Chrome Extension Permission: Security Tips for Businesses
Chrome extensions are widely used for performance, accessibility, or fun. However, they can bear hidden risks, especially if they have excessive permissions. Learn about Chrome Extension Permission, how to analyze it, and how to secure your data when using Chrome extensions.
What is a Chrome Extension Permission?
Chrome Extensions have become extremely popular in business settings. Chrome Extension permissions allow extensions to perform their tasks as well as have access to your data.
Google Chrome Extension Permissions Categories
There are several categories of Chrome extension permissions:
- API Permissions
This type of permission enables the extension to access certain APIs, for example, cookies.
- Host permissions
These permissions enable the extension to access a number of URLs or any URL. There are two subtypes. Explicit Hosts control the extension’s access to the APIs that read or modify the data. Scriptable hosts dictate the hosts on which the extension uses content scripts.
- Manifest Permissions
This category is similar to API permissions. It controls the access to certain functions, e.g., Bluetooth.
- Granted Permissions
These are the permissions that the user has agreed to and hasn’t revoked. Some of the granted permissions can come with the initial installation of the extension, while others come with the upgrades.
Users can control permissions in Google Chrome or ultimately revoke access if permissions are too broad for the purposes of the extension.
Chrome Extension permissions are also categorized by risk level:
- Low alert permissions include reading your browsing history, physical location, copypasted data, bookmarks, installed apps and extensions, tabs and browsing activity.
- Medium alert permissions also include access and editing rights to all the data on the websites you visit.
- High alert permissions also include access to the data stored on your computer.
Where can you see Chrome Extension Permissions?
The user can check the Chrome extension permissions in 3 ways:
- During the initial extension installation or upgrade in Google Chrom Webstore.
At this stage, you also grant permissions to the extension.
- In Google Chrome.
To check permissions in Google Chrome, click on the three dots in the right upper corner of your Chrome screen (next to the URL bar). In the drop-down menu, hover over the Extensions and then click Manage Extensions. You will be redirected to the page with all your extensions.
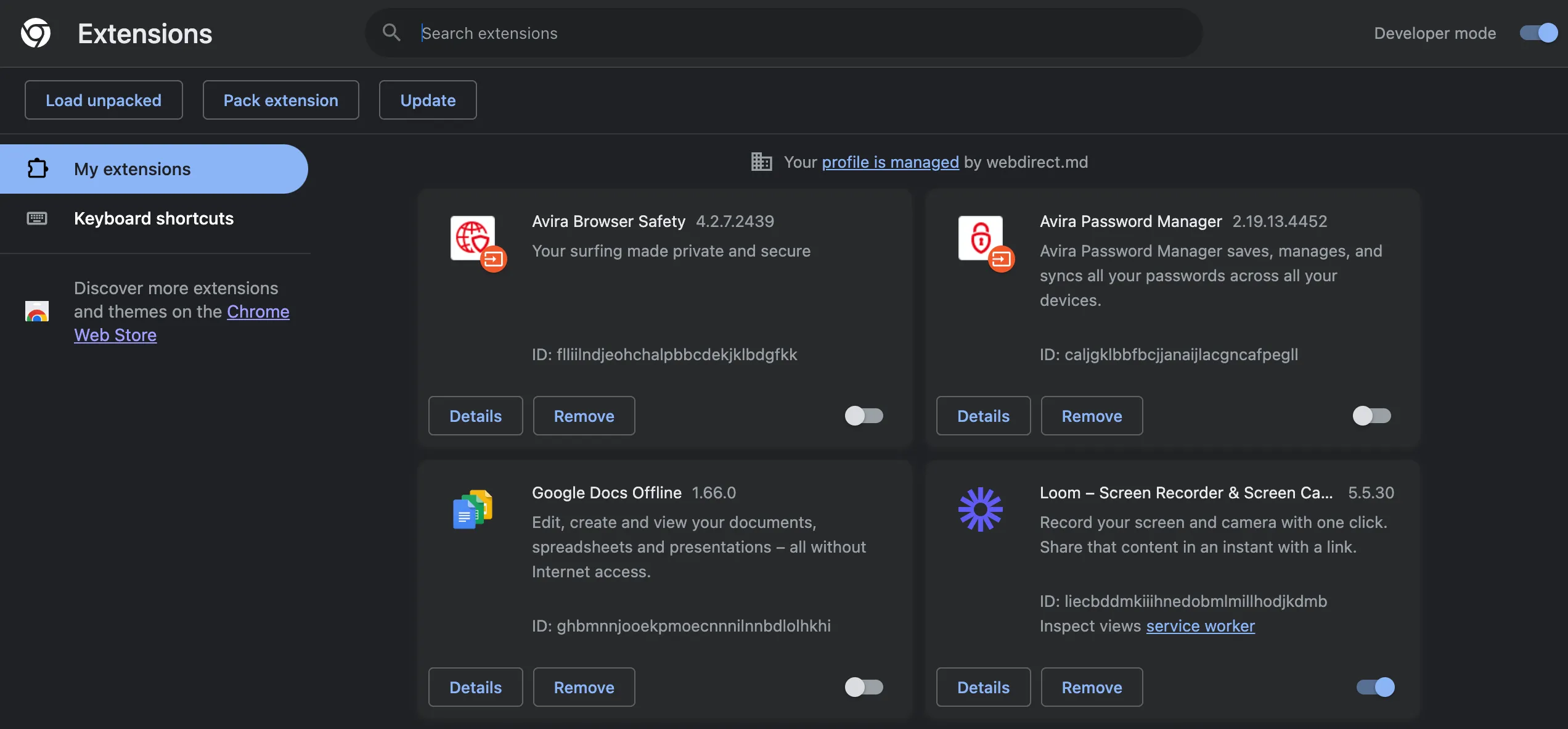
Here you can remove extensions or click on the Details to be redirected to the extension’s page in Chrome. Here you can see the permissions and can control the scope of their use (e.g., all websites, specific sites, on click).
You can also click Site Settings and will be redirected to the page where you can choose which permissions are granted to this extension and how. For example, you can block the use of a camera, mandate that the app asks for access to the microphone, and allow the location.
Security Risks of Chrome Extension Permissions
Chrome extension permissions pose multiple risks to individuals and businesses. First, permissions grant the extension access to your sensitive data as well as computer devices that can collect even more sensitive data (e.g., camera and microphone).
Most individuals do not check the developer properly:
- the Privacy Policy and Terms of Use,
- the country of registration,
- the type of entity (business or individual)
- the scope of permissions
- whether the scope of permissions exceeds the needs of extension performance.
The latter is exceptionally critical. The excessive permissions can be a major sign of a risky extension. For example, you have an extension for customizing your Google Chrome. However, it requires access and editing rights to all your data. Such broad permissions aren’t critical for browser customization. Why does the extension require them?
Many people think that Google does a proper check on all extensions and applications available on its Chrome Webstore and Marketplace. It’s true, however, that the app examination doesn’t guarantee the malicious use of the extension for data extortion, deletion, or more complex zero-day attacks.
As concerns businesses’ security, many employees use their work accounts to install various Chrome extensions. Many of them are applied to boost productivity and the use seems legitimate to the employees. However, security risks of data loss, data extortion, or zero-day attacks on business is even higher than on individuals.
Learn more about Chrome Extension Security Risks.
Chrome Extension Permissions Security Best Practices
In this section, we discuss how individuals and organizations can control and secure Google Chrome Extension Permissions.
Audit the extension and its developer
On the extension’s page on Chrome Webstore, look for the right-side panel. There you can see the information about the developer, their address of registration, email address, and the link to the privacy policies.
The following things should alert you:
- The developer doesn’t specify the organization name, legal address, and other contact data in Chrome Webstore
- Privacy Policy doesn’t contain any legal information (company name, registration address, etc.). Google doesn’t check the Privacy Policy. Only its availability. However, the privacy policy that has no registered organization signing it has no legal force.
- The website is missing or the link is broken.
- The email address has a general domain (e.g., appdeveloper@gmail.com)
- The version of the extension and the last update. Diligent developers constantly update the versions to enhance security.
- Check the country of registration of the developer. Some countries have more laws governing privacy and data protection. The companies registered in these countries have more legal consequences if their extension deletes or leaks your data or collects data it should collect (e.g., your SSN).
This quick check-up will take only a few minutes, however, it will enable you to establish the credibility and liability of the developer.
Always review Chrome extension permissions before installing.
If you find the permissions excessive or cannot make a reasonable judgment, search for alternative tools and see which permissions they request from their users.
Always review permissions before agreeing to update.
Some extensions can significantly increase the scope of requested permissions during the update. Often users agree to them without reading.
Review all the Chrome extensions and delete those you do not use anymore
If you have several computers, you need to check the Chrome extension on each of them. Many people use several Chrome profiles on their PC, for example, one for a work account, one for a personal account, and one for a family member’s account. The Chrome for each account will have different extensions and different permission settings. You need to check all of them.
Audit the existing Chrome Extensions, their developers, and their permissions
Delete those that you find risky and search for more credible alternatives. Keep in mind that you need to conduct permission revisions on a regular basis.
Update extensions regularly
Regular updates make sure that your extensions have all the security features, as well as bugs and vulnerability fixes that developers have implemented. It will reduce the chances of a zero-day attack.
Use third-party tools to control Chrome Extensions
Tools like SpinMonitor for Google Workspace™ can help businesses control risky extensions. With this app installed, your employees will only use the extensions that meet the requirements of your security policies.
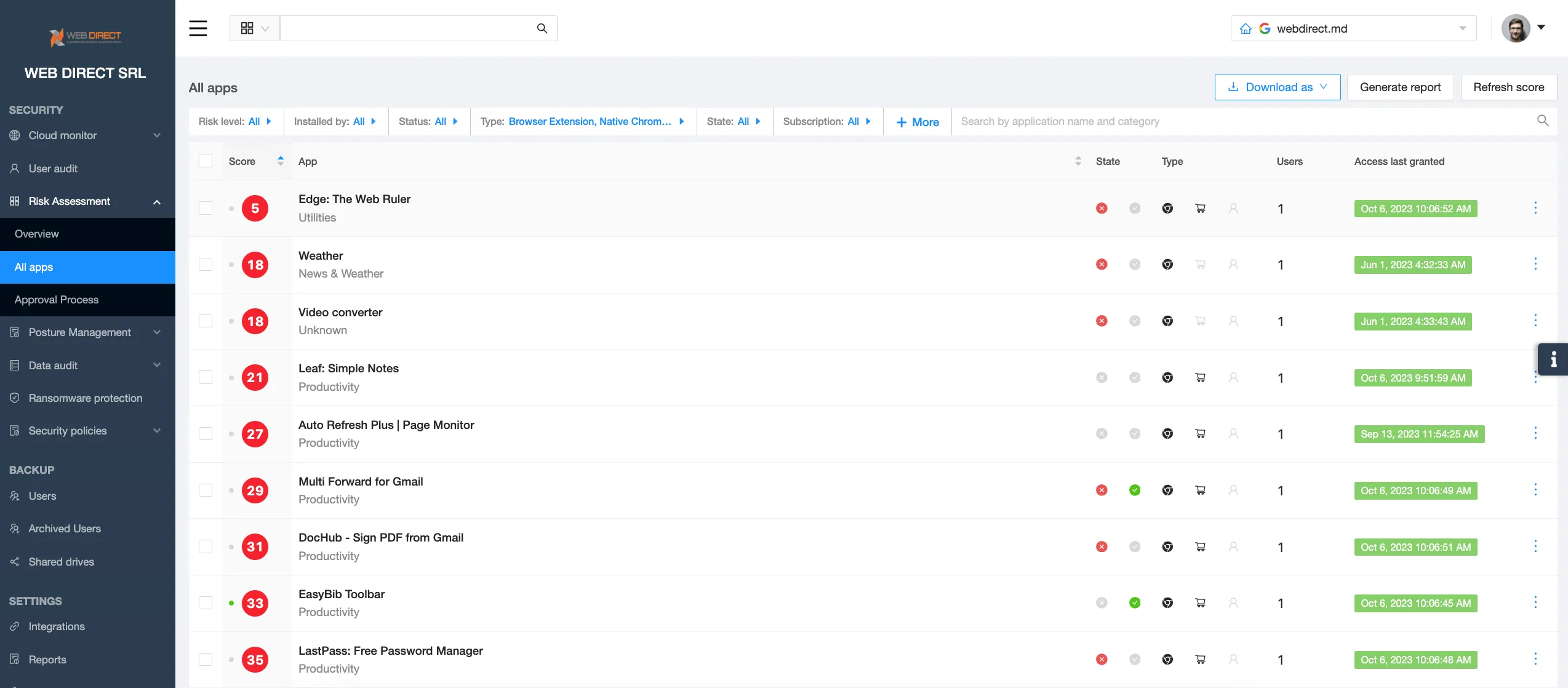
SpinMonitor capabilities include:
- Detect any and all Chrome extensions installed by your Google Workspace™ users
- Assess the extension risks automatically to help make decisions on their blocking
- Create custom allow and block lists to control extensions automatically
- Extension request functionality that streamlines the communication between the users and the IT security team.
- Block all the extensions that do not match certain risk criteria automatically.
Learn more about application and extension security with SpinOne.
FAQs
Why does a Chrome Extension need permissions?
Chrome Extension needs permission to properly perform its functions.
Can an extension access my personal data without my knowledge?
Yes. If you gave the extension permission to access your data.
How often should I review my extensions and their permissions?
We suggest reviewing extensions and permissions every 3 months.