3 Things to Consider Before a Career as a CISO
If there is one role that is pivotal to the success of today’s businesses navigating the stormy seas of cybersecurity, it is the Chief Information Security Office (CISO). However, the CISO role for enterprise organizations today is evolving from simply the “head of IT security.” It is much different than the role of the CISO in previous years. So what is the critical focus of today’s CISOs? For the brave souls entertaining the role of CISO, what are three areas today’s CISOs need to consider?
The Chief Information Security Office (CISO) of days gone by
To understand the challenges faced by today’s CISOs, we need to know how the role has evolved. Further, to fully understand the CISO transformation, we must understand how the overall technology landscape has changed. In the glory days of CISOs gone by, the role of the Chief Information Security Officer revolved around IT security.
Previously, the role of the CISO has been defined as the “head of IT security.” It may have included the CISO as the head “virus hunter,” the “boss of the firewall,” or another idea. But, true to those thoughts, they have often been responsible for the “nuts and bolts” of ensuring adequate security solutions were in place to keep the “bad guys out” and data safe.
When we think about how the landscape of technology looked a decade or more ago, businesses were still mainly operating on-premises data centers, with most employees working on-site on corporate devices behind the corporate firewall. When we think about the configuration of legacy data center architecture, challenges and risks to data were smaller, more pinpointed, and targeted on-premises clients and servers.
If the description of the Chief Information Security Officer we have just described is familiar to you, you may be surprised to know the role of CISO has evolved into a very different role in most organizations compared to what we have seen historically. Why the change?
A very different technology landscape and threat profile
The evolving CISO role mirrors the tremendous shift in the technology landscape we see today. Never before have there been more diverse, distributed, and disaggregated technologies driving business productivity, communication, and collaboration.
No longer are employees tied to the corporate office. Housing all business-critical data and services in on-premises data centers is no longer the standard approach to setting up infrastructure. The cloud evolution is fully underway. Businesses are diving head-first into cloud solutions and technologies.
One report found that:
- 94% of enterprise use cloud services
- 67% of enterprise infrastructure is now cloud-based
- 92% of businesses have a multi-cloud strategy
The cloud has changed everything, and this paradigm shift will not stop soon. Cloud services and technologies allow businesses to transform how they do business and empower their end-users. Cloud Software-as-a-Service environments enable organizations to move rapidly with innovative technologies to drive their business.
Note three technology trends that are currently evolving the role of the Chief Information Security Officer:
- A hybrid and distributed workforce
- Cloud technologies, including Software-as-a-Service (SaaS) environments
- Distributed edge locations
As we consider these three areas, we will see how these are shaping the role of the CISO.
A hybrid and distributed workforce
The transition to a hybrid workforce is a pivotal shift in the modern workforce. With the onset of the COVID-19 global pandemic, most companies worldwide shifted to a hybrid workforce, meaning employees have the flexibility to work from home at least part-time.
With the growth and explosion of cloud computing among businesses today, employees have the tools to work effectively from a remote office more than in any period in recent history.
Despite the flexibility it allows for workers, it adds immense complexity from a cybersecurity and risk point-of-view for the business. As a result, prospective CISOs must have a handle on “the big picture” of how their organization can secure a flexible, remote, and hybrid workforce.
What are the risks associated with storing data in the cloud? How do they successfully mitigate the risks associated with the hybrid workforce and not hinder the flexibility and agility of the business? Today’s CISOs must have a vision and strategy for the business.
Cloud technologies, including Software-as-a-Service (SaaS) environments
Powerful tools in cloud SaaS environments like Google Workspace™ and Microsoft 365 allow end-users to collaborate, communicate and have business-productivity tools needed to thrive in the hybrid era. However, with the ease of data sharing in the cloud and third-party apps easily integrated into the environment, the dangers of Shadow IT and data leaks are looming over businesses.
In addition, to cloud SaaS environments, organizations are heavily investing in cloud Infrastructure-as-a-Service. With a few clicks, the ability to provision new infrastructure without the tedious procurement, installation, and configuration of infrastructure on-premises is a game changer. Businesses are now transitioning to a multi-cloud approach, using an ala carte of services from multiple cloud vendors.
Today’s CISOs must understand the risks to the business of cloud Shadow IT, cloud misconfigurations, and the high likelihood of data leakage or inappropriate data sharing without the right tools in place. In addition, they need to know how to increase their organization’s “cloud cybersecurity posture” by hardening access and cloud configurations.
Distributed edge locations
Another exciting evolution in enterprise IT is the distributed edge environment. Gone are the days when businesses had a simple enterprise data center protected by an edge firewall with all the clients and servers behind the firewall. Instead, with new Internet of Things (IoT) technologies using artificial intelligence and machine learning, devices are getting placed closer to where the data is generated.
With the increasing use of the cloud and 5G availability, enterprises are using smart appliances, security systems, IoT sensors, and many other devices. Unfortunately, this trend is leading to significant security challenges around IoT security.
The new CISO must understand how to harness the technologies of the distributed edge and the risks to the business from IoT devices and ML/AI processes to secure these appropriately.
The changing scope and focus of CISOs
It is evident with the radical changes in the technology space across enterprise organizations, the scope and focus of today’s CISOs have dramatically changed. No longer are CISOs simply the “head of IT security.” Instead, their role has evolved to include more business-focused concerns. Additionally, with the sheer “width and breadth” of today’s technologies, including the cloud, it is no longer feasible or reasonable to expect to prevent all security breaches.
Therefore, CISOs are now tasked with understanding how the business can withstand a cyber attack and still maintain acceptable SLAs for the company. Data protection, resilience, availability, and compliance are vital to this aim. As a result, the CISO role has grown much broader, including a more business-focused strategy to understand and report risks effectively to the C-suite for strategic technology planning.
CISOs must leverage next-generation tools for securing the cloud
For CISOs to meet the modern challenge of SaaS security and face Shadow IT risks head-on, it requires the right tools and technologies to monitor, control, and govern cloud Saas environments. SpinOne provides businesses with the tools to protect their organization from current and emerging SaaS security risks.
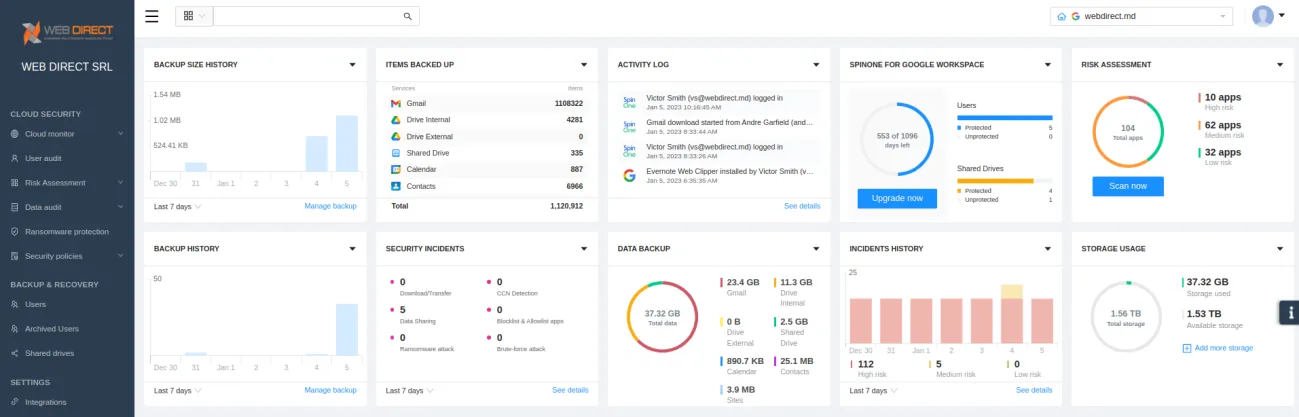
Spin.AI provides:
- Automated risk assessments of SaaS applications
- Proactive ransomware protection and remediation
- Monitoring of user activities and behaviors
- Effective tools to prevent Shadow IT activities
- Visibility and control over data sharing in cloud SaaS environments
- Technologies to introduce effective governance for SaaS apps to prevent unauthorized access
Request a Demo and see how you can help your organization secure your cloud environment effectively.