Complete Guide to Salesforce Security Best Practices for Businesses
Salesforce is a common, key SaaS application in most companies’ tech stack – contains business-critical, sensitive data that is imperative to secure. See our guide to Salesforce Security Best Practices:
Security Risks In Salesforce
Salesforce has powerful built-in security functionality. However, it doesn’t protect your sales data against all risky events. Similar to other SaaS applications, Salesforce has a shared responsibility model. It means that you will need to take part in protecting your Salesforce environment against three main cyber events:
- Malfunction
- Data loss
- Data leak.
There are several causes of these events.
1. Misconfigurations
Improper settings of Salesforce can cause several types of problems. First, the application might work incorrectly and impede the work of your revenue-generating team. Second, it can leave the entry point for hackers into your environment. As a result, malicious actors can steal your data and use it against your company.
2. SaaS apps
SaaS applications that supplement the functionality of Salesforce can bear hidden threats too. For example, apps that have mass edit permissions can malfunction and erase large sets of data in your CRM, disabling the work of your sales team.
3. Code errors
Most often code errors cause a disruption in how the data is represented in Salesforce. This type of event makes it impossible for your revenue-generating employees to perform their work.
4. Unauthorised access
There are several types of unauthorized access and each can happen in Salesforce. First, a cybercriminal can hijack the account of a user or, in a worst-case scenario, an Admin. Second, a user can access data that they should not.
5. Human error
Salespeople who use Salesforce on a daily basis can make mistakes. As a result, a part of business-critical data about potential or existing clients can be lost.
All these events have a high probability of occurrence. Let’s see what you need to do to prevent them.
General Salesforce Security Best Practices
Regular change of encryption key
Salesforce enables you to encrypt certain fields with sensitive data, for example, CCN, or SSN. This creates an extra layer of protection in case a hacker gains access to your system. The good practice is to change this key on a regular basis.
Health Check
Health Check is the functionality of Salesforce that audits your security and configurations. It grades your security with percentages and also provides you a list of issues and suggestions on how to fix them. We recommend using this tool regularly.
Use Sandbox
To protect your Salesforce from errors, it is best to test the code for errors in the Sandbox before implementing it within your organization.
Best Practices to Secure Access in Salesforce
In this section, we discuss how to protect against unauthorized access from threats within and outside organizations.
MFA & Strong Passwords
Multifactor authentication will provide an extra layer of security during the login process. It can significantly impede hacker’s attempts to hijack accounts.
Imposing strong passwords and regular password changes (e.g., once per month) will help secure accounts from password-stealing techniques (e.g., spoofing).
IP ranges & Maximum Failed Logins
IP ranges will help you prevent unauthorized access even if the hacker manages to get hold of the account credentials and bypass the MFA.
Limiting the maximum number of failed logins will prevent the attempts of hackers to log in with the most frequently used passwords (e.g., “12345”).
Profiles and permission sets
A Profile in Salesforce sets the permissions for a user on what they can or cannot do, and which type of data they are allowed to access. For example, Top Management can have permission to access any data in Salesforce. However, they do not need to change it.
On the other hand, a salesperson can access only their prospects’ information, but they can change data. However, none of them should be able to change metadata unlike developers and sometimes Admins. Outsource developers should not be able to access any data and should only work in the Sandbox with sample sets of data.
Best Practices Against Data Loss in Salesforce
Data Loss in Salesforce can happen due to errors in code, add-ons, or human errors. To prevent permanent data loss we suggest using backup.
Regular Data and Metadata backup
Salesforce doesn’t have an enterprise-grade native backup. Most of its native tools only focus on one type of data (metadata, files, or objects). They also require manual control, and it’s hard to achieve regularity.
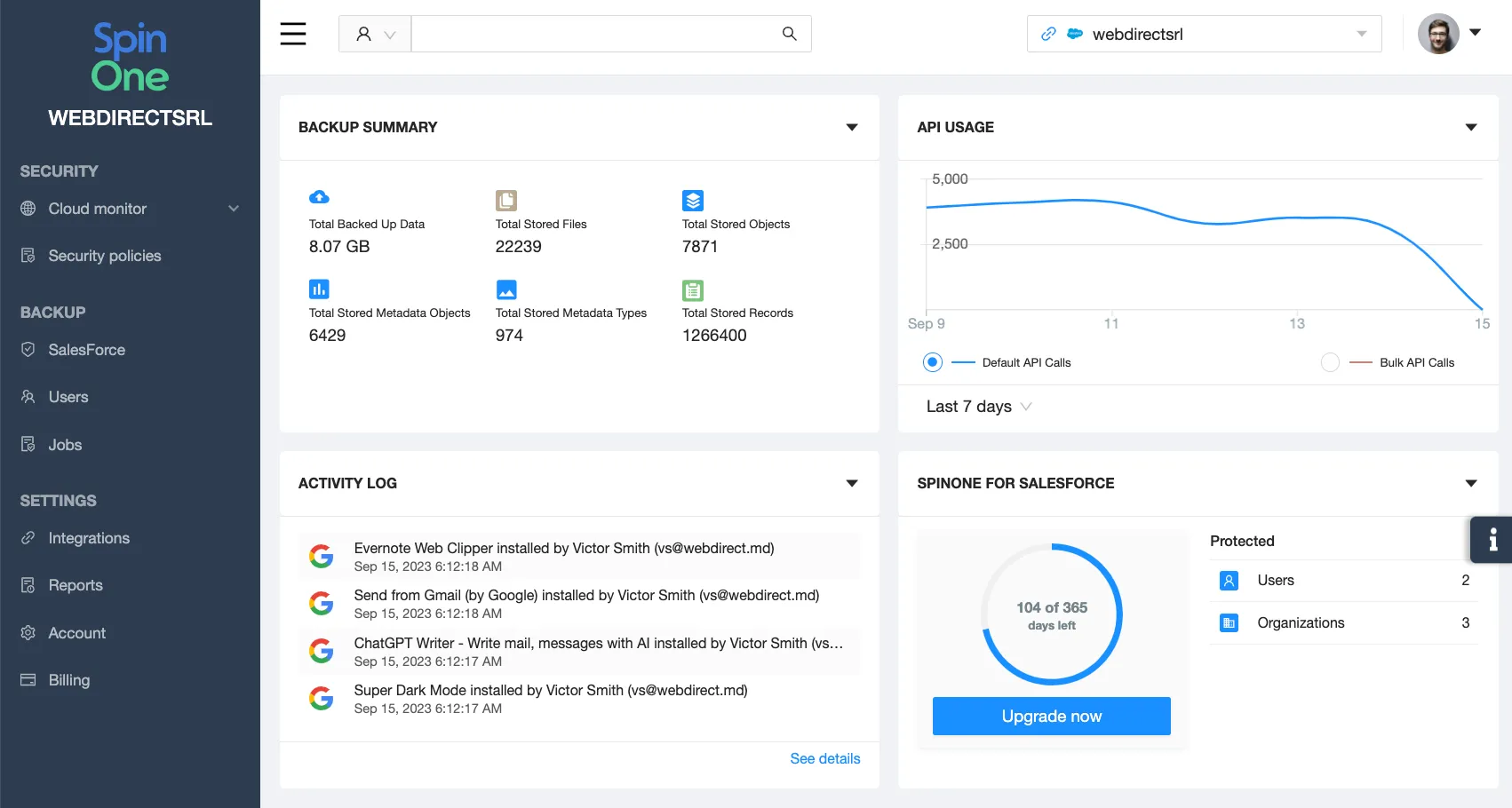
That’s why the best security practice is to have a third-party Salesforce backup. SpinOne platform has a backup solution catered specifically for Salesforce.
SpinOne has multiple advantages for the company:
- You can back up both data (files and objects) and metadata.
- The use of two types of Salesforce APIs makes it the fastest Salesforce backup on the market.
- SpinOne stores all your data in the data center of your choosing (AWS, Azure, GCP).
- You can also choose the region of the data center to achieve compliance.
- SpinOne enables granular recovery of a single record, from a chosen point in time.
- You can use SpinOne to back up your Sandbox environment making the mistakes in development easily reversible.
- You can use Compare tool, to understand what changes have been made in your data and when.
Try SpinOne for Salesforce
FAQ
Why is Salesforce security important?
Salesforce contains data necessary for the revenue generation of the company. It includes the contact information of prospects and clients, the history of communication with them. Losing this information can harm revenue generation process and impact the company’s financial performance.
How can I prevent insider threats in Salesforce?
You can prevent insider threats by using profiles and permission sets in Salesforce.
How should I assess the security of third-party apps integrated with Salesforce?
We suggest considering the following criteria: permissions, developer type (business or individual), the country of registration, the frequency of updates, the number of companies using it, the ranking, the past vulnerabilities, and the legal documents available.