Cybersecurity Awareness: Importance and Purpose
Do you know that the “human element” causes roughly 85% of data breaches? It can be a misconfiguration of sharing settings, a click on a link in a phishing email, or a poor choice of password. The result is devastating. Can it be prevented? Let’s find out in our cybersecurity awareness guide.
What is cybersecurity awareness?
Cybersecurity awareness is the knowledge system of cybersecurity threats and ways to detect and avoid them used by the potential participants of cyber incidents. Let’s dive just a little bit deeper into the components of this definition. First, let’s look at what ‘the knowledge system’ means. There are several essential characteristics:
- the knowledge pertains to a particular subject (cybersecurity, in this case)
- it is organized logically
- it has practical value.
Second, let’s overview the meaning of “potential participants.” These are people who either are the targets of cybercrime or perpetuate it due to a lack of knowledge. Here are two examples. A criminal steals a person’s credentials and uses them to transfer the person’s money to their account.
Another example is the criminal stealing a person’s credentials to steal money from the company where the person works. In this case, the person is not a direct victim. They just perpetuate the crime.
Third, the word “use” in the definition is of extreme importance. The knowledge that one cannot use has no practical value. Let’s look at the example. A person knows that ‘qwerty’ is a poor password choice, to say the least. However, they don’t change it as they prefer personal comfort to security or have an optimism bias.
To sum up, when it comes to cybersecurity awareness, it is essential that the potential participants of cyber incidents could apply their knowledge to identify and prevent cybercrime.
Why is Cybersecurity Awareness Important?
At the beginning of this article, we already mentioned that 85% of data breaches happen due to the human element. Here are more stats to ‘unwrap’ this figure:
Compromised credentials (20% of cases) and phishing (17%) are the main attack vectors, according to IBM’s Cost of Data Breach Report. Another popular human error, cloud misconfiguration, is the third most frequent data breach vector (15%). Together they comprise 52% of cases. Unfortunately, according to Mimecast, only 45% of companies impose cybersecurity awareness training.
What does it mean in practice? Humans are the Achilles’ heel of any security system. That’s why businesses need to do two things in addition to their regular cybersecurity practices:
- Enhance Cybersecurity Awareness in their employees to decrease the number of mistakes.
- Acquire the last layer of defense tools.
We’ll talk about the second option in the last section of this article. Let’s now focus on:
Benefits of cyber awareness:
1. Decrease the number of cyber incidents
The research showed that cybersecurity awareness training decreased employee susceptibility to phishing in 80% of participating organizations.
2. Improve Compliance
There are two ways your company improves compliance with cybersecurity awareness training. First, some rules and regulations imposed by a government mandate this practice. Second, see item one. Security awareness decreases the number of cyber incidents and thereby decreases the legal implications.
3. Boosts Business
In several previous years, we have seen cybersecurity incidents that caused the leak of the personal data of millions, if not billions, of people. The most recent examples are data leaks of AirAsia passengers and employees (5 million), Australian Optus (2.8 million), and the Los Angeles Unified School District (500 GB).
We predict that in the future, individuals will inquire more about the cybersecurity measures an organization takes to ensure data protection before making a purchase from them.
Similarly, there were several cases of attacks on service providers that disrupted the businesses and government organizations they served. One of the most notable cases was the CommonSpirit ransomware attack that had a toll on many healthcare organizations around the US.
We predict a surge in the number of requirements and subsequent checks of cybersecurity by clients and partners in the B2B model.
Lastly, cybersecurity influences investment decisions. For example, NASAA issued a Cybersecurity Checklist for Investment Advisers that include several items pertaining to cybersecurity awareness.
4. Secure the well-being of your employees
According to the Canadian Resource Centre for Victims of Crime, crime has a severe impact on both the psychological and physiological state of a victim. Some common implications include fear, anger, shame, guilt, confusion, insomnia, lethargy, headaches, muscle tension, and nausea. Being part of cybercrime can damage your employees’ life quality and work performance.
How to increase cyber security awareness
Through regular employee training! Here are some tips on how to improve cybersecurity awareness training:
Regularity
First, people tend to forget skills and information they do not apply on a regular basis. Second, our brain seeks the easiest way to perform a specific task.
Meanwhile, cybersecurity awareness requires us to be extra vigilant. For example, to avoid a phishing attack, you need to check the sender’s address and the URL of a link in the email. Unfortunately, your brain can push you to act the easiest way possible, i.e., open the link without checking.
Third, the optimism bias mentioned above makes people less cautious. We need a constant reminder that cybercrime is real and it can happen to anyone. Summing up, regular training is a must.
Onboarding
Onboarding cyber security awareness training is often omitted by companies. However, we see how beneficial it can be for both the organization and the employee.
You set your standards and expectations high from the very beginning. The onboarding security training sends a clear message to the employee: “we take cyber security awareness seriously here.” Of course, it must be supported by regular training.
Drills
Security education is similar to any learning process. Apart from acquiring skills, we need to apply them in practice. The drill is a fake security incident, e.g., a phishing email sent to employees to check their susceptibility.
Another essential function of the drill is checking how well the employees apply the acquired knowledge. Finally, mistakes that individuals make during the drill can help them be more attentive next time. Many security education organizations offer drills as part of their awareness training.
Management engagement
It is important to make sure that everyone receives security awareness training, including the management.
Quality
Cyber security awareness training should be engaging and easy at the same time. Gamification, storytelling, quizzes, and drills can help achieve this goal.
Cybersecurity awareness month
October is an official cybersecurity awareness month in the US. It was presented by the government in 2004. It is an easy way to remind individuals and organizations about the existing cyber threats and the ways to avoid them.
It would be great if your Security and HR Departments can work in alliance and plan a number of events to enhance cybersecurity awareness month. Enhanced training and topical content spread among the employees are examples of such events.
Explain cyber security policies
When introducing new cyber security policies, explain how they protect your organization from cyber threats. It will increase the general awareness of the employees in your organization.
Understanding cyber awareness training
In this section, we answer several most popular FAQs on security awareness training.
What is cyber awareness training?
It is a complex training program that comprises a learning program with audio, video, and text materials, quizzes, and drills. Usually, such training is repetitive and continuous over a long period of time to ensure that employees retain the acquired skills and knowledge and apply them in practice.
Why is cyber security awareness training important?
It can help employees to identify cyber threats and act accordingly. As a result, organizations become less vulnerable to cyber attacks.
How long does cyber awareness training take?
As mentioned above, the best training never stops. After an initial course that can take from several hours to several days, the organizations can conduct mini-training sessions to retain the skills of the people at the necessary level.
What are the best practices for cybersecurity awareness month?
The best practices for cybersecurity awareness month include an event with an invited speaker, a drill, and internal content. The latter include but are not limited to posts on socials for employees, articles on an internal medium, and email newsletters.
Awarding employees who performed best in training during cybersecurity awareness month is another good idea.
Comprehensive topics in cyber security awareness training
If you want to choose security education for your company, search for the following topics:
- Optimism bias
- Cyber security threats (phishing, ransomware, human error)
- The adverse outcomes of cyber incidents.
- The best practices to detect various threats.
- Steps to take after detection.
How effective is cyber awareness training?
In the study mentioned before, the phishing susceptibility dropped from 60% to 10% over the period of 12 months. It is a significant improvement. But is it enough?
Here’s another thing to consider. We analyzed the attacks listed on our ransomware tracker. And we didn’t see any significant month-by-month changes in the number of successful ransomware attacks around the cybersecurity awareness month (October).
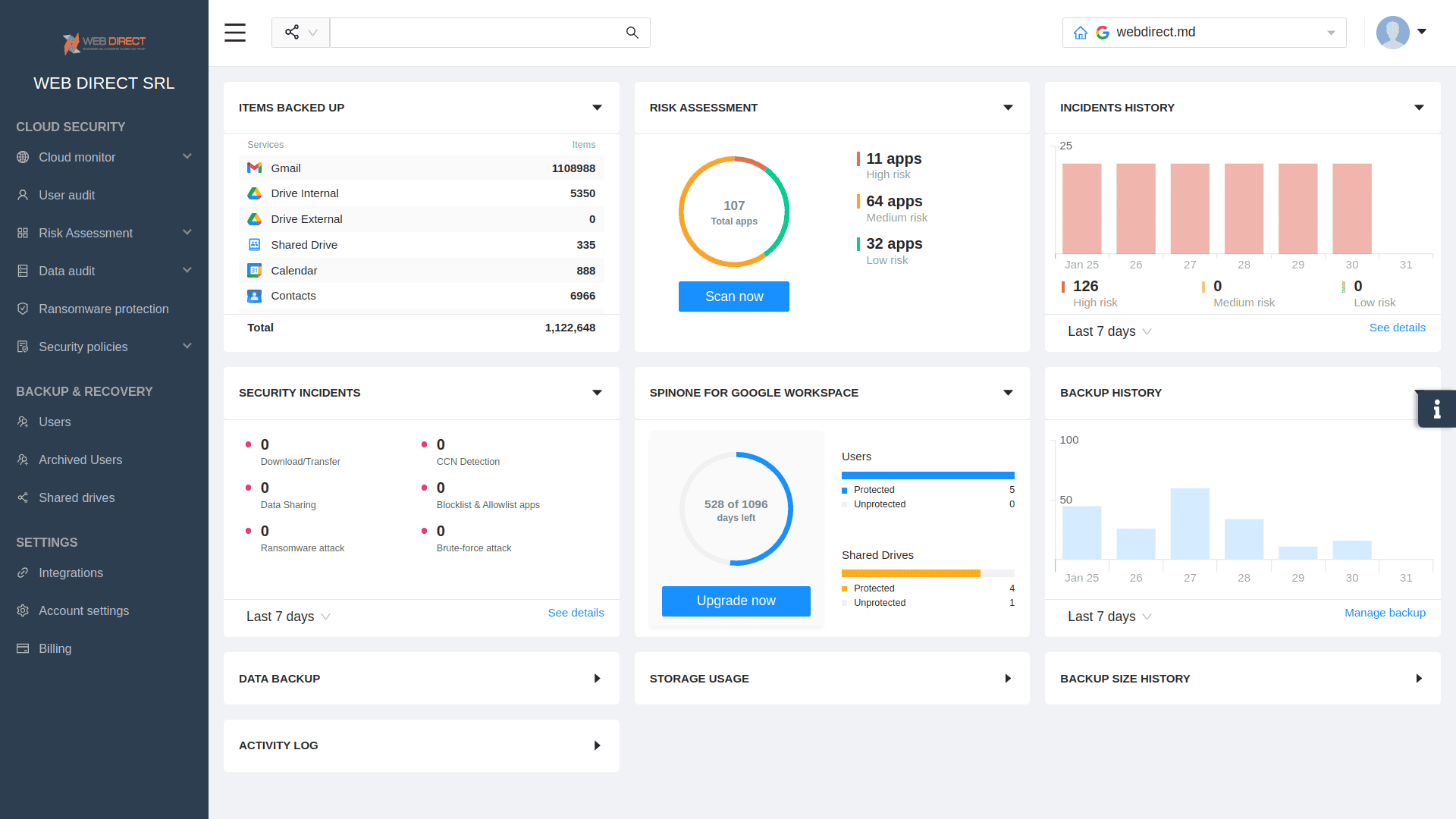
You need the so-called last layer of defense tools to enhance your security. These tools perform several important tasks:
- Stop the attack in case of a security breach.
- Back up files to prevent loss due to deletion by mistake.
- Help detect and revoke unauthorized access.
- Impose necessary security policies.
- Find and disable potentially insecure applications.
SpinOne data protection platform for Google Workspace™ and Microsoft Office 365 is an example of such a tool. It has the functionality that backs up various GW and MSO 365 services, detects and stops ransomware, and offers comprehensive DLP policies and practices. Learn more here.