What is SSPM? Importance and Key Functions of SSPM Tools
Article Summary:
SaaS Security Posture Management (SSPM) is essential for protecting cloud-based applications from security breaches, misconfigurations, and compliance risks. This guide explains why SSPM is critical, how it works, and the key features to look for in a solution.
SSPM Key Takeaways:
- What is SSPM? A security tool that continuously monitors and protects SaaS applications by detecting misconfigurations, managing permissions, and ensuring compliance.
- Why it matters: With the rise of SaaS apps, businesses face increased security risks from human error, misconfigurations, and unauthorized third-party access.
- Core functions: SSPM solutions provide real-time monitoring, automate compliance checks, and detect suspicious user behavior to prevent data breaches.
- Common threats addressed: SSPM neutralizes risks from shadow IT, third-party vulnerabilities, and over-permissioned accounts.
- Best practices for implementation: Establish security baselines, conduct continuous risk assessments, and educate users to minimize human error.
Remember when software was something you installed once and rarely thought about again? Those days are long gone.
Security today is an ongoing battle with SaaS applications running everything from emails to payroll. Unfortunately, most companies assume their cloud-based apps are automatically secure, but that’s far from the truth.
SaaS environments constantly change. New users join and permissions shift. Without oversight, a simple misconfiguration can lead to a significant security breach.
Therefore, you need SSPM (SaaS Security Posture Management) to monitor for risks and keep your security posture strong.
What is a SaaS Security Posture?
SaaS security posture identifies the overall condition of the security of a company’s SaaS applications.
This includes inter alia:
- the state of cloud data security
- the authentication methods
- the authorization process
- access to data
- the use of data.
A company’s SaaS security posture is a constantly evolving and complex issue, as new threats and vulnerabilities are discovered on a regular basis.
A proper SaaS security posture begins with researching the specific security risks associated with the SaaS apps in use. Organizations need to be aware of the potential threats that can put their data at risk, and take steps to mitigate those risks.
The use of apps implies storing corporate data in the cloud beyond the organization’s control. Many cybersecurity experts consider it to be the one of key dangers related to apps. Correspondingly, apps become a popular target for cybercriminals seeking to steal and take advantage of the data. Hence, we see constant searches (successful on way too many occasions) for the app’s vulnerabilities.
Experts recommend that organizations take the following steps in order to secure their data in third-party apps:
- Confirm that apps use up-to-date security technologies, including authentication, authorization, and data encryption.
- Reassure that the cloud provider is reputable and has a good security track record.
- Routinely monitor the security of the applications and the data.
- Set up alerts of any security incidents.
- Systematically audit the security of the applications and the data.
- Reduce the pressure on IT team and tackle the skill or talent gap.
All these tasks can be carried out either by a team of humans or software. The software that performs these tasks is usually called SSPM.
Let’s break down what SSPM solutions are and how they keep your cloud apps secure.
Importance of SSPM Tools
If you’ve ever left your phone unlocked in a crowded place, perhaps you can relate to that sinking feeling that anyone could access your messages or, worse, your bank account.
Now, consider that on a company-wide scale. But instead of your texts, it’s customer data and sensitive business operations hanging wide open.
That’s exactly what happens when SaaS security is ignored. Companies use dozens, sometimes hundreds, of SaaS applications, and each one is a potential entry point for cyber threats.
A single misconfigured setting – think an admin accidentally leaving sensitive files open to everyone – can lead to data leaks. In fact, recent data from Infosecurity Magazine reveals that around 31% of global organizations have experienced data breaches in their SaaS apps.
SSPM solutions prevent these disasters by continuously monitoring your SaaS environment and preventing threats.
Key Functions of SSPM Security Tools
A solid SSPM solution actively scans and tightens security where it matters. This way, your data stays exactly where it belongs. Here’s how it ensures that.
Monitoring and Managing Security Posture
SSPM solutions consistently track who has access to your data and where vulnerabilities exist. Besides alerting you when something looks off, they proactively manage risks to keep data breaches at bay.
It might do this by detecting unusual logins and flagging excessive permissions.
Identifying Compliance Risks and Vulnerabilities
Have you ever left the house convinced you forgot to turn off the stove? That uneasy feeling is exactly what businesses face with compliance, except instead of a kitchen fire, it’s data breaches and regulatory fines on the line.
With companies juggling GDPR, SOC 2, HIPAA, and a laundry list of other regulations, even a small misstep, like an unencrypted file, can spell disaster.
SSPM automates compliance checks so your SaaS environment always meets security standards. It scans for vulnerabilities and even provides insights on how to fix them.
This keeps you from panicking every time an audit rolls around.
Safeguarding Against Misconfigurations
Most data breaches don’t happen because of elite hackers. They occur because someone, somewhere, clicked the wrong button.
A Verizon report, in fact, confirms that 74% of data breaches involve human error and clicking a phishing link is the most common one.
SSPM scans your SaaS applications for misconfigurations that could expose sensitive data. Did an employee accidentally make an internal document accessible to the entire internet? SSPM catches it. Is an app allowing third-party access it shouldn’t? SSPM locks it down.
Common Threats Addressed By SSPM
Sometimes, the biggest security disasters start with something as small as a forgotten permission or a setting that should have been locked down but wasn’t.
Without a system in place to fix these weaknesses, businesses are practically handing cybercriminals a free pass.
SSPM solutions seal off weak points to keep systems from breaches. Below, we discuss the biggest threats SSPM neutralizes before they become your next security nightmare.
Understanding Shadow IT
Say you run a company, and one day, you find out your employees have been using an entire set of unauthorized apps to store files, share data, and maybe manage customer records without IT’s knowledge. That’s Shadow IT.
IBM explains that it’s “any software, hardware, or information technology (IT) resource used on an enterprise network without the IT department’s approval.”
Employees often use unapproved SaaS applications for work because they find them more convenient than company-sanctioned tools. The problem is that these apps aren’t secured, serving cybercriminals a golden opportunity.
Sensitive data could be floating in unsecured cloud storage or sitting in an abandoned account that hackers can easily take over.
SSPM shines a light on Shadow IT. It detects unapproved applications and gives IT teams the control they need. Because if you don’t know what tools your team is using, you have no idea where your data is going.
Managing Third-Party Risks
Every SaaS tool your company integrates comes with its own security vulnerabilities. Some might have weak encryption; others may have excessive permissions.
If just one of these third-party vendors gets breached, your data could be exposed without a single attack on your own systems. In fact, data shows that 61% of cyberattacks utilize third-party apps for this purpose.
Thankfully, SSPM monitors and manages third-party risks by identifying which apps and browser extensions have access to critical data. Following this, it flags potential threats, ensuring only the safest, most secure applications are allowed in, while risky ones get locked out.
SSPM vs. CSPM and CASB
Numerous security tools promise to protect your cloud environment, but not all do the same job. Below, we highlight the key differences and the best use cases of each one.
Definitions and Key Differences
SSPM (SaaS Security Posture Management)
SSPM continuously secures cloud-based applications (like Google Workspace™, Salesforce, or Slack). Its job is to detect:
- Misconfigurations
- Over-permissioned users
- Compliance risks.
It ensures that SaaS apps remain protected to avoid accidental data exposure and security gaps that could potentially be exploited.
Unlike CSPM or CASB, SSPM focuses exclusively on securing SaaS applications. It manages risks that arise within the apps themselves rather than the broader cloud infrastructure.
CSPM (Cloud Security Posture Management)
CSPM secures cloud infrastructure (think Azure or Google Cloud). Microsoft highlights that CSPM tools perform the following:
- Compliance monitoring
- Incidental responses
- Remediation recommendation
- DevOps integration to hybrid and multi-cloud environments
Overall, CSPM protects the underlying cloud environment, not the SaaS applications running on top of it. If your SaaS security problem is inside a specific app, CSPM won’t help much. That’s SSPM’s job.
CASB (Cloud Access Security Broker)
CASB controls and monitors how users interact with cloud services to prevent data leaks by blocking unauthorized access. CASB is especially useful for detecting shadow IT.
Remember, it focuses on who is accessing cloud apps and how, but it doesn’t manage misconfigurations or internal security settings inside SaaS apps. Again, that’s where SSPM takes over.
When to Use Each Solution
SSPM
If your business relies heavily on SaaS applications, SSPM might suit you best. It handles misconfigurations, over-permissioned users, data exposure, and compliance risks within SaaS apps.
Best for: Preventing SaaS-related security risks and reducing human errors.
CSPM
If your business runs virtual machines, cloud storage, and databases in public cloud environments, you need CSPM to scan for misconfigurations and prevent security gaps in cloud-native setups.
Best for: Securing cloud workloads and avoiding costly cloud misconfigurations that lead to breaches.
CASB
CASB is essential to:
- Monitor and regulate user access to cloud applications
- Detect shadow IT
- Prevent data leaks
- Enforce security policies for cloud-based activities
If you need to ensure only the right people access the right apps under the right conditions, CASB is the tool for the job.
Best for: Controlling access to cloud apps, preventing unauthorized data sharing, and stopping shadow IT.
SpinSPM As a Leading SSPM Vendor
A solid SSPM solution makes security management effortless, and SpinSPM does precisely that. Designed for businesses that refuse to take SaaS security lightly, SpinSPM goes beyond basic monitoring. It offers automated risk mitigation and seamless integration with tools you already use.
SpinSPM Overview
Most security teams don’t even know a problem is creeping in until it’s too late.
Fortunately, SpinSPM resolves the issue. Instead of drowning you in alerts and vague security warnings, it gives crystal-clear visibility into your SaaS ecosystem and automates threat response before things get out of control.
It also offers AI-powered risk assessments, a massive database of 400,000+ apps and browser extensions, and a level of automation that saves security teams time instead of adding to their workload.
No wonder Google recommends it, and Forrester calls it a Strong Performer!
Must-Have Features in Modern SSPM Tools
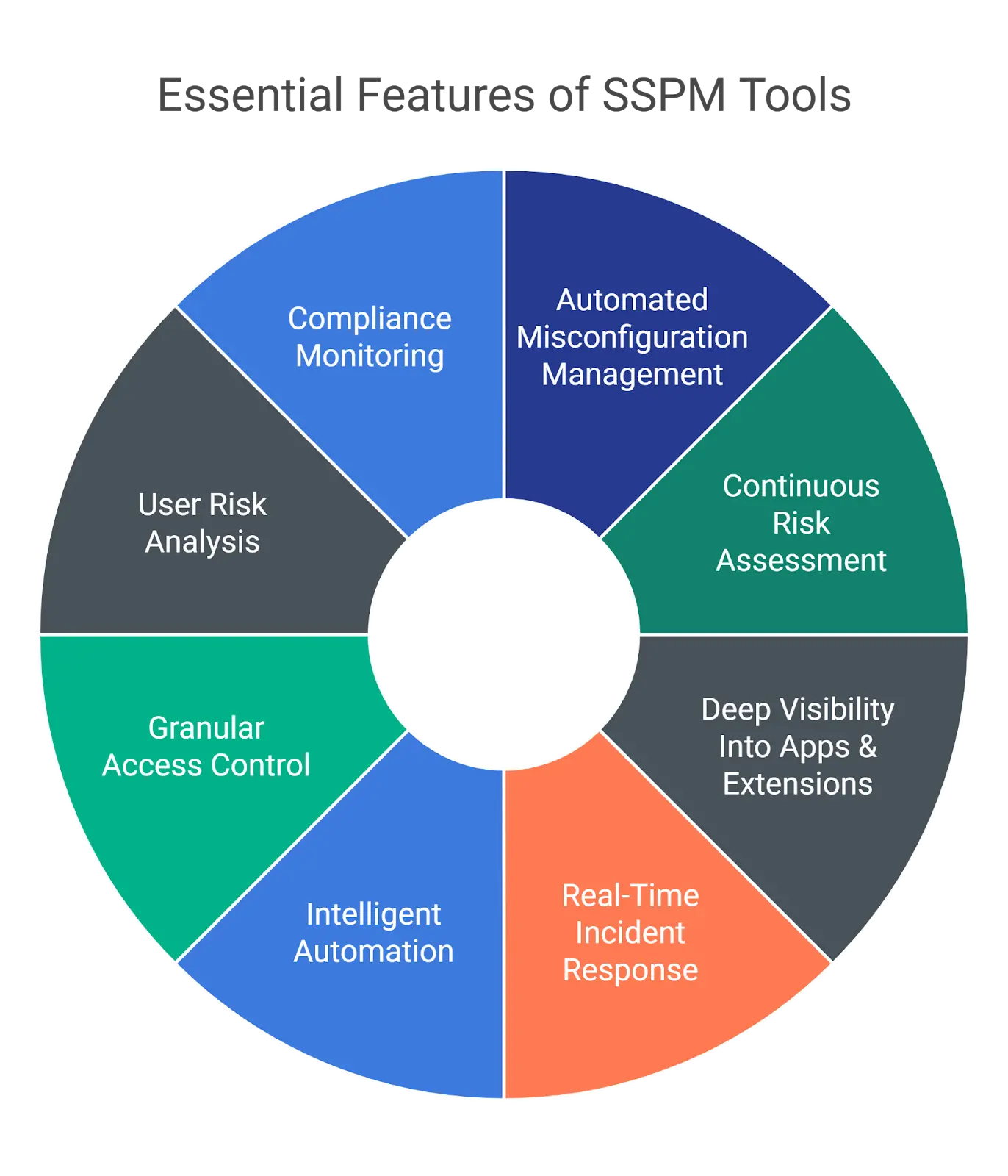
- Automated Misconfiguration Management. A single misconfiguration can open the floodgates to data breaches. Therefore, your SSPM should be able to detect, alert, and fix security drifts automatically.
- Continuous Risk Assessment. Security isn’t a one-and-done task. Your SSPM should continuously assess applications to prevent threats from slipping through the cracks.
- Deep Visibility Into Apps & Extensions. You can’t secure what you can’t see! A top-tier SSPM gives you full visibility into all SaaS apps and browser extensions. It also tells you who has access to them.
- Real-Time Incident Response. Besides informing you about threats, a good SSPM helps you respond instantly through detailed alerts and advanced reporting.
- Intelligent Automation. SSPM should work for you, not the other way around. Ideally, look for tools that automate security policies, enforce access controls, and respond to threats without manual intervention.
- Granular Access Control. Block shady apps before they become a problem. The best SSPM tools let you allowlist and blocklist apps and extensions at scale.
- User Risk Analysis. Not all security risks come from external threats. A strong SSPM solution detects suspicious user behavior and flag potential insider risks before they escalate.
- Compliance Monitoring. Your SSPM should help you track compliance with frameworks like CIS, ISO 27001, SOC 2, and NIS2.
Fortunately, SpinSPM checks all these boxes. It combines real-time security insights and deep risk analysis to keep your SaaS environment secure from all angles.
Factors to Consider While Choosing an SSPM Solution
Use this as a buying checklist for SSPM. It will help you to vet the solutions represented on the market.
Centralized platform
Define the functionality that meets the needs of your business. Search for solutions that provide all the necessary features rather than buying several siloed tools.
The Breadth of Integrations
Outline the tools that your business uses. Search for an SSPM that integrates with as many of them as possible.
Monitoring & Incident Reporting
Find out if there’s 24/7 monitoring available and how the tool reports the new risky applications, e.g., via email.
The Number of Applications
Ask the sellers how many applications their SSPM detects. Another good question would be about the frequency of their app database updates.
Application Assessment Criteria and Scoring
Often overlooked by the buying teams, this functionality is one of the most critical. Some SSPMs use only 2 or 3 criteria to evaluate risks and use a simple scoring system (e.g., High-Medium-Low).
Access Revoke Functionality
The ability to immediately revoke access of an application with a high-risk score can not only save much time for your admins but also possibly prevent a cyber incident.
Blocklisting & Allowlisting
Creating lists of ‘desired’ and ‘unwelcomed’ applications can save you much time in the long run. It also enables you to implement an initial zero-trust approach when all apps are blocked. In this case, you have no Shadow IT and get a significant leverage when it comes to cooperation with departments on app acquisition.
Security Policies
Confirm that an SSPM enables you to configure a security policy that doesn’t allow users to set up applications based on certain criteria (e.g., risk score or scope of permissions).
Employee Requests System
This functionality streamlines the request process when employees want to acquire a new application and want to send an official request to the IT department.
Company-based Customization Opportunities
SaaS Security Posture varies from company to company based on a number of factors. The possibility to customize the platform functionality will allow you to build the system that will defend your data most effectively.
Support
Check if the company provides round-the-clock support. It’s essential to be able to talk to the specialist if you have any questions pertaining to the app.
Best Practices for Implementing SSPM
Without the right strategy, even the best SSPM solution can become an overpriced notification machine, bombarding you with alerts no one acts on.
A well-implemented SSPM is one that always works in the background, protecting your SaaS environment without slowing things down. This might mean aligning security policies with business goals and avoiding the classic “set it and forget it” trap.
Establishing a Security Baseline
You can’t protect what you don’t understand. So, before you even think about securing your SaaS environment, you need to define what “secure” looks like for your organization.
This implies setting a security baseline. It’s a clear, measurable standard for what’s acceptable and what’s a red flag.
What kind of apps are allowed? Who gets admin privileges? What level of security is non-negotiable?
Setting these rules from day one will allow you to prevent security chaos before it even starts.
Continuous Monitoring and Assessments
Setting up security once and never checking in again is like locking your front door but leaving the windows wide open. For example, let’s say a marketing team installs a file-sharing app without IT’s approval. It seems harmless until it requests full access to sensitive company data.
Without continuous monitoring, this “small” oversight could become a massive data breach. But with real-time assessments in place, your security team catches the risk immediately, blocking the app before damage takes place.
An effective SSPM solution actively scans for new risks and reassesses security settings as your business scales.
User Education and Awareness
As mentioned earlier, the biggest security risk isn’t always a hacker; it’s human error. All the best security tools in the world mean nothing if employees keep clicking on phishing links or approving risky app permissions.
The key is to make security training accessible to your employees. Use real-world examples and interactive simulations to keep teams sharp. Because, at the end of the day, an informed workforce is your first line of security.