Spin Technology Adds New Security Features to SpinOne Microsoft 365
SpinOne continues to innovate and provide the features and capabilities allowing organizations to stay ahead of the curve in protecting their Microsoft 365 SaaS environments. Let’s recap the new security features introduced this quarter and newly introduced features that help customers to continue to simplify their cloud SaaS operations and cloud cybersecurity initiatives. As ransomware variants and other cybersecurity threats continue to escalate the risks to cloud Software-as-a-Service (SaaS) data, organizations must have the right solutions to protect their business’s data, services, users, and other critical assets. The rapid and accelerated migration to cloud SaaS due to COVID-19 has presented a security issue for many organizations. Unfortunately, many have migrated to the cloud without a real cybersecurity strategy and the proper tools in place to protect their data. Microsoft 365 has seen a massive uptick in adoption since last year, and the trend continues.
Recap of SpinOne Microsoft 365 security features introduced in Q2 2021
Spin has introduced new features for Microsoft 365 customers, helping to provide a better management experience, greater visibility to cybersecurity threats, easier data audits, and additional security controls. These include the following:
- Cloud monitor
- Data audit
- Security policies
- Add-ons
Cloud monitor
What if you had a single area that provides visibility to all monitored activity and allows administrators to quickly pinpoint specific events, filter the log data, export information as needed, and identify incidents? SpinOne Cloud monitor provides this functionality, giving cloud administrators a tool that empowers them to have excellent cybersecurity visibility without searching numerous dashboards and tools.
Cloud Monitor contains two child dashboards. These include:
- Activity log – provides a view of all monitored activity captured by Spin
- Incidents – cybersecurity incidents captured by SpinOne that have breached security policies
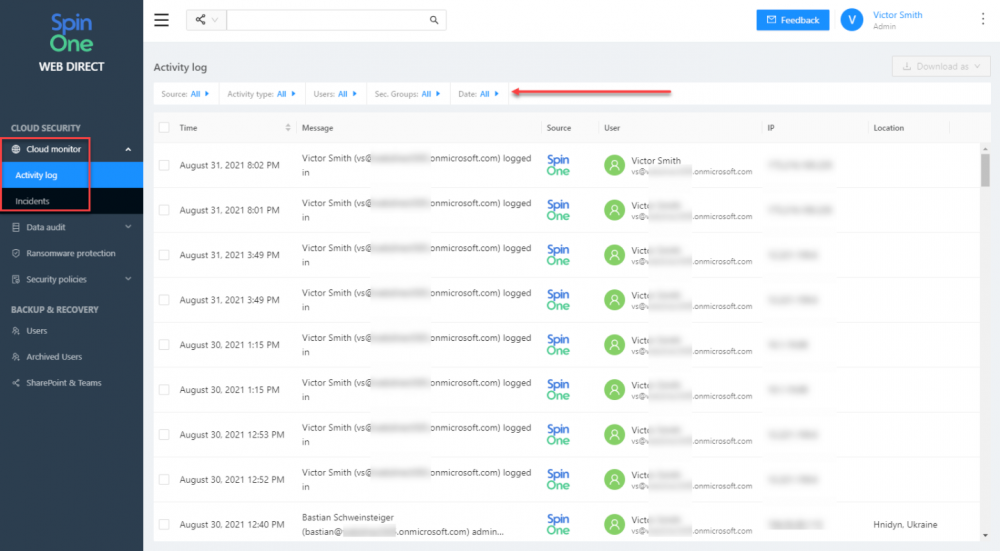
As you can see below, the Cloud Monitor Activity log provides a global view of all activity. You can easily see timestamps, activity recorded, source, user, IP address, and IP geolocation information. Also, note the filter menus at the top of the screen. These allow quickly pinpointing specific data types.
SpinOne Cloud monitor activity log
Note that you can see not only SpinOne specific information but also Microsoft 365 specific information and events.
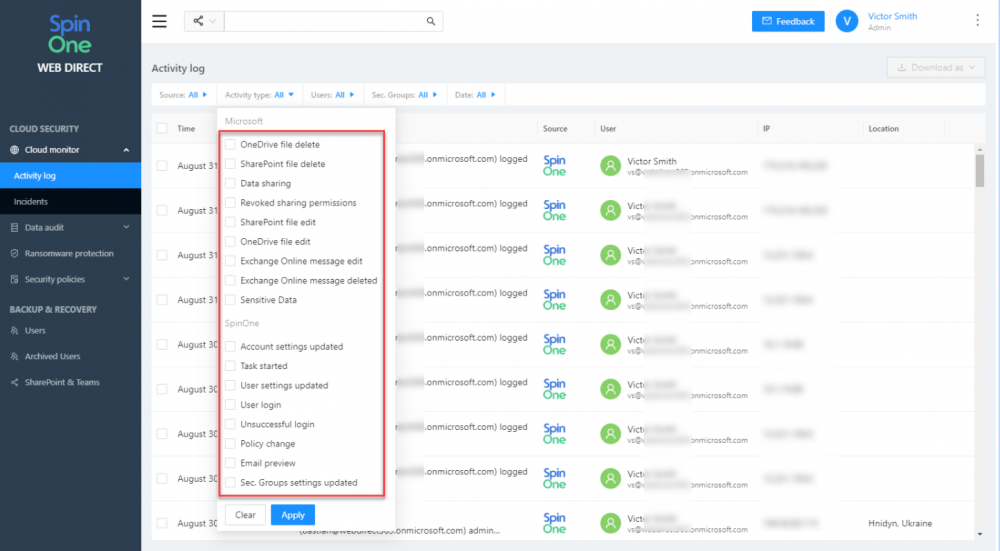
Filtering the activity type in the activity log of the SpinOne Cloud monitor
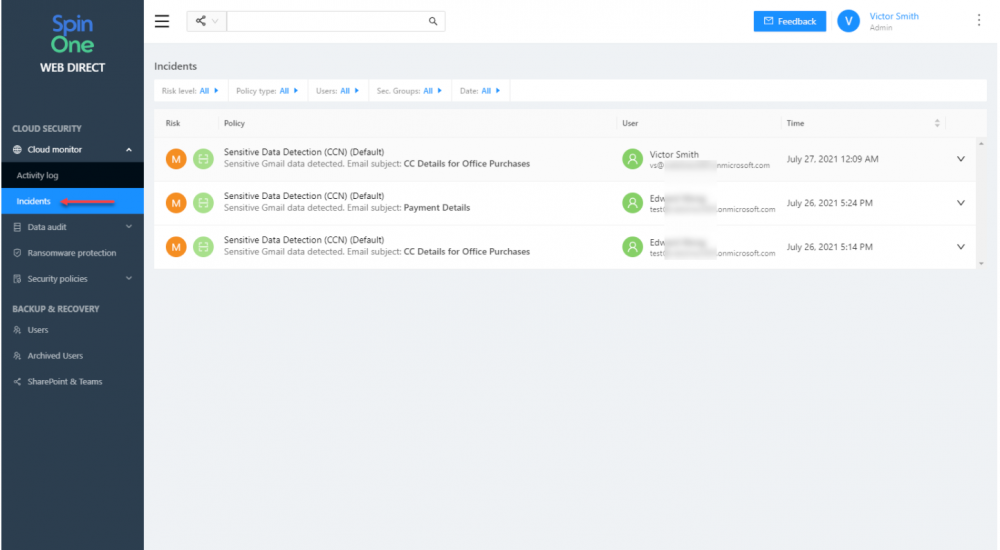
In the Incidents dashboards, you can get to the events that many cloud administrators will be keenly interested in – cybersecurity policy events. These events include:
Viewing the incidents in the SpinOne Cloud monitor
Data Audit
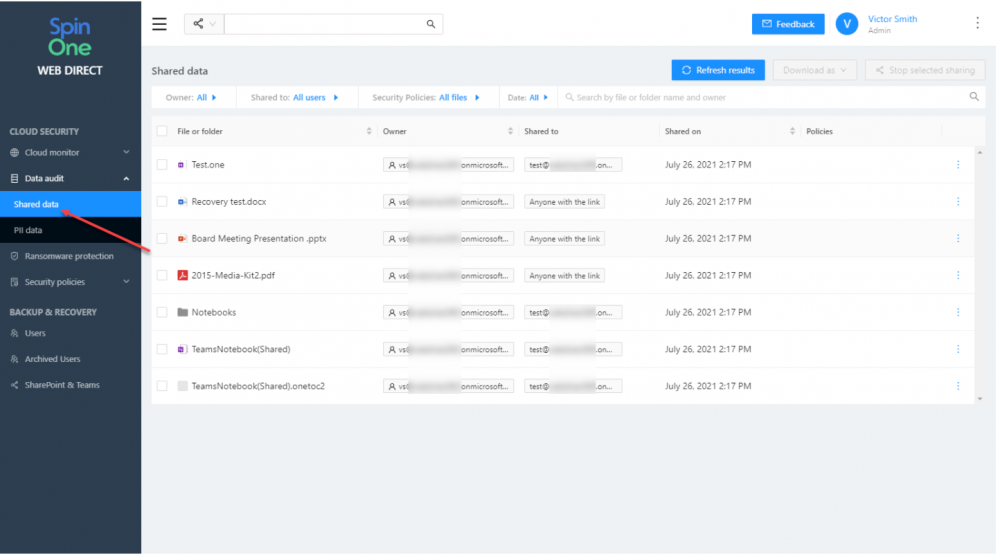
Due to data leakage and regulatory concerns, businesses today must maintain control of data sharing. SpinOne makes this monumental task exponentially more manageable with the Data audit dashboard. Using the Data audit dashboard, organizations can retain visibility on confidential information shared outside the organization.
Data audit displays OneDrive shared data and allows seeing the file or folder shared, the owner of the resources, to whom they are shared when they were shared, and any policies applied. In addition, administrators can easily revoke access to the shared resources.
SpinOne Shared data audit
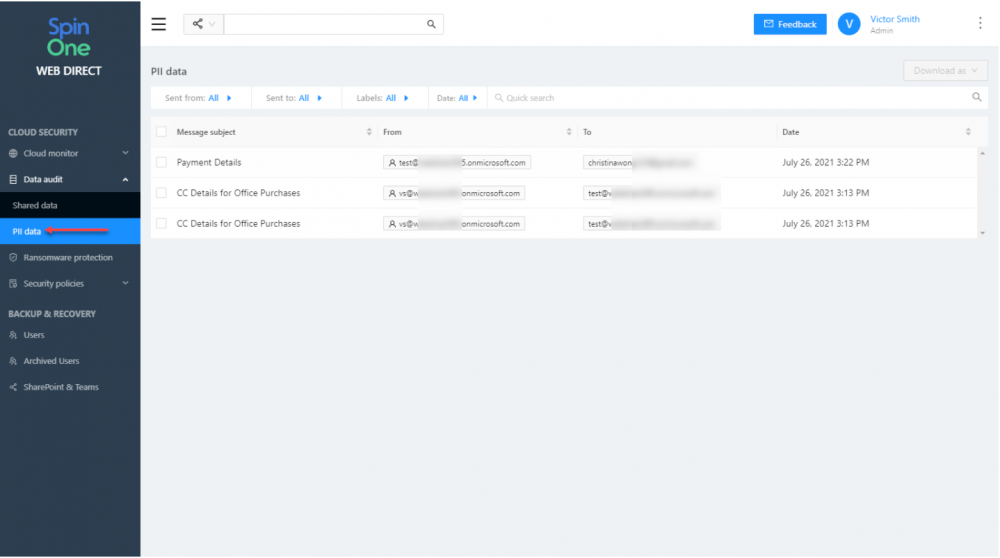
It goes a step further than simply identifying confidential data. It also classifies data that contains Personally Identifiable Information (PII). If emails are sent or received containing CCNs, SpinOne captures the information in a redacted state for auditing.
SpinOne PII data audit
Security Policies
With the brand new security policies, cloud administrators can create cybersecurity policies that control such security processes as:
- Ransomware protection
- OneDrive Sharing Visibility and Control
- Sensitive Data Detection
- Restore Filtration
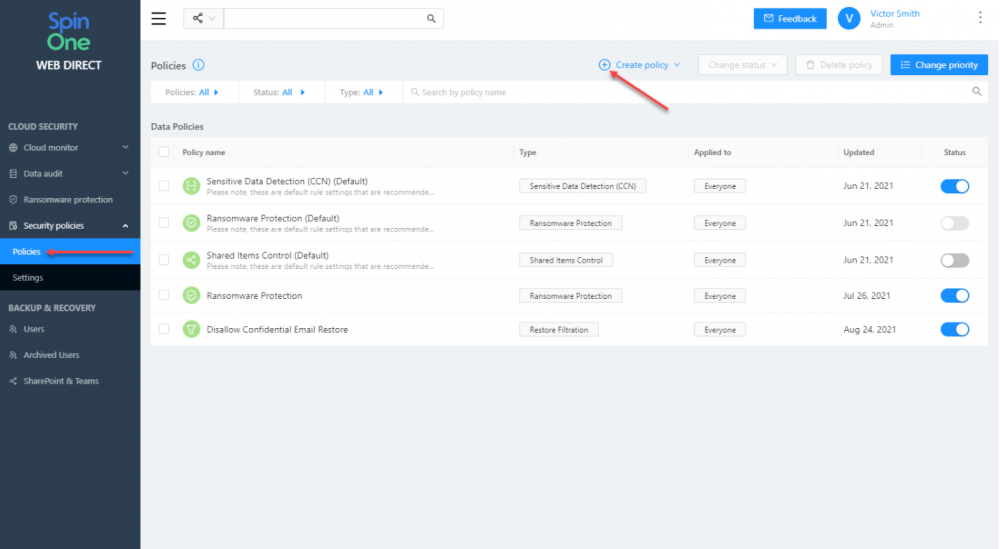
In the security policies screen, you can create new security policies, set the type of policy, the scope of users it is applied, and enable or disable the policies.
SpinOne Security Policies configuration
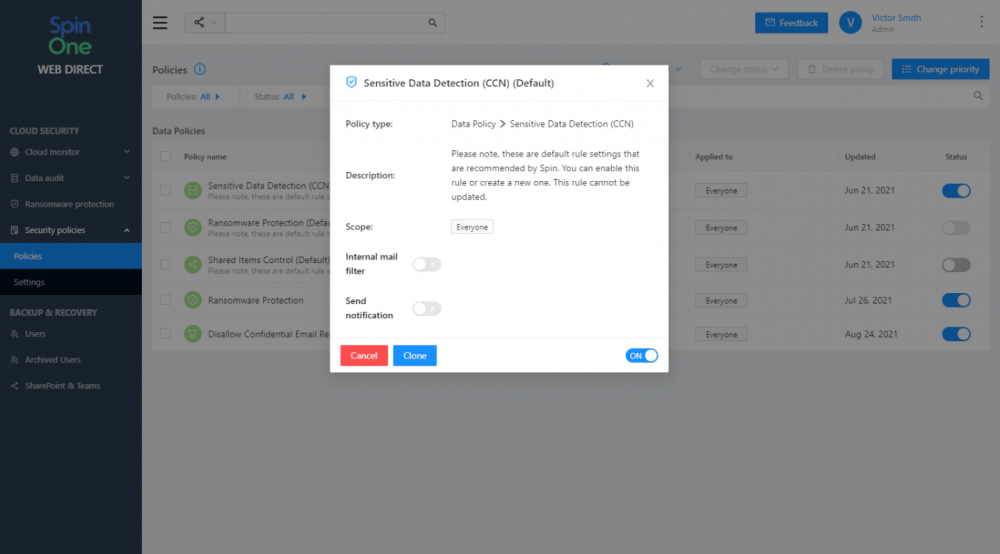
By clicking on an existing policy, these can be reconfigured or tweaked as needed. You can also clone existing policies to quickly use an existing policy as a template for a new policy.
Configuring an existing SpinOne Security Policy
Add-ons
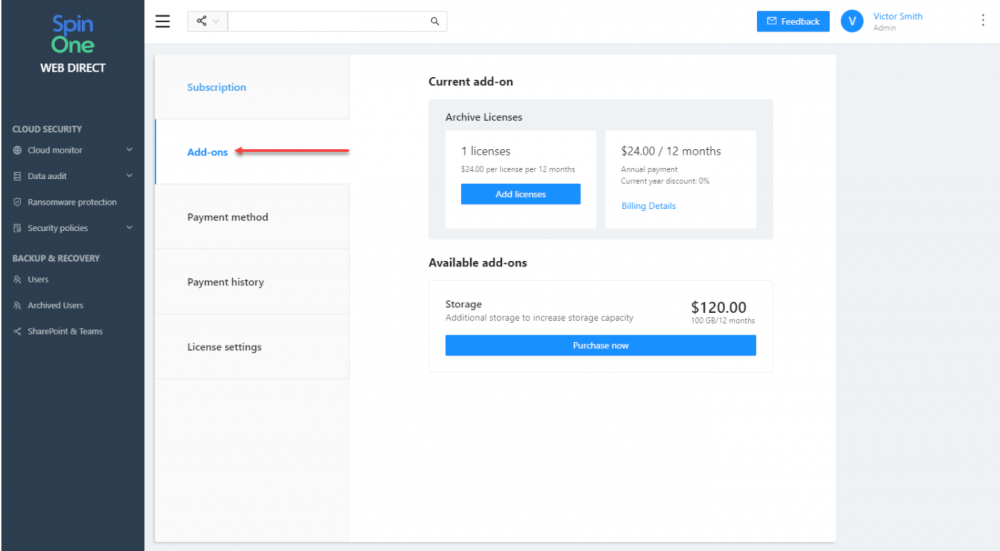
From a management and flexibility perspective, the new Add-ons feature found in your SpinOne account billing section provides a way to take advantage of the additional backend store and infrastructure offered by Google Workspace™ and Microsoft 365.
These include:
- Archive licenses- A cost-effective license that allows retaining terminated employee data
- One Automated Backup
- Unlimited Manual Backups
- Unlimited Download
- Unlimited Restore
- Unlimited Storage
- Access to the latest Snapshot
- Storage – With the storage add-on, you can increase your overall account storage capacity. Businesses can upgrade their storage capacity at any time to avoid exceeding storage limits.
Viewing SpinOne Add-ons
New Security Features introduced for Microsoft 365
In addition to the new features released in the 2nd quarter of 2021, Spin is introducing three new features in SpinOne for Microsoft 365. These include the following:
- Browse the full OneDrive folder structure for restores
- PST Export for Exchange Online
- Increased storage from 30GB to 50GB for paid SpinOne customers
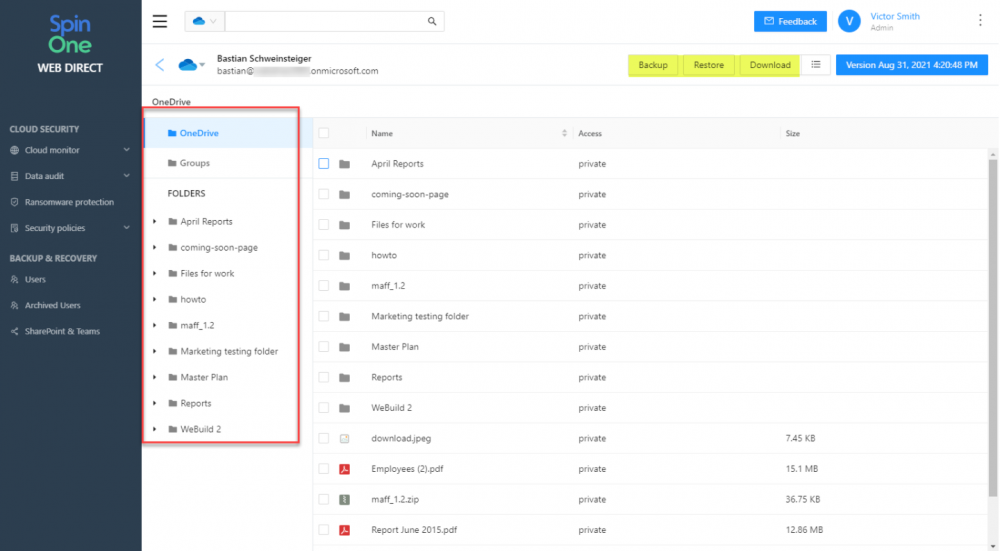
1. Browse the full OneDrive folder structure for restores
With this new feature, Spin is making it even easier for cloud administrators to quickly browse the folder structure of user’s OneDrives, locate and restore information. This new feature leads to simplified operations, quicker restores, and less downtime.
Browse the folder structure for OneDrive in SpinOne file restore
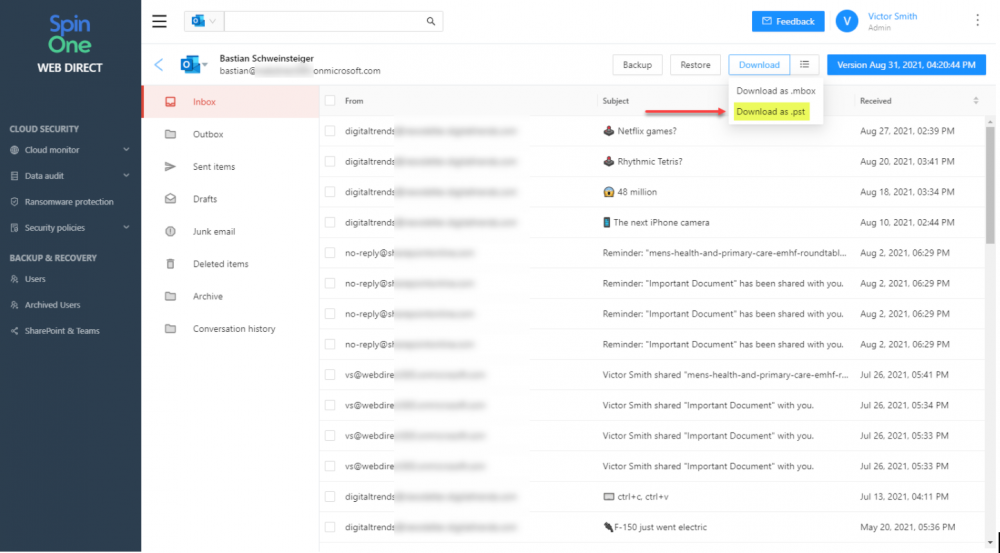
2. PST Export for Exchange Online
For decades in the enterprise, the PST file has been a standard file format for extracting emails and providing these for many different purposes, such as mounting these locally on a laptop or desktop device. SpinOne is now making it easy for cloud administrators to extract copies of cloud emails as this standard file type.
SpinOne allows cloud administrators to download Exchange Online emails as a PST file
3. Increased storage from 30GB to 50GB for paid SpinOne customers
For SpinOne paid customers, each license now provides 50 GB of storage, an upgrade from the previous 30 GB capacity. For other subscriptions, it remains the same. With this increase, Spin is providing even better value to customers and those who are looking to protect business-critical data in the cloud. As a note, this is also available for existing customers, but only those who are on the current $9 user/month SpinOne subscription plan.
Wrapping Up
Never before have cybersecurity concerns and data protection been more critical. As a result, businesses must use a capable cybersecurity and data protection solution that provides the features and capabilities that meet modern cybersecurity challenges head-on. SpinOne continues to innovate, providing better cybersecurity visibility, ransomware protection, and data protection than competitors at an economical price point.