The Growing Need for SSPM: Securing Your SaaS Applications
SSPM is becoming increasingly popular in enterprise security architecture. While it’s encouraging to see the growing demand for this category of cloud security solution, we anticipate that the demand will continue growing – especially with the surge in zero-day attacks in 2023.
The most notable 2023 attack was the MOVEit breach. In a May vulnerability exploit, the ransomware gang Clop gained access to the data of over 16 million people. Many notable businesses and organizations, including United States federal agencies, were impacted by this attack.
SSPM can help companies take SaaS applications under control and minimize the risks related to them. In this article, we’ll look at the risks and benefits that SSPM brings to companies that extensively use cloud solutions.
Understanding the Security Risks in SaaS Applications
SaaS applications can skyrocket the performance of most departments in your organization. However, SaaS apps can also bear multiple risks to your data security.
Data risks
All SaaS applications have access to your data. The extent of this access is defined by the permissions that your users give to these apps. In some cases, the tool only knows their email address and language preferences. As small as it seems, this information can still be utilized by hackers, for example, to send a more targeted phishing email.
However, many productivity applications sold on marketplaces of Google Workspace™ and Microsoft 365 can access the data that your company stores in these cloud collab tools. Furthermore, many of them have dangerous edit and mass edit rights.
An error in these applications, a vulnerability exploit, or a decision of the application developer can corrupt your data or copy it to unauthorized data storage – causing data leak or loss.
Learn more about Application Risks.
Compliance
Many SaaS applications become the storage of your corporate data. For example, CRMs store information about your potential and existing clients, their contact data, communication logs, details of the projects, the contracts, etc.
If your company falls under the laws that limit the geography of data storage and your team uses the application outside the stipulated area, you might face legal penalties and fines.
Furthermore, you might break data retention laws if a risky app erases all your data.
Zero-day attacks
Lately, we’ve seen a surge in zero-day attacks when hackers exploit previously unknown vulnerabilities of legitimate applications. As a result, criminals access your corporate data. They can leak it, sell it, delete it, edit it, hold it hostage until you pay the ransom, or all the above. They can also use zero-day attacks to infect your cloud office suits with ransomware.
The most notable one in 2023 was the MOVEit breach. In a May vulnerability exploit, the ransomware gang Clop gained access to the data of over 16 million people. Many notable businesses and organizations, including United States federal agencies, were impacted by this attack.
Visibility
Probably the most critical aspect of SaaS applications is the lack of visibility (and thus control). Most SaaS applications enable OAuth sign-in using either Google or Microsoft accounts. In just a couple of clicks, your user can create an entry point for hackers while ordering pizza.
It’s actually a real-life example. Employees use their work account to sign up for applications they intend to use for personal purposes (like online games, delivery services, etc.) almost just as often as productivity tools for work.
Your company might have strict security policies governing applications on paper. However, the research proves that without real physical barriers, employees (and even IT specialists) ignore these policies and use unauthorized apps.
Control
The inability to control applications with OAuth access is yet another problem that weighs on SecOps teams. There are several aspects that contribute to it. First, you can’t control an application if you don’t know it has access to your data.
Second, application discovery is only the first step in the process. The security team needs to assess the app’s risks and make a decision on whether to revoke access or not.
The more users you have, the more Shadow IT apps will have access to your sensitive data. As a result, you need to allocate significant resources for detecting and disabling those applications.
The Role of SSPM in Securing SaaS Applications
SaaS Security Posture Management tools were designed bearing in mind the key risks that SaaS apps pose.
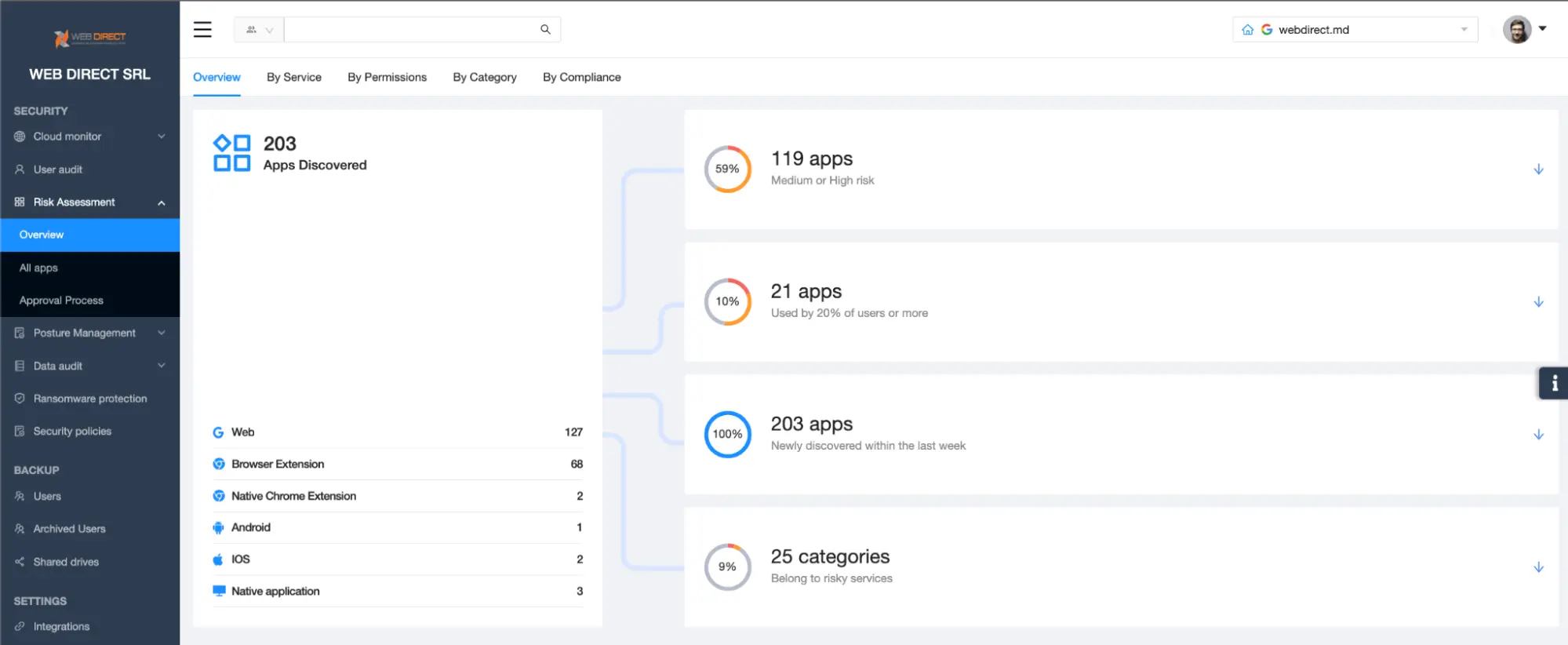
Most importantly, they provide crystal-clear visibility into all the applications that have access to your data. Here’s an example of SpinOne SSPM functionality:
As you can see in the screenshot, SpinOne can detect all the applications that have OAuth access to your sensitive data.
Furthermore, it provides all the available information about each app (like country of developer’s residence, number of users, category, regularity of updates, privacy policies, historically discovered vulnerabilities, etc.). It also makes an assessment of an application based on many criteria. These are the capabilities of SSPM tools.
SpinOne SSPM also has the functionality to disable the application right on the spot, so your security professionals do not need to go to the Admin Console of Google Workspace™ or Microsoft 365 to manage applications.
SpinOne SSPM functionality returns visibility and control over risky apps to your security team. Furthermore, it automates the discovery and assessment process taking the biggest workload off your specialists.
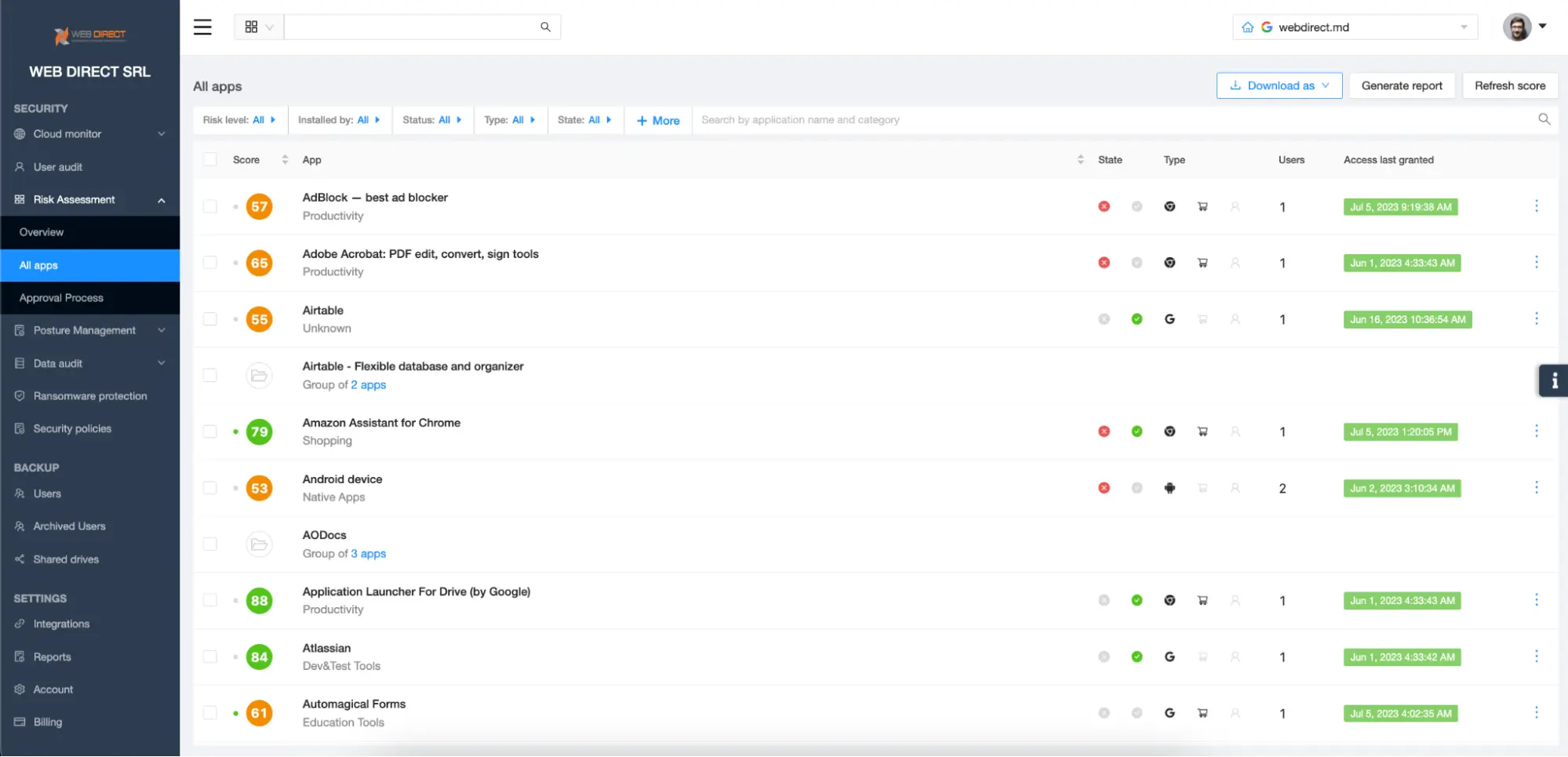
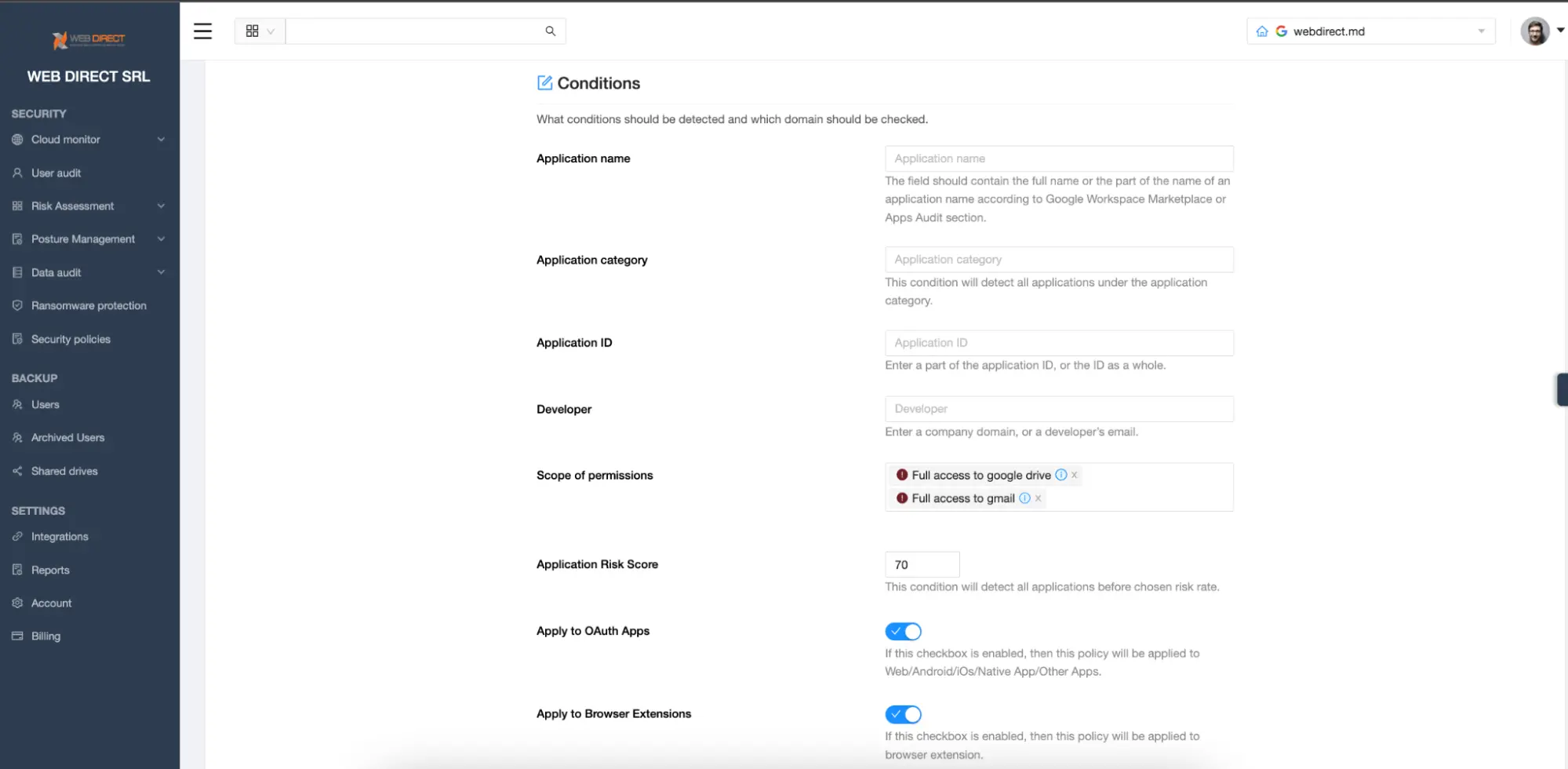
Once you’ve taken full control of your applications, you can proceed with creating security policies. The policies you establish in SSPM create real physical boundaries that prevent your users from adding applications that meet certain criteria. For example, in the screenshot below you can see that a security policy automatically blocks any app and extension that has a risk score of 70 or lower and has full access to Google Drive™ and Gmail™:
Finally, SpinOne SSPM facilitates the communication process between the Security team and other employees. It has inbuilt functionality that enables the app request process. For example, if a user needs a certain application, they can send the request using the SpinOne Chrome extension. The admins will review this request in the SSPM and allow or block the respective application.
Summing up, SSPM tools provide visibility and control over SaaS applications preventing unauthorized data access and leak. With the increase of zero-day vulnerability attacks, they are no longer a luxury but a must-have layer in the security architecture of any business.
FAQs
How does SSPM integrate with existing security infrastructure and tools?
SSPM integrates using APIs with various cloud environments and security tools. When choosing SSPM, you need to take into account these integrations so that it can fit your security architecture.
Does SSPM help in addressing misconfigurations in SaaS applications?
Some SSPM tool, including SpinOne, has the functionality that enables you to detect misconfigurations in the protected SaaS environments.
Some SSPM tool, including SpinOne, has the functionality that enables you to detect misconfigurations in the protected SaaS environments.
Does SSPM help in addressing vulnerabilities in SaaS applications? How does SSPM integrate with existing security infrastructure and tools?
SSPM cannot find unknown vulnerabilities in SaaS applications. As of the moment, it’s a human-driven process done by hackers and app developers. SSPM can report the discovered and reported vulnerabilities. It also can detect the update frequency. Developers that frequently update their applications are more likely to patch bugs, address vulnerabilities, and update security.
What role does SSPM play in preventing unauthorized access to SaaS resources?
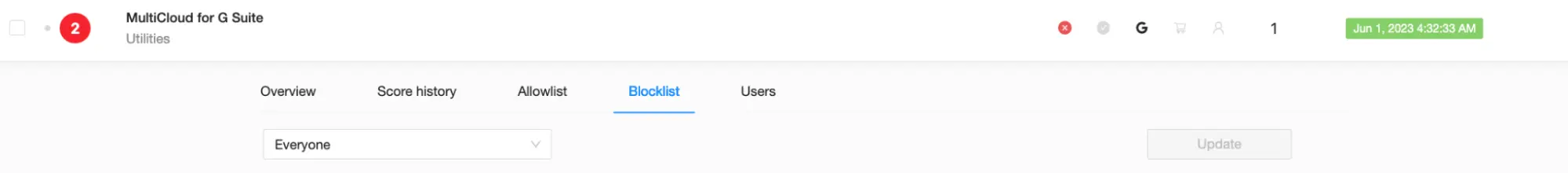
SSPM tools like SpinOne have security policies that enable you to create allow and blocklists. These lists disable OAuth access to unauthorized apps automatically.
Can SSPM support incident response and forensic analysis in SaaS environments?
SSPMs send alerts to the security team to notify about incidents. It also provides valuable data about applications and which users use them.
What is the future outlook for SSPM and its role in securing SaaS applications?
In he future, SSPM tools will continue developing more features to enable security teams to fully control SaaS applications.