Your SSPM checklist
Security and compliance are your top priority in a SaaS environment. Even apps that are secure at one point may drift away from proper configurations, introduce leaky data sharing, or install dangerous third-party SaaS apps. SaaS Security Posture Management (SSPM) helps your company meet the challenges of SaaS head-on and secure cloud SaaS data.
What is SaaS Security Posture Management (SSPM)?
What is SSPM, and why is it so important for organizations using cloud SaaS today? SSPM comprises a suite of tools that provides automated visibility and scanning of configurations, settings, and permissions to ensure these are configured according to security and compliance best practices.
These automated tools save unimaginable manual hours for SecOps professionals since SSPM can carry out the tedious manual tasks of analyzing configurations and continuously scanning for security and compliance risks.
Understanding SaaS security posture is incredibly important as it helps organizations understand their vulnerabilities and how these can be corrected. As all SSPM solutions are not created equal, it is important to understand what features should be found in a modern SSPM solution.
Creating your SSPM checklist
- Evaluate data that isn’t protected
- Provide visibility to data sharing
- Detect and remediate malicious threats
- Harden SaaS configurations
- Evaluate the risks of SaaS apps
1. Evaluate data that isn’t protected
As data is moved to cloud SaaS environments, unprotected data can become a blindspot for many businesses housing critical services in cloud SaaS. Can unprotected data be easily identified? Are all user’s mailboxes and cloud storage locations protected? SSPM solutions can help determine which data exists in SaaS environments and which ones may not be included in cloud-to-cloud backups.
2. Visibility to data sharing
A definite risk posed by cloud SaaS environments comes from the ease of data sharing. By default, most cloud SaaS providers allow all users to share data with anyone. As a result, users could inadvertently share sensitive information outside the organization with third-party users, leading to data breaches.
A single data leak can cost organizations millions of dollars in legal fees, regulatory fines, lost customer confidence, and damaged business reputation. SSPM solutions can help monitor data-sharing configurations and the actual data shared internally and externally.
3. Detect and remediate malicious threats
With the multitude of API requests and user activities that result from day-to-day cloud SaaS access by many different users, it can be a challenge to distinguish normal activity from potentially malicious activity or applications. SSPM solutions can not only help increase the security posture of SaaS configurations, but they can also help identify anomalous activity that may go undetected otherwise.
Modern SSPM solutions can help sift through the noise of everyday SaaS activity with machine learning models and provide deep, intelligent, contextual analysis of activities. SSPM solutions can not only detect anomalies and malicious activities, but they can also trigger robust automated security responses to these activities.
4. Harden SaaS configurations
Permissive cloud configurations or misconfigured SaaS application settings can lead to extreme risk for organizations utilizing SaaS apps. However, manually auditing all the core cloud SaaS configuration settings and individual third-party app settings can be extremely tedious. SSPM solutions can provide an effective means to audit the multitude of cloud SaaS and third-party application settings.
5. Evaluate the risks of SaaS apps
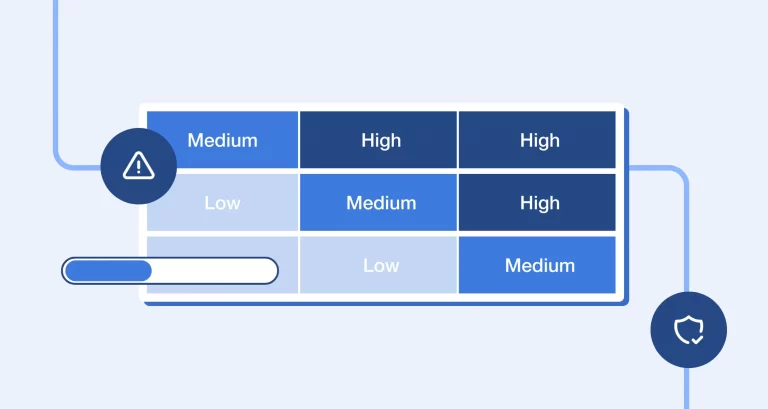
Performing a risk analysis of all third-party cloud SaaS apps using manual efforts is virtually impossible without adequate security and risk automation. SSPM solutions can offer automated risk assessments of the thousands of cloud SaaS applications, allowing organizations only to integrate specific apps that align with their security and compliance needs.
Spin.AI for SSPM
Spin.AI provides a state-of-the-art modern SaaS Security Posture Management solution allowing you to easily monitor and effectively audit SaaS apps. It offers powerful features, including the following:
- Audit your SaaS data and identify which data isn’t protected in cloud backups
- Perform automated risk assessments of third-party SaaS apps
- Complete visibility of all data shared in the organization with the ability for admins to stop data sharing at any time in a granular way
- Fully automated ransomware protection – automatically detects and fully remediates a ransomware attack with security automation, even automatic data restoration if needed
- Eliminate the risk of shadow IT operations with allow and block lists of SaaS apps
- Global security policies that drive security automation in the SaaS environment
- Visibility of all user activities, both from the cloud SaaS environment and SpinOne
Spin.AI helps level the playing field for organizations moving their data to SaaS environments, helping them meet the security and compliance challenges they face with their business-critical data.
Spin’s modern SSPM approach leverages the power of artificial intelligence (AI) and machine learning (ML) to perform the heavy lifting, so your SecOps team has the visibility and controls needed to protect the environment.
If you want to speak with a Spin Solution Engineer to discuss how Spin.AI helps protect your environment from malicious apps and browser extensions, click here.