SaaS Data Protection Checklist for Enterprises

As we have covered in our cybersecurity series, SaaS data protection and security are essential to meeting the enterprise’s modern security and compliance objectives. As a recap, let’s look at a SaaS data protection checklist of critical SaaS data protection and security objectives essential for organizations today. It helps to reveal potential “holes in the armor” of a business’s current cybersecurity and compliance postures.
Modern threats require vigilance, data protection, and security
There is no question that there are more cybersecurity threats than ever targeting business-critical data. It requires vigilance on the part of organizations today to adequately protect and secure their data. In addition, the new era of cloud SaaS services and solutions requires businesses to safeguard and secure their data on-premises and in the cloud.
In 2021, ransomware attacks cost businesses worldwide $20 billion, and 37% of all organizations were attacked. With attackers using double extortion attacks, protecting critical data and proactively stopping ransomware attacks is essential. Unfortunately, even if you can recover your cloud SaaS data, the bad guys can leak your data, which is arguably, in many cases, worse.
Attackers are continuously looking for new ways to compromise critical data, shifting their focus to include cloud environments, including cloud SaaS. With the shared responsibility model, the burden of protecting your data falls on you as the customer. This fact emphasizes the need to back up and secure critical data in cloud SaaS environments, including Google Workspace, Microsoft 365, and Salesforce.
SaaS data protection checklist
Data protection and security is challenging and requires a multi-faceted approach involving processes and technologies to safeguard data. It includes the following:
- Proper backups
- Visibility of your data and data sharing
- Controlling third-party apps
- Ransomware protection
1. Proper backups
One of the foundation cornerstones of any proper data protection strategy is backups. Backups provide a completely self-contained copy of your data that does not rely on the production environment. In addition, backups allow businesses to recreate data damaged, deleted, encrypted, or otherwise affected by a data loss or cybersecurity event.
When related to cloud SaaS environments like Google Workspace, Microsoft 365, or Salesforce, businesses may mistakenly assume they don’t need to back up their data as SaaS environments automatically protect your data. However, again, the shared responsibility model says otherwise.
When it relates to your data, you are responsible. For example, mechanisms like file versioning provided by cloud service providers like Google and Microsoft are not enterprise backups of your data since you don’t own the backups. In addition, if you stop paying for the cloud SaaS subscription, that copy of your data goes away.
A proper backup of your cloud SaaS data means you own the data and can take that with you, regardless of the cloud SaaS subscription, and have additional controls over your data.
2. Visibility of your data and data sharing
Many businesses find it challenging to maintain visibility on their critical data and ensure data governance when related to cloud SaaS environments. It becomes difficult to protect and secure data without visibility to where data resides and who is accessing that data.
Maintaining visibility of your data and data sharing is critical. Unfortunately, many find that native cloud Saas tools do not provide the visibility needed to ensure data is not accessed improperly or in an unsanctioned way, or it is cumbersome to audit access using native cloud tools.
Third-party tools are generally required to have the protection, security, governance, and compliance tooling necessary to see who is accessing what data and which third-party applications have been integrated into the environment with data access.
3. Controlling third-party apps
Third-party apps are a powerful benefit of using cloud SaaS environments. However, they can be a double-edged sword regarding security and compliance. By default, end-users can install any third-party applications from cloud SaaS marketplaces.
This capability opens businesses up to many security concerns as users can install any third-party app and allow these apps to integrate with critical data without a proper risk assessment. Therefore, organizations must perform appropriate risk assessments of all third-party applications and ensure they align with security and compliance requirements.
Performing manual risk assessments of all third-party applications in a cloud SaaS marketplace is generally unrealistic without cybersecurity automation. As a result, businesses need to leverage automated solutions featuring artificial intelligence (AI) and machine learning (ML), helping take the heavy lifting out of these tedious and manual processes.
Configuring “allow lists” and “block lists” of applications helps enforce governance and compliance requirements to bolster an organization’s cybersecurity posture.
4. Ransomware protection
Unfortunately, Google Workspace and Office 365 ransomware attacks are increasing, with attackers using new extortion tactics like double extortion to hold critical data hostage. Unquestionably, protecting critical data from ransomware is essential. Unfortunately, many protections built into cloud SaaS environments are reactive, only notifying customers if ransomware is detected.
Provisioning proactive ransomware protection for cloud SaaS environments helps ensure an attack is not only detected but remediated using cybersecurity automation. However, even if you have good backups of your cloud SaaS environment, recovery to cloud SaaS accounts can be slow and subject to throttling, slowing recovery progress even further. See Microsoft’s guidance on how they throttle API requests here:
Microsoft Graph throttling guidance – Microsoft Graph | Microsoft Learn
Meet Your SaaS Data Protection Goals
Bolster your SaaS data protection checklist with SpinOne
As we have mentioned, a proper data protection checklist should include solutions for the following:
- Proper backups
- Visibility of your data and data sharing
- Controlling third-party apps
- Ransomware protection
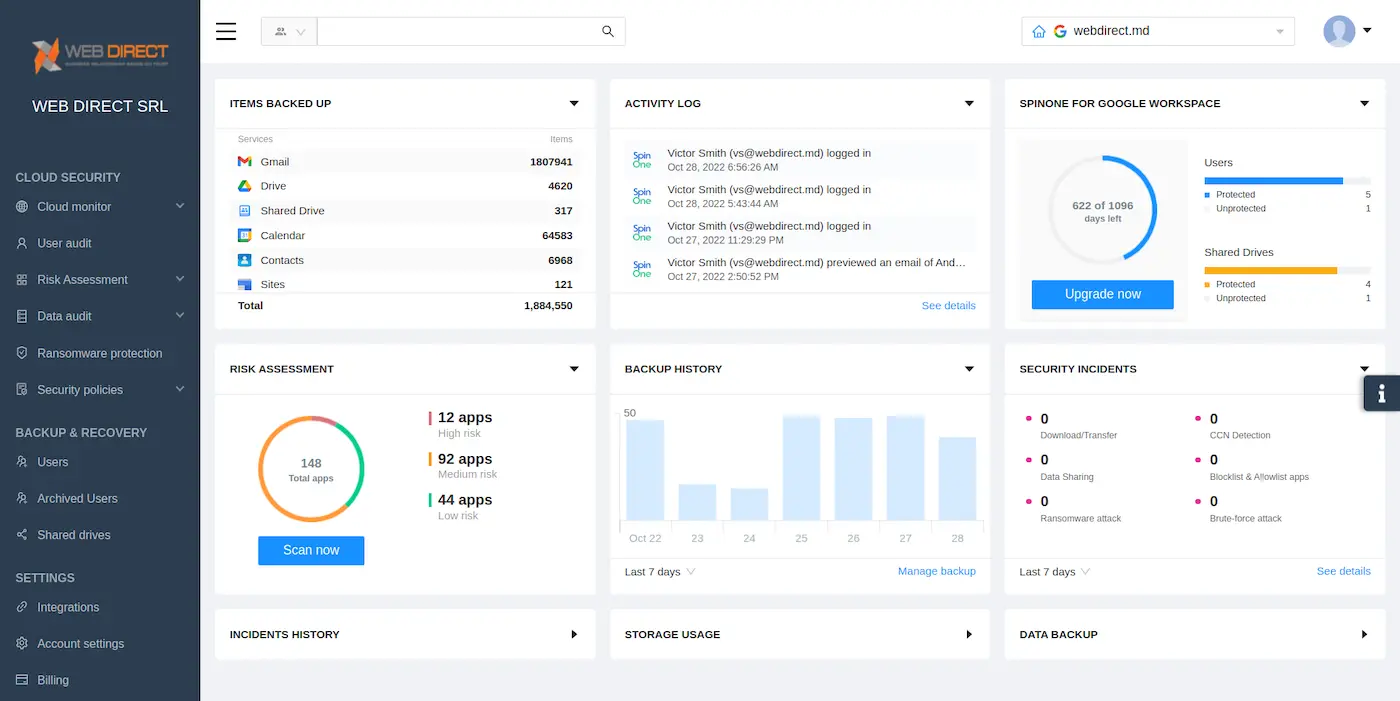
It often requires third-party tools to effectively implement proper data protection and security for critical SaaS data stored in cloud SaaS environments. SpinOne is a next-generation tool providing data protection and cybersecurity automation for organizations using cloud SaaS solutions like Google Workspace, Microsoft 365, and Salesforce.
Note the following capabilities offered by SpinOne:
- Continuously monitors cloud SaaS environments for signs of ransomware 24/7/365
- If ransomware is detected, SpinOne blocks the ransomware source
- Automatically isolates assets affected by the ransomware attack
- Automatically restores affected files to the latest backed-up version
- It Immediately notifies IT admins of incidents in real-time
In addition, the SpinOne solution enables organizations to implement Saas data protection and security best practices, including:
- Maintain offline backups of data – SpinOne stores backups in separate cloud storage locations allowing businesses to choose where and in what region cloud backups are stored
- Ensure data is encrypted and immutable – SpinOne uses the latest security standards, securing data backups end-to-end.
- Review the security and access of third-party vendors – SpinOne provides automated risk assessments, reducing what would take hours for trained SecOps professionals to only minutes with the Spin solution. It also offers policy-based cybersecurity automation to control third-party app installations
- Implement policies to enforce using only sanctioned applications and remote access solutions – In addition to providing insight into third-party applications used in the organization, admins can create allow and block lists to control third-party app usage
- Document and monitor external remote connections – SpinOne provides real-time visibility and reporting
- Implement a recovery plan – SpinOne leverages next-generation artificial intelligence (AI) and machine learning (ML) to automate cybersecurity recovery in the cloud by proactively kicking into action when ransomware is detected and proactively stopping an attack
If you would like to speak with a Spin Solution Engineer to discuss how SpinOne can help you meet your ransomware protection challenges, click here to book a demo: Request a Demo of SpinOne
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
Reducing Browser Extension Risk with Spin.AI Risk Assessment + Perc...
April 24, 2024Spin.AI is collaborating with Perception Point: integrating the Spin.AI Browser Extension Risk Assessment within the... Read more
How to Restore A Backup From Google Drive: A Step-by-Step Guide
April 10, 2024Backing up your Google Drive is like making a safety net for the digital part... Read more
Protecting Partner Margins: An Inside Look at the New Spin.AI Partn...
April 2, 2024Google recently announced a 40% reduction in the partner margin for Google Workspace renewals –... Read more


