Cloud Application Security Risk Assessment Checklist
Article Summary:
The article presents a comprehensive checklist to help businesses evaluate the security risks and operational risk causes associated with cloud applications, especially those sourced from platforms like Google Marketplace and Chrome Web Store. It highlights common web application security concerns and outlines a structured approach to risk assessment across business operation, security, and compliance categories.
Risk Assessment Key Insights:
- Shadow IT, user habits, and limited Google Workspace™ controls significantly increase third party risk from unauthorized apps.
- Business risk criteria and potential threats include user base, app ratings, developer credibility, update frequency, and app category.
- Security evaluation should cover the risk matrix for SSL status, domain history, known vulnerabilities, permission scope, encryption, and breach history.
- Compliance factors such as privacy policies, audit reports, and developer jurisdiction (favoring US/EU) are critical for regulatory alignment.
- The checklist in this article is modeled after SpinOne’s security algorithm, offering a methodical way to perform security audits and mitigate risks.
When choosing an application for your business, you’ll have to estimate its risks and consider its application security risk rating. All tools available on official platforms like Google Marketplace or Chrome Web Store seem secure. In reality, however, some of them may carry potential risks and some have an identified risk that needs to be evaluated before use.
Based on our own experience, we created a Cloud Application Security Risk Assessment Checklist. It will help you sift through multiple tools on the market and choose the best for your business.
Things you’ll learn from this risk management checklist:
- Why is it important to select application software carefully?
- How to conduct a risk assessment for cloud tools offered on Google Marketplace?
- What criteria should you look at in the first place?
- How to critically evaluate the functions and advantages of web applications from a security perspective?
- What are the best practices for cloud software management?
- What’s the easiest way to conduct a web application security audit?
Why should you trust this checklist?
Spin Technologies experts have been studying web application security best practices for several years now. We created a complex algorithm that detects cloud apps in your Google Workspace™ and estimates their risks for your business. This algorithm is part of our product SpinOne, one of the best-selling web security audit tools.
Web Application Security Concerns
There are four main concerns about apps available on official platforms like Google Marketplace or Chrome Web Store. In this section, we’ll discuss them in detail.
1. Shadow IT
Shadow IT refers to any software or hardware tool that the employees use without IT Department’s authorization and present potential hazards. Because IT specialists don’t know about these applications, it’s hard to detect them. The lack of professional control creates a security gap that might be an entry point to cybercriminals.
Unfortunately, the number of shadow IT apps is growing. Here are some reasons:
- Employees want to be more efficient in their work and look for tools to help them
- Apps from Google and Chrome Marketplaces are easy to download and install (unlike more complex software tools)
- These apps are relatively cheap so they’re covered by a department’s budget or the budget of an employee
- Google Workspace™ functionality for app control and monitoring with control measures is limited
- Lack of awareness on the cybersecurity risks pertaining to web applications
There are tools that enable you to manage cloud applications. For example, SpinOne analyzes your Google Workspace™ on a regular basis (usually once per day). It then provides a list of apps that your employees use.
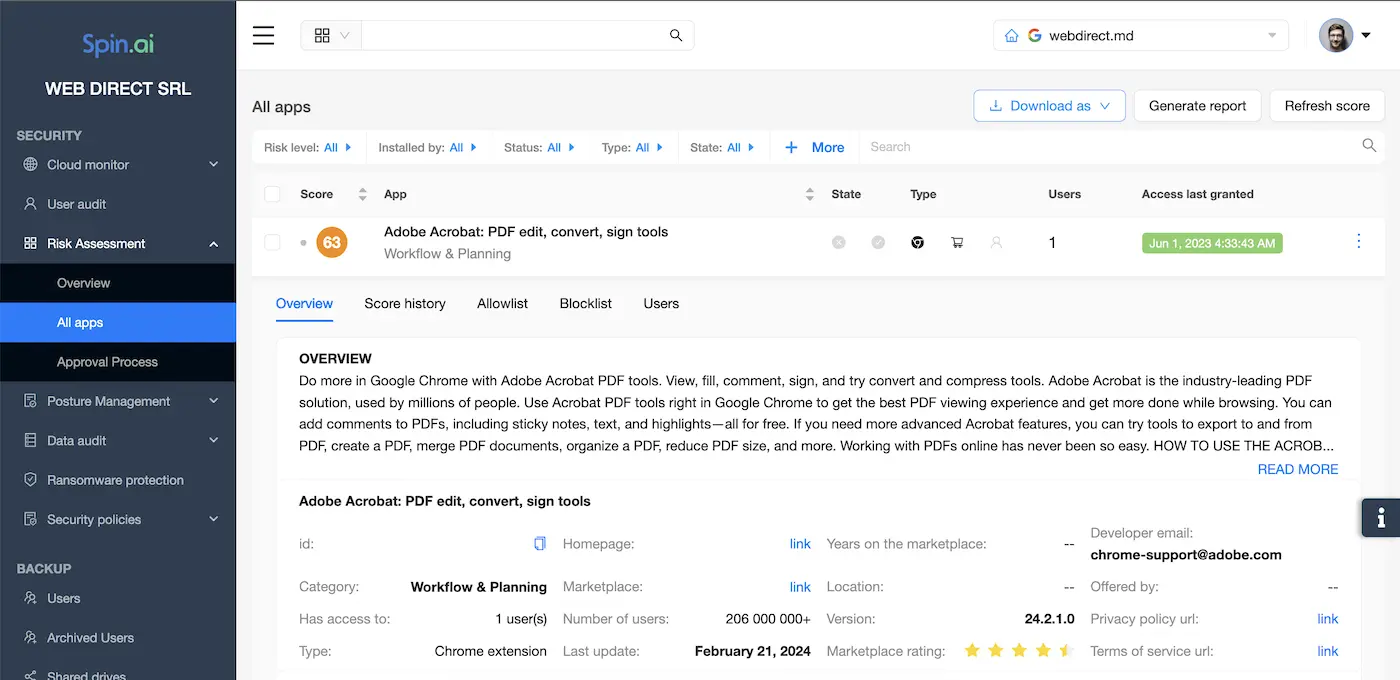
The list isn’t limited to Google applications though. It also features Chrome extensions and any platform to which your employees log in with their Google Workspace™ account. Finally, Spinone estimates the risks of the software and enables you to quickly react, i.e. turn the app off.
We strongly believe that an organization’s application security program must include the following procedure even if you don’t have special software tools
IT Admins can conduct application audits on their own, without special software. Keep in mind, however, that it will take more time and won’t be as frequent as administrators have much on their plate.
- To check for the apps, go to the Apps section of Google Admin Console. There are several tabs with a list of tools that your employees use. You’ll need Web and mobile, Marketplace, and SAML apps.
- You can turn off the access of these apps to your Google Workspace™ as well as forbid their use to all employees or to certain organizational units.
Keep in mind that Google Admin Console doesn’t assess the security risks or potential risk factors and you’ll need to do it on your own. We suggest using our checklist.
2. Business operation efficiency
People install apps because they want to be more productive in their work. However, oftentimes, they do it because they got used to some tool. In reality, this app hinders their work because of a number of problems.
We suggest assessing any tool from the standpoint of:
- Great performance: The app has no bugs (or they’re quickly removed)
- Comfortable UI and good UX
- Functionality that meets business needs
- Quick response and efficient support
3. Company Cybersecurity
The need for application security should be your primary concern. However, if you aren’t an experienced hacker it would be hard to identify the risks. There are several things to look at:
- Application’s and company’s history (are there any known problems with their security?)
- The current level of security of their website and domain.
- The extent to which the application interacts and impacts the data stored on your Google Workspace™.
4. Compliance with laws and regulations
Software security best practices state that organizations should also check for compliance issues when choosing software.
Let’s, for example, take a company that’s registered outside the US and EU. The legislation of this country might be less strict when it comes to data security or PII. And any activities considered illegal in the US will be legal there. Furthermore, it doesn’t comply with any certificates.
It means that some functions of this app might break existing regulations and your company will be engaged in illicit activities. However, you won’t be able to sue the app developer as technically it didn’t break the law or because it’s hard to reach him.
Cloud Application Security Risk Assessment Checklist
We built our checklist based on application management best practices and strategies for risk assessment process options. As mentioned above, we used the criteria that SpinOne’s algorithm applies to protect our clients’ Google Workspace™s. We divided them into 3 categories (Business Operation, Security, and Compliance risks).
Keep in mind that one single assessment criterion isn’t enough to estimate the security level of the application. You can assign marks to criteria, e.g. from 1 to 10 where 1 is low and 10 is high security.
There’s another way to calculate it. You can use percentages (100% is ultimately a secure app). And assign a certain maximum percentage to each category and criterion.
Finally, you can create your own algorithm for application security assessment.
Now let’s take a closer look at the criteria:
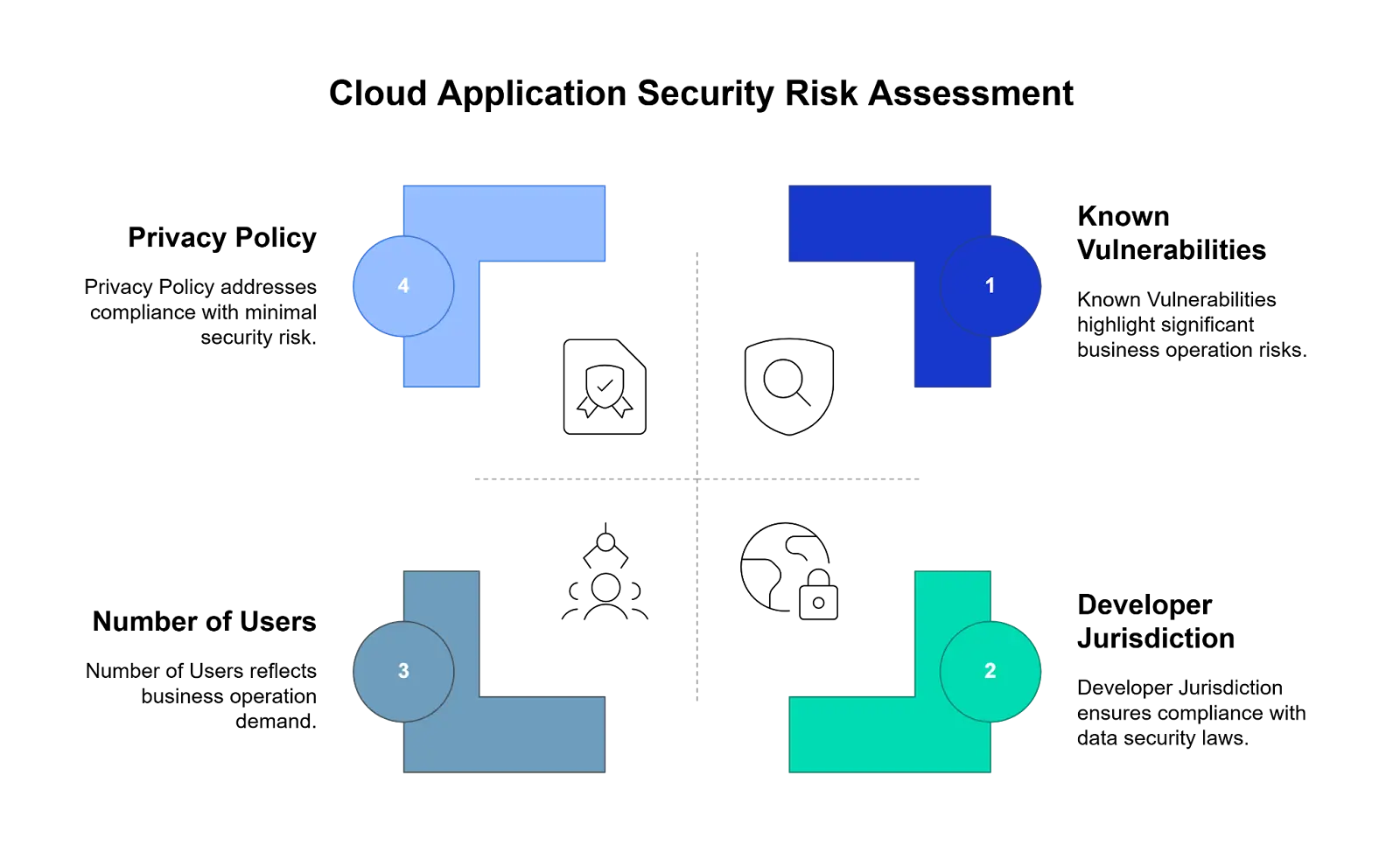
Business Operation Risk
Number of users
A substantial number of users shows that the app has a high demand. It also can be proof of good performance and great functionality.
Keep in mind that the number of users is a relative criterion. Some apps like Zoom have millions of users simply because they’re universal in use or they’re timely (or both like Zoom in 2020).
Meanwhile, other tools perform specific business functions like Vehicle Routing, a sheets add-on that helps in logistics. Finally, there are applications that connect Google Workspace™ apps with external software. For example, Wave Connect downloads data from an accounting program Wave to Google sheets.
Another aspect to think about is the tool’s age. The younger the tool the fewer users it will have. However, it doesn’t necessarily mean that the quality of a new tool is bad.
User ratings
This one is relatively simple. High ratings indicate steady performance and good functionality. You should also check the number of people who rated the app. Five stars left by 2 people isn’t a reliable rating.
Developer reputation
Look at an entity that downloaded the app. Is it a reliable company or an individual? Go to their website, try to find as much information as possible.
Another way is to see the developer’s contact information. If they don’t have their own domain like in the picture below, they’re unlikely to be a reliable party.
Latest release and Updates frequency
Updates resolve bugs that have been found in software. They also add new functionality and sometimes update the software application protection. A good frequency is once a month.
The last update more than 4 months ago is an obvious red flag.
Category
Google Workspace™ Marketplace has the following categories: Business Tools, Productivity, Communication, Education, and Utilities.
Tools from the first three categories pose the biggest risks as they’re most likely to be used in business operations. And thereby, any bugs they have will impact your work.
Security Risk
One method to discover security problems in software is to check their website for trustworthiness. There are 2 things to look at:
- SSL certificate status*
- Domain history
* SSL certificates aren’t available for apps owned by individuals
Tip: your Marketing or Web Development teams might be using a domain checker tool so you can ask them for help.
Known vulnerabilities
There are organizations that collect application security vulnerabilities reports. One good example is NIST (National Institute of Standards and Technology). They have National Vulnerability Database. You can check your applications there.
Scope of permissions
We estimate 3 levels of permissions:
- The highest risk: apps that obtain read/write access permissions can corrupt your data.
- The moderate risk: apps that only read can disclose your information to thor parties.
- The low risk: apps that have no access to your Google Workspace™ data.
Data Transmission Encryption
This is one of the application security requirements. However, it’s hard to get any reliable data on the encryption the tool is using. For this reason, we suggest lowering the security rating of any app that has data transmission.
Known breaches:
Application security has many vulnerabilities. Most of them remain undiscovered. What you can do is look up the history of breaches. Many cybersecurity journals post reports about such breaches in their blog. Some even have special sections.
We also suggest looking at the company’s response to such an incident. Denial is the worst way of conduct in such cases.
Domain Install/Individual Install
If you have many IT Administrators or you recently joined the company, you might be unaware of all the previously installed apps. Domain install signifies that the application was authorized by the IT department and thus is more reliable and secure than individually installed tools.
Compliance Risk
Privacy policy
Software security best practices state that organizations should include a Privacy policy. In reality, not all apps add it on their website or Google Marketplace. Individual developers rarely support such a practice.
Compliance and audit reports
The easiest way to obtain this information is to go to the developer’s website and look for it. Many SaaS that provide tools for enterprises have a special section in their menu (Compliance). You can also contact their sales directly.
We also advise you to ask your legal department about the compliance documentation your company requires.
Developer Jurisdiction
As we mentioned before, some jurisdictions have no laws governing data security and other aspects of app functioning. Companies and individual developers from some countries will be out of your reach simply because the relations between your homelands are tense. Another possible reason is the lack of international treaties between your countries that help solve such cases.
We suggest choosing apps created by companies registered in the EU or US.