Unlock Operational Bliss for Your SecOps Team in 4 Simple Steps
The Security Operations (SecOps) team is an essential part of an organization’s overall cybersecurity posture, helping protect valuable and sensitive assets. Cybersecurity threats are evolving rapidly, and SecOps teams are challenged to stay ahead of the curve. How can organizations embrace operational bliss allowing Secops teams to be more efficient, productive, and agile? Let’s discuss four ways to unlock operational bliss for your SecOps team.
1. Streamline Workflows with Automation
One of the powerful security tools available to SecOps teams today is automation. Automating repetitive tasks lets your team focus on higher-level, strategic activities. Here are some ways to leverage automation:
- Incident Response – Implement automated solutions to identify, assess, and remediate threats in real-time. It helps in reducing the time and effort required to handle incidents manually.
- Threat Intelligence – Integrate automated threat intelligence solutions to gather and analyze threat data from various sources. It enables your team to identify and prioritize potential risks more effectively.
- Patch Management – Automate identifying and deploying software patches, ensuring your systems are up-to-date and less vulnerable to attacks.
2. Provide Necessary Tools and Solutions
The right tools and solutions are needed for SecOps teams to achieve the operational efficiency required to meet security challenges today.
- Enhanced Threat Detection – The right tools and solutions provide SecOps teams with real-time monitoring and advanced analytics capabilities, enabling them to quickly identify and respond to potential threats, thus reducing the risk of breaches and minimizing damages
- Streamlined Incident Management – The right tools and solutions allow SecOps teams can focus on higher priority issues, improving efficiency and reducing response times, ultimately strengthening an organization’s security posture.
- Continuous Improvement – Advanced SecOps tools help collect and analyze security data, empowering teams to refine their strategies, optimize resource allocation, and stay ahead of evolving threats, ensuring a proactive and adaptive security approach.
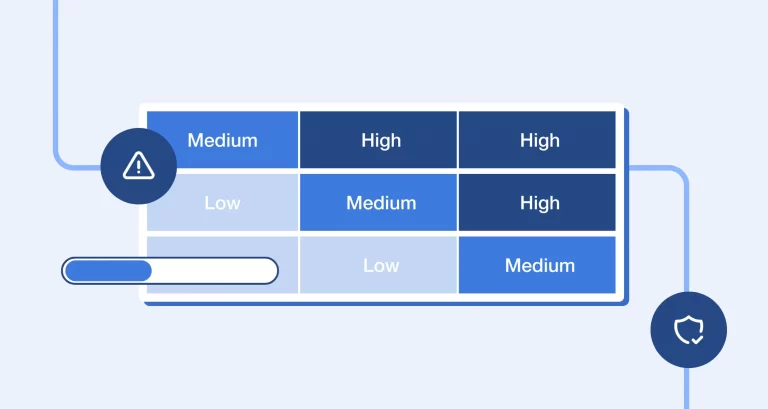
3. Automate Risk Assessments
Proper risk assessments are critical to bolstering an organization’s overall cybersecurity posture. However, manually performing risk assessments is tedious and labor-intensive for SecOps teams. As a result, SecOps operations can benefit from consistent evaluations, optimized resource allocation, and real-time monitoring provided by automated risk assessments.
- Consistent Risk Evaluation – Automation of risk assessments ensures that the analysis is carried out using standardized criteria and methodologies, reducing human error and providing a more accurate understanding of the organization’s risk landscape.
- Time and Resource Optimization – By automating the risk assessment process, SecOps teams can save valuable time and resources that would otherwise be spent on manual evaluations, allowing them to focus on high-priority tasks and incident response.
- Ongoing Monitoring and Updates – Automated risk assessment tools enable continuous monitoring and real-time updates of an organization’s risk profile, allowing SecOps teams to promptly identify and address emerging vulnerabilities and threats, enhancing overall security posture.
4. Use SaaS Tools to Streamline
SecOps teams constantly seek to improve efficiency and bolster their security posture. One approach that has gained traction in recent years is adopting Software-as-a-Service (SaaS) tools to streamline SecOps operations. By leveraging SaaS solutions, organizations can reap several key benefits, including enhanced scalability, reduced implementation time, and simplified maintenance.
- Scalability and Flexibility – SaaS tools offer seamless scalability to adapt to changing SecOps requirements, allowing organizations to easily adjust their security infrastructure as they grow or face new threats without investing in additional hardware or software.
- Reduced Implementation Time – By leveraging cloud-based SaaS solutions, organizations can quickly deploy and integrate new security tools with existing systems, streamlining SecOps operations and reducing the time spent on installation and configuration.
- Simplified Maintenance and Upgrades – SaaS providers handle software updates, patches, and maintenance, ensuring that organizations always have access to the latest security features and improvements while freeing up SecOps teams to focus on core security tasks and incident response.
Wrapping up
Unlocking operational bliss for your SecOps team is a journey that requires ongoing commitment and investment. Streamlining workflows through automation, the right tools and solutions, automated risk assessments, and leveraging SaaS security solutions can empower your team to achieve greater efficiency, productivity, and success. Embrace these four strategies to transform your SecOps team into a well-oiled cybersecurity machine and enhance your organization’s security posture.
To learn more, schedule a demo here.
Spin.AI helps SecOps teams achieve operational efficiency
With many organizations rapidly adopting SaaS solutions for business communications, collaboration, and productivity, protecting critical SaaS environments from cybersecurity threats is a priority. Spin.AI leverages artificial intelligence (AI) and machine learning (ML) to provide robust cybersecurity automation protecting against the following threats:
- Ransomware
- Shadow IT
- Data leak
- Data loss
Spin.AI provides SecOps teams with automated risk assessments and incident response, automatically responding to and remediating ransomware attacks in cloud SaaS environments. To learn more, book a demo here.