Ransomware Protection: 9 Proven Strategies for 2026
Ransomware remains one of the most damaging cybersecurity threats facing organizations today. Beyond ransom payments, attacks often result in extended downtime, operational disruption, regulatory exposure, and long-term reputational damage.
In recent years, the average cost of a ransomware incident has reached multiple millions of dollars when factoring in downtime, lost productivity, and recovery efforts — often excluding ransom payments altogether.
At the same time, ransomware has matured into a highly scalable criminal business model, enabling attackers to target organizations of all sizes across industries.
This guide explains what ransomware is, outlines the most common ransomware types, and, more importantly, walks through nine practical strategies organizations can use to protect against ransomware in 2026.
What is Ransomware
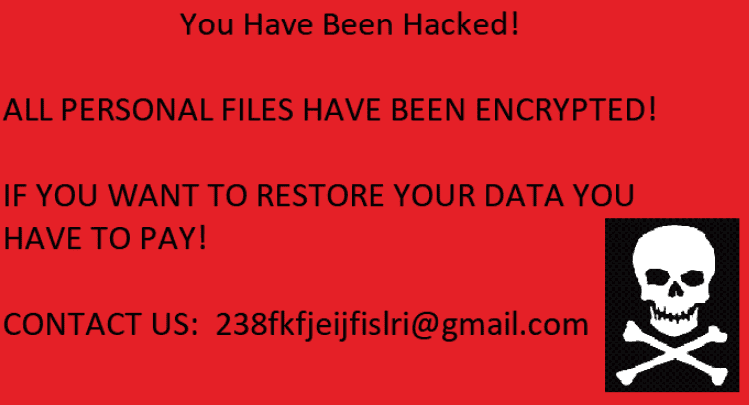
Ransomware is a type of malware that blocks access to a computer system and/or encrypts data until a victim pays a ransom. Typically, attackers demand payment in exchange for restoring access to the affected system or data. Ransomware can spread through phishing emails, infected websites, or software vulnerabilities, and it poses a significant threat to individuals, businesses, and organizations by disrupting operations and potentially leading to data loss.
Attackers then hold the data hostage until a ransom is paid. After receiving a payment, criminals provide encryption keys to unlock and normalize the data,
Early signs of ransomware activity are hard to notice. In many cases, organizations only become aware of an attack once encryption is complete and a ransom note appears, demanding payment for recovery. For a deeper explanation of how ransomware works, its lifecycle, and standard attack patterns, see our whole definition of ransomware: https://spin.ai/blog/ransomware.
Learn about what to do with the ransomware and the common steps to take during the ransomware attack.
Types of Ransomware
Over the past 3 decades, ransomware has evolved into several distinct forms. The most common types include:
Wiper Ransomware
Wiper ransomware permanently deletes data instead of encrypting it. Recovery is impossible unless clean backups exist. These attacks are often politically or ideologically motivated and designed to cause maximum disruption
Encryptor Ransomware
Encryptors are the most common ransomware type. They encrypt files or entire disks and demand payment in exchange for a decryption key. Some variants encrypt specific files, while others target complete systems.
Leakware (Double and Triple Extortion).
Leakware steals data before encrypting it. Attackers threaten to publish or sell sensitive information if payment is not made. In some cases, attackers escalate pressure by threatening customers or partners associated with the victim organization.
Ransomware-as-a-Service (RaaS).
RaaS is a model where ransomware tools and infrastructure are made available to other criminals. This has significantly lowered the barrier to entry for ransomware attacks and contributed to their rapid growth.

How to Protect Against Ransomware
The following strategies reflect best practices in 2026, and they’re an in-depth approach to ransomware protection.
Backup Your Data Regularly!
Backups remain the foundation of ransomware resilience. Without reliable backups, recovery options are minimal.
However, backups are not ransomware-proof by default. If ransomware gains access to production systems, it can also encrypt connected backup data.
Best practices include:
- Following the 3-2-1 rule – have a minimum of three copies of your backup, on two mediums, keeping one copy offsite;
- Backing up data multiple times per day.
- Enabling versioning and long-term retention.
- Isolating backups from production access.
Some backup platforms now include ransomware detection and automated recovery features, helping organizations reduce recovery time and operational impact.
Install Antivirus and Endpoint Protection
Antivirus software remains a vital baseline defense, but modern ransomware often bypasses signature-based detection.
Endpoint protection platforms that use behavioral analysis, anomaly detection, and automated containment are now essential components of ransomware defense.
Use Firewalls to Control Network Traffic
Firewalls continue to play a critical role in blocking malicious traffic, limiting lateral movement, and reducing exposure to exploit-based attacks.
Both network-level and host-based firewalls should be configured appropriately and continuously monitored.
Conduct Application and SaaS Access Audits
Unauthorized or overly permissive third-party applications remain a common ransomware entry point, especially in SaaS environments.
Organizations should regularly audit application access, permissions, and OAuth grants to minimize exposure.

Filter Emails for Phishing and Malware
Phishing remains the leading ransomware delivery vector. Advanced email security controls, combined with real-time link and attachment analysis, are critical to reducing risk.
Email filtering should be paired with behavioral detection to identify suspicious user actions.
Manage Access and Permissions Carefully
Excessive permissions increase ransomware impact. Least-privileged access, regular permission reviews, and a straightforward role management process significantly reduce the blast radius of an attack.
Enforce Strong Authentication and MFA
Credential-based attacks continue to fuel ransomware campaigns. Strong password policies and mandatory multi-factor authentication (MFA) are now baseline security requirements.
Train Employees on Ransomware Protection Strategies
Human error remains a factor in many ransomware incidents. Ongoing security awareness training, phishing simulations, and transparent reporting processes help reduce risk, but must be reinforced with technical content.
Use Third-Party Ransomware Protection Solutions
Dedicated ransomware protection platforms can provide advanced detection, automated response, and continuous monitoring, particularly for SaaS environments where native protections are limited.
How Can Ransomware Infiltrate Your Environment?
Ransomware commonly enters environments through phishing emails, malicious attachments, compromised websites, or exploited vulnerabilities. Once executed, it can rapidly encrypt data across endpoints, shared storage, and cloud-connected services.
Ransomware Can Infect Public Cloud
Public cloud services such as Microsoft 365 and Google Workspace provide high availability, but not complete ransomware protection.
Native retention and recycle features are not substitutes for backups. If ransomware encrypts synchronized data, clean versions can be overwritten or aged out before decryption.
Cloud data must be protected with the same rigor as on-premises systems.
Ransomware Protection With Spin.AI
Organizations may also consider third-party SaaS security platforms that combine backup, ransomware detection, and automated response. Spin is a great option designed for Google Workspace and Microsoft 365 environments.
Concluding Thoughts
Ransomware defense in 2026 requires layered controls, continuous monitoring, and tested recovery processes.
No single tool can prevent every attack, but organizations that invest in preparation and response capabilities are far better positioned to minimize impact and recover quickly.
By implementing a proactive, automated, and intelligent response provided by SpinOne, businesses can take the offensive against ransomware attacks instead of simply reacting to an attack and restoring data manually.
FAQs
What is the first action to take against ransomware?
Immediately isolate affected systems from the network to prevent further spread, then begin containment and investigation.
Can antivirus software detect ransomware?
Antivirus software can detect some ransomware variants, but modern attacks often require behavioral, AI-driven, and layered defenses.
What is the most common way ransomware is spread?
Phishing emails, malicious links, compromised websites, and exploited vulnerabilities remain the primary delivery methods.










