Essential Tips for Protecting Company’s Sensitive Data in the Cloud
Leaking or losing sensitive data can have unwanted consequences for your business. We compiled 8 valuable tips for protecting company’s sensitive data.
What is sensitive data and what are the major risks to it?
Sensitive information is the type of data that requires limiting access and protection against exposure. If such data becomes available to certain individuals or the general public, the owner of the data can face damaging events. An example of individual sensitive data is a credit card number or medical information.
Laws identify many types of sensitive data. If we simplify it, we can discern two types of sensitive data:
- Personal information about their clients, partners, or employees.
- Business, financial, or operational data.
Another way to categorize data is by risk level and regulation:
- High-risk: the leak can have severe consequences for a person’s safety or identity.
- Restricted: the disclosure is prohibited by law.
- Confidential: the leak is regulated not by law, but by internal business security policies.
The three main risks for sensitive information are:
- Loss – the result of accidental or premeditated deletion or corruption of the information.
- Leak – the unauthorized access to sensitive information.
- Extortion – the unauthorized copying of sensitive data to an external medium (e.g., data download).
It is essential to remember that the retention of certain types of sensitive data is mandated by the law. Losing other types of sensitive data can cause financial losses and downtime.
Extortion can be caused by leaks (unauthorized access to data), but not necessarily. It can be caused by a ransomware attack, a man-in-the-middle attack or a zero-day attack when a hacker exploits the vulnerability of an app that has authorized access to data.
Data leak doesn’t necessarily result in data extortion (data copying) but can still have negative consequences. For example, a person can access sensitive data about future corporate mergers and use it for insider trading.
Security Tips for Protecting a Company’s Sensitive Data
Understanding the key risks to sensitive data can help you identify the necessary areas for sensitive data protection. Here are the main security tips:
Data Management
Data management is the practice that enables you to categorize your corporate data and outline records containing sensitive information requiring special protection. There are three stages of data management:
- Discover and map data of your organization.
- Categorize data by its sensitivity and identify which users/departments can have access to it (and what type of access).
- Create security policies that you will implement with DLP.
Acquire Data Backup
Third-party data backup can help you recover your sensitive data in case it has been lost. Remember about the 3-2-1 rule. Keep three copies of your data on two different mediums, one of them off-site.
Check out the best-in-class data backup for SaaS environments.
Use Ransomware Protection
Modern ransomware can cause both data extortion and data loss. Unfortunately, most ransomware protection tools wait for the attack to stop and then begin recovery from backup. It can take weeks or even months to restore large data sets stored in SaaS applications due to API limitations.
We suggest acquiring ransomware protection that uses AI to detect the attack and stop it right after it begins.
Employee Training
Employees can become your allies when it comes to data protection. Educating them on the importance of correct file sharing, strong passwords, and social engineering techniques can help them avoid a major incident with sensitive data.
Manage Access
Access management enables you to avoid unauthorized access to your sensitive data by external and internal actors. The following practices will help you prevent outside threats like account hijacks:
- Strong and Unique Passwords
- Regular password change
- Two-factor authentication (2FA)
Document-sharing policies in cloud environments will help you prevent unauthorized access by those who are within your environment.
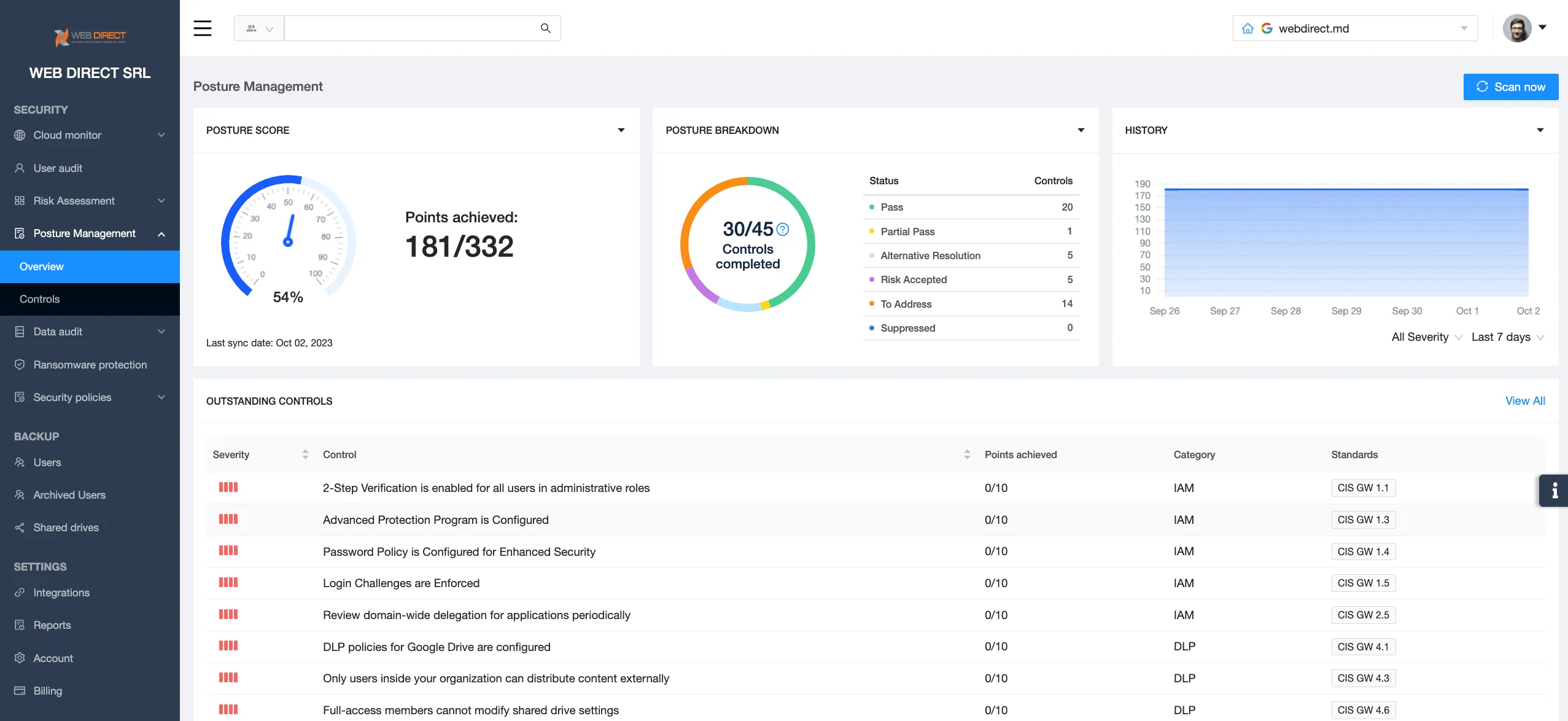
Check the system for misconfigurations
Misconfigurations can often leave vulnerabilities and create entry points for hackers to access your sensitive information. Control of misconfiguration should be regular. Implementing manual control can be hard especially if a company has multiple cloud environments.
We suggest using SSPM tools that detect misconfigurations and even fix some of them automatically.
Use SaaS Application Control
SaaS applications and browser extensions have access to your sensitive data as many employees would use their work account to work in these applications. Using OAuth and granted permissions applications can not only access your sensitive data but also edit it.
To control applications, the IT security team must detect, analyze, and disable them when necessary.
Alternatively, they can use SSPM which automates the discovery, risk assessment, and blocklisting process.
Implement Data Loss Prevention (DLP)
Data Loss Prevention is a functionality within SaaS environments that enables teams to impose security rules and automate their implementation. These security rules govern both data loss and data leak accidents. In other words, they control not only the data deletion but also prevent unauthorized access to sensitive data.
An example of such a rule is to ban the sharing of SSNs in emails or create a copy of a document containing sensitive data when it’s edited or deleted. Get the best Data Loss Protection.
FAQs
What role does Data Loss Prevention (DLP) play in data protection?
Data Loss Prevention helps to prevent sensitive data deletion or unauthorized access to data.
What makes a password strong and how does it protect my data?
A strong password contains numbers, capital letters, and special characters. It must be unique, i.e., qwerty is a bad password just as 12345 or NBA20223. It shouldn’t contain your personal data (e.g., your name, date of birth, place of living, etc.) as this data can easily be found online.
Data Loss Prevention helps to prevent sensitive data deletion or unauthorized access to data.A strong password contains numbers, capital letters, and special characters. It must be unique, i.e., qwerty is a bad password just as 12345 or NBA20223. It shouldn’t contain your personal data (e.g., your name, date of birth, place of living, etc.) as this data can easily be found online.
A strong password contains numbers, capital letters, and special characters. It must be unique, i.e., qwerty is a bad password just as 12345 or NBA20223. It shouldn’t contain your personal data (e.g., your name, date of birth, place of living, etc.) as this data can easily be found online.
Two-factor authentication adds another step in the authentication process. This step requires to use of another medium (usually a mobile phone) that people have with them all the time.
How does Two-Factor Authentication (2FA) enhance security?
Two-factor authentication adds another step in the authentication process. This step requires to use of another medium (usually a mobile phone) that people have with them all the time.
Can using public Wi-Fi networks put my data at risk?
Yes, hackers often hunt in public Wi-Fi networks for users who might have valuable sensitive information.
How can I identify phishing emails and protect my sensitive information?
Phishing emails have several distinctive features:
- Mistakes in email address of the sender (especially in the domain name)
- Grammatical errors.
- Too-good-to-be-true offers.
- Sense of urgency.
- The style of an email is off (e.g., unusual email signature).
- The links in the email lead to fishy websites (the URL is excessively long).
Why should businesses back up data, and how often should we do it?
Businesses must back up data at least every day. In case of data loss, you can easily restore it from a backup.
Why is protecting sensitive data so important in the digital age?
Sensitive data can be used for criminal purposes and severely damage the lives, safety, and well-being of individuals. It can also be damaging to business operations.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Why Google Drive Backups Are Important
Google Drive offers customers a unique blend of robust security features to keep their data...
Evaluating the Best Backup Services: What to Look For and Popular O...
If you’re here right now you’ve probably realized how important it is to backup your...
Brewing Trouble: How a Starbucks Ransomware Attack Poured Cold Wate...
Cybercriminals often carry out attacks around holidays as this helps to ensure the most amount...


