Ransomware Attacks Surge in 2023: What SMBs Should Know
Ransomware attacks are on the rise again in the first quarter of 2023. No business is exempt from being a target and potentially a victim. This post is a warning of the ransomware attacks surge for small and medium-sized companies. Learn the main trends in ransomware and how to protect your data.
Ransomware Attacks Surge
In mid-2022, we saw a significant decrease in ransomware attacks. It looked quite promising for many companies who had ramped up their security measures, hoping that the threat was declining. However, many cybersecurity experts didn’t share enthusiasm around this “lull.” It’s usually the calm before the storm.
In the autumn of 2022, the ransomware gangs began getting back on track and peaked in March 2023.
There have been several major attacks on companies that impacted their employees, partners, and clients, causing downtime and disruption in thousands of organizations. The examples include attacks on CoomonSpirit Health (several hundred hospitals suffered), CommScope (several thousand employees), and NCR (hundreds of restaurants impacted).
This isn’t surprising. Successful ransomware gangs earn millions of dollars, tax-free, within several months. Furthermore, the members of these gangs remain unknown to the authorities in most cases and thus can enjoy the earned money anonymously.
Key Ransomware Trends for SMBs to Know in 2023
Cybersecurity analysts at Spin.AI have been closely watching the key cybersecurity trends over the past several years. Here are the three most recent ransomware trends to watch out for:
Encryptionless Ransomware
As one journalist desperately wrote: “Let’s tell the truth, it’s no longer blackmailing, it’s a straightforward data theft.”
Fewer ransomware victims report data encryption. Meanwhile, there has been a significant increase in news reporting on the sales of stolen data on the Dark Web and the threats of data exposure to the public.
Data theft is powerful leverage in negotiating with companies that are unwilling to pay a ransom and instead plan to use data backup or available decryption keys.
Cybersecurity legislation is tightening
Meanwhile, countries are adopting more laws to hold the targets of cybercrime accountable for ransomware attacks that cause data leaks. At the same time, paying ransom is getting harder, as it’s banned in some countries. Furthermore, under certain legislation, paying for your data can be considered terrorist sponsorship.
As a result, companies end up between laws forbidding them to pay criminals and the real possibility of sensitive data being exposed.
SMBs are targetted for data extortion
While enterprises remain the main focus of ransomware gangs, SMBs are targeted primarily for the data they have. It includes customers and business partners. This is especially critical for B2B companies that serve large businesses and the IT sector.
How to Protect Against Ransomware
As data security challenges intensify, the new ransomware trends demand new approaches to ransomware protection. The old approach for small businesses was to wait until the end of the attack and the subsequent data recovery from backups. Now, there’s a higher possibility of data theft than before. And companies cannot just passively wait.
We suggest the following strategy:
Transform your cybersecurity culture
Cybersecurity culture defines how your employees treat IT security and the possibility of incidents. Cyber awareness training can help your employees detect phishing emails – one of the key ransomware attack vectors. It should be continuous and regular.
Change your cybersecurity policies
Even the best training cannot guarantee 100% security. Human mistakes are inevitable, even more so if your digital environment lacks policies that enforce safer behavior. For example, account highjacking is another widespread attack vector.
If you do not impose two-factor authentication, complex passwords, and monthly password changes, training your employees will not help. They will simply forget or silently refuse to comply.
Get proactive ransomware protection
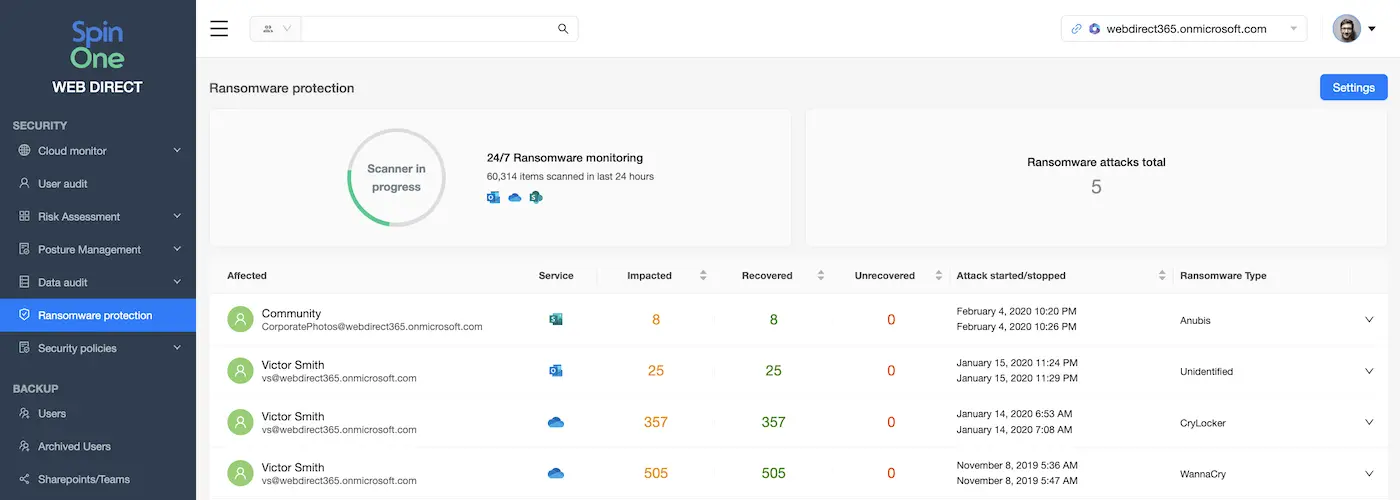
AI protects against ransomware by analyzing data behavior, identifying the source of trouble, and blocking its access to the IT system. Companies with such protection do not have to wait for the attack to stop.
Get data monitoring tools
Another way to deal with modern ransomware attacks is by using data monitoring tools. These tools can detect abnormal patterns in data, like large downloads, and alert IT security. It can also suspend users who act abnormally.
Check out SpinRDR – the platform that has data behavior monitoring and proactive AI-based ransomware protection.










