SaaS Security Governance & Compliance | CISO Guide
As we saw in the previous post, many cybersecurity challenges face businesses today, and CISOs must wisely invest in effective cybersecurity solutions to protect business-critical data. In the last post, we looked at the current state of cybersecurity threats and the need for organizations to use next-generation solutions to protect their hybrid cloud SaaS environments. This second part of the CISO cybersecurity guide will look at the SpinOne SaaS Security Posture Management (SSPM) platform features that effectively protect business-critical SaaS data from current and future cybersecurity threats.
SpinOne capabilities solving the biggest challenges of enterprise CISOs
In the following walkthrough of features, we will consider the SpinOne features that help CISOs and organizations, in general, solve the very complex SecOps challenges facing enterprise cybersecurity. What are some of these challenges related to cybersecurity in cloud SaaS environments? Note the following:
- Lack of visibility in cloud SaaS environments
- Granularly applying cybersecurity profiles to different users and groups
- SaaS apps risk management
- Analyzing and prioritizing risk
- Justifying security spend and prioritize security investments
Lack of visibility in cloud SaaS environments
One of the challenges that CISOs have overseeing cybersecurity strategy for the hybrid cloud is maintaining visibility to key areas in cloud SaaS environments. Organizations that shift business-critical data and services to the cloud can often suffer from a lack of visibility to their data, user behaviors, data access, and applications interacting with the environment.
It is due to many different reasons, including lack of familiarity with cloud SaaS tooling, lack of native tools and capabilities, and using traditional, non-cloud-aware security tools that have no relevance in cloud SaaS environments. This combination of factors can lead to a “black box” regarding security in the cloud with a total lack of visibility.
Attackers are increasingly compromising cloud SaaS environments using malicious third-party applications, OAuth attacks, and others. Businesses today must have visibility to all crucial aspects of the environment to take a proactive approach to security risks.
SpinOne provides visibility to essential elements of your cloud SaaS environment. Notice the single-pane-of-glass interface details the following:
- Risk assessment
- Incidents history
- Security incidents
- Items backed up
- Backup history
- Data backup
- Activity log
- Storage usage
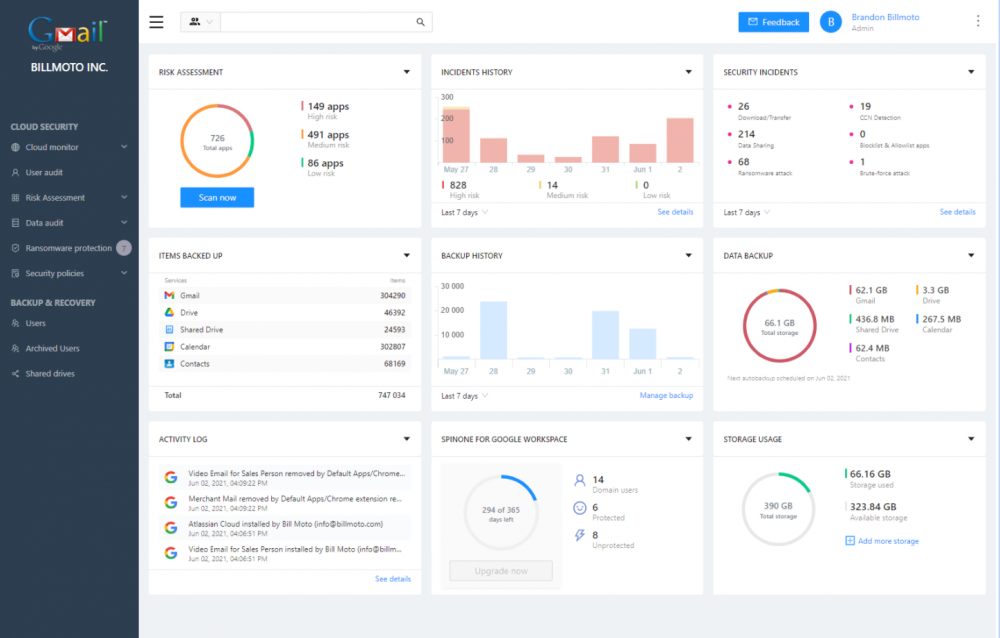
You can drill into each dashboard for further details into the cybersecurity and protection of your environment. Below is additional detail concerning incidence history when clicking the details of the Incidence History dashboard.
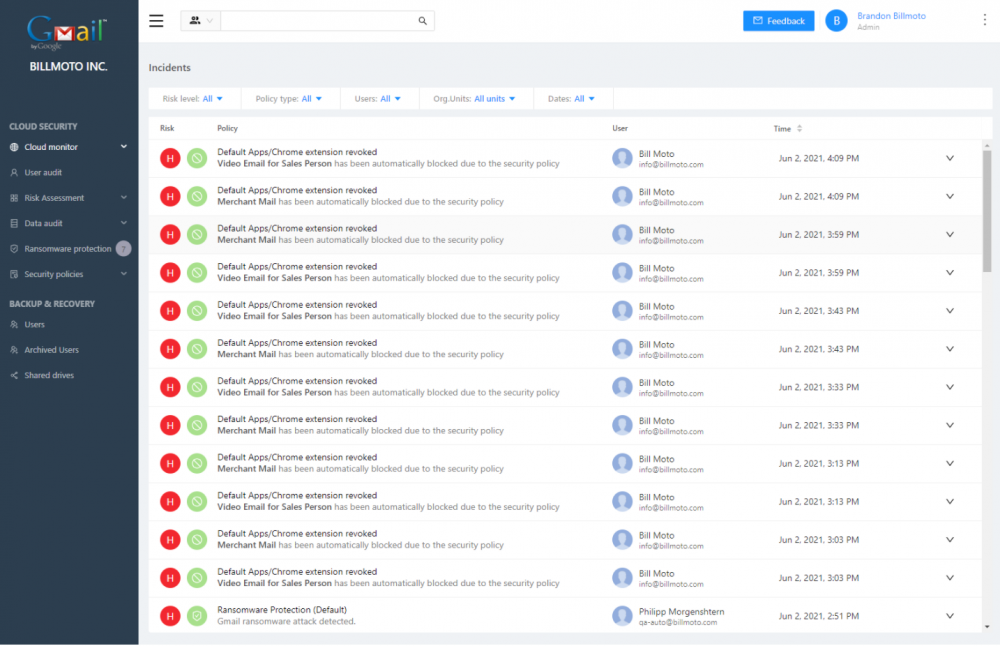
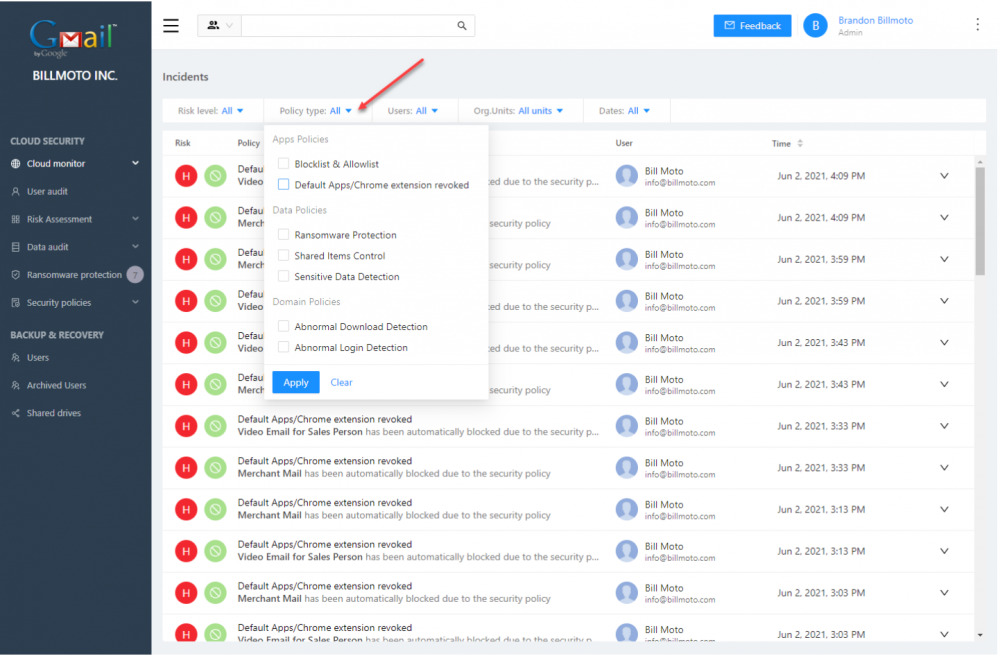
Having granular visibility into the cloud SaaS environment is critical for CISOs to understand current risks facing the environment, the users and groups that are primarily responsible for the risk, and which data is affected.
Granularly applying SaaS cybersecurity profiles to different users and groups
Unfortunately, without an intelligent cloud SaaS cybersecurity solution that effectively gives visibility to risk across the organization in a granular way, many security admins apply blanket controls across the entire environment without really understanding which controls are needed. This approach is not ideal for business productivity nor cost-effective.
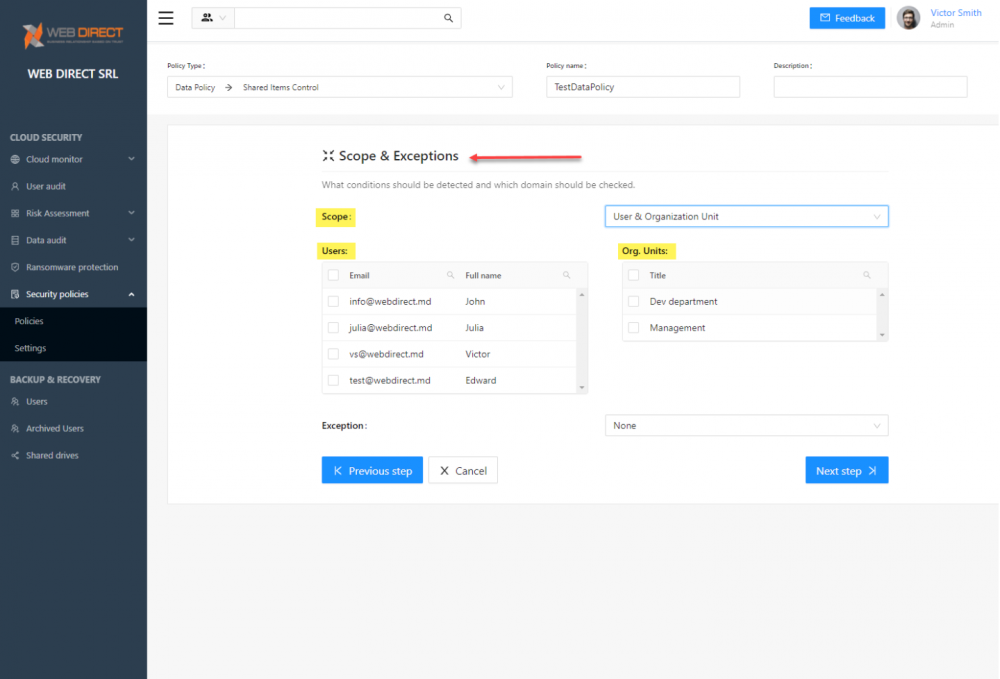
Different organizational groups may use and access various SaaS applications. The needs across the full range of end-users in most organizations are most likely different. The better approach is to apply scoped security controls based on the risk factors associated by departments and by end-user. It allows creating customized security controls that are best suited for business continuity in your organization and the individual needs of groups and users.
SpinOne provides the full range of security features that allow enterprise CISOs to focus their efforts and apply new security controls to users or applications representing the most significant risk to the organization. SpinOne’s Policies feature allows segmenting employees by such factors as departments, seniority levels, and types of risk factors. The ongoing risk assessment provided by SpinOne enables monitoring applications and behaviors as these access business-critical data.
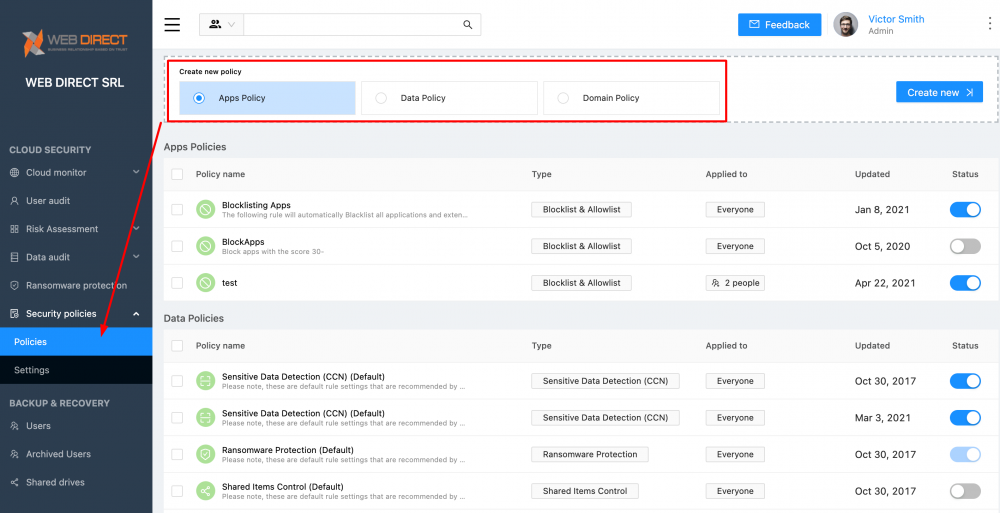
These can be applied in a granular fashion to specific users or organizational units.
SaaS applications risk management
Most CISOs are dealing with an explosion in SaaS applications for business productivity. One of the many features of cloud SaaS environments is the wide range of third-party SaaS applications available for business productivity. Many legitimate cloud SaaS applications provide robust features and capabilities to businesses making use of the cloud.
However, attackers are using malicious third-party applications as a doorway into cloud SaaS environments and as a way to launch ransomware and other cyberattacks. Third-party applications make use of a cloud authentication mechanism known as OAuth permissions delegation, allowing end-users to grant permission to applications to access data on their behalf. Essentially, a user gives the application a key to their data and applications when they grant OAuth permissions.
Governing OAuth security concerns
While OAuth allows end-users to grant permissions to applications without disclosing their password, it can lead to security compromise if end-users unknowingly give permissions to a malicious third-party application. OAuth also bypasses two-factor authentication mechanisms in most environments by design and can only be manually revoked by the user. Attackers use OAuth compromise techniques much like phishing attacks, where they make malicious applications look extremely legitimate. A user may think a legitimate application is requesting access when it may be a malicious application laced with ransomware.
Former hacker turned security consultant Kevin Mitnick detailed an attack he dubbed “RansomCloud,” where a malicious third party application masqueraded as a legitimate “AntiSpamPro” application. Rather than apply a legitimate security update, once permissions are granted, the application begins encrypting the user’s cloud email inbox in real-time.
Risk assessment module
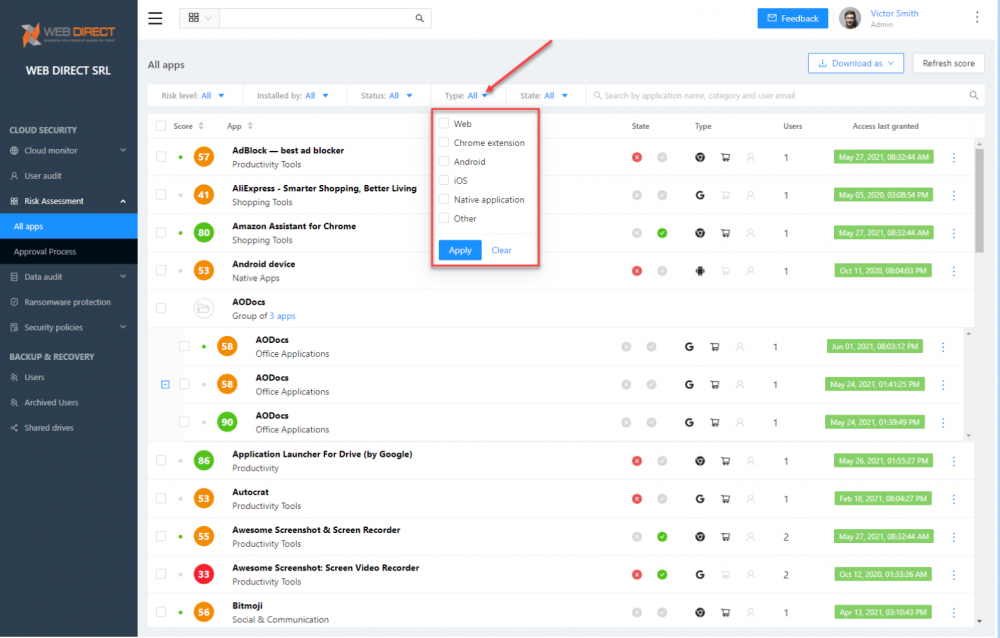
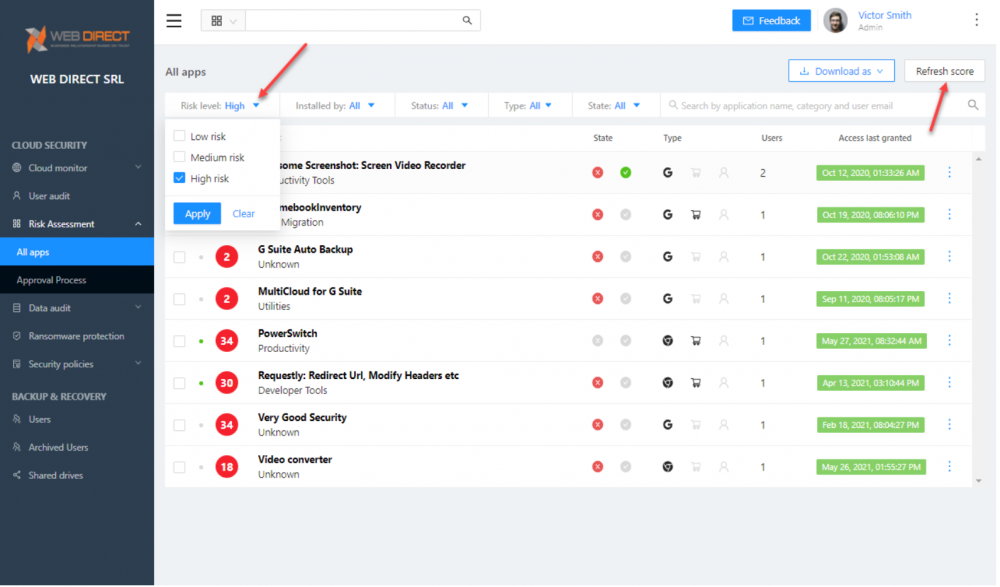
This attack is one example of how CISOs must have a plan of action to scrutinize and control which applications can access the sanctioned cloud SaaS environment. SpinOne provides a powerful Risk assessment module that scans and scores third-party applications based on risk. This feature allows CISOs and security admins to determine which applications are whitelisted or blacklisted in the environment for end-user access.
It also helps to provide visibility into which applications users, groups, and others are attempting to install and which data is accessed. SpinOne provides rich filtering capabilities that allow seeing a granular view of the risk levels, who tried to install and the types of applications. This detail enables seeing from which platforms the risks are originating.
SpinOne SaaS security policies
Regarding third-party applications, SpinOne policies allow applying policies to applications that meet various criteria, such as:
- Application category
- Application ID
- Developer
- Scope of permissions
- Application Risk Score
- OAuth permissions delegation
- Chrome Extensions
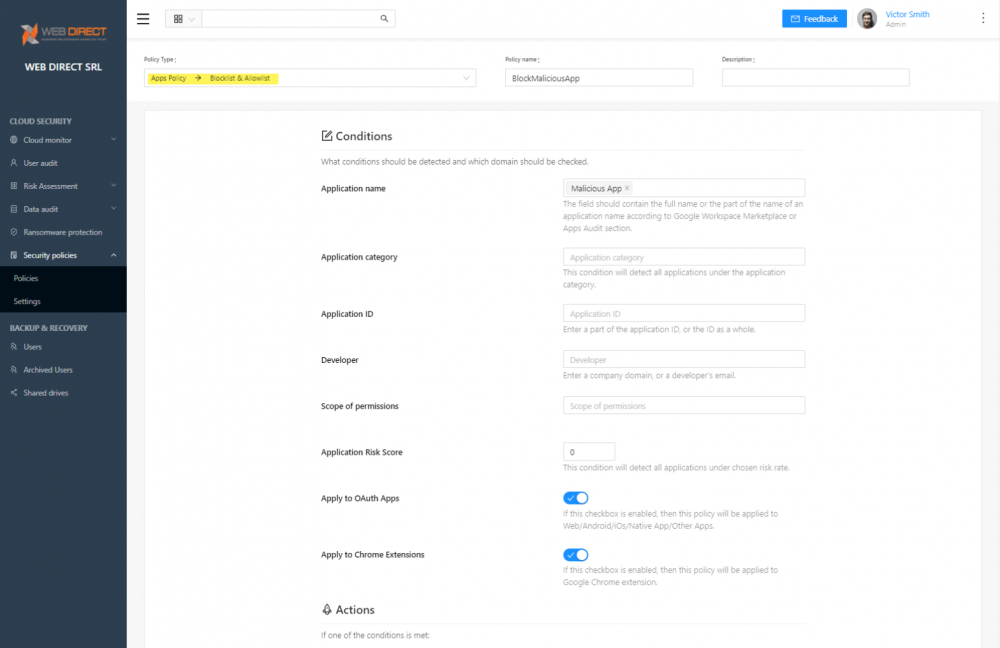
SpinOne’s risk assessment and apps policies provide CISOs with the tools needed to effectively control and protect cloud SaaS environments from malicious applications.
Analyzing and prioritizing risk
One of the challenging tasks under the purview of the CISO is analyzing and prioritizing risk in the environment. Manual efforts to investigate and prioritize risk are tedious and error-prone. There are tens of thousands of third-party applications in the Google and Microsoft marketplaces for use in the respective cloud SaaS environments. Determining the risk of each of these by hand would be a nightmare.
SpinOne provides an AI-powered risk score that reflects the diversity and severity of security threats, behavioral vulnerabilities, and access privileges. Using artificial intelligence (AI) and machine learning (ML), SpinOne takes on the heavy lifting of assessing and prioritizing risk. CISOs and SecOps teams have the cybersecurity intelligence needed to secure the cloud SaaS environment using this automated risk assessment.
The Risk Assessment module allows filtering based on the risk level to allow drilling into high-priority risks and applications in the environment. The application risk assessment score is a dynamic score that can change over time. SpinOne continually scans and assesses the risks of applications over time so benign apps that become risky or malicious are categorized appropriately.
Justifying SaaS security spend and prioritize security investments
There is a wide range of security solutions and tools available to enterprise organizations to protect various environment segments. Cybersecurity is no doubt on the top of the IT budget list for many businesses. Many organizations may currently use a wide range of different, disjointed solutions to stitch together proper protection of their cloud SaaS environments. Additionally, companies may perceive they need to hire additional security professionals to deal with the ballooning threats that exist, both on-premises and in the cloud. The features and capabilities provided by SpinOne help organizations solve both challenges.
SpinOne helps enterprise security leaders answer three important questions:
- How do we prioritize the different types of threats targeting my employees?
- How can we effectively simplify and reduce the process of SaaS apps risk management without disrupting business?
- How can we justify the security spend and prioritize future investments?
A Spin One license answers all three:
- It prevents organizations from requiring additional SecOps team members.
- It achieves manageability, visibility of third-party apps, automated risk assessments, and instant control
- It provides tools to apply security in a customized, granular way across the cloud SaaS organization
A single solution for a wide range of security challenges
We have only scratched the surface of the functionality contained within the SpinOne SaaS Security Posture Management (SSPM) as it helps organizations confidently use cloud SaaS environments and applications while maintaining a proactive and robust security posture.
We will continue the CISO cybersecurity guide with one final part covering arguably the most ominous threat facing organizations today – ransomware. Global Ransomware Damage Costs Predicted To Reach $250 Billion (USD) By 2031
How does SpinOne protect businesses from the plague of ransomware in cloud SaaS environments? We will cover this topic in the final part of the CISO cybersecurity guide.