SaaS Security Posture Management (SSPM)
Protect SaaS data with SpinOne SaaS Security Posture Management (SpinSPM)
What is SaaS Security Posture Management (SSPM)?
The growing risks of uncontrolled Shadow IT and cloud configuration calls for a solution that will help companies close these security gaps.
SaaS Security Posture Management (SSPM) refers to the security solutions and tooling needed for automated continuous monitoring and visibility of an organization’s SaaS apps in the cloud SaaS environment.
It helps to minimize cloud misconfigurations and security risks of SaaS apps and provides native security controls to help protect sensitive data housed in cloud services. In addition, it bolsters the security team by providing 24x7x365 monitoring of the environment, quickly detecting security gaps in cloud apps, and allowing SecOps to address security issues effectively or use automated responses to remediate these.
Advantages of an SSPM Platform for Enterprise

Over 80% of organizations have SaaS misconfigurations and risky, third-party apps that lead to immediate security threats.
Solve for risky SaaS security misconfigurations, shadow IT, and shadow AI with SpinSPM – a SaaS Security Posture Management solution that gives you full visibility and automated incident response. You’ll save time, reduce security overhead, and improve your security posture by enforcing compliance across all the apps and extensions that actively expand your attack surface and create serious security gaps across your SaaS ecosystem.
SpinSPM lets you apply strong security controls without adding time and tool management burdens.
Tapping our proprietary database of over 550,000 apps and browser extensions assessed by AI algorithms, SpinSPM is recommended and integrated by Google, recognized as a Strong Performer in the Forrester SSPM Wave report, and listed as and trusted by 1,500+ organizations worldwide.
Related SSPM Solutions to Reduce Browser Risk Management Burdens
Application & Browser Extension Risk Assessment Tools
Award-Winning Solution

2x Recognition by
Global Infosec Awards
- Market Innovator Data Recovery
- Market Leader SaaS/Cloud Security

What Our Users Say About Our SSPM Solution
What Makes SpinSPM Different?
Did you know Spin.AI is the only SSPM solution with both robust risk assessment of browser extensions and apps as well as automated incident response – from a single pane of glass?
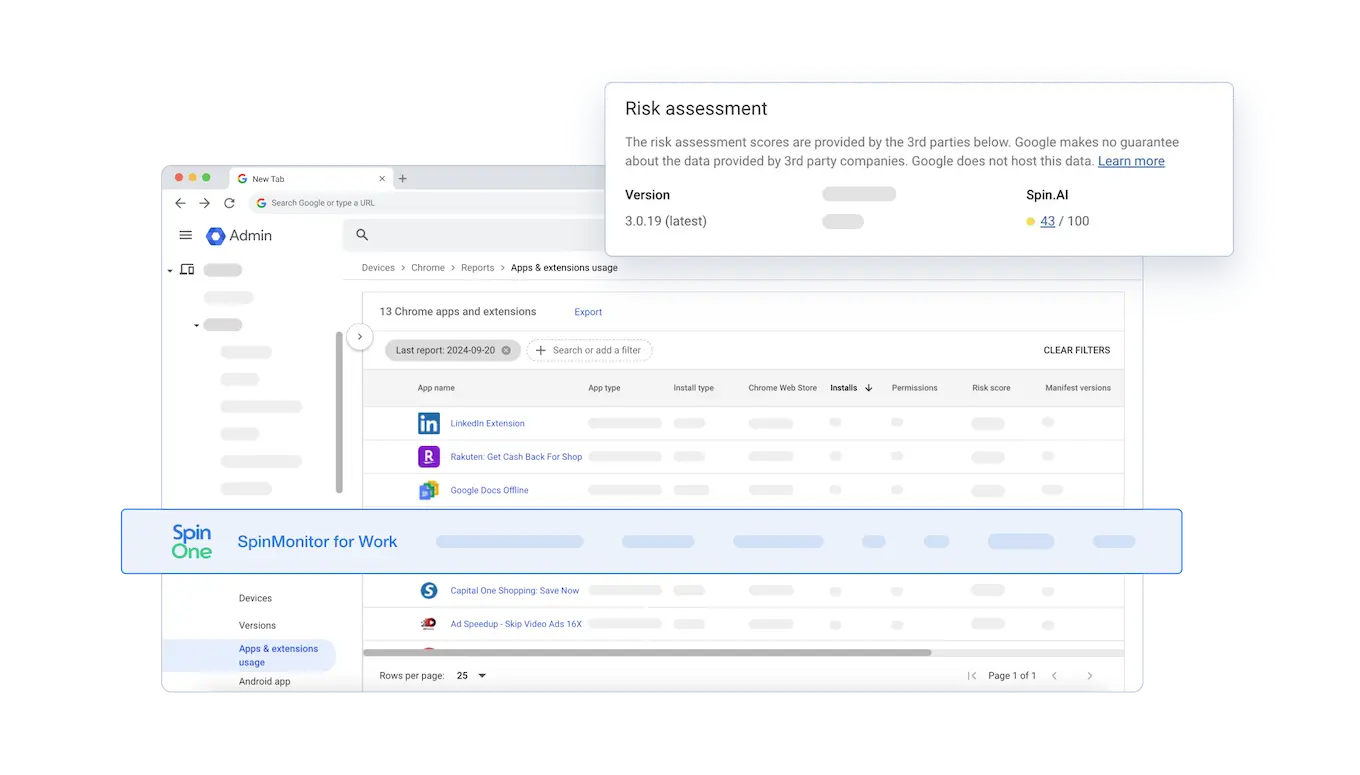
Powerful Assessment Done in Minutes
SpinSPM is the only SSPM solution that gives you in-depth risk assessments for Microsoft Edge and Google Chrome browser extensions. In fact, SpinOne was selected by Google to be integrated into its Console, leading to hundreds of enterprise organizations who now trust Spin.AI to show them all the risks associated with extensions their end-users attempt to install.
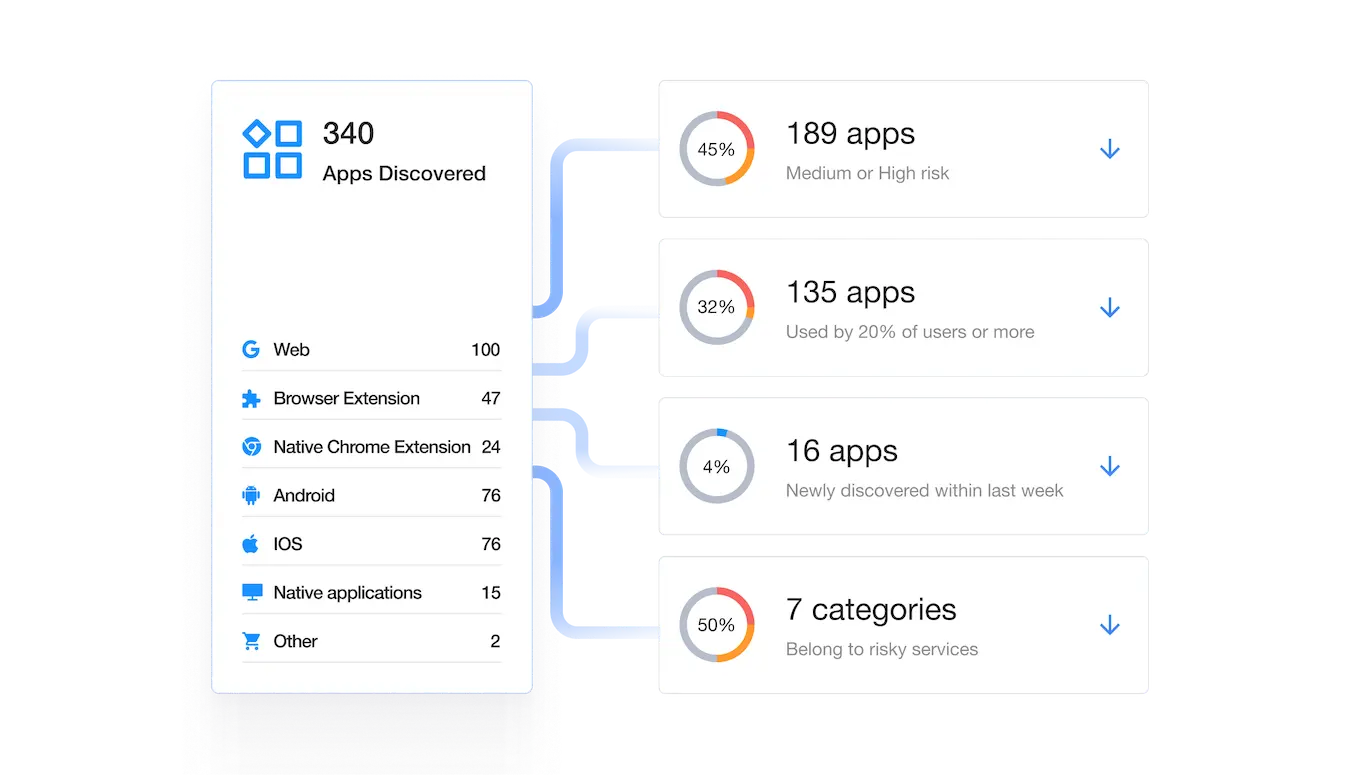
Shadow IT and Third-party App Discovery
SpinSPM has discovered and assessed over 550,000+ OAuth applications and browser extensions using its AI-algorithms, helping organizations reduce risk assessment time from months manually to seconds automatically. Anytime an app or extension is updated, Spin.AI reevaluates its risk levels to prevent malicious and accidental vulnerabilities that would otherwise be very hard to find.
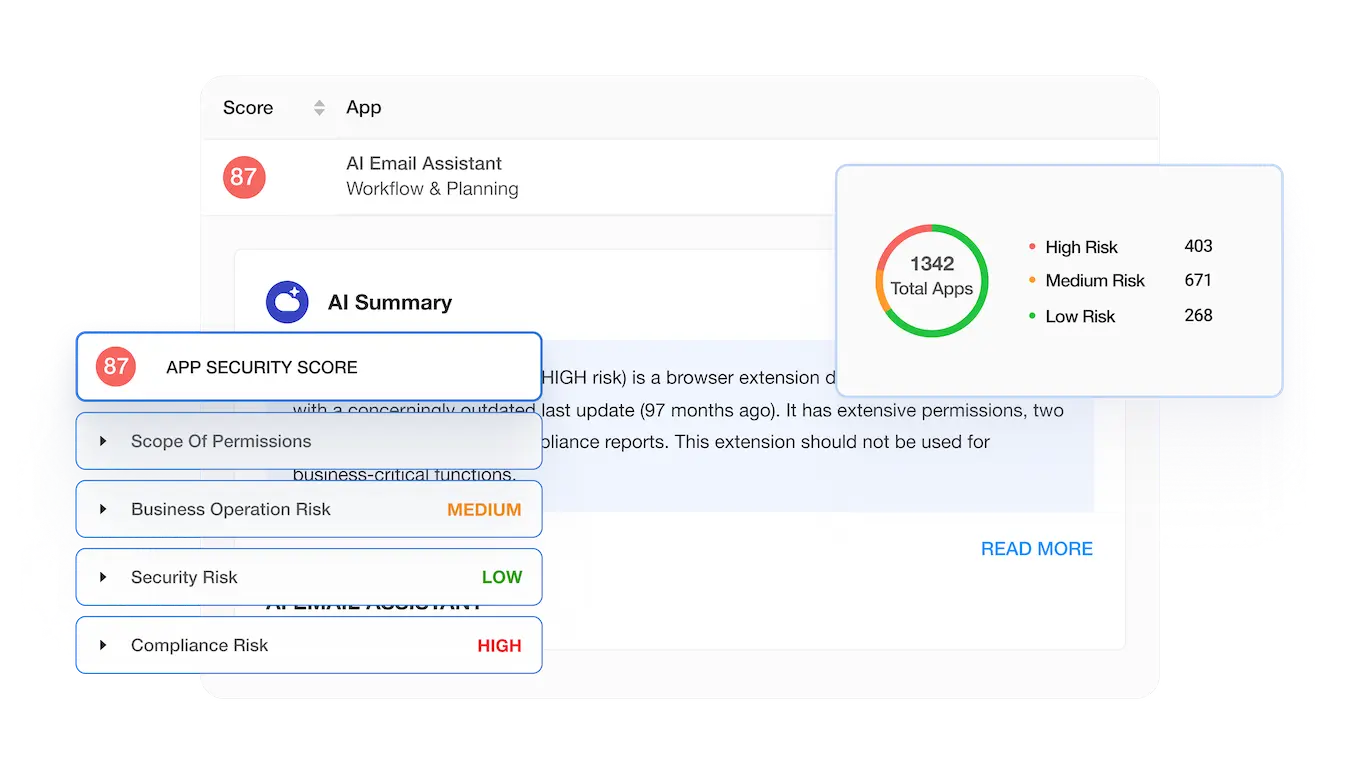
Granular Risk Assessment
SpinOne uses over 15 data points to assess application and extension risks, breaking the assessment down into the following sections: scope of permissions, external communications, business operation risk, security risk, and compliance risk. Based on this data each app receives a security score from 0 to 100 to zero in on the riskiest applications and extensions to facilitate your decision-making process.
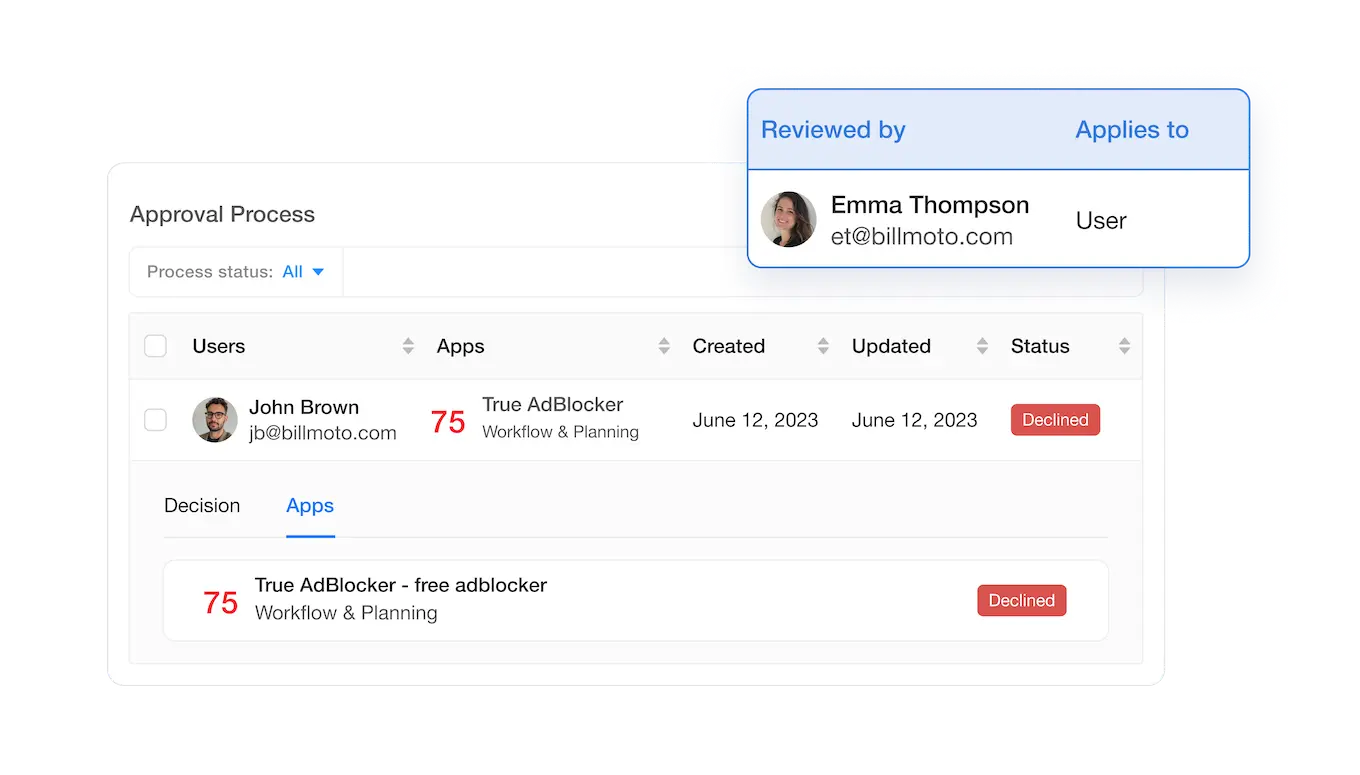
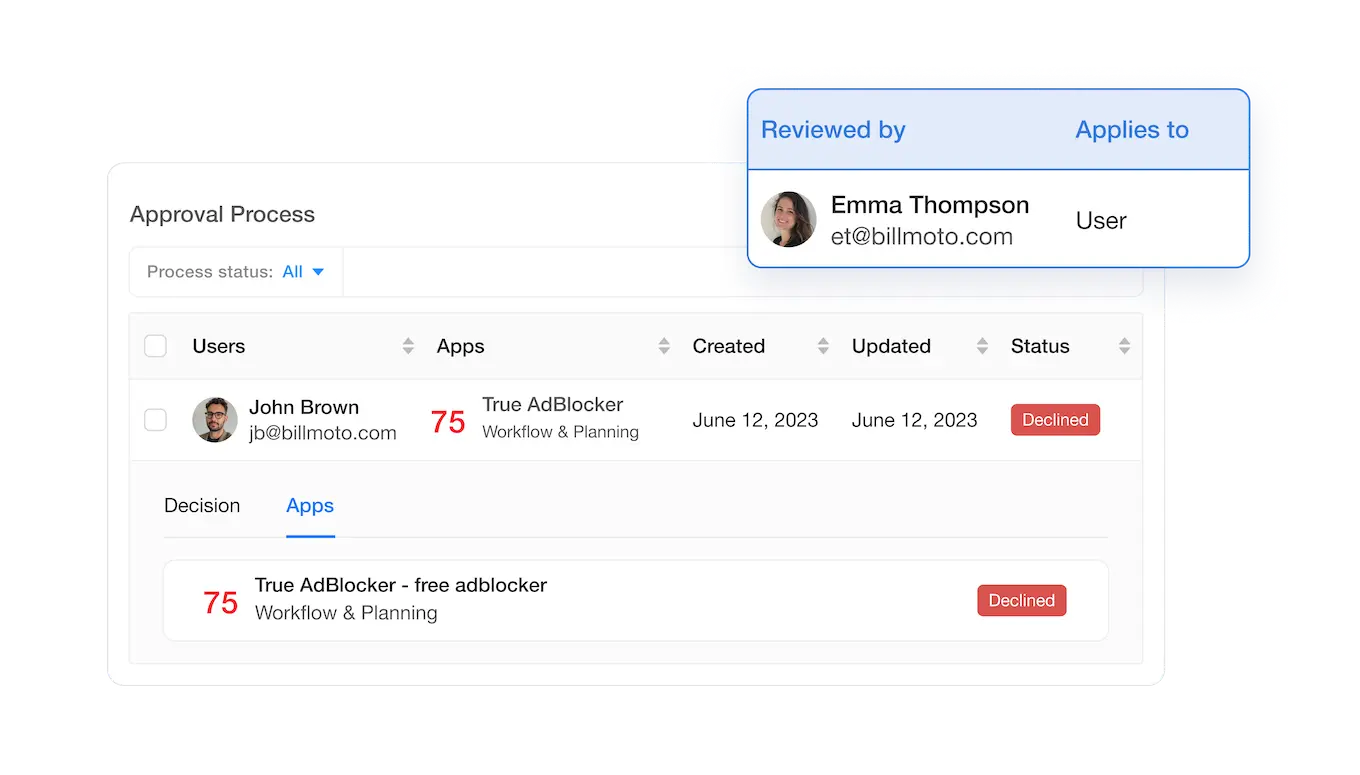
Customizable and Automated Access Management and Incident Response
SpinSPM gives you full control over access management and incident response cases by providing you the ability to customize security responses, allowing you to manage unique use cases. Custom policies can trigger automated incident responses upon detection of any policy violation, reducing the time to mitigate risks. SpinOne also automates the access management and incident response processes through highly configurable policies.
All-in-One SaaS Security Platform
SpinSPM is a solution within SpinOne, the all-in-one SaaS security platform for mission-critical SaaS apps that protects SaaS data for Google Workspace™, Microsoft 365, Salesforce, and Slack. SpinOne provides SSPM, SaaS DLP, SaaS ransomware protection, advanced threat protection, and SaaS backup to for more than 1,500 organizations worldwide to enhance cyber resilience, streamline security operations, and reduce security costs.
AI Compliance and Browser Extension Risks in 2026
AI Compliance and Browser Extension Risks in 2026
Frequently Asked Questions
SpinSPM FAQ’s
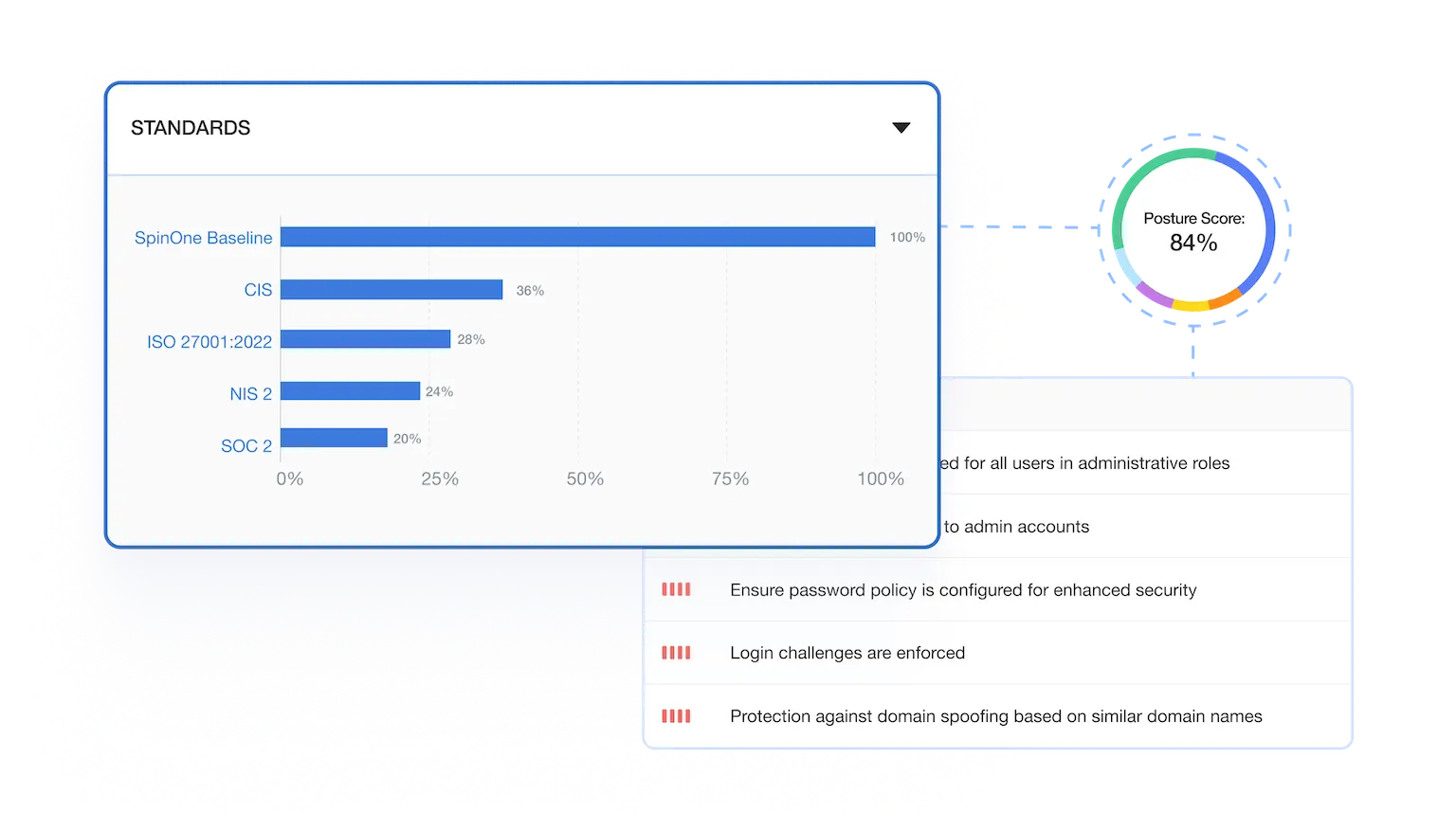
How does SpinSPM ensure security and compliance standards for my data?
SpinSPM helps you operationalize the technical safeguards auditors look for without slowing teams down.
Audited & attested:
Spin.AI is SOC 2 Type II audited and supports enterprise compliance programs (HIPAA, PCI DSS, GDPR, and the Data Privacy Framework).
Read more about our Security and Compliance practices
| Security Control Category | HIPAA Security Rules | PCI DSS v4.0.1 | SOC 2 (Trust Services Criteria) | How SpinOne helps (products) |
| Access control & authentication | Unique user identification, access management, and transmission security to prevent unauthorized access. | Req. 7/8: least privilege, unique IDs, MFA for non‑console access to CDE; strong password policies. | Logical access controls aligned to roles with periodic review. | SPM monitors risky auth settings & abnormal logins; optional SpinOne login + 2FA and ability to disable Google login; DLP to reduce oversharing. (SpinSPM, SpinDLP) |
| Logging, monitoring & audit trails | Audit controls to record and examine activity in systems that contain ePHI. | Req. 10: log & monitor access; automated reviews & real‑time alerts; retain 12 months (90 days immediately available). | CC7 (System operations): detect, log, and respond to security events. | Centralized activity logs & reports; real‑time alerts; SIEM integrations; configurable log retention and daily/periodic review workflows. (SpinOne Platform) |
| Misconfiguration management | Ongoing risk analysis and risk management; adjust controls as risks change. | Req. 2/6: secure configurations & change management/patching. | Establish baselines, monitor, and remediate deviations (change mgmt/system operations). | Detects configuration drift across SaaS; highlights risky settings and orchestrates policy‑based remediation. (SpinSPM) |
How to choose the Right SaaS Security Posture Management (SSPM) Solution for Your Organization?
To choose the right SaaS Security Posture Management (SSPM) solution for your organization, consider the following factors:
- Centralized Platform: Opt for a solution with comprehensive functionality to avoid using multiple tools.
- Integrations: Ensure compatibility with the tools your business already uses.
- Monitoring & Incident Reporting: Look for 24/7 monitoring and effective reporting methods, like email alerts.
- Application Coverage: Confirm how many applications the SSPM detects and how often the database updates.
- Risk Assessment: Evaluate the criteria and scoring method for app risk assessment.
- Access Revoke: A feature to revoke high-risk app access is essential for swift risk mitigation.
- Blocklisting & Allowlisting: Supports a zero-trust approach, preventing shadow IT issues.
- Security Policies: Ensure the SSPM allows configurable security policies based on app risk.
- Employee Request System: Streamlines app acquisition requests for IT management.
- Customization: Look for platform customization to align with your unique security needs.
- Support: Confirm the availability of round-the-clock support.
- Pricing: Assess the value in terms of cost savings, automation, and incident prevention.
What are SSPM Key Features and Capabilities?
The three key features of every SSPM include detection, assessment, allowlisting and blocklisting. Detection is essential as cloud environments usually lack functionality that provides visibility into the OAuth applications that have access to them. Assessment is essential to make informed decisions on whether to keep an application or block it. It helps the security team cut time on manual app risk assessment. Finally, the ability to create allowlists and blocklists can automate even further the process for the team.
What is the difference between SSPM and CASB?
Many people, and even cybersecurity professionals, find it difficult to tell the difference between CASB and SSPM solutions. There are some similarities between them. For example, both are security solutions that are deployed in the cloud and help prevent cyber incidents.
However, CASB differs from SSPM when it comes to application, deployment, timing, and scope. Let’s take a closer look at each of these aspects.
Application: CASBs work with both on-premise and cloud environments, while SSPMs are cloud-only solutions.
Deployment: SSPMs are typically subscription-based, whereas CASBs can be either SaaS or on-premise tools, sometimes requiring additional hardware to operate.
Timing: Unlike SSPMs, CASBs do not identify the security incidents after they take place.
Scope: CASBs mainly manage cloud data access, while SSPMs offer a broader view, identifying vulnerabilities and helping to remediate them across the entire cloud environment.1
How can I see and fix risky SaaS misconfigurations and shadow apps before they cause trouble?
Look for SSPM and DSPM solutions that surface misconfigurations, oversharing, riskyusers, and unsanctioned apps with prioritized remediation, which is built into SpinOne.
How do you evaluate Chrome extensions and OAuth apps at scale?
An AI-powered registry analyzes permissions, behavior, publisher reputation,and data flows to score risk across hundreds of thousands of items in SpinOne.
Can we get visibility into browsing risks across the company?
You receive dashboards and alerts on risky extensions, app permissions, and data access patterns across users and groups using SpinOne.
How does SaaS Security Posture Management (SSPM) work?
SSPM continuously checks your SaaS settings against best practices and compliance frameworks to surface misconfigurations, risky users, shadow IT, and unsanctioned apps, then guides remediation to improve your posture score. You can deploy SSPM quickly across Google Workspace and Microsoft 365 with SpinOne to gain visibility and reduce risk fast.
What is enterprise browser security and why do extensions and OAuth apps matter?
Extensions and OAuth apps can request powerful permissions that access email, files, and calendars, creating a pathway for data leakage or account compromise if they’re risky or trojanized. Enterprise browser security evaluates and controls extension add‐ons at scale—allowlisting trusted tools, blocking high‐risk ones, and assessing over 550,000 items—capabilities offered by Spin.AI.
SSPM FAQ’s
How does SpinSPM help organizations secure their clouds?
While cloud SaaS is ripe with modern tools and technologies empowering businesses, it can equally be filled with security pitfalls using SaaS applications. For example, cloud misconfigurations, risky third-party applications, shadow IT, ransomware, data leakage, and many other threats can jeopardize critical and sensitive data and lead to security breaches. SpinSPM provides the capabilities needed for automated continuous monitoring and visibility of an organization’s SaaS apps in the cloud SaaS environment. It helps to minimize cloud misconfigurations and security risks of SaaS apps and provides native security controls to help protect sensitive data housed in cloud services. In addition, it bolsters the security team by providing 24x7x365 monitoring of the environment, quickly detecting security gaps in cloud apps, and allowing SecOps to address security issues effectively or use automated responses to remediate these.
Does SSPM cover third-party applications as well?
Yes. SSPM helps you inventory and gain visibility of all third-party cloud services, mobile apps, generative AI (GenAI) apps, and SaaS apps that have access to Google Workspace™, Microsoft 365, and Slack and understand who has access to these apps. Unlike other SSPM solutions, SpinSPM goes a step further by also providing visibility into third-party browser extensions.
How do I get started with implementing SSPM for my organization?
Implementing SSPM and understanding SaaS security posture is incredibly important as it helps organizations understand their vulnerabilities and how these can be corrected. An SSPM checklist can help you get started, including these steps:
- Evaluate data that isn’t protected
- Provide visibility to data sharing
- Detect and remediate malicious threats
- Harden SaaS configurations
- Evaluate the risks of SaaS apps
Why Do Enterprises Need SaaS Security Posture Management (SSPM)?
Over 75% of third-party SaaS applications are considered medium or high-risk applications according to our App Risk Report. And nearly 50% of installed extensions are high risk according to our Extension Risk Report. To respond to these SaaS risks, SSPM provides automated visibility and scanning of configurations, settings, and permissions to ensure these are configured according to security and compliance best practices. SSPM automation saves manual hours for SecOps professionals since SSPM can carry out the tedious manual tasks of analyzing configurations and continuously scanning for security and compliance risks.
What is the SpinSPM pricing model?
Please see the pricing page for details on SpinSPM and all our packages.
Does SpinSPM support compliance with industry regulations such as GDPR or HIPAA?
Yes, SpinSPM helps support compliance with GDPR, HIPAA, and other laws, regulations, and standards by offering secure 1x or 3x daily backups, 256-bit AES encryption, automated policy-based controls over data sharing, robust access control, and more.
Can SpinSPM be deployed on-premises, or is it cloud-based only?
SpinSPM is an exclusively SaaS-based solution. It cannot be deployed on-premises.
Does SpinSPM scale with the growth of an organization’s SaaS usage?
Yes, SpinSPM can scale effectively with an organization’s SaaS usage growth. It is designed to handle large and complex SaaS environments, scaling to support additional users, applications, and data volumes as the organization expands. In addition, you can adapt security policies, monitor settings, and ensure compliance measures to suit your organization’s evolving needs.
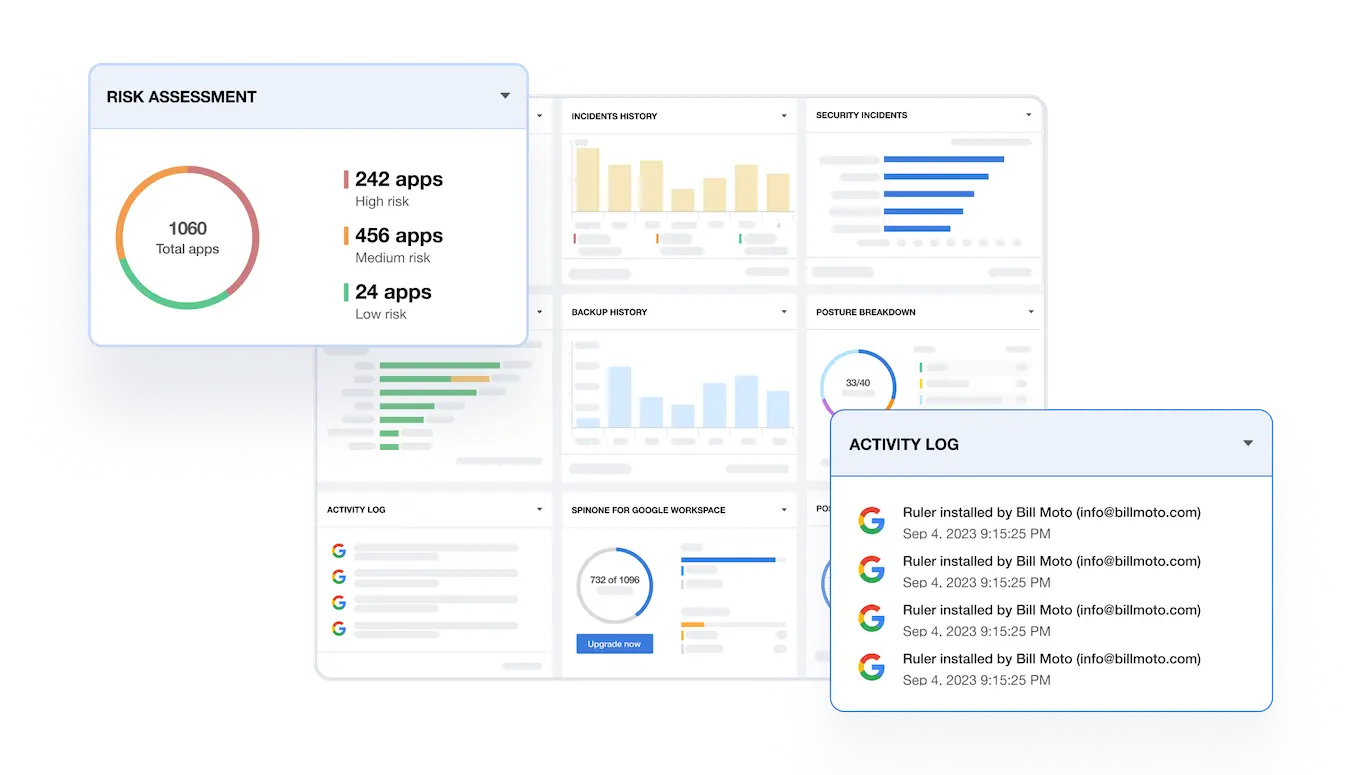
What kind of reporting and analytics does SpinSPM offer?
All essential alerts, reporting, and analytics are accessible on a unified SpinSPM dashboard. Administrators can enable real-time alerts by connecting with Splunk, ServiceNow, Jira, and Slack. Furthermore, SpinSPM offers detailed activity reports on a weekly and monthly basis.
How many third-party applications does SpinSPM detect?
SpinSPM leverages a unique database of over 400,000 apps and browser extensions assessed by our AI algorithms. It can detect a wide range of third-party applications, generative AI (GenAI) apps, and SaaS apps that have OAuth access to the SaaS data we protect in Google Workspace™, Microsoft 365, Slack, and Salesforce.
What are the key benefits of SpinSPM?
SpinSPM enhances your overall security posture, reduces security costs, and improves compliance by:
- reducing the risk of misconfigurations and shadow IT
- providing automated, in-depth risk assessments
- ensuring complete visibility over your SaaS environment
- providing automated incident response
What is the recommended workflow with SpinSPM?
As an administrator, you first install the SpinOne app from the Google or Microsoft Marketplace and then set up necessary security posture management policies to identify misconfigurations, Shadow IT, and other threats. Once configured, SpinSPM initiates automated application risk assessments and provides automated incident responses.
What type of access permissions does SpinSPM require and why?
To start using SpinSPM, an administrator login is required. Admin-only access heightens data security and enables more efficient supervision and administration of the platform’s features
What vendors have integrated with the Spin.AI Chrome Extension Risk Assessment?
















