10 Questions Businesses Should Ask About Their Cloud Security
It is often said that stepping back and taking an honest look at oneself is a great way to grow, mature, and improve on weaknesses. Similarly, businesses that honestly self-examine their cloud security can reap tremendous rewards in terms of understanding their current security posture, where flaws exist, and how they can improve. Let’s look at questions businesses should ask about their cloud security and see how these can help improve the overall cybersecurity posture.
Why should businesses question their cloud security?
Undoubtedly, most businesses will find many areas where improvements need to be made in an honest examination of cloud security and their security posture in general. Therefore, asking questions is a key requirement in a proper risk assessment. In effect, you are asking questions to discover risks that you potentially need to account for or haven’t accounted for in your security solution.
A risk assessment identifies dangers or risks that could negatively impact an organization’s ability to conduct business. But, again, asking the right questions about your cybersecurity posture is integral to this process. Another compelling reason companies ask tough questions regarding their cloud security is that cyberattacks have increased year after year, with high-profile attacks frequently making news headlines.
Regular evaluations of cloud security and cybersecurity posture, in general, help organizations continually prove their cyberdefenses and adjust where needed.
Questions businesses should ask about their cloud security
There are definitely good reasons for all businesses today to examine their security posture across the board, including cloud security. However, what questions should businesses be asking about cloud security? Let’s look at the following important questions that help shed light on the current cloud security posture and improvements that may be needed.
- Do we know what data is shared outside the cloud SaaS environment?
- Which third-party cloud applications are users installing and using?
- Have we performed a risk assessment of third-party cloud applications?
- Are we meeting compliance objectives with cloud data?
- What cloud infrastructure and services are vulnerable to attack?
- Do business units and teams have the tools they need to succeed in the cloud?
- Is business-critical data protected, and do we have gaps in data protection?
- Do we have visibility of insider threats?
- Are we protected against a ransomware attack affecting cloud data?
- What does failure look like, and what will it cost the business?
1. Do we know what data is shared outside the cloud SaaS environment?
It is an understatement to say there has been an explosion of data in the enterprise in organizations worldwide. Data has become the “new gold,” allowing organizations to carry out business more effectively, efficiently, and with greater intelligence. However, over the past few years, led by compliance frameworks like GDPR, there has been greater responsibility and liability tied to sensitive data.
Organizations are tasked with understanding where sensitive data exists in business-critical systems and dealing with and handling this data appropriately. The problem for many businesses is understanding where sensitive data resides. Rick Hedeman, Senior Director of Business Development at 1touch.io, was quoted as saying:
“Most of these organizations know where the data originates (for the most part) and what would be considered the source of record, but they have a very hard time understanding how the data is transformed, copied, and used throughout the organization. They most often will have controls around the source of record but much less likely around the copies and derivatives of that data downstream.”
It becomes increasingly challenging as companies migrate their business-critical data to the cloud to maintain visibility and control over where sensitive data is stored, processed, and shared. With cloud Software-as-a-Service (SaaS) environments, users can easily share and transfer data outside the organization by default, without the knowledge of IT or SecOps.
2. Which third-party cloud applications are users installing and using?
The extensibility of cloud SaaS environments has become a “double-edged” sword as users have access to thousands of cloud marketplace apps they can install with just a few clicks. But, again, by default, users can install any third-party cloud SaaS application in SaaS environments like Google Workspace™ and Microsoft 365.
The very nature of cloud SaaS environments is a breeding ground for “Shadow IT” operations to develop, even innocently or without malicious intent. For example, a user can unknowingly install or use an unapproved third-party application in the environment without understanding the security and compliance implications.
3. Have we performed a proper risk assessment of third-party cloud applications?
Without a proper risk assessment performed on the third-party application or an understanding of how data is accessed or stored, third-party apps can integrate and access sensitive data. Therefore, organizations must have visibility to and understand which third-party applications are used by SaaS users and perform proper risk assessments of these applications.
The challenge with performing effective risk assessments with cloud SaaS apps is the sheer number of apps on the marketplaces of both Google Workspace™ and Microsoft 365. As a result, performing a risk assessment of each application by hand is tedious and unachievable in most organizations.
Businesses must use effective cybersecurity automation to perform cloud app risk assessments in an automated way. By tapping into the power of artificial intelligence (AI) and machine learning (ML), much of the manual, low-level tasks can be performed automatically.
4. Are we meeting compliance objectives with cloud data?
Regulatory compliance has become one of the most critical objectives for organizations outside of cybersecurity. Compliance frameworks like General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), Payment Card Industry Data Security Standard (PCI-DSS), and others have “real teeth.” As a result, they can leverage fines and other penalties on organizations found to be negligent in maintaining compliance with data in scope.
This question ties back into many of the questions already asked. Businesses must first know where data is shared, how it is accessed, and by which users or applications to understand if they are meeting compliance objectives. As the other questions are asked and understood, companies have a much better picture of their compliance stance.
5. What cloud infrastructure and services are vulnerable to attack?
Like performing an inventory of which applications, technologies, and other services are used on-premises, businesses must understand which cloud infrastructure and services they use, how they are used, and by which users. In addition, a thorough understanding of the technologies used helps organizations know where their vulnerabilities lie.
For example, organizations that use Amazon S3 storage need to know what applications and services are using S3, how it is configured, and so on. If using Google Workspace™ or Microsoft 365, knowing which cloud SaaS services are being leveraged helps to understand if these are vulnerable to attack and how they can remediate these attacks.
6. Do business units and teams have the tools they need to succeed in the cloud?
Organizations must provide the tools and services required for business units and teams to succeed and effectively carry out business-critical tasks. Without the right tools and critical services needed, users are much more likely to get involved with Shadow IT operations, installing apps outside of the purview of IT or SecOps to have the tools they feel they need to carry out their jobs effectively.
Getting honest and open feedback from business units and users on what they feel might be lacking in the cloud SaaS environment helps engender respect for the IT policies. In addition, it also allows the business to empower users with tools adequately screened for security and compliance.
7. Is business-critical data protected, and do we have gaps in data protection?
When organizations shift data to the cloud, there can be a misconception about data being “automatically protected” without any chance of losing data in the cloud. Unfortunately, this is a dangerous misconception that has left many companies struggling to recreate data lost in the cloud for several reasons, including user error, ransomware, or a cloud outage.
Since cloud Software-as-a-Service (SaaS) hyperscalers like Amazon, Google, and Microsoft operate using what is known as a shared responsibility model, it means you as the customer or tenant are ultimately responsible for protecting your data.
In addition, popular SaaS solutions like Google Workspace™ and Microsoft 365 do not include native “data backup solutions” that can be leveraged to recover lost data. As a result, organizations must bring their own third-party solution to ensure data is adequately protected. Also, not all third-party cloud SaaS backup solutions are created equal. So, businesses must be careful to choose solutions that allow protecting data in a way that aligns with their data location requirements and with their cloud storage vendor of choice.
Even with many third-party cloud-to-cloud backup solutions on the market, it may be challenging to determine which data is protected or if there are gaps in data protection in the environment. Therefore, businesses must ensure they have not missed critical data as part of their configured backup solutions.
8. Do we have visibility of insider threats?
Insider threats are often just as dangerous as external attacks coming from outside the environment. For example, a malicious insider may be a disgruntled user looking to harm the business in some way or intentionally leak information to the outside, possibly to a competitor.
Attackers may also have compromised a legitimate account. However, these can be difficult to discover and have visibility since this activity often looks like legitimate user activity. Therefore, organizations must consider their tools and visibility to potential insider threats. Do they have the means to discover malicious or anomalous user activity?
9. Are we protected against a ransomware attack affecting cloud data?
Ransomware attacks are gaining momentum and increasing in frequency and intensity across the board. According to the Verizon Business 2022 Data Breach Investigations Report (2022 DBIR), ransomware breaches have increased by 13%, more than in the last five years combined. Additionally, attackers increasingly use ransomware to “lock up” business-critical data. As a result, businesses worldwide must ask, “are we protected against a ransomware attack affecting cloud data?” If not, what can companies do to improve data resiliency and the ability to recover from and protect against ransomware?
Many organizations are focusing only on how they can recover. However, there are many good reasons to protect the business from ransomware proactively. Backups alone are no longer good enough. Attackers are using new tactics such as “double extortion,” which targets companies with a ransom to recover their data and prevent it from being intentionally leaked to the dark web.
Proactively protecting against ransomware in the first place is a better approach than simply saying how we can recover from ransomware. Intentional data leakage can result in tremendous damage from compliance violations, lost customer confidence, tarnished business reputation, and other consequences.
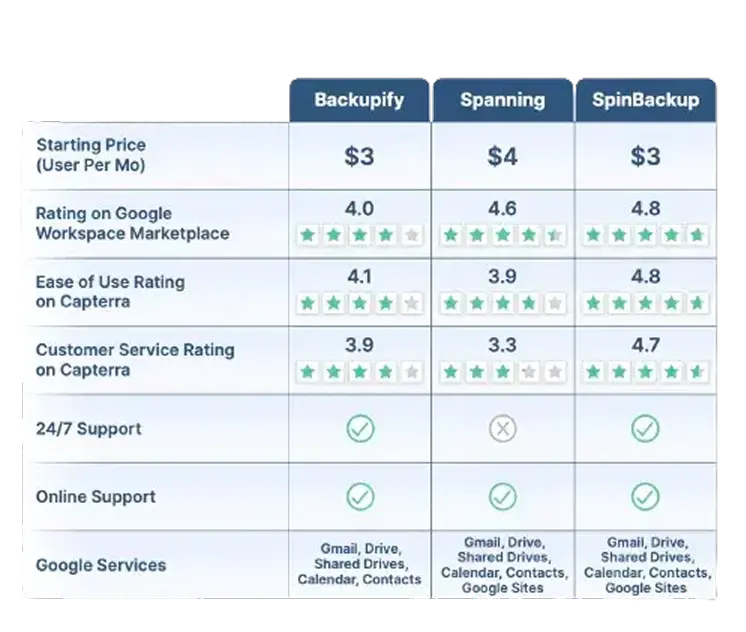
Google Workspace™ Backup Solution Comparison Table
SpinBackup stands out as a comprehensive backup solution for Google Workspace™ compared to competitors like Backupify, and Spanning. We offer a fast onboarding process (under an hour), advanced recovery features like granular and on-demand restoration, and robust security. Read More
Robust security features include:
- Ransomware protection
- Risk assessment of third-party apps
- Misconfiguration management
SpinBackup also supports multiple cloud providers (GCP, Azure, AWS) and compliance with GDPR, SOC 2, HIPAA, PCI DSS, and ISO 27001. With competitive pricing ($3/user per month) and high user ratings (4.8/5 for ease of use on Capterra), we provide a well-rounded and secure data protection solution for businesses.
Read Less*Contact Us for current pricing.
SpinOne – the right solution for tough cloud security questions
Ultimately, your cloud security solution is an important component in the overall cybersecurity posture of your cloud environment. Unfortunately, many organizations struggle as they attempt to use legacy or traditional security solutions never built for use in the cloud. SpinOne is a modern, next-generation cloud security solution that helps organizations tackle many of the complex cybersecurity challenges they face in cloud SaaS environments today.
It leverages modern artificial intelligence (AI) and machine learning (ML) to provide cybersecurity automation for businesses with critical data located in modern SaaS environments. SpinOne helps to close the gap for companies that are ill-equipped to deal with modern cloud security challenges. Using cybersecurity automation, SpinOne allows organizations to have the technology tools needed for data protection, data loss protection, compliance, insider threat, and ransomware protection.
Note the following capabilities provided by SpinOne:
Note the following key capabilities of the SpinOne platform:
- Automated risk assessments of third-party cloud SaaS apps – Performing manual risk assessments of cloud SaaS apps across cloud marketplaces can be time-consuming and even infeasible. SpinOne enables businesses to have a proactive, automated risk assessment that can be used with cloud SaaS policies to enforce the use of only sanctioned cloud SaaS applications
- Policy-based cloud SaaS app control – Using policy-based automation, SpinOne provides the tools needed to enforce governance and cybersecurity across the cloud SaaS environment
- Visibility to shared cloud data – Using native tools in cloud SaaS environments leaves businesses lacking in visibility to data sharing. SpinOne allows admins to quickly see which data is shared inside and outside the organization and disable data sharing.
- Prevents data leak – With SpinOne, organizations can effectively limit data sharing, third-party applications, and other risks in the environment
- Automated backups of your cloud SaaS environment – SpinOne provides enterprise backups of your critical data. Unlike other cloud-to-cloud backup solutions, you can choose which cloud stores your cloud-to-coud backups, in line with the 3-2-1 backup best practice model.
- Insider threat protection – Quickly see activities of malicious users or identify the possibility of compromised credentials
- Proactive Ransomware Protection – A unique offering from SpinOne is automated ransomware protection, automatically remediating attacks in your cloud SaaS environment with the following:
- An automatic cybersecurity scanner, empowered with artificial intelligence, scans your cloud SaaS environment for ransomware 24x7x365
- If ransomware is discovered, it automatically blocks the ransomware process
- SpinOne identifies all files that may have been initially affected by the ransomware
- The files are then automatically recovered, leveraging Spin’s automated cloud SaaS backups
- SpinOne notifies the cloud SaaS administrator about the ransomware attack
In the screenshot below, SpinOne’s Ransomware Protection module provides simple yet powerful proactive ransomware protection.
SpinOne provides an automated solution with AI/ML that allows businesses to take control of their cloud security needs. Learn more about SpinOne and the capabilities and features it provides here: Enterprise ransomware protection and apps security solutions (spin.ai)