SSPM for Microsoft 365
Protect Microsoft 365 Data with Spin SaaS Security Posture Management (SpinSPM)
SSPM Advantages for Enterprise
Get full visibility and fast incident response for misconfigurations and unsanctioned 3rd party apps and browser extensions with SpinSPM, a solution within the SpinOne platform. Reduce security, compliance, and data loss risks while reducing manual workloads.
What Makes SpinSPM for Microsoft 365 Different?
Powerful Assessment Done in Minutes
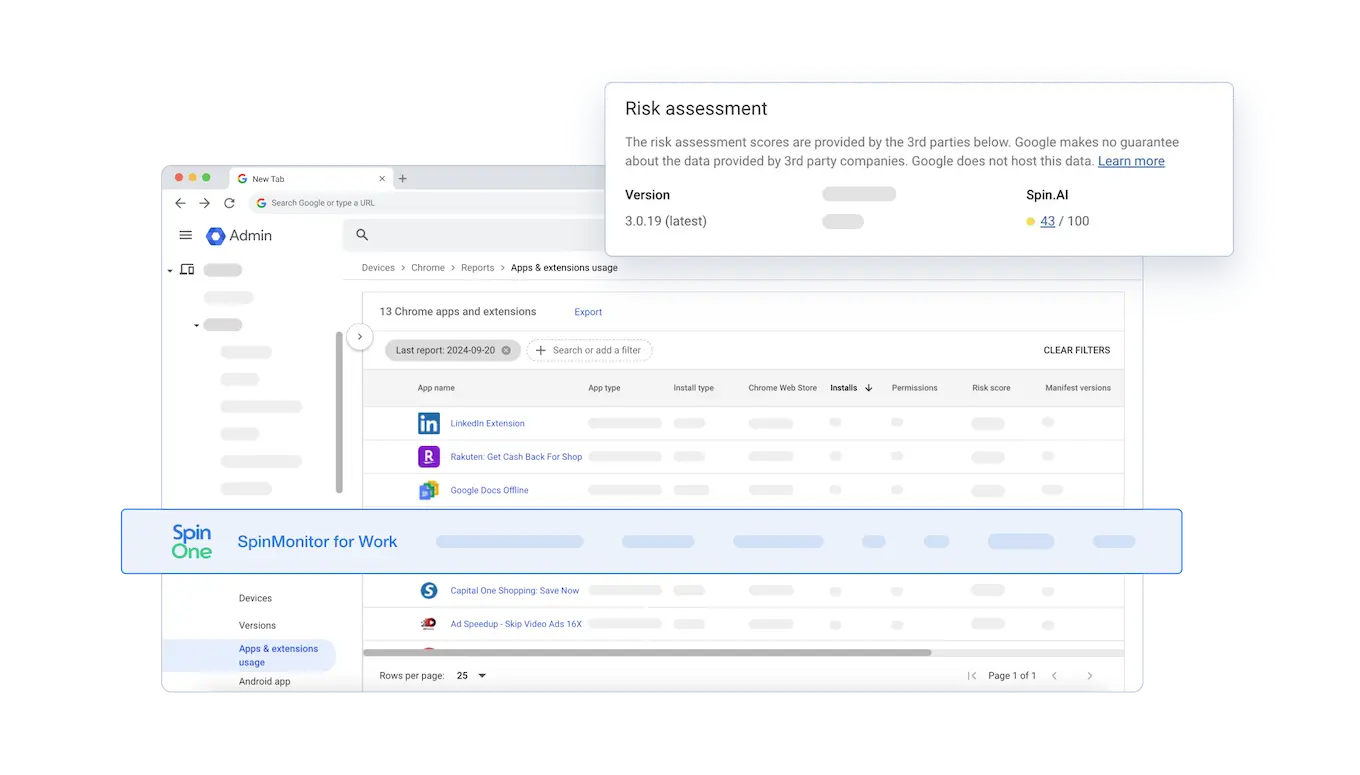
SpinSPM is the only SSPM solution that assesses Chrome browser extension risk for Microsoft Edge and Google Chrome. In fact, SpinOne was selected by Google to be integrated into its Console to assess the risk of sanctioned and unsanctioned browser extensions.
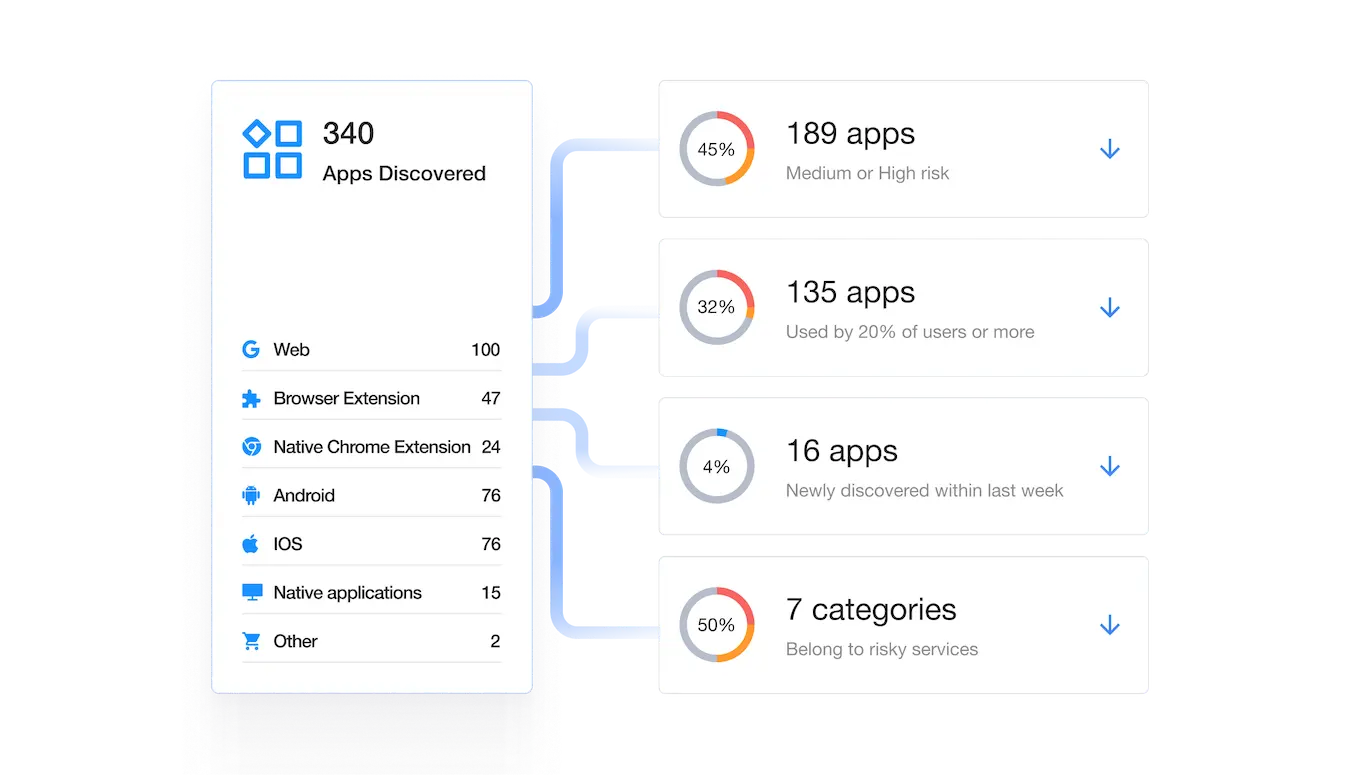
Shadow IT Discovery
SpinSPM has discovered and assessed over 550,000+ OAuth applications and browser extensions using its AI-algorithms, helping organizations reduce risk assessment time from months manually to seconds automatically.
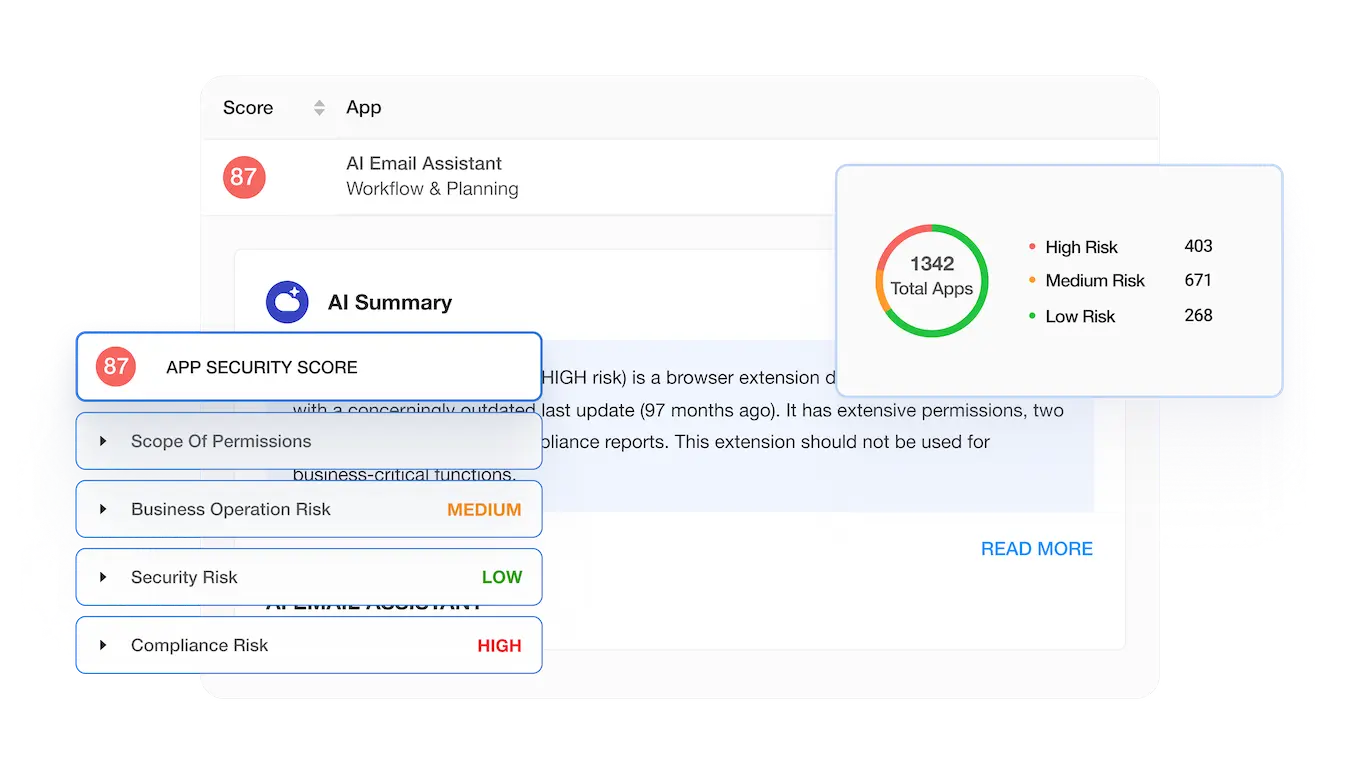
Granular Risk Assessment
SpinOne uses over 15 factors to assess the application and extension risk, and breaks the assessment down into the following sections: scope of permissions, business operation risk, security risk, and compliance risk. Based on this data each app receives a security score from 0 to 100 to zero in on the riskiest applications and extensions and facilitates your decision-making process.



Book a Demo with Spin.AI
Schedule a 30-minute personalized demo with one of our security engineers.
Award-Winning Solution

2x Recognition by
Global Infosec Awards
- Market Innovator Data Recovery
- Market Leader SaaS/Cloud Security


Related Solutions
Application & Browser Extension Risk Assessment Tools
SpinOne is the Platform Behind the World’s Best Security Teams
Frequently Asked Questions
Does Microsoft 365 have any protection against Shadow IT?
No. Businesses, SMBs, and enterprises alike need solutions like SpinOne for Microsoft 365. Our platform detects and assesses OAuth applications and extensions. It also alerts about any apps with high risk.
Why are third-party applications and extensions risky?
Each application and extension has some sort of access to user data. They can have vulnerabilities that cybercriminals exploit or a hidden malicious code that can be triggered at any moment and infect your Microsoft 365 environment or steal your SaaS data.
Is SpinOne safe?
Yes. SpinOne applies functionality to encrypt data in transit, at rest, and in use. It stores backups on cloud storage (AWS, GCP, or Azure).
How does SpinSPM protect Microsoft 365 data?
SpinSPM provides full visibility and fast incident response for misconfigurations and unsanctioned third party apps and extensions helping organizations harden their security posture and minimize risky access to mission-critical SaaS data.
Does SpinSPM for Microsoft 365 scale with the growth of an organization’s SaaS usage?
Yes, SpinSMP is designed to handle large and complex Microsoft 365 environments, scaling to support additional users, applications, and data volumes as the organization expands.
What kind of reporting and analytics does SpinSPM offer to help gain insight into my Microsoft 365 security posture?
SpinSPM offers essential alerts, reports, and analytics on Microsoft 365 security posture on your dashboard. It also supports integrations with Splunk, ServiceNow, Jira, and Slack to receive real-time alerts. Additionally, you can access extensive reports on your SaaS security in real-time or on a scheduled basis.
How many third-party applications can SpinSPM detect?
SpinSPM detects all third-party applications with OAuth access to your Microsoft 365 environment, including applications for collaboration, productivity, project management, CRM, HR, finance, and more.
What is the frequency of your risk assessment updates?
We offer continuous risk assessments. This means that we continuously monitor the Microsoft 365 environment for new third-party apps and browser extensions while also reassessing already installed ones for operational, security, and compliance risks.








