Balancing Security and User Experience with SSPM
When discussing user experience and security most authors focus on app development with security in mind. These articles are written for web developers and UI/UX designers or are focused on user interface. This article has a different approach. Created for security experts, it explains how cloud security and user experience needs can cancel each other out, and how you can balance them with an SSPM tool.
Cloud Security
To understand the impact of security on user experience we need first to understand how cloud security works.
First, clouds do not have defined security perimeters, unlike on-prem environments. People can access the cloud from any point in the world, and it makes the cloud especially susceptible to account hijacking. Ultimately, it means that any user in the cloud can be a malicious actor aiming to harm the environment or steal data.
That’s why the notion of zero trust is so prominent in modern cloud security.
Second, clouds are especially vulnerable to Shadow IT. Many cloud environments enable users to access applications using their accounts. In return, SaaS applications can access and even edit data stored in the cloud environments (depending on the permission settings). This creates an opportunity for zero-day attacks.
Monitoring and controlling Shadow IT is one of the most tedious and time-consuming tasks for the Admins in cloud environments.
Third, sharing options for files with different editing permissions makes the cloud even more “porous” and susceptible to attacks.
User Experience in the Cloud
User experience has become the single most important indicator of user retention in the B2C sector. It is not as important for B2B solutions just yet. There are several reasons for this. First, it is the business that makes purchasing decisions, so user’s opinions about their experience with the product might actually fail to reach the decision-makers.
Second, many other factors can impact retention. For example, Salesforce is considered the most secure CRM tool, and companies that are interested in security and compliance will keep it no matter what. Another factor is compliance. Many applications that have better functionality and UX aren’t used because of their region or lack of certain certifications.
Third, user experience in these tools can differ for Administrators and for users. For example, Google Workspace™ services are usually praised for their usability. However, the Admin Center can be very tricky to navigate.
This disregard for user experience when acquiring cloud office suites and SaaS applications often forces employees to use certain unauthorized applications. Such a practice is called Shadow IT.
At the same time, SaaS developers might pay less attention to the UX of Admin Centers. We think there are several reasons for this phenomenon. First, the users of the Admin Centers, i.e., Admins, are considered tech-savvy. Therefore, the need to make the application as user-friendly as possible might be less significant than focusing on the UX for non-Admin users.
Second, the Admin centers have so many features and controllers that making light UX might be hard. Thus, the developers hope that Admins will eventually rely on “muscle memory” when getting around the endless tabs and sections of the center.
However, this can often result in cloud misconfigurations that can lead to serious security breaches. Misconfigurations are incorrect settings of applications, in particular, security settings. They happen when Administrators are overloaded with work and need to introduce new configurations in the complex system which is hard to navigate. Another possible scenario is the mistakes during the initial setting of the system.
There are many metrics that measure user experience and usability. These include:
- completion time,
- task success rate,
- retention rate,
- conversion rate,
- error rate,
- satisfaction.
When talking about the usability evaluation of large cloud environments like Google Workspace™ or Microsoft 365, retention and conversion rates can be omitted, as most users have little to no impact on a business’ decision to acquire the cloud office suite.
First, the market of cloud office solutions is divided roughly fifty-fifty between the two giants. Second, both Microsoft 365 and Google Workspace™ offer a very good balance between user experience and security.
Third, the security functionality (from protection against natural disasters to DLP) in these environments is the best in class. Therefore, any hindered user experience is often disregarded during the purchasing process.
Cloud Security and User Experience
The above-mentioned specifics of cloud security can hamper the user experience for both cloud users and cloud administrators in charge of security.
Zero-trust security architecture can have a significant impact on the user experience. Contrary to the popular perception, zero-trust security doesn’t imply complete zero-trust, i.e., asking for a user to prove their identity before completing any minor action like editing a document.
Such an approach would severely impact at least two UX metrics (completion time and satisfaction). It would probably increase the error rate and decrease the task success rate.
One of the best practices for security with user experience in mind is “to make security invisible.” In cloud environments, it is achieved by giving a user minimal access and privileges possible. In other words, you need to create an environment of “closed doors” that requires users to “knock before entering.” That’s zero-trust in a nutshell.
Thus you need to build a system in which all files and folders are inaccessible by default. And that’s exactly how the Google Workspace™ and Microsoft 365 environments are built. The problem begins when users start sharing their files.
Disabling the sharing option can severely impact user experience, i.e., task success rate, task completion time, and user satisfaction. That’s why most companies enable their users to share files within the organization. This can have severe consequences for security and cause data loss and data leakage.
The risks begin to pile up when you add uncontrolled third-party SaaS applications. Many companies have policies that forbid using apps unauthorized by the company. In practice, even IT security leaders end up using Shadow IT simply because it boosts their productivity and ultimately increases the UX metrics like task completion, and
Cloud environments still have security gaps and require third-party tools to close them. The abundance of such tools can hinder user experience for Administrators who are forced to work in multiple environments and keep track of many alerts at once. This impacts admins’ user experience decreasing satisfaction. Furthermore, overwhelm and fatigue among cybersecurity professionals is one of the most severe problems.
How SSPM Helps Balancing User Experience and Cloud Security
SSPM can help IT security professionals by providing invisible security, enhancing zero-trust without the user’s knowledge, and controlling sharing and third-party apps. Let’s take a closer look at these functions.
First, SSPM provides complete visibility and control of shared files. Not only does it alert Admins on improper or risky sharing it enables them to create sharing policies and even change sharing options right on the spot for the Admin. This process is carried out without the necessity to go back and forth with the user trying to convince them to change the sharing options.
Second, SSPM enables Admins to have a bird’s eye view of the Shadow IT. They detect all the applications that have OAuth access to your data. SSPM tools have a built-in app risk assessment function that can help security professionals streamline the decision-making process on app usage. Furthermore, they also provide control to Admins like manual access revoke and the ability to create allowlists and blocklists to automate the process. SSPMs have functionality that helps users request access to certain apps right in the browser omitting the communication in the email or messengers.
Third, SSPMs have proven to be very efficient in addressing misconfigurations in SaaS applications. These solutions can detect and notify Administrators on the gaps in their settings and prevent data breach just in time.
Finally, SSPMs provide a single pane of glass for many security functions that close the cloud environment security gaps, alleviating the overwhelm of the Admins.
SpinOne SSPM
SpinOne SSPM solution can help businesses overcome the major security challenges in the cloud. It’s the best tool to balance security needs with user experience for both end users and administrators.
SpinOne SSPM functionality has three major components:
- Application monitoring and control
SpinOne detects any SaaS applications and browser extensions that have OAuth access to your business-critical SaaS data. It also has an in-built risk assessment tool that evaluates the security of an application based on 15 different criteria.
SpinOne SSPM provides a control panel that enables Admins to block the application right on spot. They can also create blacklists and allowlists to automate application control. Finally, it has an inbuilt functionality to enable communication between the Admins and the users requesting for the app approval.
- Access control
SpinOne SSPM gives your Admins to monitor and control the access to your data. It begins with a full visibility into your files sharing settings. You can check any file and see if it has been shared with unauthorized people (e.g., outside the organization, or outside department).
Next, your Administrators can change the sharing settings to meet your security needs and even take over the document if they think that the user has compromised themselves.
Finally, they can create DLP policies to automate sharing control process. With these policies, SpinOne will be able to change the sharing settings automatically.
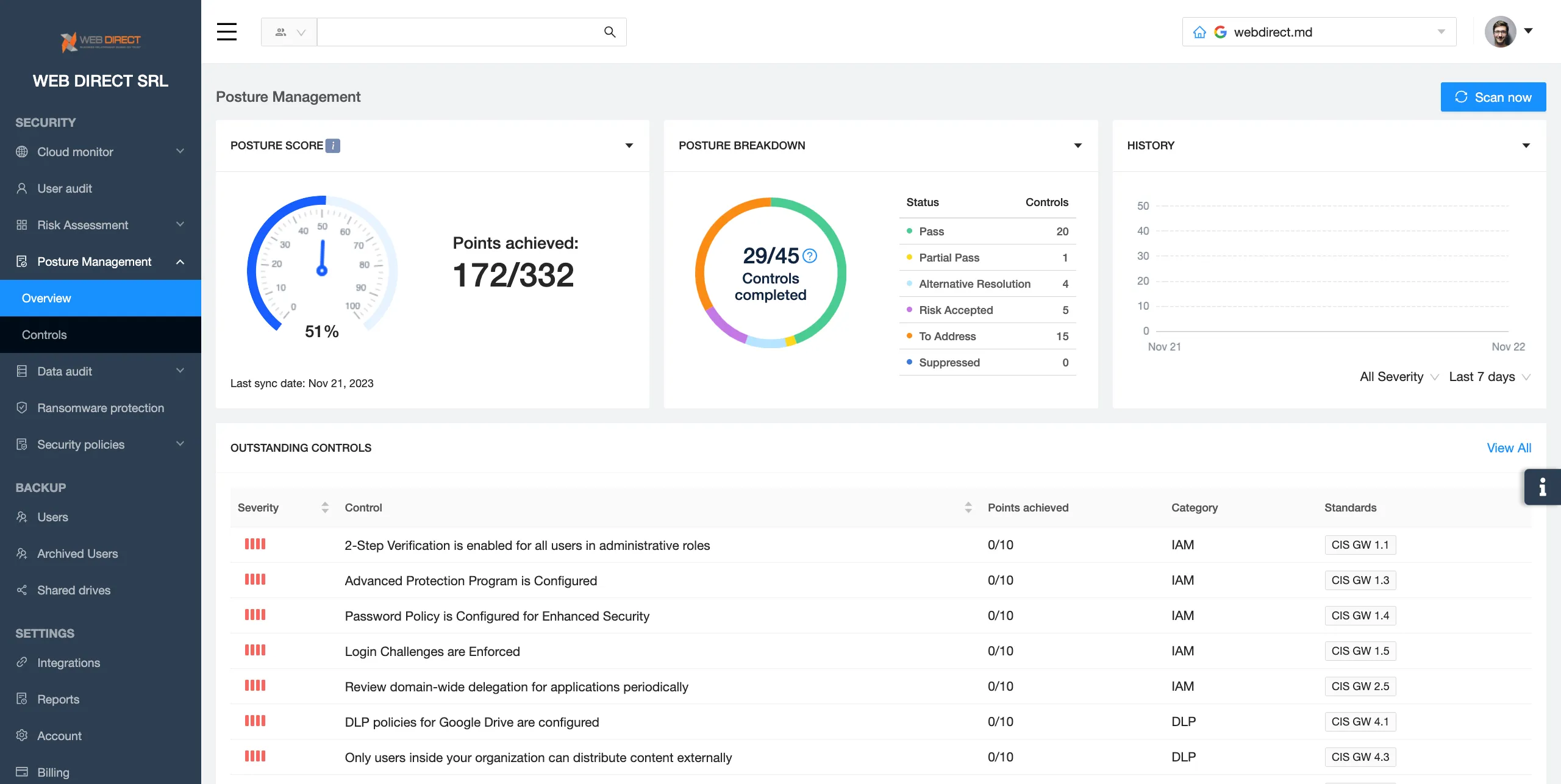
- Misconfiguration control
SpinOne can easily detect any misconfigurations in the cloud and suggest the changes that need to be done. The tool assigns the priority to each misconfiguration. It helps Admins to address the most critical security gaps in the first place.