Rise of Cyber Attacks on Education Sector: Reasons, Methods and Protection Tips
Over the past year, we’ve seen a surge in cyber attacks on education sector. This article overviews the main reasons behind it, methods of attacks, and ways to protect against them.
There is seemingly no end to cybersecurity concerns across all public and private business sectors. Arguably, the primary cybersecurity threat today for most organizations is ransomware. Ransomware is a growing threat facing organizations worldwide. Attackers often capitalize on unpatched or zero-day vulnerabilities, security flaws, weak passwords, and many other attack vectors to launch ransomware attacks.
There is essentially no business or business sector that is out of the sight of attackers. Unfortunately, education institutions are not immune to these attacks and are often poorly equipped to deal with a major ransomware attack affecting critical systems. Recently, ransomware attacks have targeted educational institutions, leaving essential data held for ransom.
Recent cyber attacks on education sector
At the beginning of September, Los Angeles Unified (LAUSD), the 2nd largest school district in the United States, was hit with a ransomware attack targeting critical infrastructure systems and data. The school has over 640,000 students enrolled from kindergarten through 12th grade.
Hackers disrupted access to LAUSD systems, including email servers. A few hours after the incident occurred over the weekend, the school announced it was a ransomware attack. The White House helped deliver a rapid response to the cybersecurity incident by bringing together the Department of Education, the FBI, and the Department of Homeland Security. In addition, the school district used Twitter to announce details regarding the cyberattack.
The Vice Society ransomware group was responsible for the attack on the LAUSD school district. The group claimed to have stolen some 500 GB of data from the LAUSD network before encrypting the data with ransomware.
Bleeping Computer reported they made contact with a representative of the group. The representative confirmed the 500 GB of stolen data. However, the representative refused to provide proof of the stolen data until they had published the data to their leak site.
FBI and CISA warn of increased attacks on school districts
On September 6, 2022, the Cybersecurity & Infrastructure Security Agency (CISA) released a joint cybersecurity advisory with the Federal Bureau of Investigation (FBI) warning of ransomware attacks associated with Vice Society threat actors. The advisory noted the Vice Society group was disproportionately targeting the education sector with ransomware attacks.
The advisory noted that K-12 institutions had been frequent targets of ransomware attacks, impacting network and data access, causing or disrupting school days, and leading to the leaking of sensitive data of students, faculty, and staff.
The joint consortium of FBI, CISA, and the MS-ISAC see strong evidence that ransomware attacks on school districts may increase in the 2022-2023 school year. Often, K-12 school districts have limited cybersecurity resources and capabilities to thwart attacks. These are often the most vulnerable to these types of attacks.
Educational organizations are especially lucrative for cybercriminals since they possess large amounts of sensitive student data that can be extremely valuable on the dark web.
How Vice Society deploys ransomware
Like many other ransomware groups, Vice Society’s primary method of operation is to break into networks, leak data, and extort victim organizations. They typically use readily available ransomware variants, such as Hello Kitty, Five Hands, and Zeppelin.
They use common attack vectors when targeting education institutions, such as obtaining and using compromised credentials, exploiting remote access systems, or forward-facing applications connected to the Internet. Like other attackers, they infiltrate the network and move laterally across the network to see what resources are available.
Before launching a ransomware attack, they exfiltrate data to carry out the double extortion tactic. Double extortion allows a ransomware group not only to hold data hostage but also to extort victims to prevent sensitive data from being leaked.
They are also known to exploit vulnerabilities, such as the recent PrintNightmare vulnerability (CVE-2021-1675). Any other unpatched vulnerabilities across the network are likely to be exploited to compromise critical resources.
The rise in ransomware cyber attacks on education sector
Ransomware is a plague that continues to prove to be challenging for businesses and their cybersecurity defenses. Cybercriminals use a wide range of attack vectors to launch ransomware attacks. Thus, organizations must remain vigilant to these and bolster their cybersecurity defenses accordingly. What are the primary ways that ransomware gangs are launching attacks?
These include:
- Compromising external remote access solutions
- Targeting vulnerabilities
- Phishing emails
- Malicious websites
- Supply chain attacks
1. Compromising remote access solutions
Remote access solutions have exploded in their use and popularity among organizations today. With the onset of the global pandemic in early 2020, organizations scrambled to provide remote employees access to critical services, applications, and collaboration and communication tools.
Many businesses shifted to quick and easy remote access solutions, such as exposing an RDP server to the Internet or using traditional VPN technologies. Unfortunately, many of these were not architected with security in mind. Instead, businesses tried to get something up quickly and easily.
Improperly secured remote access solutions are attackers’ primary means to compromise critical networks, launch ransomware attacks, and leak data. According to Group IB’s Ransomware Uncovered 2021-2022 report, attacks on external remote services were the number one attack vector for ransomware groups.
Remote Desktop Protocol (RDP) servers are among the favorite remote access solutions hackers like to attack. Unfortunately, RDP can be riddled with vulnerabilities, especially on unpatched Windows Servers. In addition, weak passwords further weaken the solution’s security, and many companies are still not using multi-factor authentication. As a result, attackers often brute force attack RDP servers to easily find known weak user account passwords.
Not surprisingly, it often only takes minutes for new RDP servers to be “found” on the Internet and start receiving brute force “alphabet-style” attacks where attackers cycle through common usernames and known compromised passwords.
VPN technologies are often no better. The major ransomware attack on Colonial Pipeline is a classic example of how extensive and damaging compromised remote access credentials are. Attackers used compromised VPN credentials as part of a breach credentials list published on the dark web. The account was not secured with multi-factor authentication. It allowed hackers to launch an attack on Colonial, leading to the shutdown of over 5500 miles of critical pipeline and fuel shortages for weeks.
2. Phishing emails
Email is one of the most common attack vectors for ransomware gangs looking to hold critical data hostage. Phishing emails masquerade as legitimate or official communications from vendors or other reputable companies. Attackers often use official logos, fonts, and other characteristics of corporate branding to make phishing emails appear as legitimate as possible.
“Click-happy” employees often click embedded links in phishing emails without scrutinizing the source. The embedded link is most likely a malicious link that downloads a remote access bot or ransomware. Bots are a crucial piece of the overall compromise framework attackers use to gain a foothold in the environment.
Bots are malicious software that allows attackers to carry out post-exploitation activities, including loading other malicious tools like Cobalt Strike. New bot frameworks are being used to help curtail the detection rate of these from security software. Cybersecurity researchers have observed certain bots such as Trickbot, BazarLoader, and IcedID pushing specific malicious remote access tools like DarkVNC.
Bots come heavily into play in today’s phishing activities. One distribution technique associated with the Emotet bot contained links to fake Google Drive™ pages. When the unsuspecting end-user attempts to preview the document, they are presented with a dialog requesting them to preview PDF files. The victim was asked to install a seemingly harmless Adobe PDF component when clicking the preview prompt. When they do, it downloads and installs the malicious AppxBundle used to install Emotet.
Using sophisticated phishing and vishing campaigns, attackers distributed the BazarLoader bot by sending SPAM emails to the victim, noting certain paid subscriptions that could be canceled by phone. Once the victim is on the phone, attackers direct them to a malicious website and have them download and open a weaponized document. Once the document is opened, it loads BazarLoader.
Attackers increasingly use public cloud services and storage locations to store malicious resources, including malicious files and documents. Malicious activities are increasingly intertwined with cloud Software-as-a-Service (SaaS) environments.
3. Targeting vulnerabilities
Ransomware groups are increasingly weaponizing vulnerabilities as part of their arsenal to launch attacks. As a result, unpatched and zero-day vulnerabilities pose a significant threat to organizations in their efforts to secure critical data. In addition, businesses with a lackadaisical approach to patching can easily find themselves missing critical patches with exploits in the wild.
It is not a good position to be in as attackers increasingly use vulnerabilities and capitalize on these for exploits. Furthermore, zero-day vulnerabilities are even more challenging to protect against since they have no patch available from the software vendor. Attackers can rush to use exploit code before software vendors can release patches to remediate the issue.
REvil affiliates were able to use a zero-day vulnerability to attack thousands of Kaseya customers by exploiting a vulnerability in the Kaseya VSA server. Additionally, Clop ransomware developers exploited zero-day vulnerabilities in Accellion’s legacy File Transfer Appliance (FTA) and were able to deploy a web shell.
Note the following vulnerabilities identified in 2021 and that have been used and exploited by ransomware groups to target businesses:
- CVE-2021-20016 (SonicWall SMA100 SSL VPN)
- CVE-2021-26084 (Atlassian Confluence)
- CVE-2021-26855 (Microsoft Exchange)
- CVE-2021-27101, CVE-2021-27102, CVE-2021-27103, and CVE-2021-27104 (Accellion FTA)
- CVE-2021-30116 (Kaseya VSA)
- CVE-2021-34473, CVE-2021-34523, and CVE-2021-31207 (Microsoft Exchange)
- CVE-2021-35211 (SolarWinds)
Organizations, including those in the education industry, need robust patching regimens to help remediate vulnerabilities across the board, including third-party software.
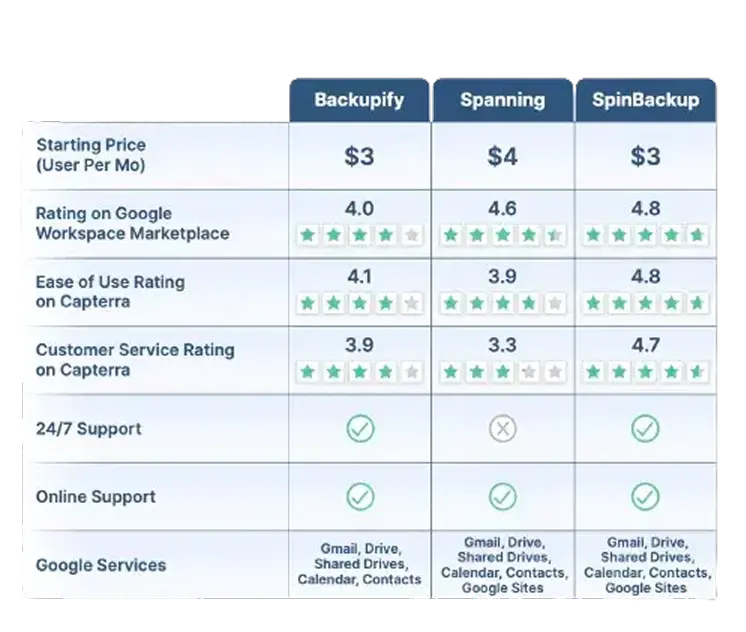
Google Workspace™ Backup Solution Comparison Table
SpinBackup stands out as a comprehensive backup solution for Google Workspace™ compared to competitors like Backupify, and Spanning. We offer a fast onboarding process (under an hour), advanced recovery features like granular and on-demand restoration, and robust security. Read More
Robust security features include:
- Ransomware protection
- Risk assessment of third-party apps
- Misconfiguration management
SpinBackup also supports multiple cloud providers (GCP, Azure, AWS) and compliance with GDPR, SOC 2, HIPAA, PCI DSS, and ISO 27001. With competitive pricing ($3/user per month) and high user ratings (4.8/5 for ease of use on Capterra), we provide a well-rounded and secure data protection solution for businesses.
Read Less*Contact Us for current pricing.
4. Malicious websites
Malicious websites are another favorite of attackers. Shady websites can carry out drive-by attacks, execute malicious code on the victim’s computer, or take advantage of unpatched software vulnerabilities of software installed on the endpoint.
Malicious websites can also entice users to download seemingly legitimate files that contain malicious code. Other sites may redirect users to websites using scare tactics. These may display messages about a user’s computer being infected and force downloads of “utilities” to clean the computer or protect them from further infection. In actuality, these are malicious. Educational institutions have a wide range of users legitimately browsing the Internet, including students, faculty, and staff. It emphasizes the need for strong filtering, segregation of critical services, and endpoint protection.
5. Supply chain attacks
Supply chain attacks are growing more common and sophisticated. For example, the infamous SolarWinds attack, discovered at the end of 2020, is one of the most sophisticated and intricate supply chain attacks in modern history. A Russian intelligence group used the routine software update process on SolarWind’s own servers to push out a malicious code release infecting SolarWinds Orion software.
After aiding in investigating the SolarWinds attack, Microsoft estimated that more than 1000 engineers were involved in creating and carrying out the supply chain attack. It helps to show that attackers are willing to go to extraordinary lengths to carry out attacks on critical business data, services, and applications.
Many educational institutions use third-party software solutions for various needs in their environments. These need to remain vigilant to third-party vendors and their security practices. Additionally, they need to have the necessary security layers to help contain breach events if and when these happen.
How Educational Institutions can protect cloud assets
Protecting cloud assets is often overlooked as part of the overall security strategy for educational institutions and others when drawing up their ransomware protection and recovery strategies. Most educational institutions are using some form of cloud Software-as-a-Service environments for campus email and file storage solutions. How can these be protected from the threat of ransomware?
SpinOne helps educational institutions and other organizations protect their valuable cloud assets from modern ransomware threats. It uses artificial intelligence (AI) and machine learning (ML) to provide an agentless and fully automated Google Workspace™ and Office 365 ransomware protection framework and cuts downtime due to cloud ransomware to 2 hours, saving costs by up to 90%.
SpinOne uniquely helps protect businesses from the threat of double extortion used by Vice Society and others. Not only can it recover data from a ransomware attack, but it can also stop malicious processes. Therefore, it helps to minimize data leaks by malicious processes. Note the following features of SpinOne Ransomware Protection:
- It monitors cloud SaaS environments for signs of ransomware 24/7/365
- When ransomware is detected, SpinOne blocks the ransomware source
- It automatically isolates assets affected by the ransomware attack
- It restores files automatically to the latest backed-up version (configurable)
- Admins are notified of incidents in real-time
- It provides granular SaaS security policy orchestration
If you would like to speak with a Spin Solution Engineer to discuss how SpinOne can help you meet your ransomware protection challenges, click here to book a demo: Request a Demo of SpinOne
Next, we will look at the recommendations from CISA and the FBI for educational institutions and others to protect themselves from the activities of Vice Society and others.










