Shadow IT Examples that will Make You Question Your Company Cybersecurity
Most enterprises don’t realize how many risky apps have access to their Google Workspace™ and the data stored there. They rely on Google security solutions until they have a major data breach. In this article, we collected five Shadow IT examples demonstrating how fragile a company can be against cyberattacks via applications.
What is Shadow IT? A Short Overview
So what is Shadow It? Shadow IT is any information technology system that a company’s employees apply in their daily work without the approval or knowledge of their IT Department.
Example: A medium car rental company has a Bring Your Own Device (BYOD) policy. They also use Dropbox to share files. Because most employees don’t have antivirus tools installed on their laptops, a virus infects their devices that causes severe downtime.
Back in 2018, Gartner predicted that shadow IT would be responsible for about 1/3 of resultful cyberattacks. A recent survey of Forbes states 21% of companies suffered a “cybersecurity event due to an unsanctioned IT resource.”
In late 2020, Spin Technology conducted a meta-data analysis to check the accuracy of Gartner’s prediction as well as provide aggregated data on shadow IT. Here’s what we found:
- ~49% of cyberattacks were due to shadow IT.
- Large enterprises spend ~42% of their IT budget on it
- The average number of applications per company is ~477.7.
- The real number of applications used in the company is 14.6 times bigger than the number known to the IT department.
- ~67% of individuals and teams brought their own tools to their organization, ~40% use unauthorized software in their daily work
Shadow IT Security Risks
In most cases, when an employee downloads an application for work, it means they want to boost their productivity and efficiency.
Example: many people purchase Grammarly (or use its free version) to express their thoughts better.
It can also signify that a company lacks proper communication between departments. As a result, some employees have no idea about the tools that their company has bought for them.
Examples: The Web Development department deployed Asana as software for project management. They don’t know that their organization is using Basecamp.
Headquarters in New York purchased Google Workspace™ Business Standard. Their regional affiliate used Google Workspace™ Business Starter.
Finally, it can indicate that the tools that the company purchased are too complex and employees need additional training to use them with convenience.
Example: To comply with the existing regulations and security requirements, the company purchased a CRM from Salesforce. However, the sales team is reluctant to use it because it’s hard to find the functionality they need in the menu with 40 buttons. They secretly apply MailChimp for most of their outreach.
Unauthorized software risk:
- Decrease of business efficiency due to:
- Issues in data search and incompatible data formats
- Impediments in collaboration between departments
- Excess expenses on software
- Problems in communication
- Double work
- Security risks:
- The level of security of certain tools might be insufficient and create a large number of entry points for cyber attackers
- Security gap: IT team can’t protect a tool about which they’re unaware
- Outdated security: employees often do not upload necessary updates
- Third-party access to critical data (such as your credentials, sensitive information, etc.)
- Data and accounts on shadow IT are beyond the control of your IT department
- Compliance issues
- Some apps can help your employees bypass the security restrictions that might cause data leak
- Stealing PII of your employees (especially C-level) can create multiple opportunities for social engineering attacks.
The biggest risks of shadow IT are the lack of visibility and awareness. Such seemingly secure things as an account in Google or Microsoft can pose serious danger if it’s under the radar of your IT department. Shadow IT policy is crucial in preventing and mitigating the risks associated with unauthorized applications.
Unfortunately, most experts predict that this problem will worsen with time as more digital natives will be joining the workforce each year. That’s why businesses need a reliable tool to find shadow IT and control it.
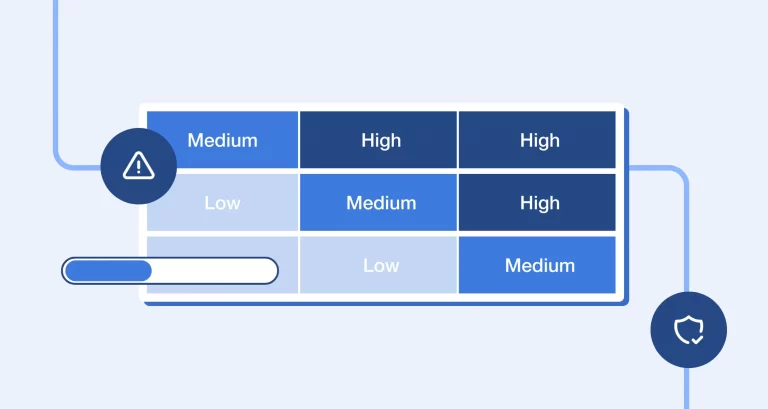
At our demo calls our sales usually ask potential clients how many applications their users work. Then we use SpinOne to detect shadow IT. In most cases, the number of applications exceeds significantly what cybersecurity managers think. Our next step is to show how risky these apps really are.
Shadow IT Examples
Reports of shadow IT are scarce. As a rule of thumb, cybercriminals use it to access sensitive information (e.g. PII) in order to sell it to third parties or commit crimes (such as social engineering).
In the present article, we’ll take a look at some of the most notable and some of the biggest data breaches. By studying them we can estimate the possible impact on businesses:
A Bug in Anti-scam App Opened a Backdoor to Scammers
App name – Truecaller
Victims – 47.5 million
Time of detection – Spring 2020
Security breach reported by Cyble
App functionality – Identifies callers, blocks scam and fraud calls
Country of app origin – Sweden
Problem – Bug: Criminals could modify their profiles by inserting a malicious link. A click on this link would initiate a malware script on a user’s telephone, no user’s consent is required.
Result – PII (Name, job title, gender, city of residence, telephone number, work email, Facebook account, etc.) of 47.5M users were sold on the dark web for $1,000.
More details: Cyble’s report
Background:
In May 2019, an independent researcher Rajshekhar Rajaharia reported the leak of 300M citizens of India. According to him, victims included CEOs, politicians, and celebrities. Truecaller denied these accusations.
In Q4 2019, Ehraz Ahmed, a cybersecurity expert, uploaded a video on YouTube revealing the weakness in the Truecaller security system. The bug was reportedly fixed by the company.
However, in Q1 2020 the stolen PII of 47.5M app users surfaced in DarkWeb. Again, Truecaller denied that their app was the source of this data.
Possible outcomes to the businesses:
The Personally Identifiable Information opens the gate to a large amount of spam as well as cyberattacks based on social engineering.
The World’s Largest Platform for Building Apps Hacked
App name – Docker
Victims – 190K app creators
Time of breach – 2019
App functionality – App building platform.
Country of origin – USA
Problem – Data breach
Result – Hackers stole the credentials of 190K users of the platform. This potentially opens the gate for cybercriminals to alter the application’s built-in Docker and insert malicious code.
Data Breach Contributes to the Decline of Google’s Major Competitor
App name – Yahoo!
Victims – approximately 3B people
Time of breach – 2012-2016
App functionality – Web services including search engine, news, email, web directory, advertising, etc.
Country of origin – USA
Problem – Data breach due to phishing attacks
Result – Multiple attacks happened throughout the years due to poor security practices. As a result, cybercriminals took the records of 3B users and could access their emails and calendars.
Yahoo! Had to pay $117.5M as a settlement and it also lost its top positions in the world.
The outcomes for businesses and individuals affected by this data breach remain unknown.
Biometric Smart Lock Opened to Reveal the Unchangeable Data
App name – BioStar 2
Victims – approximately 1M people
Time of detection – Summer 2019
Security breach reported by Noam Rotem and Ran Locar
App functionality – Biometrics smart locks and access control. Clients include banks, governments, and police around the world.
Country of origin – South Korea
Problem – Data breach
Result – Criminals stole PII: fingerprints, iris scans, facial data and photos, usernames with passwords and IDs, contact data (home address, email, telephone), titles, and work data (such as time of visit to restricted areas, months in the position, etc.). They also gained access to the client admin panels and other sensitive data.
Probably the worst outcome is the fact that some of the stolen personal data can’t be changed by the owners. Unlike username or password (or even your full name and facial traits), you can’t change your fingertips or iris.
Medical Records Stolen because of the Billing Webpage
App name – American Medical Collection Agency
Victims – approximately 20M people
Time of breach – 2019
App functionality – billing webpage
Country of origin – USA
Problem – Data breach due to phishing attacks
Result – Cybercriminals stole 11.9M medical records (along with billing information, social security numbers, and insurance data) from Quest Diagnostics and another 7.7M from Labcorp.
Frequently Asked Questions
What is the new term for shadow IT?
Shadow IT is often referred to as business-managed IT, which is not entirely correct. Shadow IT and business-managed IT are related concepts within an organization’s technology landscape as they both involve technology initiatives that are adopted and managed outside the traditional boundaries of the IT department. Yet, business-managed IT is characterized by a higher degree of responsibility for IT components and tasks in the BUs. Business-managed IT is typically more intentional, controlled, and aligned with organizational strategies, while shadow IT can be more risky.
Is shadow IT a threat?
Yes, shadow IT can also introduce serious security risks to your organization through data leaks, potential compliance violations, and lack of proper resource management.
What are the examples of shadow IT?
Using a cloud-based file-sharing service like Dropbox or Google Drive™ within your organization without formal IT knowledge or oversight is an example of using shadow IT. Imagine an employee needs to collaborate on large files with external partners regularly. Instead of going through the formal IT approval process, this employee signs up for a cloud-based file-sharing service (e.g., Dropbox, Google Drive™) using their personal email account.
What does the term shadow IT mean?
Shadow IT refers to the use of information technology (IT) systems, hardware, software, applications, or services by employees without the explicit approval, oversight, or control of the organization’s IT management. It typically involves employees or departments independently adopting and managing their own technology solutions to meet their specific needs, often bypassing formal IT security protocols.