SaaS Application Security Risk Assessment and Modeling
SaaS application security risk assessment is critical for companies looking to ensure their critical data is secure and protected. Learn what it is, why it is important, and how to conduct a Saas application security risk assessment.
SaaS apps have become a pivotal asset for many organizations, especially in a world that embraces remote and hybrid work. They can significantly boost productivity, connect us in new and convenient ways, and improve our workflows. On the other hand, they also reveal vulnerabilities cybercriminals can exploit.
In this article, we’ll discuss the risk assessment pertaining to the SaaS apps using OAuth authorization via Google Workspace™ and Microsoft Office 365 accounts.
We’ll cover the process itself as well as the security risk assessment apps that let you automate it.
SaaS Applications Basics
SaaS applications are used for productivity improvement by employees. Most of them use OAuth to provide access to their functionality. The same mechanism is also applied by websites with gated content, for example, online magazines.
This authorization process is extremely user-friendly – employees don’t need to remember multiple logins and passwords to various programs. They simply use one set of credentials for all programs.
Many people consider Google Workspace™ and Microsoft Office 365 trustworthy (the result of the human experience and marketing efforts of both IT giants). This trust is undeservedly and unreasonably transferred to applications available on Google Marketplace or Microsoft Marketplace. Using them creates a serious risk and we’ll discuss why in the next section.
One of the key problems with OAuth is the app access to your data and its permissions scope.
Here’s an example of OAuth access to Semrush:
As you can see, the program will access some of the user’s personal information like name, email address, language preference, and profile picture. At first glance, it’s not much: but it can easily be used in an engineering attack on your employee.
Let’s talk about permission scope. In the case of Semrush, the program requires no special permissions. However, if you want to install, for example, Grammarly Chrome Extension, you will permit this app to read and change all your data on all your websites. This applies inter alia Google Workspace™ documents.
The scope of permissions differs from one software to another. In most cases, responsible developers don’t request permissions that aren’t necessary for the proper operation of an application. However, not all developers are responsible – or worse, they can sometimes operate in a country with gray-area app development and data protection laws. Not being subject to prosecution can create a nefarious problem.
The outcomes of cyber incidents related to SaaS applications
Below is the list of possible outcomes caused by cyber-attacks using SaaS applications:
- Business downtime.
- Money losses.
- Reputational losses.
- Data theft.
- Sensitive information leak.
- Legal implications.
- Disruption (especially if the attack is carried out on supply chains).
- Severe damage to human health (e.g., as a result of an attack on a hospital or a factory).
- Damage to communities (if the target is governmental institutions).
SaaS Applications Security Risks for Enterprises
Let’s now quickly overview the main SaaS app security risks. Many things that we’re discussing in this section you can find in our webinar on mitigating Zero-Day Attacks and Shadow IT:
1. Unauthorized Apps aka Shadow IT
One of the key OAuth application security risks is their invisibility to the IT team. That’s why they comprise a large category in Shadow IT. Unless your company has software that detects these applications and reports them immediately, the task of searching for such applications will be a tedious task.
The more employees work in your business, the more unauthorized applications you will have. Here’s an example. An employee wanted to order pizza via the restaurant’s website. They used their corporate account by mistake to log in to this website. Now, a pizza restaurant has an access to a company’s IT system. It has been done unbeknownst to the IT department and it might take much time for them to detect this risk and take necessary action.
Keep in mind that:
- On average, there are 975 unknown SaaS apps that have access to corporate IT systems.
- 80% of workers use SaaS applications at work without notifying IT or getting their approval.
- 77% of workers believe their company can benefit from embracing Shadow IT.
- 35% of employees claimed they had to work around their corporate security policy to do their job.
The discovery of a single application can consume the precious working time of your IT specialists that can be otherwise used on other tasks. And they will spend even more time (up to 80 hours) to application security risks assessment for the business.
How to fight it? Use software that enable you to detect these applications and assess their risks.
2. Data corruption and leak
We discussed above the scope of permissions requested by different applications. Certain permissions enable apps to not only access your information but also modify it. This creates an opportunity for app owners and cybersecurity criminals to steal or corrupt your information without your knowledge.
Here are several examples of app permission scopes detected by SpinOne Application Risk Assessment software:
1. Productivity software for Google
2. Chrome extension
3. Video Conferencing software for Google Workspace™
As you can see, all these applications have access either directly to your files or to different SaaS software that contain your corporate information. This creates a large attack surface.
SaaS applications can damage your data through:
- Exposure, unauthorized editing or deletion due to an internal app error (especially critical in case of mass entry changes.)
- Vulnerabilities exploited by a third-party
- Attack by an application developer
3. Ransomware attacks
Modern cloud ransomware is – in essence – a SaaS application exploiting OAuth. Its scope of permissions includes accessing and editing the entire data you have access to. Check out how it works in Microsoft Office 365 in our video of a live ransomware attack:
Microsoft Office 365 OneDrive Ransomware Attack
Usually, cybercriminals use social engineering to initiate a ransomware attack. Simply put, they trick people into believing that their application is safe and beneficial for them.
4. Zero-day attack
Most applications have vulnerabilities that provide an entry point for hackers. They can be used for the purposes of crime, corporate espionage, cyber wars, and terrorism. And their search is a constant process. How can threat actors exploit them?
First, criminals can use vulnerabilities to get to clients’ data, either stored in target applications or accessed by apps via OAuth. Second, they can implant malicious code into these programs for the following purposes:
- Spying
- Attacks
- Information theft.
Here’s an example of discovered vulnerabilities in an open platform used to build developer portals.
Responsible developers spend much of their time looking for vulnerabilities and fixing them through patches. That’s why you need to look for apps with regular updates.
5. Compliance risks
This category of SaaS application security risks is especially essential for large businesses and companies that operate in highly regulated environments, for example, medical institutions or critical infrastructure. There are several aspects to ponder.
First, the laws can directly limit the country of registration of application creators. Digital data privacy and SaaS data security are relatively new phenomena. That’s why not all countries have laws that govern them. In case of a breach or leak, there will be little to no possibility to hold the application developer accountable for it.
Second, some OAuth applications can keep your information in their own storage. For example, CRMs keep gigabytes of information pertaining to clients and business partnerships. Where do they store the information? Some apps can buy cheap storage in countries that have no data regulations. Meanwhile, the laws of your country can strictly limit the regions where your entries can be stored.
Finally, some application developers make sure that their applications are compliant with standards and regulations like GDPR, SOC, ISO, etc. Meanwhile, others don’t care much about it. As a result, your company uses software that breaches the laws and regulations. The same is true about the Privacy Policy or Terms of Use.
Check out this example of Compliance application risk assessment by SpinOne:
As you can see the developer is registered in the EU or US, where data is strictly regulated. The app is compliant with multiple standards. And it has a Privacy policy. That’s why our software has assigned “low” to the compliance risks.
The key problem here is that when using OAuth access, your employees won’t be checking compliance risks. First, they don’t know about compliance (unless they work in the legal department). Second, it requires additional research and few people know how to conduct it.
6. Operation risks
These SaaS application risks are beyond the concern of Information Technology security. However, we believe that it is important to mention them.
First, working with multiple productivity software tools that perform similar (or the same) functions creates a disruption in business processes. Some information might fall through the cracks as it is passed from one employee to another.
For example, different sales managers use different CRMs to work with their clients. It will be extremely hard and inconvenient for the head of the sales team to gather all the necessary information about their sales pipeline in one document to analyze it and predict revenues.
Second, the lack of centralized control over applications might cause a situation where employees do not make the best acquisition choice.
Let’s say, the employees of a department need a task manager to track their performance. Each chooses the task manager that they are most familiar with. However, it doesn’t mean that the application of their choice will fit the business needs and requirements.
Unfortunately, siloed solutions is one of vulnerabilities of many companies. And IT Department might help fix this problem by creating whitelists of OAuth applications. There are modern cybersecurity software that can do it.
SaaS Application Security Risk Assessment
Usually, people understand SaaS Application Security Risk Assessment in two ways. The first meaning is the risk assessment process carried out by the developer to identify risks and make sure that their product is secure for clients.
The second meaning of SaaS Application Security Risk Assessment is the process of evaluating the potential risks of OAuth apps to the IT system of a company. The Information Technology or SecOps team can carry it out during the acquisition/buying or upon detection.
This article focuses exclusively on the second meaning of the process. Despite the fact that developers’ actions on attaining app security are important, it is critical for businesses to understand and control the risks of the software they use.
The pitfalls of Application Security risk assessments
Regular risk assessments can help the company to minimize risks of breach or leak. They can also help your company avoid any legal implications and financial losses. Unfortunately, this process has its pitfalls.
1. Despite posing a great risk, unauthorized software is oftentimes part of the process.
2. Risk assessment is a very long and tedious process. It takes a lot of resources from the IT team.
3. Finding the proper criteria and organizing the seamless step-by-step process.
4. Lack of knowledge about the available automation software or lack of will to acquire it.
Manual SaaS Application Risk Assessment in Cloud Environments
App seucurity risk assessment can be carried out manually or with the help of special risk assessment apps.
In this section, we will talk about the manual step-by-step process of app risk assessment in Google Workspace™ and Microsoft Office 365. These two office suits are the most used by businesses in the US and outside. Furthermore, their satellite app environments are very big and continue to grow.
Your IT security team should take the following steps of risk assessment:
I. Preparation Stage
At the preparation stage of application security risk assessment, you will be collecting all the information that you need to analyze at the next stages.
1. Outlining legal limitations and requirements governing the use of an application.
Request the information from your legal department. Even if they have provided it before, it’s good to check for updates, just in case. In the best-case scenario, they will join your risk assessment team.
2. Defining application use goals.
You will need this information when you carry out business operations risk assessment. You can cooperate on the goals with the departments that are going to operate the application. It can also help the acquisition team if they have to explore alternatives.
3. Detecting shadow IT.
Investigate if the employees of your company use similar tools unbeknownst to you and their coworkers. This step will enable you to get rid of unauthorized applications. It might also help you find better software for your company.
4. Collect public information about the app in question.
At this stage, you simply get all the information available about the developer and the app, you will analyze it at the next stage. Get all the links in one place (to the website, to the marketplace, to the privacy policy, etc.)
II. Compliance Risk Assessment Stage
We suggest that Compliance risk assessment should be the first step you make after the preparation stage. Starting with it can save you a lot of time and effort. Otherwise, you might dedicate a lot of resources to app evaluation only to find out that the application does not fit your compliance requirements.
3. Check the developer
Some applications are developed by companies, while others are developed by an individual. It might have unwanted legal implications. For example, the ability to hold the developer accountable will be impossible.
In the screenshot below, you can see how SpinOne assigned high risk to an application because it was developed by an individual
4. Check if the developer’s country of registration meets the requirements of your legal department
Usually, you can find such information in the contact section of the application website, their Privacy Policy, or Terms of Service.
5. Find out which standards the application complies with.
The app owners usually display such information on their websites. For example, SpinOne has a special page dedicated to our certifications.
6. Look for a Privacy Policy
This document is critical as it clearly stipulates the rules and procedures of data collecting and processing. It is also legally binding as it is a contract between an app owner and the user.
7. Provide all the above information to the legal department for their revision.
It is better if your legal department reviews all the information you’ve collected and makes its own evaluation.
III. The scope of permissions risk assessment
After understanding that there are no compliance-related application security risks, you can check other potential threats to your information.
8. Check the app’s scope of permissions and analyze if this scope exceeds the performance needs.
For example, the above-mentioned Semrush is a marketing software that enables you to analyze the SEO performance of your page, pick keywords, get domain reports, etc. It doesn’t need to view or edit your Google Workspace™ files. Therefore, if they requested access and edit rights, it would be very suspicious.
Here’s another example. SpinOne platform has backup and recovery functionality. That’s why it justifiably requests access and editing of the documents to be able to copy your files and then restore them.
IV. Security Risk Assessment
At this stage of application risk assessment, you need to check if the app you are evaluating has any potential threats to your sensitive information.
9. Check encryption
If the application in question accesses, edits, and stores your information, you need to find out as much as possible about their methods of encryption. Here’s an example of how we encrypt the data that our customers entrust us with
You might find this type of information on a developer’s website or request them directly via Support.
10. Search for the vulnerabilities discovered in the past
It will show you not only the number of mistakes the developer has made in the past but also if they managed to fix them.
Here’s an example of app vulnerabilities detected by our Application Risk Assessment program:
Obviously, the fact that the company patched previous vulnerabilities doesn’t imply there is still such risk. Nor does it mean there is no more.
V. Business Operations Risk Assessment
Some IT specialists might say that business operation risks are not within their scope of responsibility. However, we believe that their evaluation can benefit not only your business but also the IT team.
For example, you need to justify why you blocklisted an application that your creative team loves so much. High business operation risk can be a more solid argument than security because you will tell them that they are not using the best solution on the market.
11. Check for the number of users and ratings
This stage of risk assessment will help you to understand how the application meets the needs of the users it caters to. Apart from the official Marketplaces, you can also check the ranking websites like G2.com. The presence of an application there will also signify that the vendor is reliable as these platforms usually do an audit of the vendors.
12. Check the developer’s reputation
This information will indicate the readiness of the developer to contribute to the security and development of its apps. Updates often contain new up-to-date measures to protect applications
13. Check the frequency of updates
This information will indicate the readiness of the developer to contribute to the security and development of its apps. Updates often contain new up-to-date measures to protect applications from new threats. Also, they might contain patches for the discovered vulnerabilities. And finally, they bring new features for your employees to improve their work even more.
VI. Make Decision
Upon thorough application risk assessment, you can finally make a decision whether to grant or revoke app access to your Google Workspace™ or Microsoft Office 365 environment.
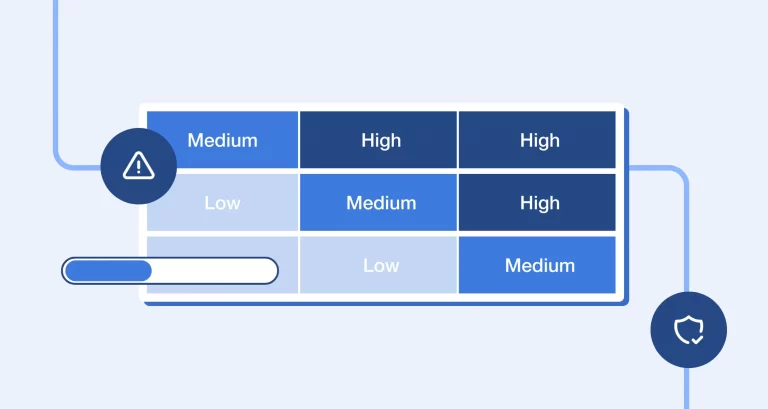
One of the ways to facilitate your risk assessment process is to apply a scoring system. However, we suggest against assigning similar scores to each of the items on the above list.
SaaS Application Risk Assessment Software
One of the biggest issues of SaaS Application Risk Assessment is the time an IT team spends collecting and analyzing all the necessary information. We assessed that doing it manually can take approximately 80 hours.
In large organizations, with thousands of GW and MSO 365 users, the number of OAuth applications is overwhelming for IT teams.
For this reason, we recommend using security risk assessment apps. They can detect every app that has access to your office suite and evaluate its risks within minutes.
Benefits of application risk assessment software:
- Making Shadow IT visible.
- Saving resources of security teams.
- Automating the app request process.
- Creating policies to control applications, e.g. allow/blocklisting.
- Providing comprehensive reports on the apps.
One example of an app risk assessment program is SpinOne. It’s a data protection platform for Google Workspace™ and Microsoft Office 365 that can detect Shadow IT. Check out the functionality in our video:
The functionality of SpinOne includes:
- 24/7 automated detection of OAuth access: apps, websites, and browser extensions.
- Listing all the essential information about an app in one place.
- App security risk assessment based on 15 criteria
- 1-100 Scoring system.
- Allow/blocklisting.
- The functionality that enables revoking access immediately.
- App security policies.
- Functionality to streamline application requests by employees.
- Creating reports and sending notifications.
Learn more about our application risk assessment software for Google Workspace™ and Microsoft Office 365.