How does Data Leak Prevention (DLP) work
Data leaks can have serious legal, financial, and reputation implications for your business. To minimize the risks associated with data leaks, IT security professionals use various DLP tools for on-prem and cloud environments. How does Data Leak Prevention (DLP) work? What is the best DLP for the cloud environment? Learn the answers to these questions in our blog.
Understanding Data Leak and DLP Solutions
In literature dedicated to IT security, data leak often refers to the exposure of sensitive data to unauthorized people. However, a number of experts discern between data leaks and data exfiltration.
The difference between the two lies within the copying. In cases of a data leak, unauthorized people simply access sensitive data and “read” it. Meanwhile, data exfiltration also includes copying the accessed data to the external drive.
In most cases, this division seems to be unnecessarily complicated. All the more, when a person perceives the sensitive data they technically copy this information to their memory. And they then can even disseminate such information.
That’s why most experts simply use the term data leak to refer to both data exposure and copying to external storage.
The confusion with the terminology doesn’t end here. Many DLP solutions that focus predominantly on preventing data leaks are actually labeled Data Loss Prevention rather than Data Leak Prevention.
Now, many processes in IT systems aiming to prevent data leaks also prevent data loss and vice versa. However, they are not identical. For example, controlling access to the system and data protects the information from both loss and leak. However, features like data retention and backup serve solely the purpose of data loss prevention.
In this article, we will exclusively cover Data Leak Prevention tools with a specific focus on cloud environments.
Data Leak in Cloud Environments
To understand how Data Leak Prevention works in the cloud we need first to outline the ways data can be leaked in these environments.
- Incorrect file sharing
This is one of the most widespread reasons for data leaks in the cloud. Several biggest data leaks in history included terabytes of data contained in files that were shared with anyone with a link.
- Account hijack.
Account hijack is yet another widespread reason for data exposure to unauthorized people. Hackers are actively looking for ways to acquire credentials and gain access to cloud environments. And they often succeed.
- Ransomware
The growing popularity of double extortion or even triple extortion makes ransomware one of the leading reasons for data leaks globally.
- Zero-day-attack
Finding and exploiting application vulnerabilities is also on the rise. Many OAuth applications have unlimited access to cloud environments and data stored within. Using them to access this data can lead to data leaks.
- Person-in-the-middle attack
Sometimes, employees of the organization decide to use their access to cloud environments to steal corporate information.
- Social engineering.
Phishing emails requesting to send credit card information remain popular. In particular, hackers use CEO fraud and spear phishing techniques to make sure they get the necessary information.
- Misconfigurations
Last but not least, the mistakes of cloud administrators in configuring the cloud security accordingly, can also lead to data leaks (e.g., banning external sharing).
- Improper employee leave
In many cases, employees still have access to their work account weeks or even months after they leave the company. It creates an opportunity for them to steal.
How does Data Leak Prevention (DLP) work in Cloud
In the previous section, we listed the ways data leak incidents can occur in cloud environments. DLP solutions do not address all of them. For example, they do not protect against ransomware, zero-day attacks, or misconfiguration. You’ll need separate tools that provide ransomware protection, app risk assessment, and misconfiguration detection control. Alternatively, you can acquire the SpinOne platform that encompasses DLP functionality with all the above-listed features and provides you a comprehensive protection of your cloud environments.
Learn the best Data Leak Prevention practices
Let’s now take a look at the core features of DLP solutions that help them prevent data leaks. We can divide all these features into two major categories:
- Monitoring and control
- Policies
Monitoring and control features of DLP
Monitoring and control features provide visibility into the cloud, its vulnerabilities, as well as the potentially dangerous incidents that take place within the cloud. They also give the necessary controls for the Admins to take necessary actions.
Sharing control
This feature provides visibility into the sharing settings of every file and folder within the cloud environment. Some tools like SpinOne also enable Admins to change sharing permissions (e.g., from anyone with a link to anyone in the organization to a set number of users).
DLPs also enable administrators to take ownership of a file. This feature is especially useful if an employee has been acting suspiciously online or if they’ve left the company but still have access to their account.
Sensitive data sharing via email
This feature helps find out and control when people send sensitive information (e.g., CCN) inside or outside of the organization. It might signify that they have malicious intentions or have fallen a victim to the social engineering attack.
Abnormal user behavior
Abnormal user behavior implies abnormal logins (outside working hours or regions). It can signify that a hacker has taken over the account and is currently trying to take malicious actions against the company.
Abnormal data behavior
When talking about abnormal data behavior, we mostly mean mass downloads. Employees usually do not download all the files and folders on a drive at once. Such activity might signify the malicious intention to steal data from the company either by an employee or a hacker.
DLPs detect and report mass downloads to the Administrators.
Security Policies features of DLP
It is hard for Admins to constantly monitor cloud environments for potential data leak incidents, especially if an organization has hundreds of employees and doesn’t have enough Admins. That’s when security policies come in handy.
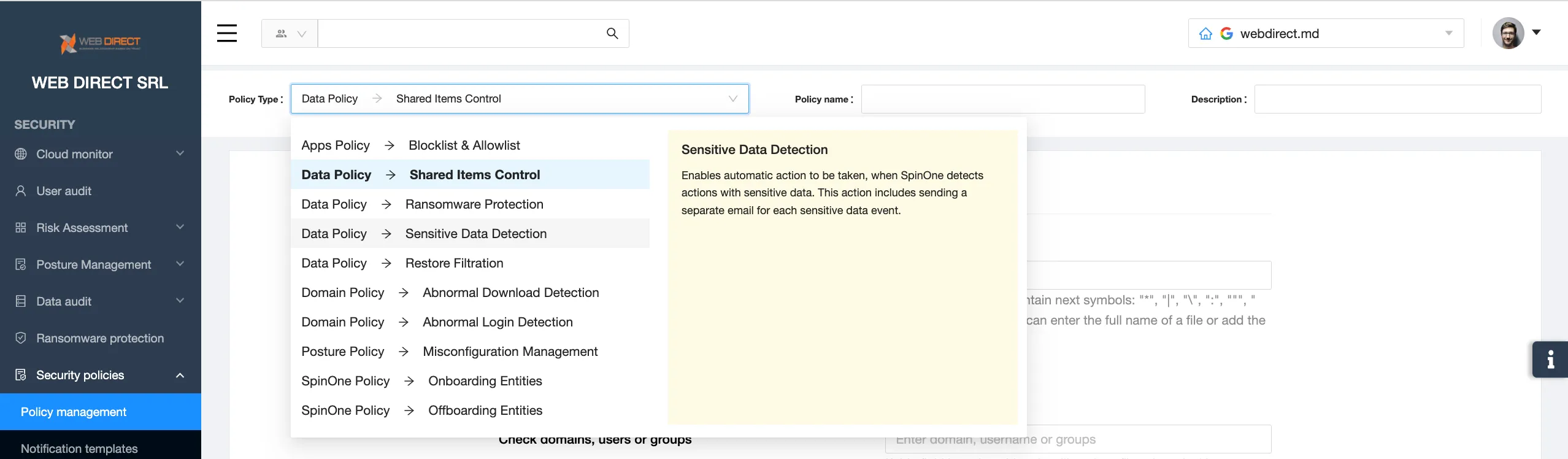
These features enable Admins to automate the control of data leak incidents like incorrect sharing, abnormal login, or abnormal downloads.
Security policies enable Admins to create an algorithm of actions that the DLP should take in case of an incident. For example, you can set up to transfer ownership of a file with sensitive data in case it’s shared outside the organization.
FAQs
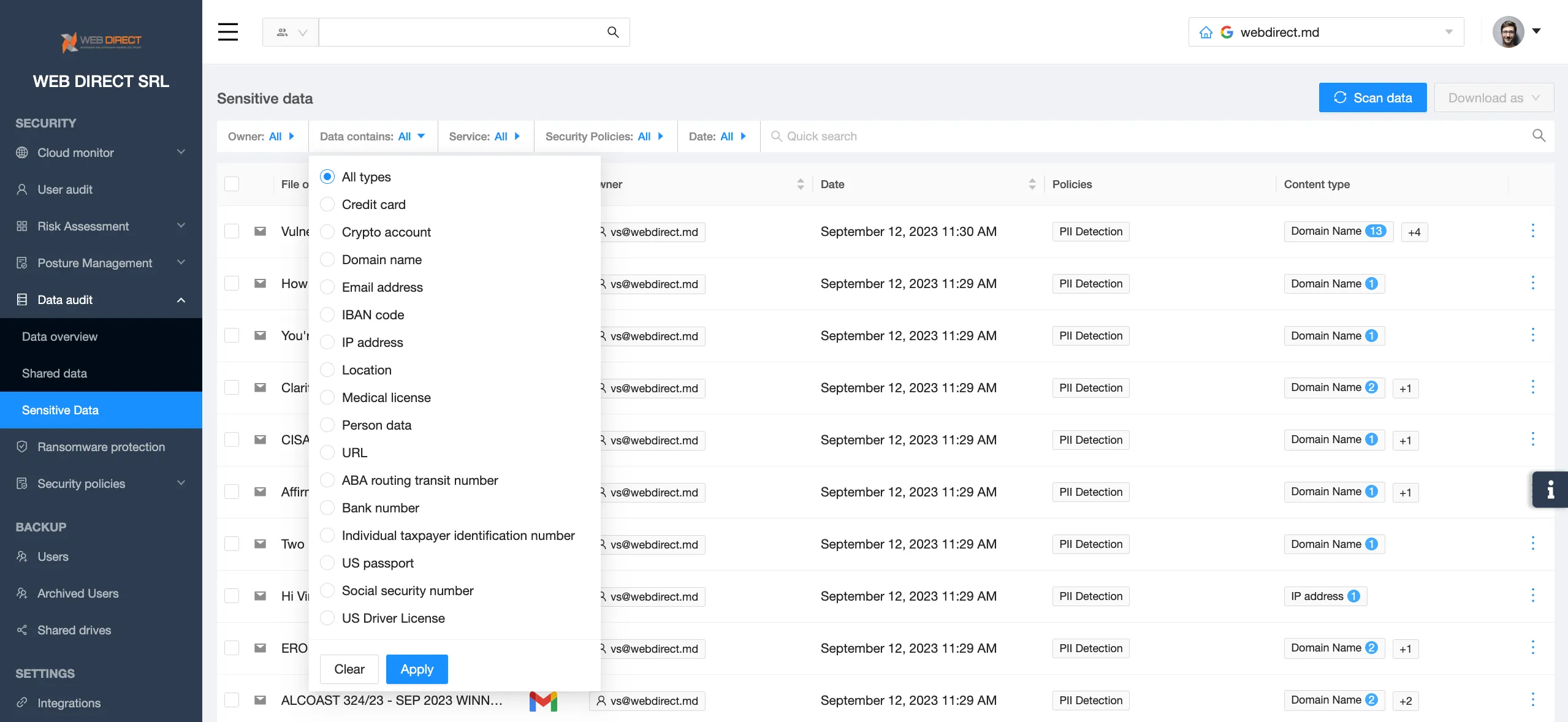
How do DLP solutions identify sensitive data?
DLP solutions identify sensitive data by its content (default settings) or by keywords that admins set up.
Can DLP solutions monitor real-time data transactions?
Yes, DLP solutions monitor real-time data transactions. In this way, they guarantee timely leak prevention.
What actions can DLP take when a potential data leak is detected?
They can stop the activity (e.g., stop the email sending) and/or notify the admins and other IT security employees.
How does a DLP solution integrate with other security tools?
Many security tools have an inbuilt DLP solution. Some DLP solutions can be integrated into “foreign” security tools.