Spin.AI: SaaS security solutions that protect and recover your data — fast
Protect Google Workspace, Microsoft 365, Salesforce, and Slack from ransomware, data loss, misconfigurations, insider threats, and risky third‑party apps. One AI powered SaaS apps security platform.
Less complexity. Real outcomes.




Recommended by

Trusted by over 1,500 organizations across 100+ countries




What Spin.AI SaaS security software does
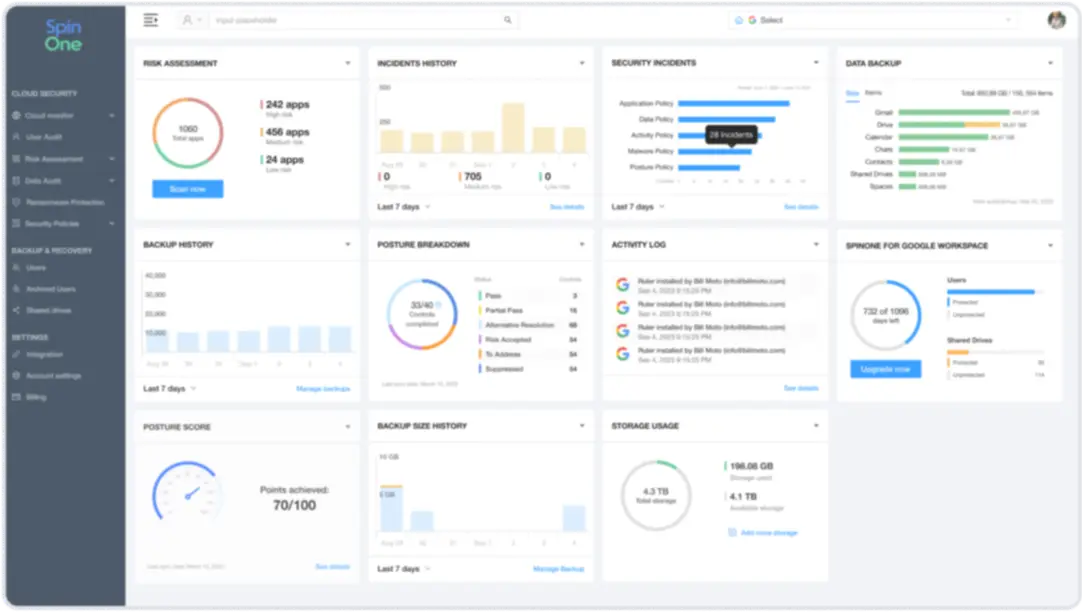
Our solutions secure, back-up, and recover your mission-critical Software as a Service data—in one unified platform—or start with just the solutions you need. SpinOne is our all-in-one SaaS security and data protection solution with automated backup, ransomware detection and response, archiving, and eDiscovery. SpinSPM is our SaaS Security Posture Management (SSPM) to find and fix misconfigurations before they turn into incidents, as well as manage all 3rd-party apps and extensions your users attempt to install. SpinCRX is our enterprise browser security solution to control risky extensions and stop browser-to-cloud data loss. We have everything you need to protect SaaS, working together by design.
SaaS Security & Data Protection Platform
Protect SaaS data for Google Workspace™, Microsoft 365, Salesforce, and Slack–all in one dashboard
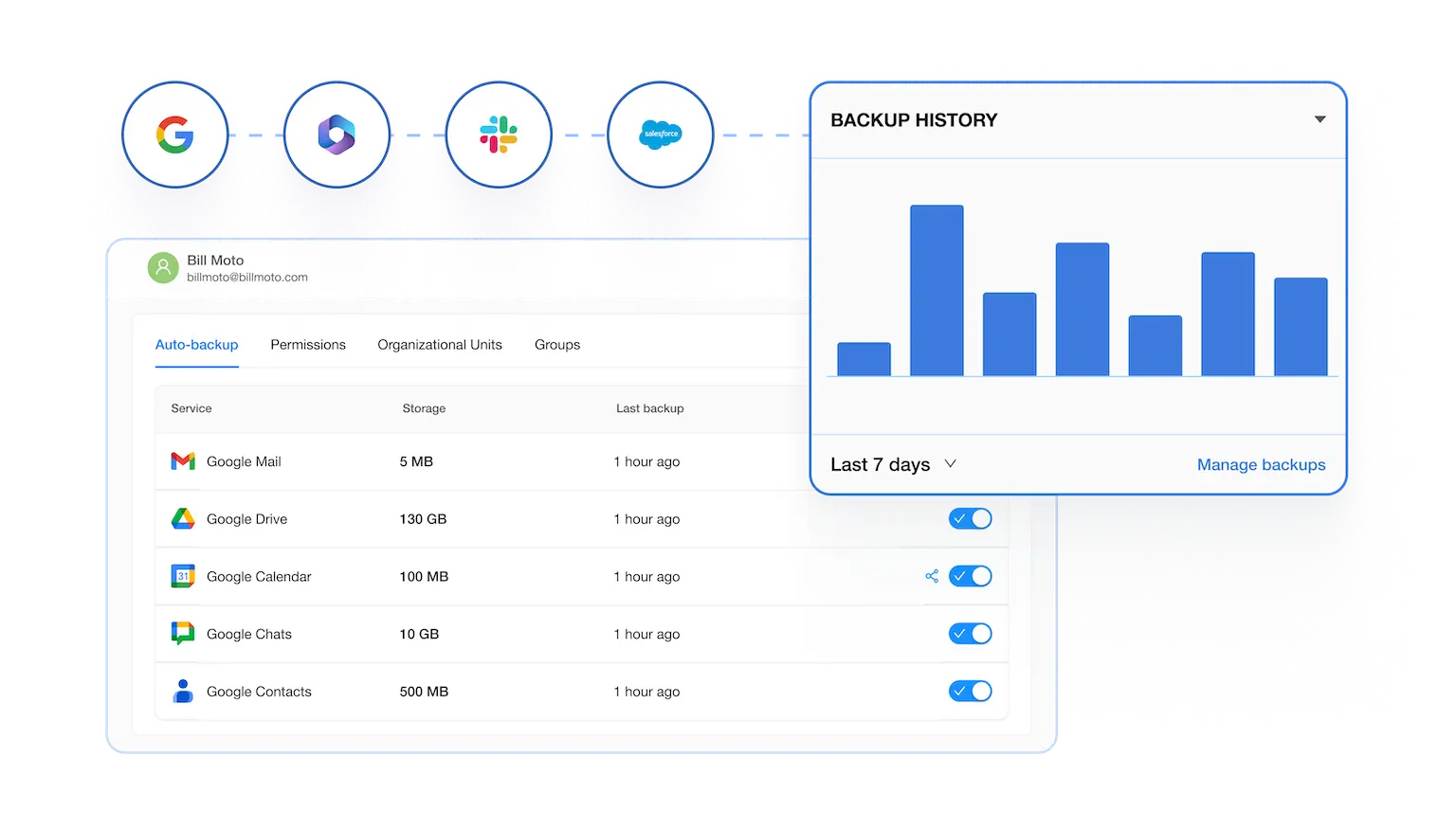
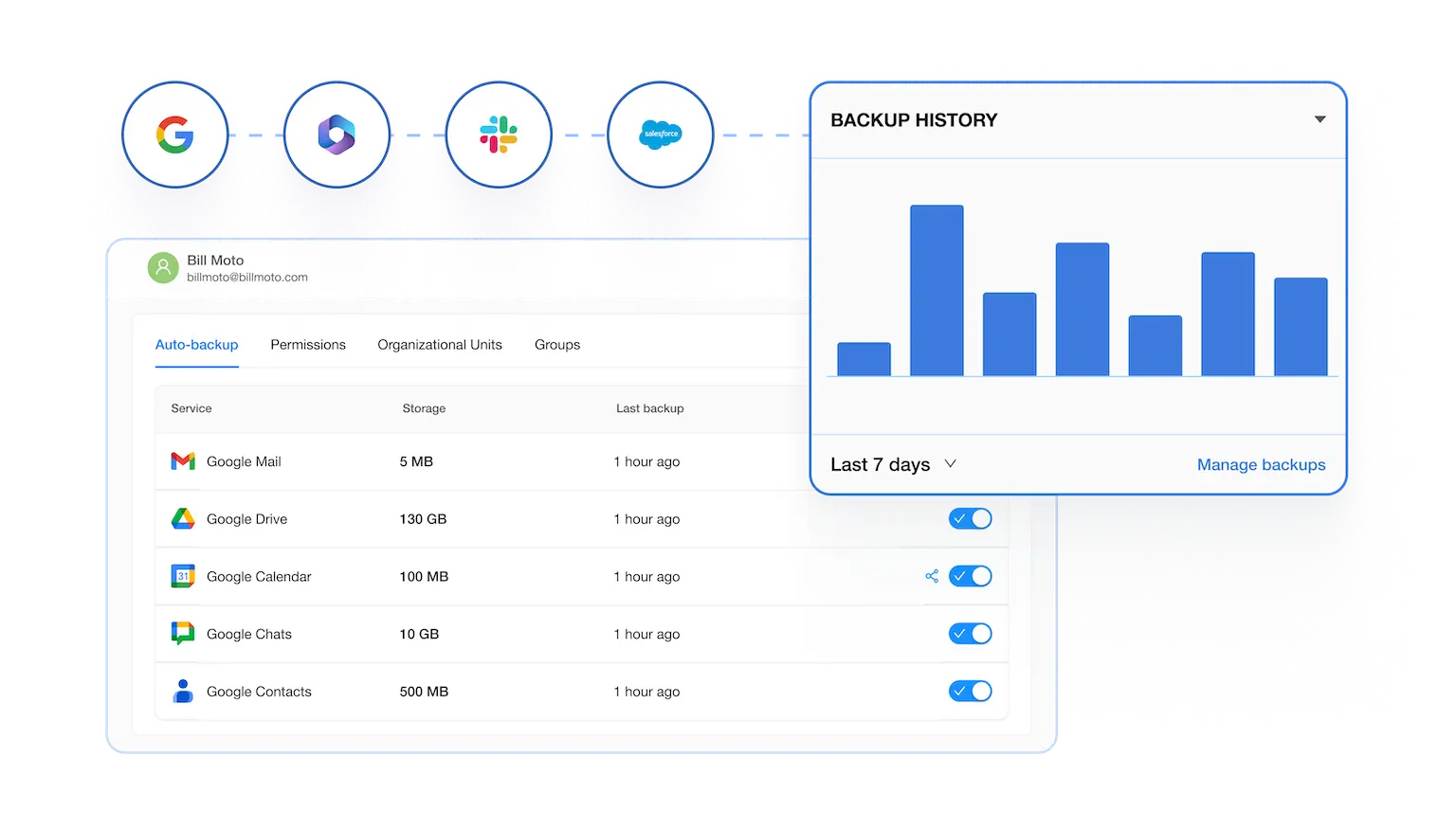
SaaS Backup & Recovery with Ransomware Protection
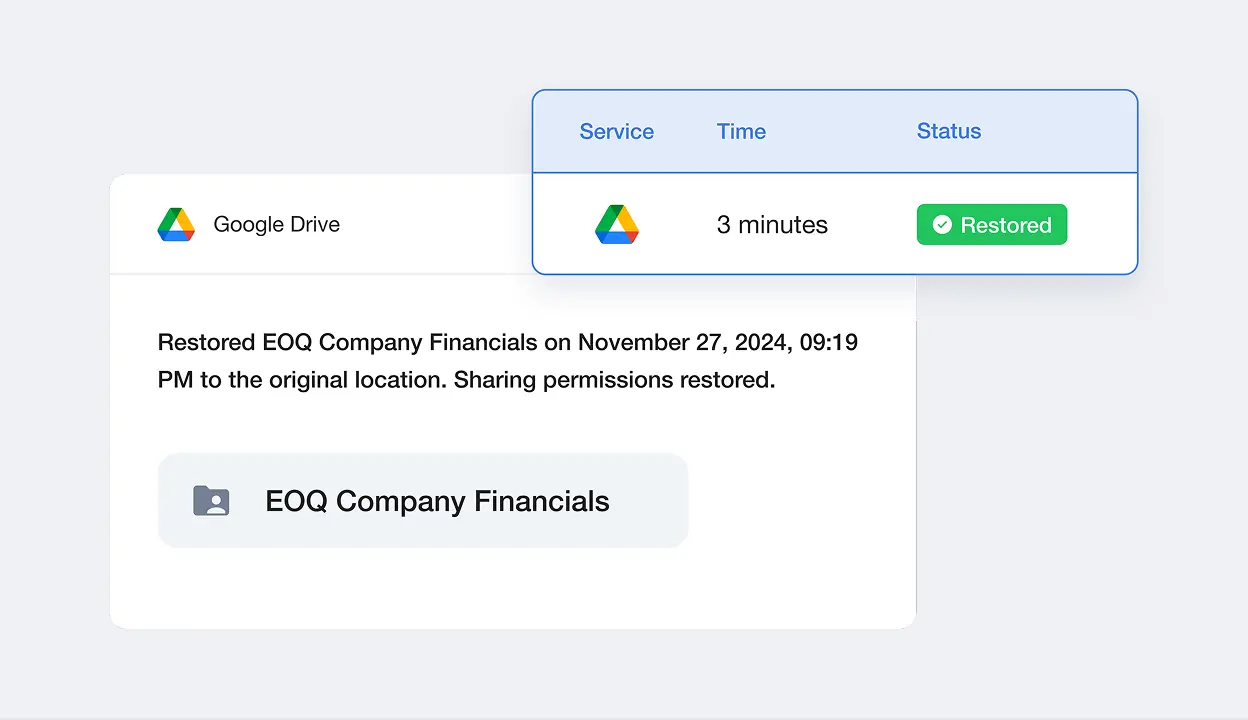
Increase cyber resiliency with automated, 3x daily backup for your SaaS data. Detect and stop SaaS ransomware attacks in real-time. Reduce downtime to less than 2 hours instead of weeks or months with the industry’s fastest SLA.
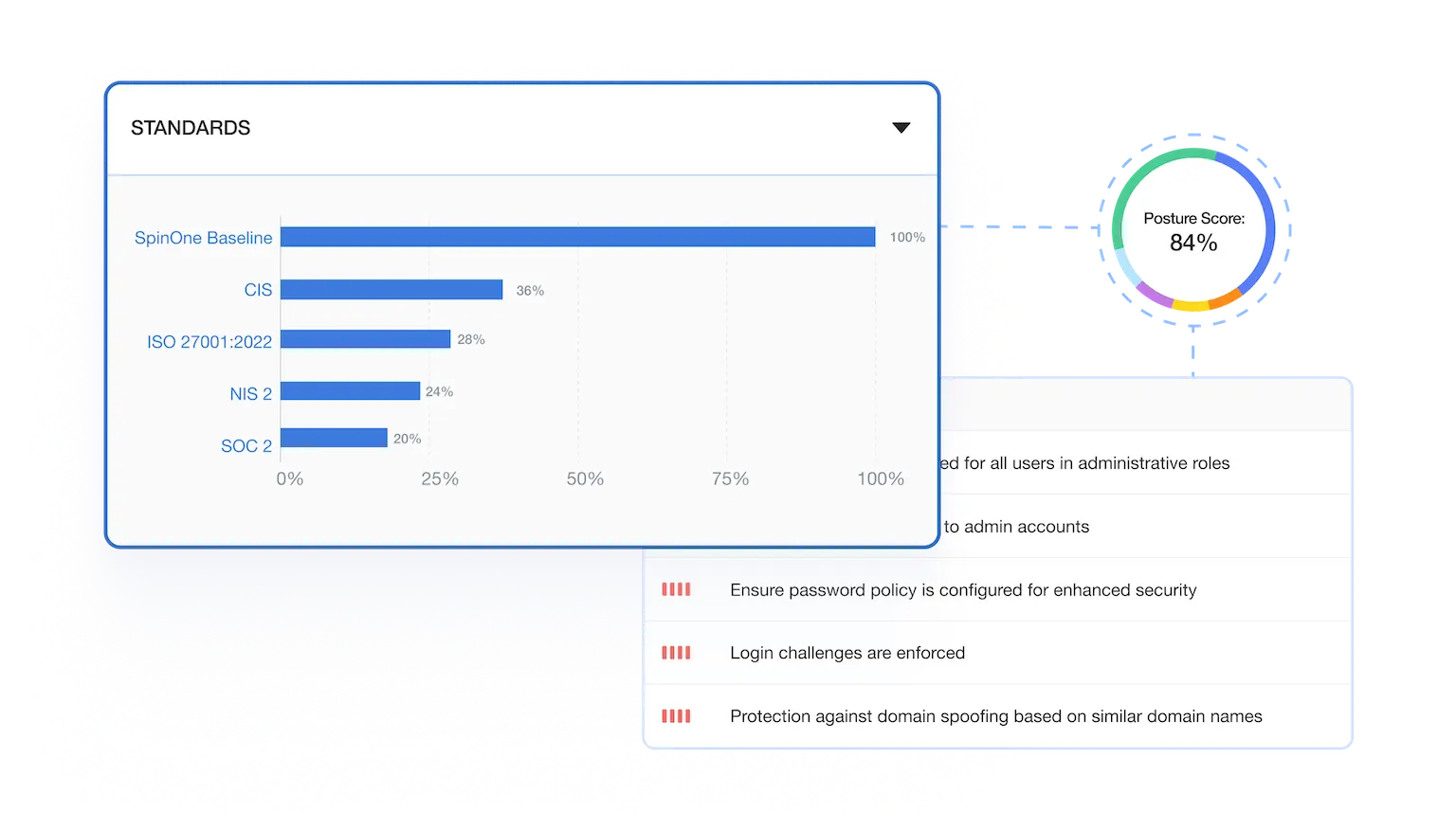
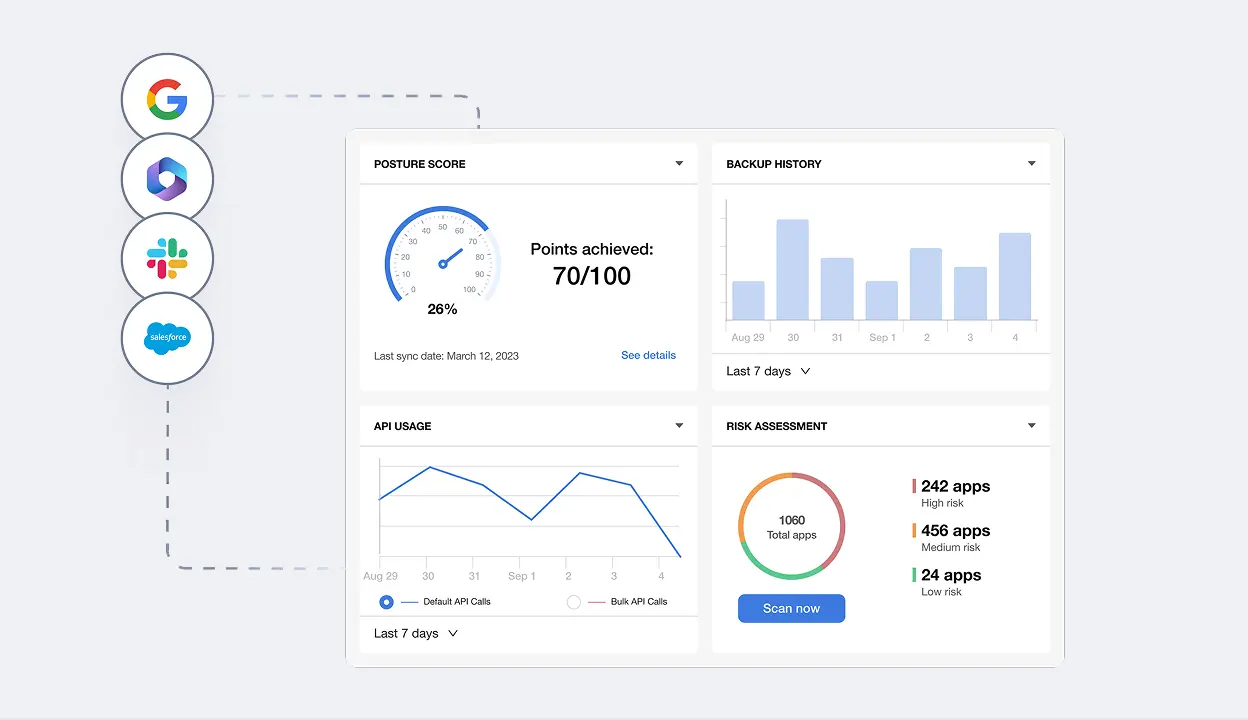
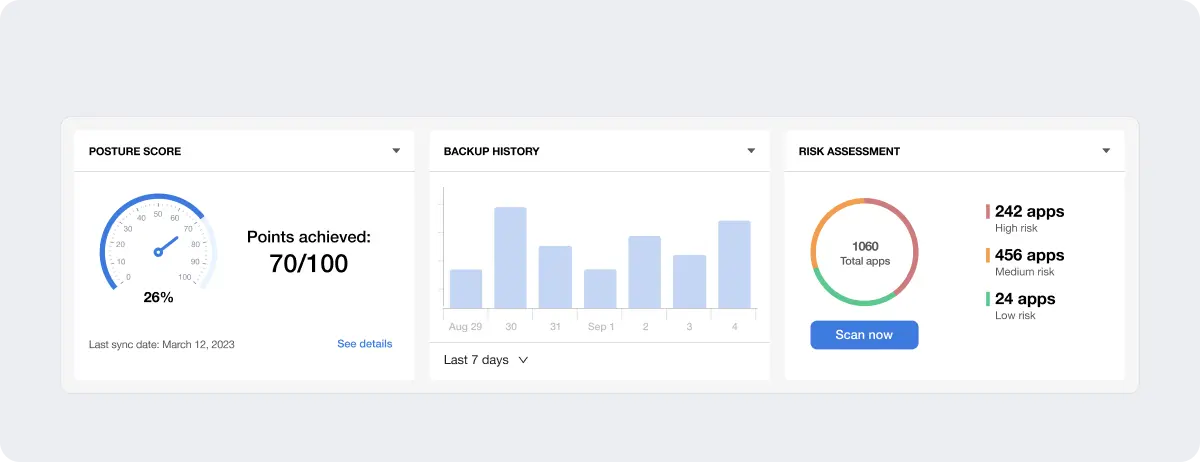
SaaS Security Posture Management (SSPM)
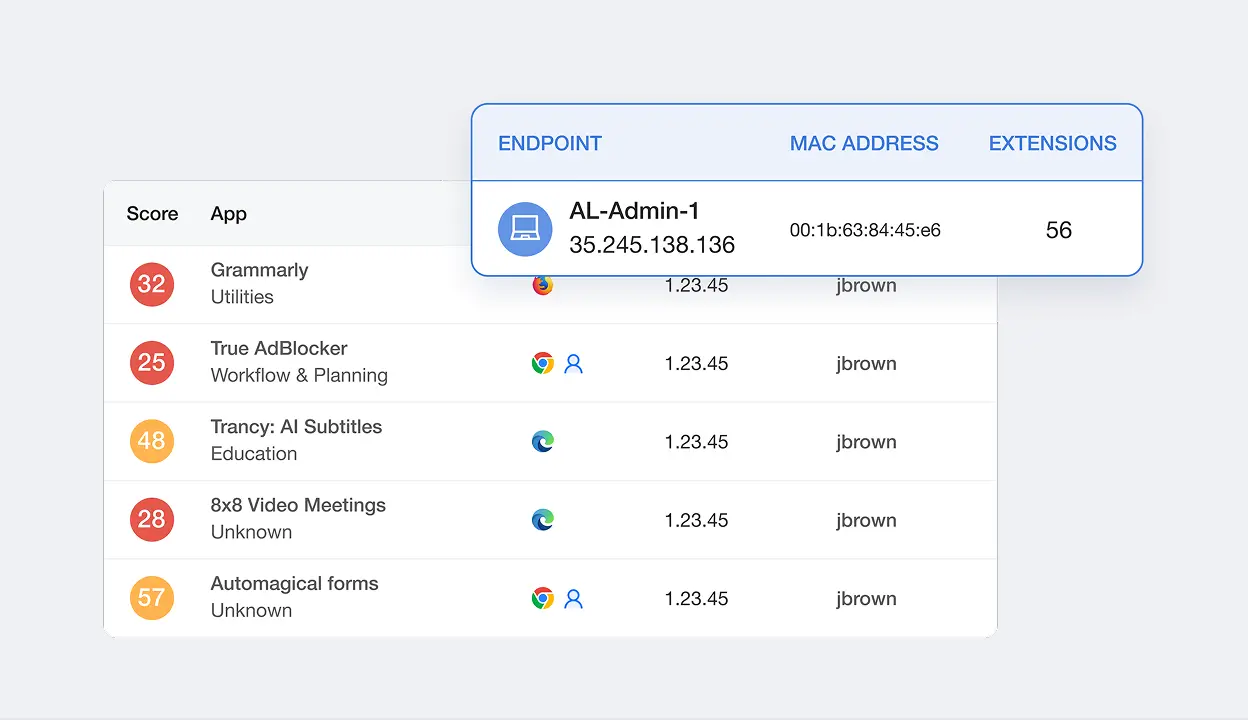
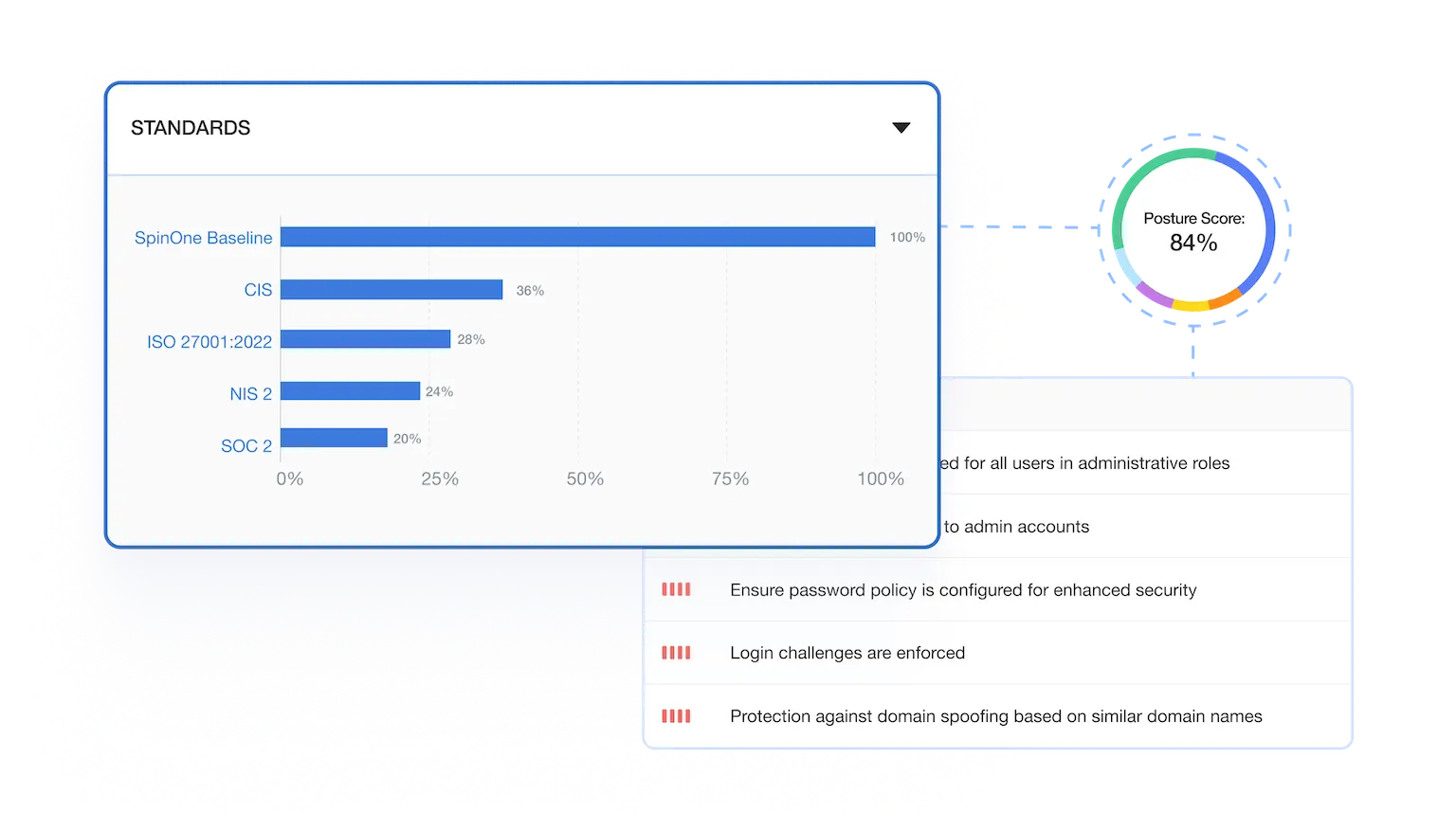
Get full visibility and fast incident response for SaaS misconfigurations, risky users, unsanctioned apps, and malicious browser extensions. Improve your posture score by up to 80% while increasing compliance.
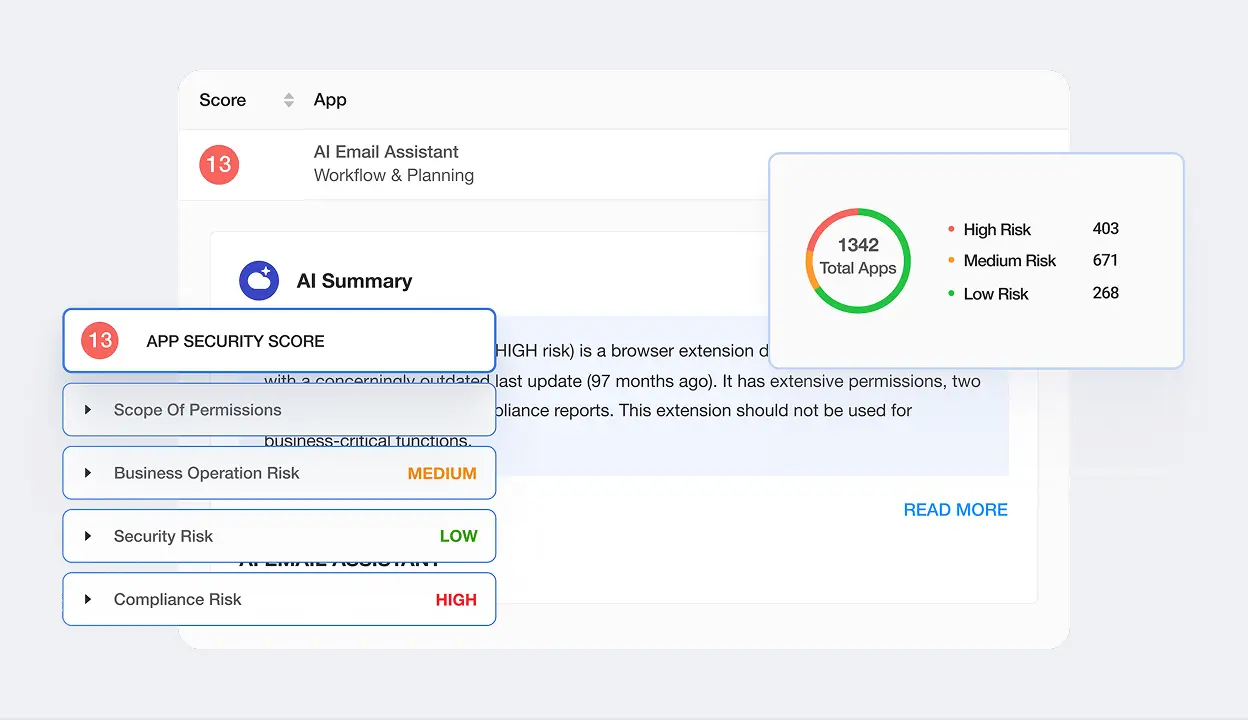
Browser Security
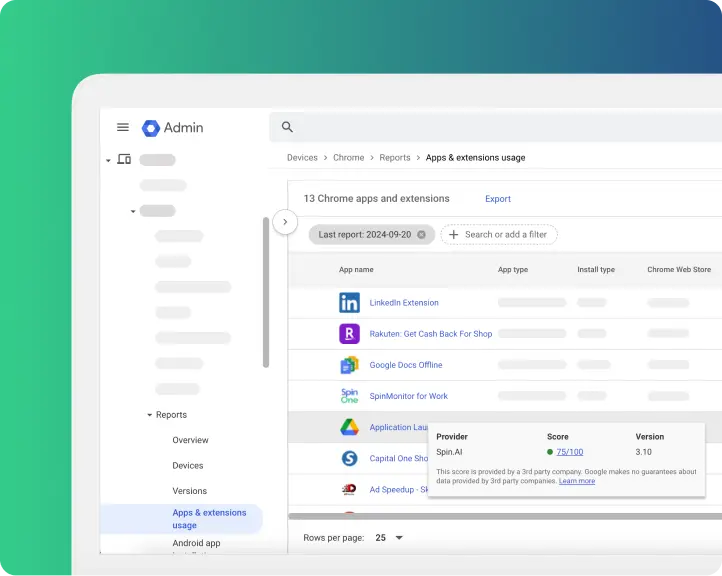
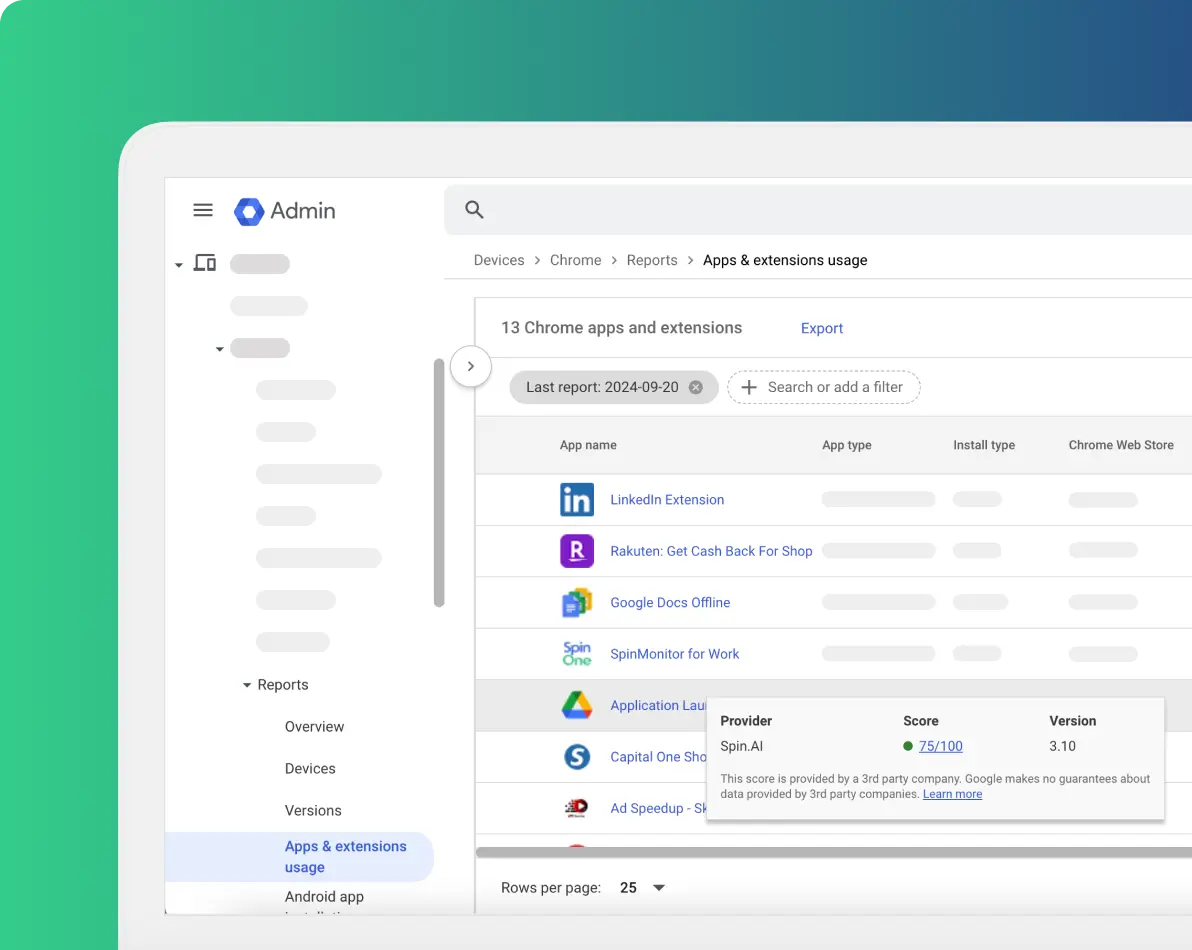
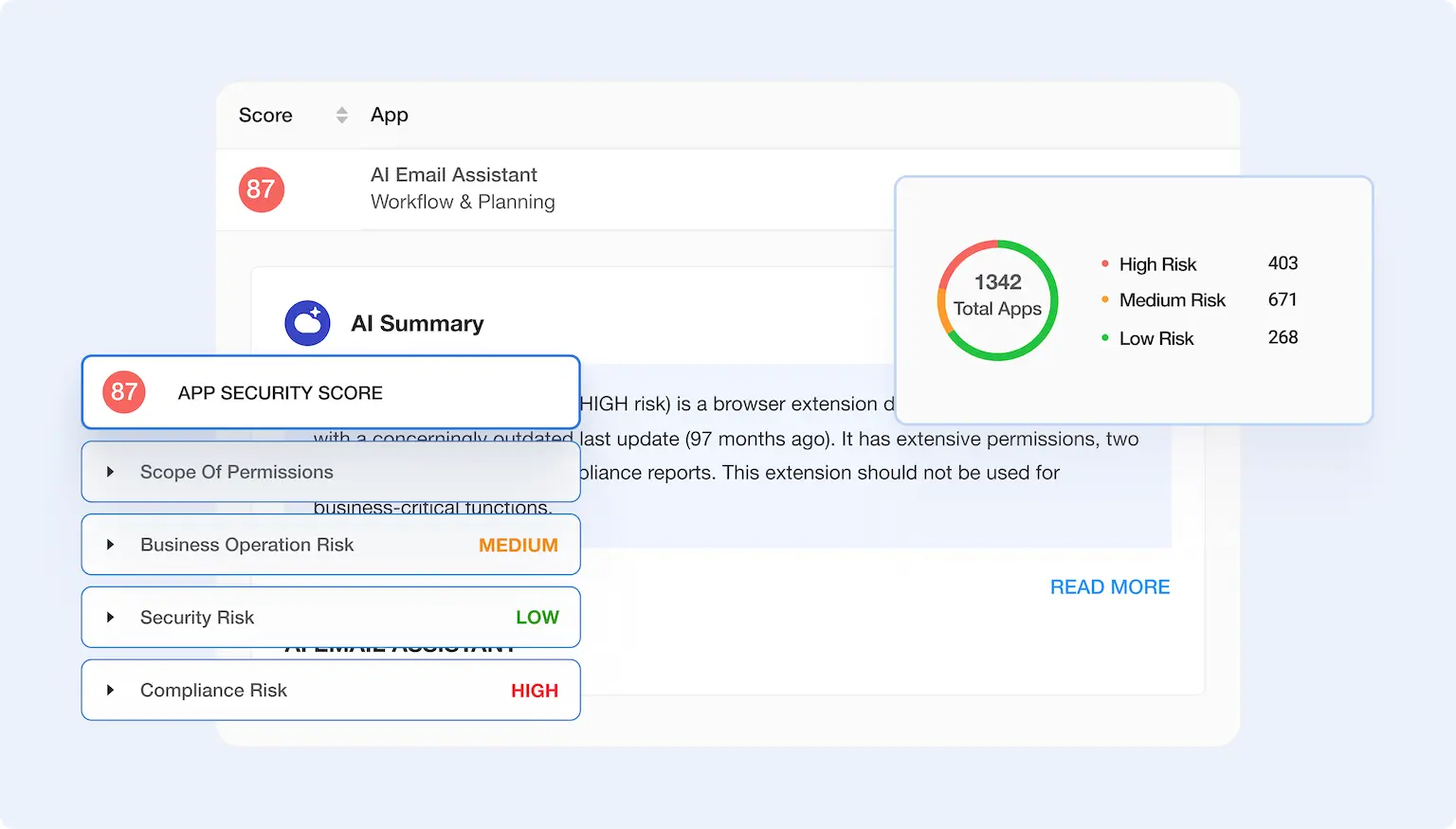
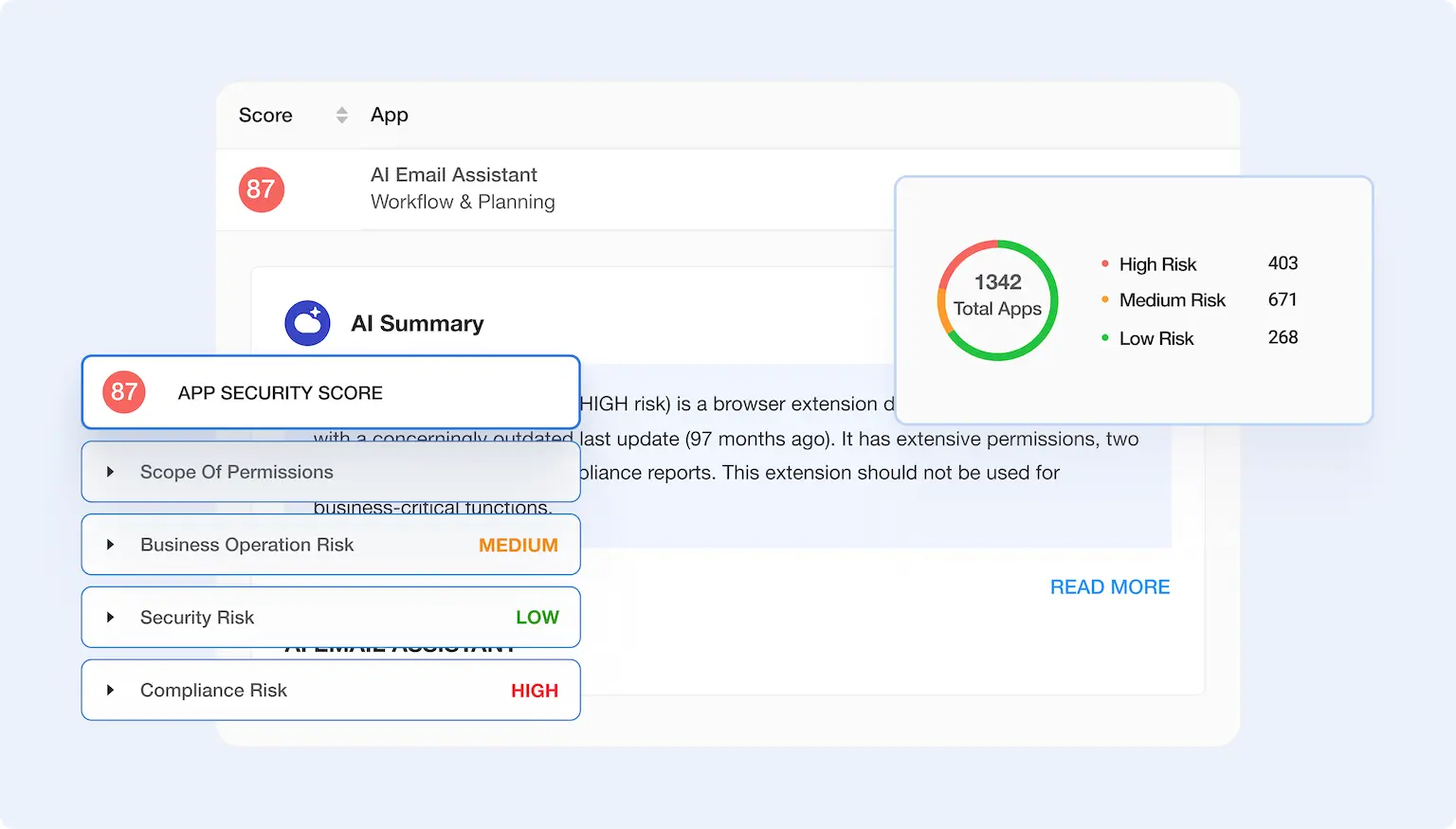
Get full visibility and control to over 550,000 apps and browser extensions assessed by our AI-algorithms. Assess and manage risk in a minute, not weeks, to ensure secure enterprise browsing.
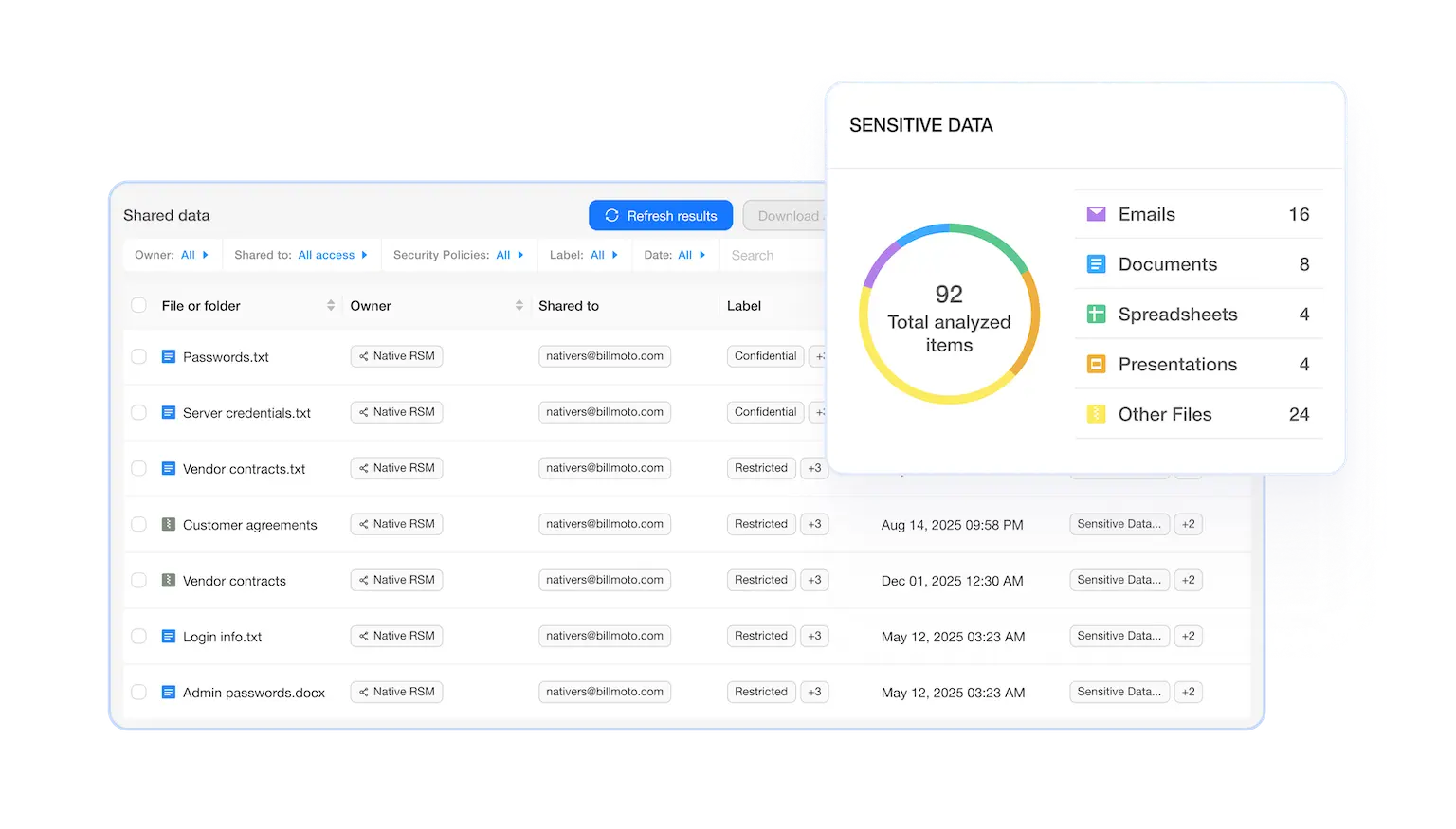
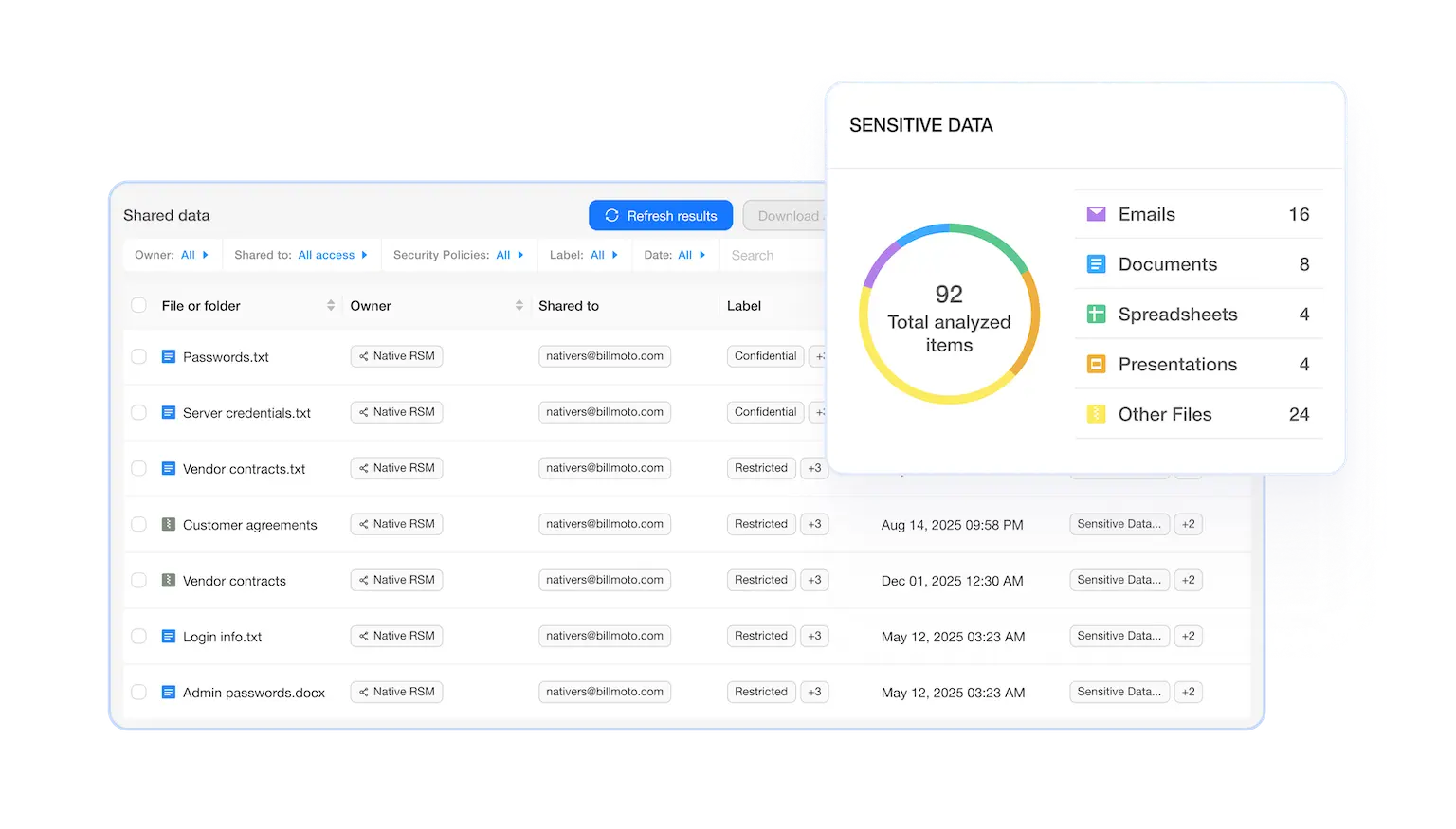
SaaS Data Security Posture Management (DSPM)
Get full visibility and access control across all your SaaS data. Respond to security incidents and data breaches in seconds, not hours or days.



Book a Demo with Spin.AI
Schedule a 30-minute personalized demo with one of our security engineers.
Are these the problems you’re dealing with?
| Challenge | Solution |
|---|---|
Ransomware in SaaS keeps you up at night. | SpinOne detects ransomware behavior in your SaaS data, isolates the blast radius, and restores clean versions fast—backed by the industry’s fastest ransomware recovery SLA, so downtime doesn’t become the story. Attackers are increasingly targeting Google Drive, OneDrive, SharePoint, Slack, and Salesforce data via OAuth or compromised accounts—not just endpoints in a security framework. Even if your endpoint is covered, SaaS recovery can be painfully slow, business-disrupting, and expensive. |
Third‑party app sprawl and SaaS security risks are out of control. | Spin.AI uses AI-driven risk assessment across 550,000+ apps to score, allow, or revoke access automatically. You keep the tools people love, without letting risky apps love your data. Employees connect “just one more” OAuth app to move faster, and suddenly there are hundreds—maybe thousands—of unvetted apps with access to sensitive data. Manually chasing them down is impossible, and blocking everything hurts productivity. |
Misconfigurations expose data you didn’t mean to share. | SpinSPM continuously monitors posture, flags misconfigurations, and guides you to fix them—before auditors or attackers find them. No guesswork, no finger-crossing. SaaS platforms are powerful, but settings can be complex and easy to miss. A single public link, an overly broad sharing rule, or a mis-set admin permission can create a quiet, costly exposure. |
Insider threats and departing employees create real risk. | Spin.AI helps you spot suspicious behavior patterns and reduce data exposure with policy-based controls and fast rollback, so one click doesn’t turn into a headline. Most users are trustworthy, but people make mistakes—and sometimes act with intent on the way out the door. Detecting anomalous activity early and limiting access quickly can be the difference between a near-miss and a breach. |
Fragmented tools slow your team down. | Spin.AI brings the essentials together—backup, ransomware detection and response, posture management, eDiscovery/archiving, and enterprise browser security—so your team can move faster with fewer moving parts. One product for backup, another for app risk, another for browser security… and another for posture. Integration gaps, inconsistent data, and multiple contracts add cost and complexity while creating security blind spots. |
Browser-borne risks keep slipping through. | SpinCRX gives security teams fine-grained control over extensions and permissions, with real-time visibility and policy enforcement—without forcing users to change their browser or how they work. Extensions and browser sessions can quietly exfiltrate data or introduce vulnerabilities. Blocking everything isn’t realistic, but letting everything in isn’t safe either. |
Why Spin.AI?
What key product options does Spin.AI offer?
Spin.AI offers 4 key product options: SpinOne, SpinSPM, SpinBackup, and SpinCRX

All-in-one SaaS security and data protection
- Automated, 3× daily backups with rapid restore for Google Workspace, Microsoft 365, Salesforce, and Slack.
- Ransomware detection and response that isolates affected data, limits spread, and recovers fast.
- Archiving and eDiscovery to preserve, search, and export data for legal and regulatory needs.
- Outcome: reduce downtime, protect business continuity, and prove you’re in control.

SaaS Security Posture Management (SSPM)
- Continuous monitoring for misconfigurations, risky sharing, and overpermissioned access.
- Clear remediation guidance and policy enforcement to reduce attack surface proactively.
- Coverage for 50+ SaaS applications
- Outcome: prevent SaaS security threat exposure before incidents and simplify compliance reporting.
See Why Customers Love Us
The benefits you can count on:
One platform, fewer headaches Consolidate SaaS security, data backup and data governance, and posture management on one AI-powered platform. Fewer vendors and consoles means faster workflows and lower operational overhead. Your team spends more time preventing incidents and less time stitching tools together.
-
1. Fast ransomware recovery you can prove
Ransomware is a when, not an if. SpinOne pairs real-time detection with automated, 3× daily backups to restore clean data quickly and confidently. The industry’s fastest ransomware recovery SLA for SaaS means you can set expectations with the business—and meet them.
-
2. Compliance-ready from day one
Auditors ask for evidence, not opinions. With immutable backups, archiving, and eDiscovery, you can preserve, search, and retrieve data across Google Workspace, Microsoft 365, Salesforce, and Slack. Posture monitoring and reporting make it easier to demonstrate control—without scrambling.
-
3. AI-driven risk decisions at scale
Manual reviews don’t scale when you’re staring at hundreds of thousands of apps and events. Spin.AI uses AI-driven analysis to assess third‑party app risk and surface what matters. You get consistent, explainable decisions that reduce risk without strangling productivity.
-
4. Protection that matches how your teams work
Your data lives in SaaS and flows through browsers. Spin.AI protects both, giving you end-to-end coverage from browser to cloud. Users keep using the tools they love while you keep sensitive data where it belongs.
-
5. Coverage for the platforms you depend on
Whether your core stack is Google Workspace or Microsoft 365—or you run Salesforce and Slack alongside them — Spin.AI meets you where you are with our security tools. Crossplatform coverage means consistent policies and visibility across your environment. No more solving the same problem four different ways.





Users Love Us
Who we serve and why it matters
If you’re a cloud-first, mid-market organization (200–5,000 employees), large midmarket enterprise (up to 10,000 for browser security), or an MSP serving other businesses, you rely heavily on SaaS. You also need to meet compliance mandates without slowing teams down. Spin.AI helps IT, security, and compliance leaders reduce security risk and protect the data that lives in SaaS—without adding tool sprawl or operational drag. Spin.AI is based in the United States, with a large office in Lisbon, Portugal, and a customer support team that follows the sun, allowing us to support organizations around the globe.
50+ Integrations
We have dozens of integrations across SpinOne comprehensive protection, SpinBackup, SpinSPM, and Security Operations Tools, and we’re always adding more.
What makes Spin.AI different?
- All-in-one SaaS security that actually unifies backup, ransomware detection and response, posture management, archiving, eDiscovery, and enterprise browser security. Less complexity, more control.
- AI-driven risk assessment across 550,000+ apps to tame OAuth sprawl without blocking productivity. Real signal, less noise.
- Automated 3× daily backups so your recovery point objectives are practical, not aspirational. Yes, really—three times a day
- The industry’s fastest ransomware recovery SLA for SaaS. When minutes matter, speed is a security control.
- Coverage for Google Workspace, Microsoft 365, Salesforce, and Slack—so your policies and protection are consistent across the tools your business runs on.
Executive FAQs, and how to answer them:
How fast can we recover from a SaaS ransomware incident with this solution?
With SpinOne’s rapid restore and recovery SLA, you can answer in hours, not days.
Are we exposed by risky OAuth apps?
Spin.AI continuously evaluates third‑party apps and automates safe allow/deny decisions you can explain.
Can we prove compliance without a fire drill?
Yes—immutable backups, archiving, eDiscovery, and posture reports give you the artifacts auditors expect.
Will this solution slow users down?
No. Policies are precise, automated, and designed to preserve productivity while reducing risk, and we offer a variety of solutions with deployment models designed to meet your use case.
Can we start with one platform and expand?
Absolutely. Many teams begin with Google Workspace or Microsoft 365 and add Salesforce and Slack over time.
Do we need to rip and replace our stack?
No. Spin.AI layers onto your existing SaaS, bringing security and recovery without forcing big changes.
Related Resources
Ready to protect your SaaS—and prove it?
Let’s make SaaS security tangible, fast, and defensible for your team. If you’re ready to reduce risk, meet compliance with confidence, and recover from ransomware without panic, we’re ready to help.