According to Gartner, by 2026, 60% of organizations will see preventing cloud misconfiguration as a cloud security priority. No surprise here, as the cloud adoption rate is over 90% and businesses have become increasingly dependent on cloud environments for their operations and data storage. One tool that can help tackle the challenges of the new environment is Cloud Security Posture Management.
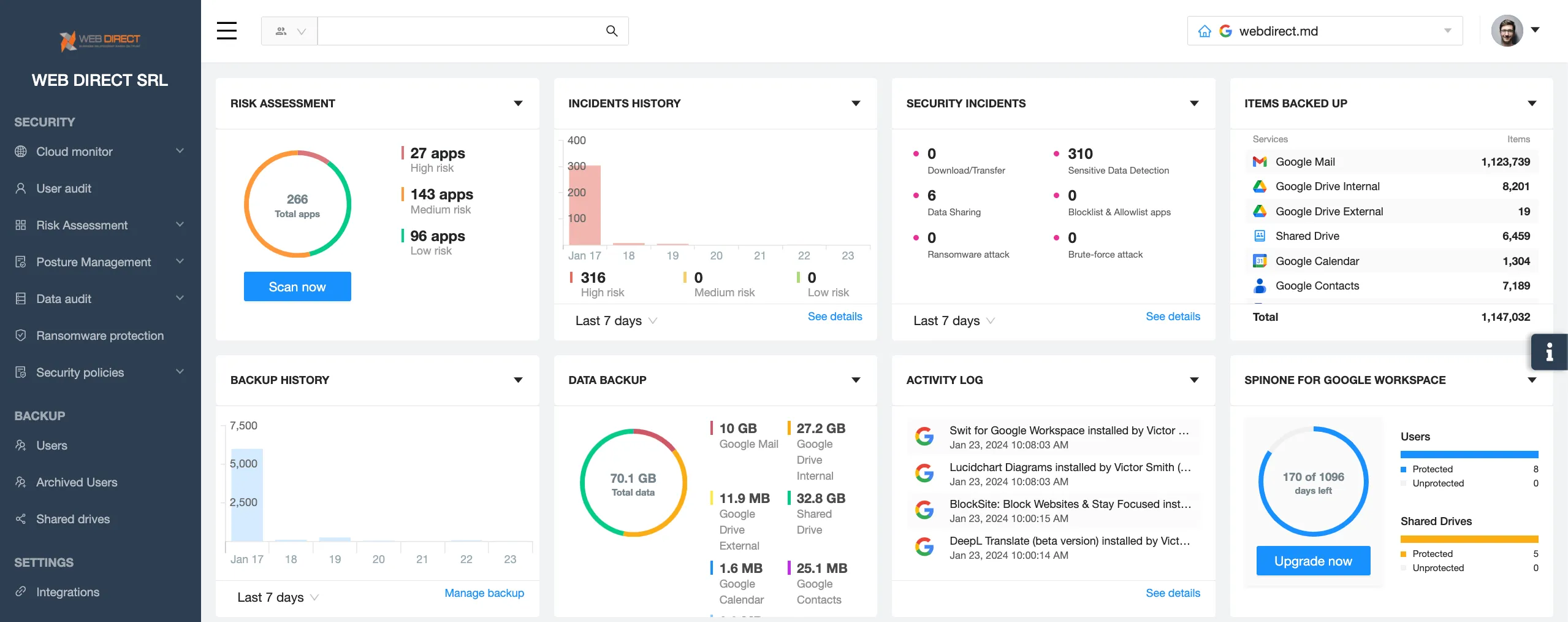
CSPM helps IT security teams identify cloud misconfigurations, and provide visibility into the cloud and control over the access to the environment. In this article, we will discuss the best practices for Cloud Security Posture management for your organization.
Understanding CSPM
The rapid adoption of cloud technologies enabled businesses to harness powerful computing capabilities while cutting costs on system building and maintenance. It also helped companies broaden their workforce geographically and employ the best talents worldwide.
The new cloud environment was less prone to natural disasters, outages, and hacker attacks. However, it had new vulnerabilities that made the traditional security architecture obsolete and inapplicable.
The biggest challenges for cloud security are:
- Access control
- Ransomware protection
- Detection of misconfiguration
- SaaS applications control
- Maintaining compliance
- Security visibility
- Closing the talent gap through automation
To meet the majority of these challenges cybersecurity experts created a new category of tools – Cloud Security Posture Management. CSPMs help tackle all the issues listed above except for ransomware protection.
Benefits of CSPM
Cloud Security Posture Management tools have multiple benefits for the organization that acquires and implements them. The main features of CSPM help IT security teams enhance cloud security and achieve compliance through:
- providing a bird’s eye view of the cloud
- a control panel for misconfiguration detection and remedy
- ensuring mass and individual control over user access
A category of CSPM, SSPMs also help prevent zero-day attacks through SaaS applications control.
The benefits of CSPMs include:
- Improved security posture
According to Gartner, through 2025, 99% of cloud security failures will be the customer’s fault. Gartner analysts imply that cloud misconfigurations will lead to the majority of cloud cyber incidents such as data loss or leakage. CSPM will help organizations to identify incorrect cloud settings.
Access monitoring and control is another CSPM functionality that helps companies enhance security. Clouds have no defined security perimeter and have multiple access points through user accounts. Keeping track of all employees is next to impossible without a tool that analyzes user behavior and identifies the abnormal.
Automation provided by CSPM helps reduce the workload on a security team and cover the talent gap.
- Enhanced compliance
Compliance is tightly connected to cloud configurations. Many CSPM tools have incorporated compliance kits that provide a number of rules to comply with certain laws or regulations.
- Cost reduction
The cost of data breaches is increasing year over year. It includes downtime, legal penalties, and reputational losses. CSPMs help avoid the expenses associated with data breaches by increasing security posture and preventing major cybersecurity incidents.
CSPM Best Practices
In this section, we discuss the best practices for implementing Cloud Security Posture Management.
1. Map your cloud environments
There are several types of cloud environments: Infrastructure-as-a-Service, Platform-as-a-Service, and Software-as-a-Service. An organization can have one or several types of these environments.
It’s critical to understand where your business operations take place. Failing to secure a cloud environment can lead to serious implications.
If your organization uses SaaS tools, it will be hard to map all of them (learn more about Shadow IT) and you will need an SSPM tool to do it.
2. Identify the security gaps in your cloud
You need to understand the security capabilities of each cloud environment your organization uses. And then identify which areas remain vulnerable.
Most cloud providers have the so-called shared responsibility model. This model stipulates which areas of security the vendor undertakes and which are left for you to protect. For example, most cloud providers take care of data center maintenance and proofing against natural disasters.
Most cloud providers leave the access control in the sphere of responsibility of the buyer. The same is true for cloud configurations. Your IT and legal team needs to study the shared responsibility model along with the security configurations of your cloud and then outline the gaps.
Learn about cloud security threats.
3. Outline the compliance requirements
It’s best to have all the compliance requirements listed in one document. Your legal team needs to update documents on a regular basis. Modern legislation is rapidly changing to fit the needs of the cybersecurity landscape and balance them with the rights of individual citizens.
Additionally, we see new cybersecurity standards. While these standards aren’t mandatory for the majority of businesses, meeting them will guarantee your cloud data security and even help with closing certain clients and establishing new partnerships.
4. Create security policies
Write down what security policies can enhance your cloud security gaps and help with compliance. You’ll need to do this exercise twice. First, before looking for CSPM tools, then after purchasing one.
Your security policies can change over time. Chances are, no CSPM tool will meet your particular security needs perfectly. However, it can help to significantly improve your security posture and automate most of the processes, while your team will handle the rest.
5. Outline access strategy
CSPM can help you control the access of users to your data as well as identify possible account hijack instances. We suggest creating an access strategy to make the most of your CSPM tool.
The cloud access security is based on the zero-trust approach. The term is a bit misleading as it might seem that you must never trust any users, i.e., lock the environment and don’t let anyone it. That’s not the case with the zero-trust approach.
In reality, you simply need to give minimal trust and minimal access to the user. The minimal trust implies that you need to regularly make sure that the person logged in under a certain username is indeed the user and not an imposter. This can be achieved by multifactor authentication, regular password change, and user behavior analysis. The last is the CSPM feature.
Minimal access implies that users should only have access to data that they absolutely need to carry out their job tasks. For example, a salesperson doesn’t need to access the accounting spreadsheets, accountants do not need to read marketing strategy, and none of them should have access to product documentation. This principle includes restricting the sharing of data outside organizations.
6. Choose the CSPM tool
There are many high-quality CSPM tools on the market. We suggest looking for the following criteria when choosing one for your organization:
- It covers all or most of the cloud environments that you are using
- It has the necessary compliance certifications
- It meets your other compliance requirements
- It covers most of the security gaps that your cloud has
- It has the necessary features (e.g., security policies and access configurations)
7. Work with your team on CSPM implementation
Introducing a new tool in your organization can be a difficult task. Apart from teaching your team how to use it, we suggest creating a new playbook for using CSPM.
Include the roles and responsibilities. Stipulate the backup employees in case a person executing a certain task cannot come. Help your team create new schedules and routines around using the new tool. Many IT tools implementations fail because the team forgets to use it or doesn’t know the tips and tricks that will make usage more comfortable. Look for the best practices to use your CSPM.
8. Audit and update
Make sure that compliance requirements, security gaps, and security policies are updated regularly. Audit the work of your Cloud Security Posture Management solution on a regular basis and make sure that it’s up-to-date.
Wrapping up, Cloud Security Posture Management is a category of tools that meets the specific requirements of the cloud and helps close security gaps. Implementing CSPM in your cloud environment has multiple benefits, like enhanced compliance, cost reduction, and improved security posture.
CSPM implementation can have multiple challenges, but if your IT security teams follow the best practices, you can achieve success in using this tool and have a smooth introduction.
FAQs
What are the common security challenges CSPM can help address?
The common security challenges CSPM can help address are cloud misconfigurations, risky apps, lack of visibility, non-compliance, and a talent gap.
How does CSPM help with compliance and regulatory requirements?
CSPM detects misconfigurations in the cloud including those that cause non-compliance. It also strengthens the cloud security posture and prevents cyber events that can cause breach of compliance.
What are the key features and capabilities of CSPM tools?
The key features are misconfiguration detection, app control, visibility, and automation of security controls.
Do CSPM solutions support multi-cloud environments?
Yes, some CSPM solutions support multi-cloud environments.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
What You Need to Know About AT&T’s Data Breach and How t...
Arguably, it is one of the worst breaches that has happened recently. AT&T disclosed in...
Lessons from the Twilio Breach: Securing SaaS Applications Against ...
Another recent security breach has made organizations think yet again about SaaS apps they may...
Unpacking the CrowdStrike Outage: Causes, Impacts, and Protecting Y...
A major global IT outage occurred on Friday, July 19, 2024, causing widespread disruptions across...