6 Best Practices for Microsoft 365 Security Monitoring for Admins
The purpose of this article is to outline the best practices for Microsoft 365 security monitoring. This means it mainly focuses on detecting cyber threats. It also provides clear guidelines for Admins on how to supervise the cloud environment. For threat prevention and response, read our guide on Microsoft 365 security best practices.
Microsoft 365 Security Risks
Overall, Microsoft 365 security issues are scarce. There are, however, several inalienable weaknesses. Mostly they are associated with human error or malicious intent.
Thereby, cybersecurity experts identify several risks associated with Microsoft 365:
- Criminals get hold of a user’s account to steal or corrupt data or implant malware.
- Users set up insecure sharing permissions that enable unauthorized people to access information.
- Ransomware can infect your Microsoft 365 environment and encrypt your files.
- Your users or administrators can initiate man-in-the-middle attacks.
To efficiently withstand these threats and enhance Microsoft 365 security, you need to constantly monitor several important indicators:
- Access
- Sharing permission
- Privilege escalation
- Abnormal data behavior
- Microsoft 365 Policy changes
- Exchange monitoring
In the next section of the article, we’ll take a look at Microsoft security best practices and discuss how to monitor each indicator more efficiently. In addition to that, we’ll take a look at third-party tools that can help you automate your operations.
Related Link: 6 Dangerous Microsoft 365 Security Concerns for Business
The Best Practices for Microsoft 365 Security Monitoring
These are the general Microsoft 365 security recommendations for Administrators.
1. Monitor Access
Cybercriminals would attempt to steal the credentials of your users and gain unauthorized access to your information. That’s why you need to look for abnormalities, such as, for example, access from unusual locations or devices.
Disabling external sharing is one of the security monitoring best practices for O365. However, not all companies have the opportunity to do it. That’s why we highly recommend limiting the number of departments that have permissions for external sharing.
2. Sharing permission
In 2020, 30% of admins provided access to sensitive data solely upon coworkers’ requests. The users often don’t follow the existing sharing policies (if there are any).
You need to check for the following instances:
- Public sharing or access by link
- Inside sharing with unauthorized employees
- Granting editing permissions
You can also set up data loss prevention policies to have better control over your files.
3. Privilege escalation
Privilege escalation is used in both man-in-the-middle and outside attacks. Admin roles will be of particular interest in both cases. You need to monitor the abnormal changes in user access to different types of data and their permissions.
4. Abnormal data behavior
Any bulk items deletion or editing might signify an attack. In most cases, it will be ransomware that infects your Microsoft 365 environment. Other instances include mass deletion or mass data downloads. The earlier you spot such events, the sooner you will be able to stop the attack and start recovery.
5. Changes in Microsoft 365 policies and Exchange Online filtering policies
This is a regular practice for Microsoft security monitoring. Policy changes are a more subtle way to initiate a cyberattack targeting OneDrive or Exchange Online. For example, the criminal removes the outside sharing restriction. In this case, they can then easily share large sets of data without being spotted.
6. Monitor Exchange security
Microsoft Exchange is the gateway to all sorts of cyber threats. Phishing attacks are one of the most popular ones. As an Administrator, you need Microsoft 365 email security settings that will help you protect your environment from attack attempts.
Microsoft 365 Security Tools
Microsoft provides a range of solutions that will help you facilitate and automate your monitoring process. Apart from these, there are third-party tools that help control Microsoft security. Let’s take a closer look at each of them.
Native M365 security assessment tools
- Microsoft Sentinel is a Security Information and Event Management system that provides an opportunity for Microsoft 365 monitoring of multiple adverse events on a single pane of glass. You can configure alerts for incidents, abnormalities, and suspicious activity.
- Microsoft Defender (former Advanced Threat Protection) is the tool that defends Microsoft Services from multiple cyber threats. Its two most renowned features are the detection of insecure attachments and links in emails and powerful anti-phishing protection.
Ransomware protection with SpinRDR
Powered by AI, SpinRDR is a ransomware protection tool for monitoring Microsoft 365 business security. It utilizes a unique algorithm to detect ransomware by monitoring abnormal behavior in data. Once it identifies the cyberattack and its source, it blocks the access of the ransomware to your Microsoft 365 environment. Next, SpinRDR recovers your data from its backup.
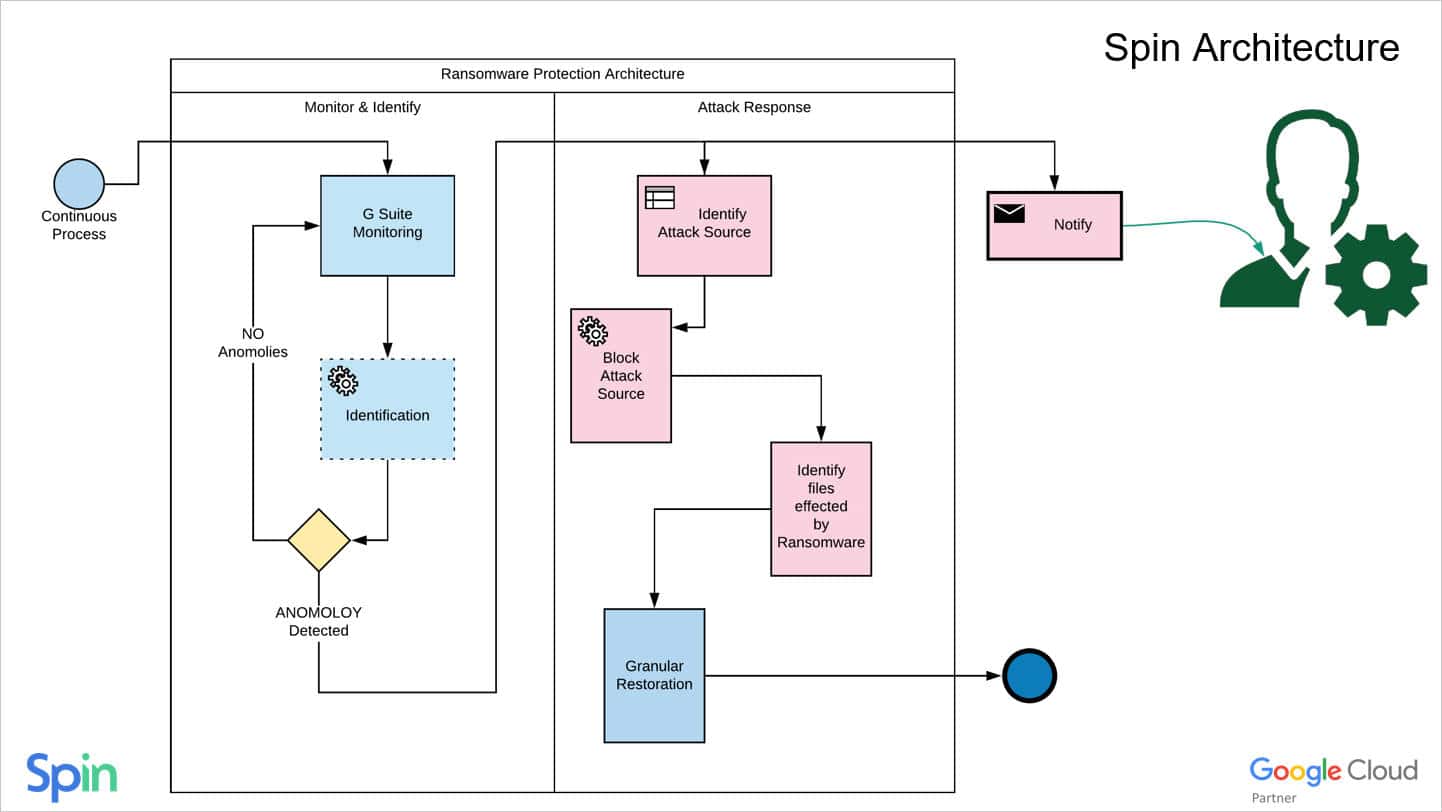
The process is fully automated. That’s why our tool doesn’t require the intervention of a human neither for monitoring nor for incident response.