Disaster Recovery in the Cloud: Ultimate Guide For Businesses
Disaster recovery is essential when a major cyber incident strikes and a company’s employees can’t access IT systems or data. In this article, we discuss the specifics of disaster recovery in the cloud and suggest tools that can minimize downtime.
What is Disaster Recovery (DR)
Malfunctions in IT systems are inevitable. They occur due to human errors, software bugs, or malicious actions of third-party actors. Regardless of the source of malfunction, businesses must be prepared to a disaster and have a recovery plan for any and all possible cases.
Disaster Recovery is the body of procedures that an entity takes to recover from a disruptive incident within its IT environment. Many organizations with complex IT systems have Disaster Recovery Plans in order to speed up the process. When talking about disaster recovery you should also take into account tools that facilitate such a recovery.
Objectives of disaster recovery
The objectives of disaster recovery include:
- Recover data that has been lost during the incident
- Restore the functionality of an IT system
- Minimize the downtime caused by the disaster
- Make sure that no data has been leaked or will be leaked
- Mitigate all the negative outcomes of the incident.
A disaster recovery plan has similar objectives. It also documents the ways to achieve these objectives and the tools that will be used to this end. For example, the goal is to recover the data. The tool to attain this goal is a backup solution. The method is data recovery from the backup.
One of the key disaster recovery objectives is to minimize the costs of a cyber incident to the organization.
These costs include:
- Data recovery costs
- Cost of permanently lost data
- Cost of restoring the IT systems
- Cost of downtime
- Cost of revenue and reputational losses
- Legal fees and fines.
Differentiating DR from data backups, business continuity and incident response plan
People sometimes confuse data recovery, backup, business continuity and incident response. These terms are different, although most of them are connected to cyber incidents in one way or another.
- DR vs. Backup
Backup is a tool or a procedure for regular data copying. Backup tools are used during disaster recovery to restore the information if the incident includes data loss.
- DR vs. Business continuity
Business continuity is the body of measures that an organization undertakes to continue its operations during a cyber event. Meanwhile, disaster recovery is focused on restoring data and the IT system’s functionality.
For example, during a ransomware attack, all cloud files have been encrypted. The data recovery from the backup can take weeks or even months (depending on the size of data lost). While disaster recovery will be focused on speeding up the recovery, business continuity will look for ways to continue operations without access to the data. For example, they’ll be working with paper copies of the documents.
- DR vs. Incident Response
Incident response includes disaster recovery but encompasses more activities. These include, for example, stopping the cyber attack, investigating its sources and reasons, etc.
How does Disaster Recovery work?
Disaster recovery in organizations has two major stages:
- Anticipation
- Mitigation
- Analysis
Some include Disaster Prevention. In our opinion, it’s incorrect to include prevention tactics and methods in disaster recovery. Cyber accident prevention should be a separate part of the general cybersecurity strategy of an organization.
Anticipation in disaster recovery is basically the planning or preparation stage. At this stage, the IT security team of the company must analyze and list all the possible cyber incidents and associated risks that can take place within its IT environment.
Next, the team should analyze how to minimize the outcomes of these incidents and create a recovery plan for each type of incident. For example, the team should understand which tools they need to purchase to help disaster recovery. It’s reasonable to prepare a disaster recovery plan and incident response plan simultaneously.
The mitigation stage encompasses the disaster recovery process from the beginning of the incident till the end of recovery. Remember that some data or systems might remain lost permanently.
At the analysis stage, the IT security team analyses how recovery went, which mistakes were made, and how to improve disaster recovery in the future.
Disaster recovery (DR) in cloud environment
Cloud environments differ from on-prem environments. That’s why disaster recovery should be different from on-prem recovery.
The main difference is that in cloud environments the physical systems do not belong to the organization as it hires them from the data center. It is extremely rare, that any cloud environment has any type of physical damage. Virus attack is also rare unless it is cloud ransomware.
The most widespread risks in cloud environments include:
- Data loss
- Data leaks
- Human errors
- Zero-day attacks via risky applications
- Account hijacks
- Ransomware
- Cloud misconfigurations.
One of the greatest challenges for disaster recovery in cloud environments is the speed of data upload in the cloud. Many cloud solutions use APIs to connect with backup tools. The API calls are limited to avoid cyber attacks. If your organization has experienced a major data loss event, the recovery can take days or even weeks.
You need to take into account this issue when you’re planning your recovery. The best practice is to catalog and categorize your data. For example, there are documents that are necessary to preserve for legal purposes and your organization is not actively using them at the moment.
For example, organizations retain data of employees who are no longer working in the company. Another example is the data about past projects. These files can be recovered last. Meanwhile, files that contain the current projects must be restored first-hand. Keeping your data cataloged and mapped can help you speed up the recovery process.
Leading Disaster Recovery (DR) Tools for Cloud
There are two types of tools that can help you make disaster recovery in your cloud fast and seamless.
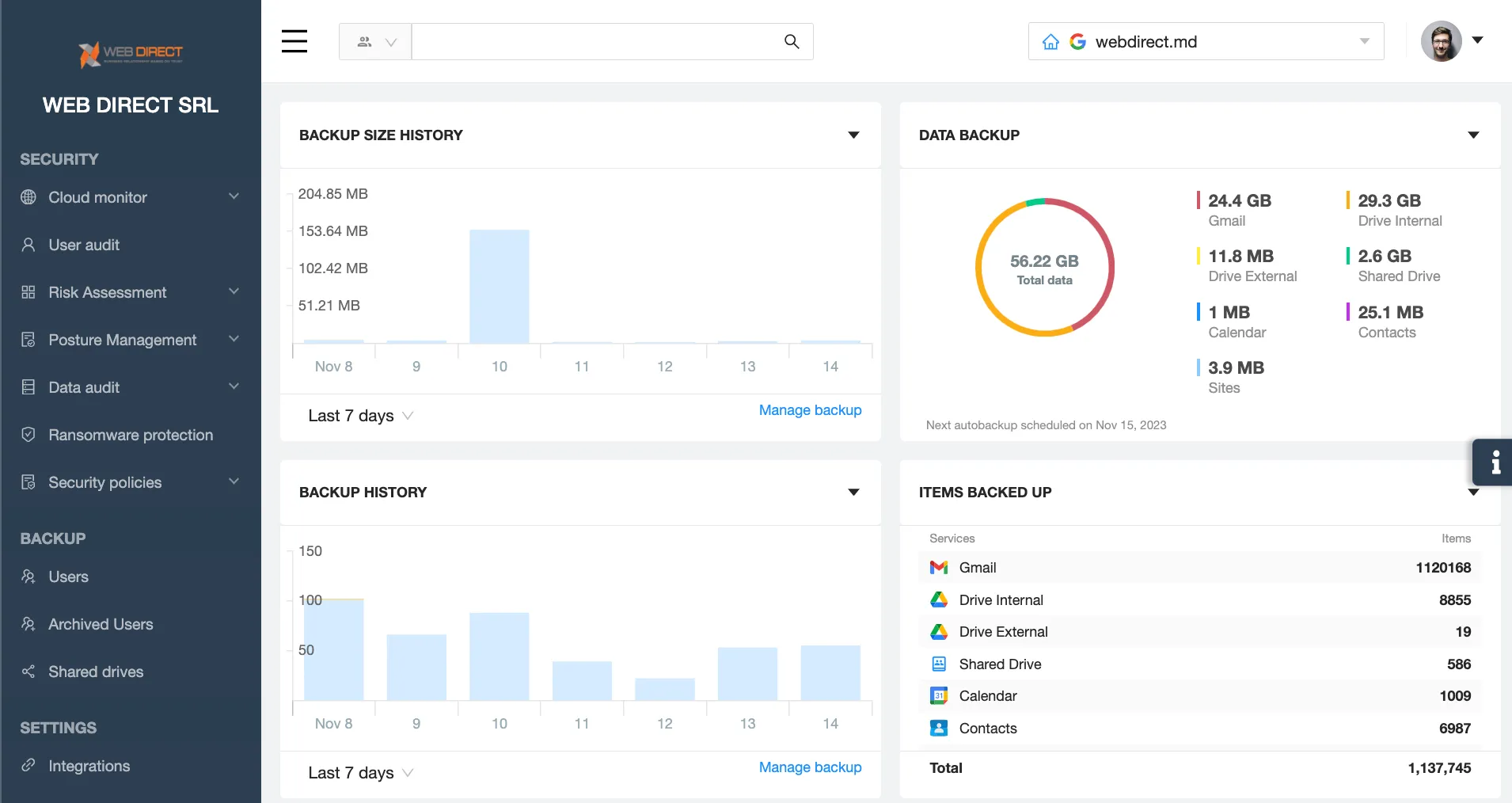
First, it’s a cloud-to-cloud data backup. These tools can help you avoid permanent data loss and can shorten associated downtime significantly. When choosing a backup for your cloud we suggest looking into tools that have the following features:
- regular daily snapshots;
- incremental backup;
- unlimited storage;
- ability to choose between several data centers and geographic locations;
- possibility to download data on your desktop.
Second, we recommend proactive ransomware detection and response. Keep in mind that not all ransomware protection tools are equally effective. Look into the following features:
- AI detection based on data behavior
- ability to stop ransomware within minutes after the beginning of the attack
- automatic recovery.
Ransomware protection tools with such characteristics will help you minimize your downtime and streamline your recovery.
FAQs
Why is Disaster Recovery important for businesses?
Disaster recovery is critical when a major cyber event takes place and an organization’s workforce cannot work with its IT systems and/or data. The faster and more efficient this process is, the smaller is downtime and general impact on business operations.
What is the process of disaster recovery?
Disaster recovery starts with analyzing possible cyber incidents, acquiring recovery tools, creating a reliable disaster recovery plan, and then acting on this plan.
What is disaster recovery with example?
Disaster recovery is a body of activities aimed at restoring IT systems and recovering data after a major cyber incident. An example of disaster recovery is restoring data from backup after it has been lost.