How to Implement Data Leak Prevention in Microsoft 365
Microsoft 365 Office Suite contains business-critical information. Despite the company’s powerful security measures, data leak incidents happen due to security misconfigurations and a lack of certain features. Learn how to implement Data Leak Prevention in Microsoft 365 and how to empower it with third-party tools.
Understanding Data Leak Prevention (DLP)
Data leak prevention is the umbrella term for processes, policies, and tools to prevent unauthorized access to sensitive information and its theft.
Environments like Microsoft 365 offer great collaboration opportunities for teams that annihilate document duplicates and streamline editing. However, the nature of such collaboration bears hidden risks, as unauthorized individuals and entities can access sensitive data and even steal it.
Understanding these risks and building security systems to minimize them is one of the key challenges for organizations using Microsoft 365 SaaS products.
One more aspect that companies need to consider is the confusion between data leak and data loss prevention. For example, in Microsoft 365, data leak prevention policies exist as part of Data Loss Prevention functionality.
The lack of understanding of the difference between the two can cause severe gaps in your MSO 365 security.
The Importance of Data Leak Prevention for Microsoft 365
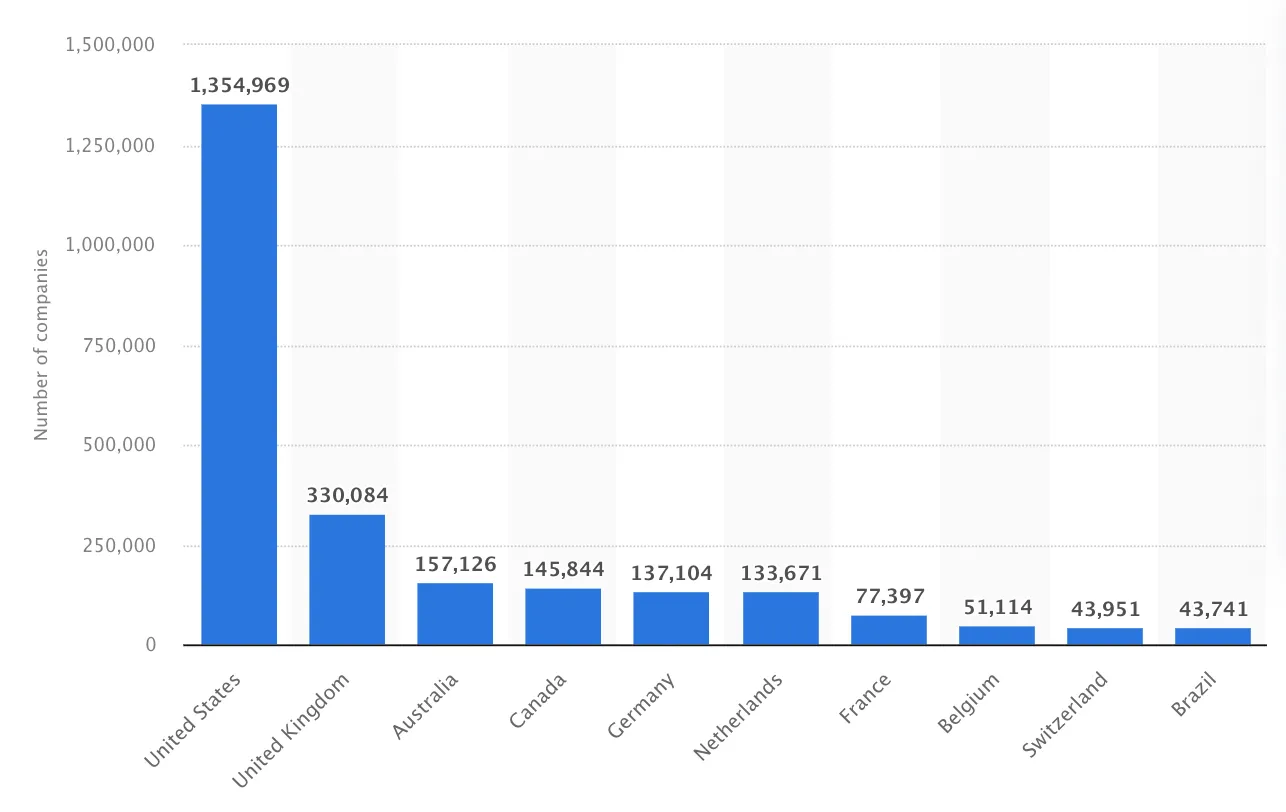
In early 2023, Micorosft 365 controlled 46% of the market share for major office suite technologies worldwide. The rest of the market is occupied almost exclusively by Google Workspace™. 19% of companies using MSO 365 have annual revenue that exceeds $50M. The revenue of 6% of their customers is over $1000M.
This makes Microsoft 365 a desired target for many cyber criminals aiming to profiteer from the exfiltrated data. Despite the developer’s best efforts and ~$1B investment in security annually, data breaches and exfiltrations happen on a regular basis.
Microsoft 365 has a shared responsibility model. It states that the business using MSO 365 is responsible for certain security measures, for example, preventing phishing attacks or controlling access to its data stored in MSO 365 services.
Data Leak Prevention in Microsoft 365
Microsoft 365 has data leak functionality. These are security policies that Admins can configure in its Compliance Center. As mentioned above, the DLP stands for Data Loss Prevention, however, you can configure policies that will help you prevent both loss and leakage.
Microsoft 365 DLP policy capabilities
Let’s take a closer look at the different features of DLP policies offered by Microsoft.
Each DLP policy in MSO 365 has several customizable components:
- Name and description.
- Locations – MSO 365 services where it can be applied (e.g., OneDrive).
- Policy rules that consist of conditions (e.g. Content contains), exceptions, and actions (e.g., restrict access and remove on-premises files).
- Policy mode (run test, turn off, remain off).
The DLP policies have multiple templates with different types of sensitive data. They are conveniently organized by:
- categories (e.g., medical),
- country,
- law/regulation (e.g., HIPAA).
You can edit the condition of each template to fit your organization’s security policies. You can also create custom rules.
How to implement data leak prevention in Microsoft 365
Implementing Data Leak Prevention in Microsoft 365 requires diligent planning, careful setup, close monitoring, and subsequent tuning. We suggest 7 simple steps:
- Catalog data and identify sensitive information.
- Define DLP policy objectives.
- Assign DLP responsibilities to the team.
- Configure policies in Microsoft 365 Security & Compliance Center.
- Inform your organization about the policies.
- Monitor policy implementation and possible data leak incidents.
- Fine-tune policies for minimal false positives.
- Add new data leak prevention policies when necessary.
MSO 365 Data Leak Prevention limitations
The key limitation of Data Leak Prevention in Microsoft 365 is that it is not available in all subscriptions. Below, you can see the list of subscriptions that have DLP for files and emails:
- Microsoft 365 E3
- Microsoft 365 E5
- Office 365 E3
- Office 365 E5
- Microsoft 365 F5 + Compliance
Additionally, the following subscriptions have DLP for Teams chat:
- Microsoft 365 E5
- Office 365 E5
- Microsoft 365 F5 + Compliance
Other limitations include the lack of control of the following risky events that can lead to data leak:
- OAuth applications
- Misconfigurations
- Ransomware
Finally, Microsoft 365 doesn’t provide visibility into abnormal behavior of data and users that can signify data leaks (for example, mass download of OneDrive files, or a suspicious login).
Learn how to implement data leak prevention in Google Workspace™.
Integrating third-party tools for enhanced DLP capabilities
To fill the gaps in Microsoft 365 data leak prevention, we suggest using third-party tools like SpinOne. These solutions were specifically created to help companies detect and control cyber incidents that lie within their sphere of responsibilities under the shared responsibility model.
SpinOne data leak prevention capabilities include:
- Ransomware protection
- DLP policies that MSO 365 lacks
- Abnormal user behavior monitoring
- Abnormal data behavior monitoring
- Application detection, risk assessment, and control
- Misconfiguration detection and remediation
Get better Microsoft 365 data leak prevention with SpinOne.
FAQs
Why should my organization consider implementing DLP for Microsoft 365?
Consider implementing Microsoft 365 Data Leak Prevention (DLP) to detect and prevent the leakage of sensitive data, maintain compliance requirements, minimize human error, and ensure overall data protection. Data leakage is costly due to fines and reputational damages, while an advanced DLP solution helps reduce financial and reputational risks and position you as a reliable business partner or service provider. The benefits of Microsoft 365 Data Leak Prevention (DLP) start with the ability to classify and monitor your data and include improving overall visibility and control over the sensitive data you handle. Relying on antivirus software, AI, and machine learning, Microsoft DLP can also automate data classification, detect and block suspicious activity, maintain regulatory compliance, and monitor data access and usage.
How do I begin the process of implementing DLP for Microsoft 365?
The process of implementing the Microsoft 365 Data Leak Prevention (DLP) should start with a planning process that would include:
- identifying stakeholders (these may include regulatory and compliance officers, security and compliance officers, business users, or anyone involved in sensitive data management.)
- describing the categories of sensitive information to protect (you can either choose financial information, medical and health information, personal information or a combination of those.)
setting goals for your policy (e.g. regulator compliance, enhancing security practices, etc.)
What are the key steps involved in implementing DLP for Microsoft 365?
The key steps in implementing Microsoft 365 Data Leak Prevention (DLP) include:
- Developing a DLP plan that would include stakeholders, categories of sensitive information to protect, as well as the main goals and strategies for your policy.
- Designing a DLP policy by choosing what you want to monitor and when, the conditions that must be matched for a policy, and the action to take when the policy conditions are met.
- Mapping your existing business needs to policy configurations.
- Creating and deploying data loss prevention policies by using either predefined or custom scenrios.
- Implementing, monitoring, and investigating your DLP alerts.
Can I customize DLP policies to suit my organization’s specific needs?
Sure, you can customize your Microsoft 365 Data Leak Prevention (DLP) policy to establish actions, rules, and conditions that can help meet the specific needs of your organization, and which may not be covered in one of your DLP templates that already exist. For this, go to Admin Center > Compliance management > Data loss prevention. Below the list of existing policies click Add + icon, and select New custom policy. Complete the Custom policy page and click Save. Now you have the policy added to the list of all policies that you have configured.
What types of sensitive data can I protect using Microsoft 365 DLP?
Microsoft 365 Data Leak Prevention (DLP) policies can be applied to the following categories of sensitive data,
- Financial information including credit card number, SWIFT code, bank account number, international bank account number (IBAN), Individual Taxpayer Identification Number (ITIN), U.S. social security number (SSN).
- Medical and health information such as insurance number, health service number, international classification of disease, etc.
- Privacy data that include but are not limited to the full names, driver’s license number, physical address, bank account number, and social security number.
Note that the specific sensitive information types in each category are defined by the laws, regulations, and standards (such as GDPR, PCI DSS, HIPAA, GLBA) relevant to countries/regions (Australia, Canada, Japan, Israel, Saudi Arabia, the UK, the US, the EU, and other countries) where Microsoft DLP can be applied.
Do I need technical expertise to implement DLP in Microsoft 365?
Implementing Microsoft 365 Data Leak Prevention (DLP) can vary in complexity depending on your organization’s needs and the level of control you want to have over your data. For instance, Microsoft offers out-of-the-box DLP policies that can be applied to common data protection scenarios and implemented without extensive technical expertise.
However, if you have more specific or complex data protection requirements, and need to integrate DLP with other security solutions, technical expertise is highly recommended. A specific DLP expertise is also reasonable when your organization needs to adhere to specific compliance standards (HIPAA, GDPR, etc.)