary of all applications and their breakdown, with insights on how many applications are medium or high risk, and even how many were installed in the past week
- By Service (if applicable) – breakdown of the most impacted services within your SaaS application (Mail, Drive, …)
- By Permissions – visibility into scopes of permissions and insights into their risk
- By Category – common categories from installed applications and extensions
- By Compliance – executive insights on applications and compliances they adhere to
Dive deeper into each tab to uncover insights and identify which applications and extensions are risky for your organization.
Heatmap
The Apps Risk Heatmap on the right hand corner is a configurable risk matrix showing Risk and Exposure. The Risk Trend on the bottom indicates number of High, Medium or Low risky applications that meet the defined factors.
Click on the Settings icon on the top right to configure factors.
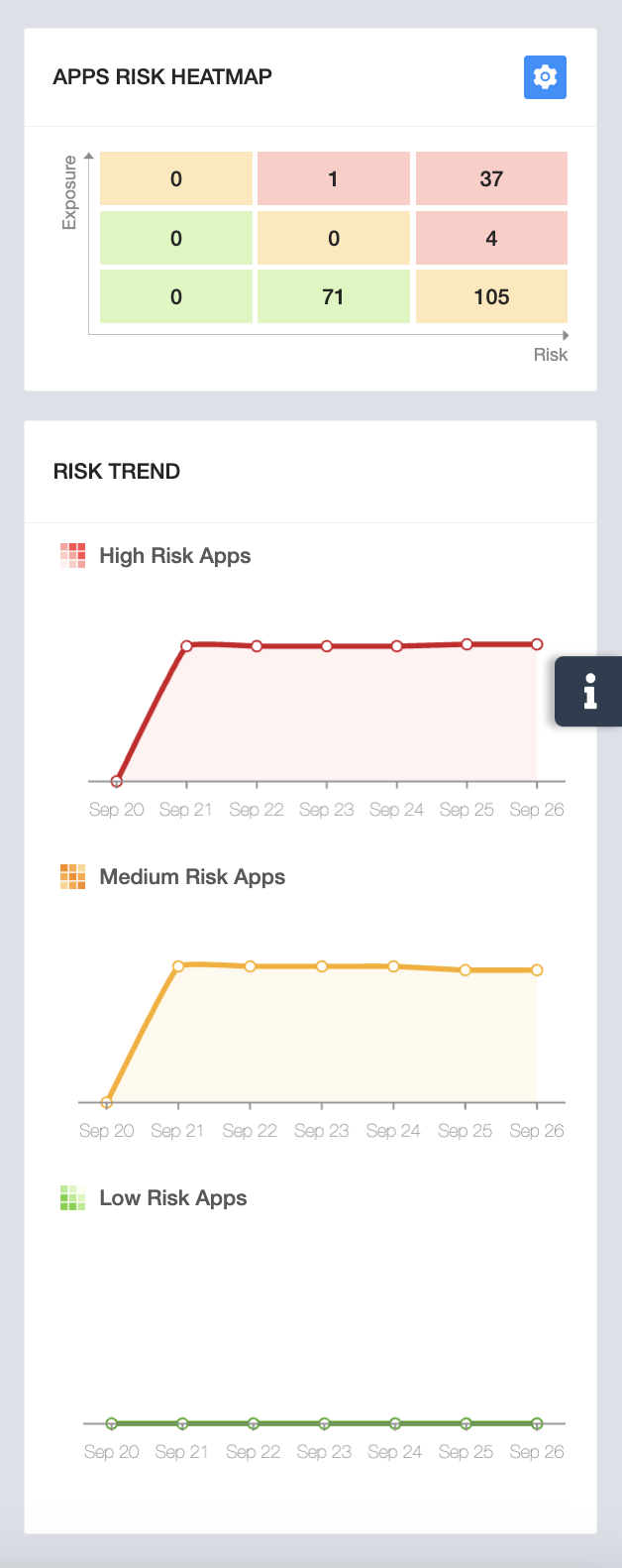
For Risk and for Exposure, you will be able to configure and define what is Medium or High risk. To add a new factor, click on the + icon, select a factor and specify the risk you’re looking for.
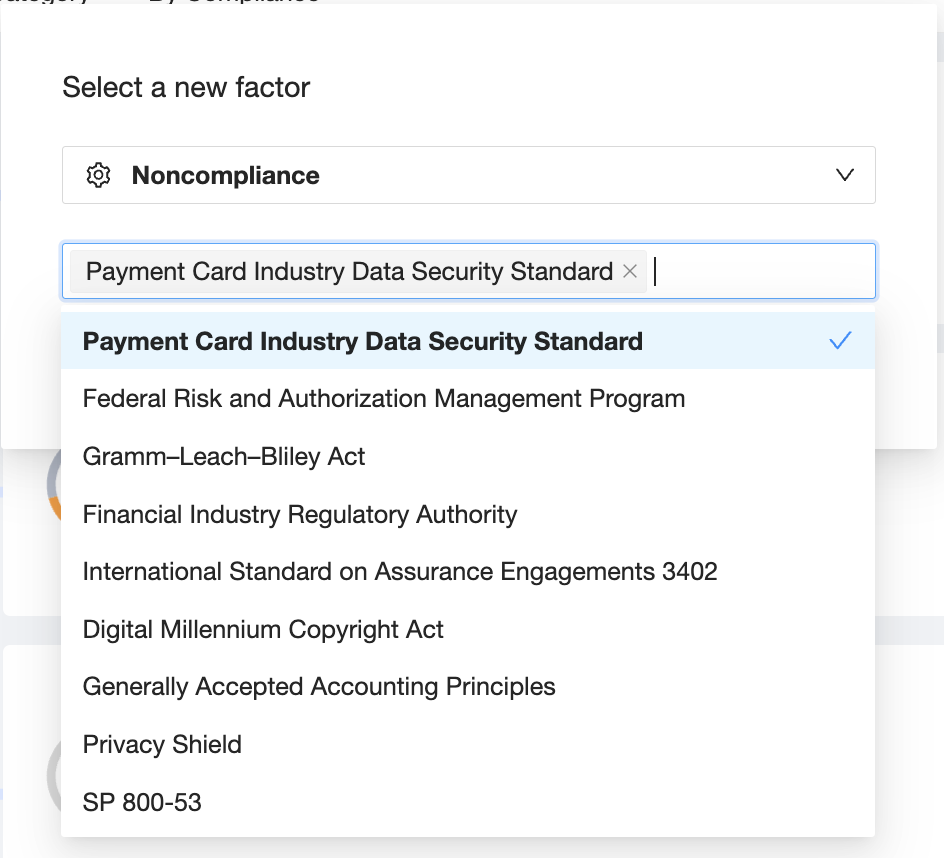
Once you’ve configured all factors, click Save in order to immediately see the results on the heatmap.
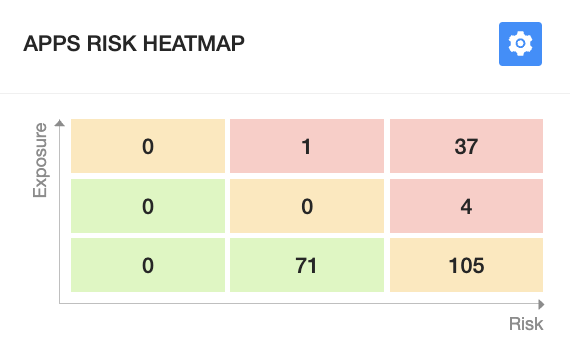
Click on each box to uncover applications that fall under that criteria.
Get more information on Google Workspace™ Backup Solutions