Cybersecurity Incident: Definition, Types, Prevention & Defense
What is a cyber incident?
A cybersecurity incident is an event in a digital ecosystem that has a potentially harmful effect on and damaging consequences to an information system and organization that owns this system.
Types of incidents in cyber security
By intent:
- Malicious intent;
- Human errors & system malfunctions.
For example, downloading an app for work can bear hidden threats that your colleagues aren’t aware of.
By location:
- Internal incidents happen due to the mistakes, malicious intent of employees, system malfunction;
- External incidents take place because of events or human actions outside the organization.
For example, cybercriminals used disruptions caused by COVID-19 pandemics to carry out phishing attacks on people.
By carrier:
- Software;
- Hardware.
For example, ransomware can infect cloud drives or computers.
Examples of cyber incidents
- Power outage
- Hardware breakdown
- Software bug
- Malware infection, e.g. Ransomware attack
- SQL injectioт
- Man-in-the-middle attack
- Errors in sharing settings
- Data Breach
- DoS and DDoS attacks
- Social phishing email
- Password attacks
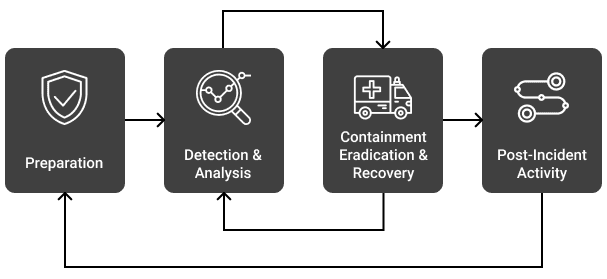
Incident management in cyber security
Management of cybersecurity incidents has three main stages:
- Prevention
- Detection & Response
- Post-incident recovery
There are several vectors of work for cybersecurity experts at each stage:
- Acquire special software tools that defend your system, detect events, and help recover. Some tools, for example, can perform several functions at once.
- Configure programs to increase your security level. Check out how you can tune your Office365.
- Enforce security policies like passwords, the use of mobile devices, checking emails for phishing, incident response plan.
- Install hardware and equipment that decreases the dependence on physical damage to information system components.
- Educate your colleagues.
- Assign incident response team for better management.
- Report cyber attacks and cases of malware infection to law enforcement agencies.
No activities can guarantee 100% prevention of cybersecurity incidents. That’s why it’s critical to think about the recovery measures you’ll be taking after the event.
Cyber security event vs incident
Many people use these terms interchangeably. However, a cyber event has a broader meaning. It denotes any occurrence in a given digital system (neutral or dangerous). Meanwhile, incidents have harmful consequences.
Example:
Event: An employee shared a file outside an organization.
Non-harmful event: Sales manager shared a product demo with a potential client.
Cybersecurity incident: Sales manager shared the client database file with anyone with a link.