Minimize Ransomware Downtime
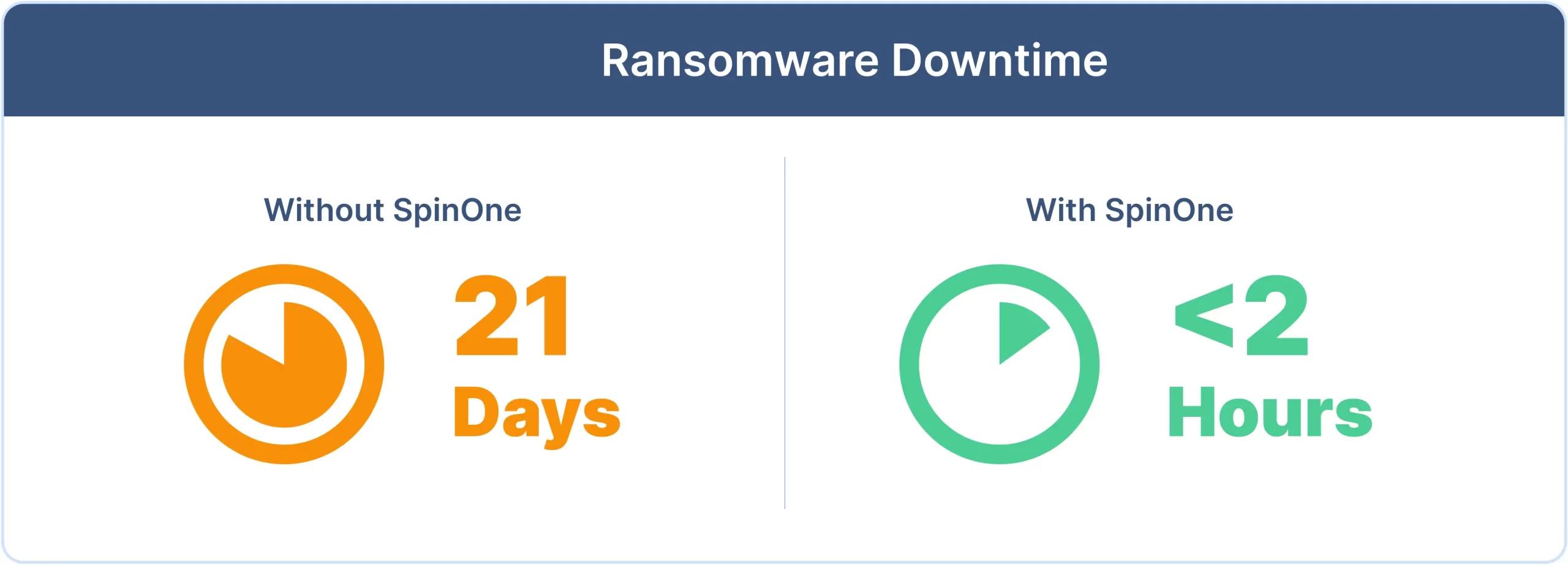
Drastically reduce costly ransomware downtime from weeks to <2 hours with SpinRDR

Ransomware Downtime Use Case
When it comes to SaaS ransomware attacks, it’s not if, it’s when. 73% of ransomware attacks are successful and come with costly downtime that can take weeks – even months – due to API and throttling limitations of SaaS providers such as Google Workspace™ and Microsoft 365.
In an evolving threat landscape, organizations need fast incident response SLAs to minimize RTO/downtime and avoid crippling their business continuity in case disaster strikes.
Impact of Ransomware Downtime
Calculate Your Potential Ransomware Downtime
Amount of data in your SaaS application:
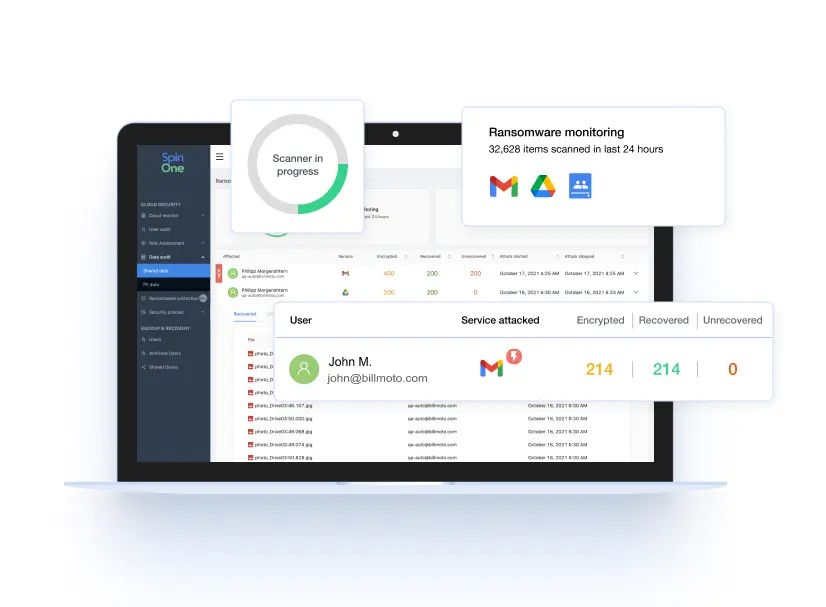
SpinOne provides a 2-hour incident response SLA from cloud ransomware attacks,
reducing downtime from an average of 21 days to 2 hours.
Reduce the Risk of Ransomware Downtime
SpinOne Ransomware Detection and Response (SpinRDR)
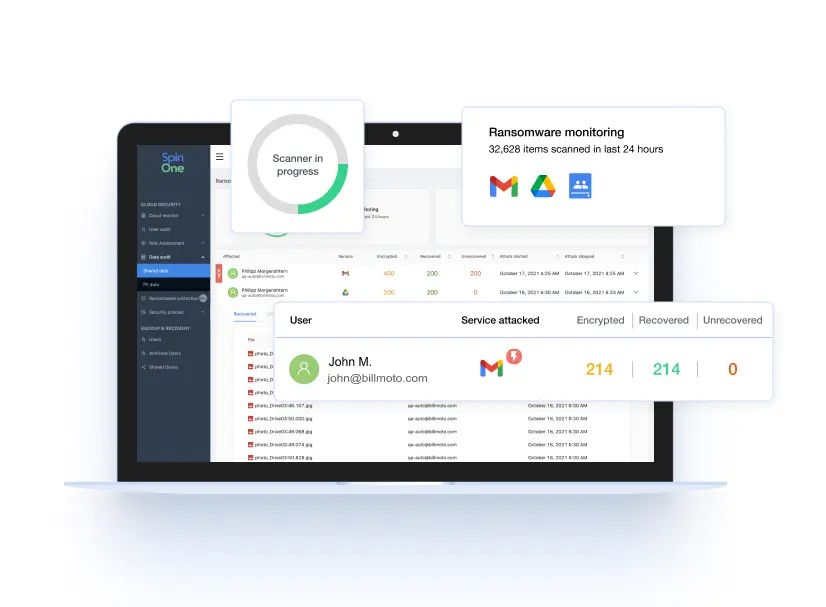
Defeat ransomware attacks on your mission-critical SaaS data with full visibility and fast, fully automated incident response from SpinRDR, a solution within the SpinOne platform. Reduce business downtime to less than 2 hours guaranteed, and reduce recovery costs by over 90%.
Ensure Fast Recovery

When recovering from a ransomware attack, time is money – your business can’t afford days of downtime. Reduce impact and recovery costs with the fastest SLA available on the market, slashing downtime from weeks to hours.
Why Businesses Choose SpinRDR
Related Resources
Frequently Asked Questions
How does ransomware cause downtime?
Cloud ransomware is a type of sophisticated crypto-malware targeting cloud environments that locks users out of their devices or prevents them from accessing SaaS data until a ransom is paid. Cloud ransomware attacks result in lengthy downtime due to the API and throttling limits of cloud vendors which slow SaaS data recovery.
How does ransomware spread in a SaaS environment?
Cloud ransomware is a type of malware that infiltrates cloud-based systems and encrypts data, rendering it inaccessible to users. The attackers then demand a ransom, typically in the form of cryptocurrencies like Bitcoin, to decrypt and release the affected data.
What are the common consequences of ransomware downtime?
Cloud ransomware attacks can result in downtime, data breaches, data loss, and potential theft of intellectual property. This can cause huge losses for businesses – in reputation, customers, revenue, and penalties.
How does SpinRDR handle ransomware removal and data recovery?
SpinRDR handles ransomware through the following automated capabilities:
- Monitors cloud SaaS environments for signs of ransomware 24/7/365
- Blocks the ransomware source
- Isolates assets affected by the ransomware attack
- Restores affected files to the latest backed up version
- Provides real-time notifications on incidents
- Provides granular SaaS security policy orchestration
Is minimizing the downtime the only advantage of SpinRDR?
No. Along with minimizing downtime, SpinRDR also helps reduce damages from a potential ransomware attack. It provides 24/7 AI-driven ransomware monitoring that proactively detects ransomware patterns and responds to them immediately in real time.
If SpinRDR is installed after a ransomware incident, can it assist in data recovery?
No, SpinRDR can only recover data that it has previously backed up.
Does SpinRDR offer protection from all existing ransomware variants?
We aim to provide robust protection against a wide range of ransomware variants. Ransomware continuously evolves, with new variants emerging regularly, each with unique characteristics and evasion techniques, so we constantly monitor these new threats.