What to Know About the New SEC Cybersecurity Disclosure Rules
The Securities and Exchange Commission (SEC) announced new additions to rules around disclosing cybersecurity risk management, strategy, governance, and incidents for public companies. If you’re one of the almost 9,000 public companies operating under SEC rules (or preparing to be publicly traded) or an interested investor, you may want to learn these new rules and its impact on the cybersecurity industry. Our cybersecurity expert at Spin.AI, Will Tran, summarizes what these changes mean and how to prepare your organization for a new era of disclosure and transparency.
What are the SEC cybersecurity disclosure rules?
On July 26, 2023, the SEC introduced new cybersecurity disclosure rules. These were intended to provide transparency to investors around the cybersecurity risks faced by public companies.
SEC Chair Gary Gensler states, “Currently, many public companies provide cybersecurity disclosure to investors. I think companies and investors alike, however, would benefit if this disclosure were made in a more consistent, comparable, and decision-useful way. Through helping to ensure that companies disclose material cybersecurity information, today’s rules will benefit investors, companies, and the markets connecting them.”
The new amendments to these original rules now require disclosure of material cybersecurity incidents. Public companies are now required to disclose a cybersecurity incident within 4 days of determining that the incident is material (material meaning anticipated to have a substantial impact on the company’s finances, operations, or business). (Source)
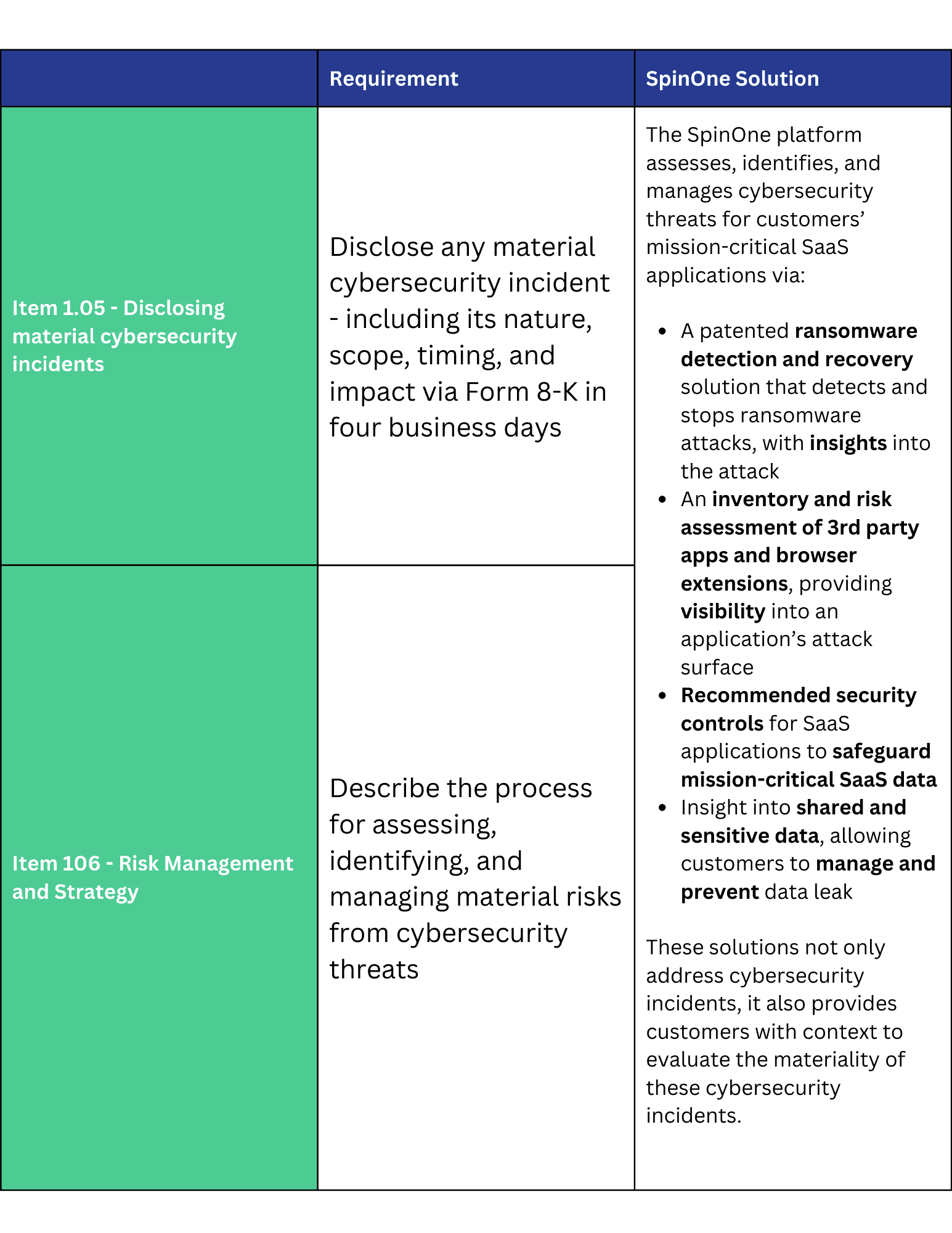
Item 1.05 – Disclosing material cybersecurity incidents
“This requires registrants to disclose on the new Item 1.05 of Form 8-K any cybersecurity incident they determine to be material and to describe the material aspects of the incident’s nature, scope, and timing, as well as its material impact or reasonably likely material impact on the registrant. An Item 1.05 Form 8-K will generally be due four business days after a registrant determines that a cybersecurity incident is material.”
Item 106 – Risk Management and Strategy
“The new rules also add Regulation S-K Item 106, which will require registrants to describe their processes, if any, for assessing, identifying, and managing material risks from cybersecurity threats… [and to] describe the board of directors’ oversight of risks from cybersecurity threats and management’s role and expertise in assessing and managing material risks from cybersecurity threats.”
What does this mean?
Item 1.05 is a step in the right direction for adding structure and transparency around cyber security incidents. However, there is still a gray area when it comes to determining which incident is “material”.
For example, JPMorgan Chase recently reported it defends itself against 45 billion hacking attempts every single day. So how does one determine which attacks are material? When assessing materiality, the company must develop and implement a structure that considers both the qualitative and quantitative consequences of the incident, including the incident’s potential impact to the company’s business operations, customers, and reputation.
Item 106 elevates the importance of cybersecurity within a company by bridging the possible gap between its board of directors and executive leaders with the company’s CISO. According to a Harvard Business Review research, less than half of board members regularly interact with their company’s CISOs; and nearly a third of them only see their CISOs at board presentations. With Item 106 in place, a company’s board of directors and executive leaders are now expected to have oversight into the company’s cybersecurity processes and risks.
Just as important, Item 106 also requires companies to disclose their practices for addressing cybersecurity threats. This forces CISOs to continuously reassess their existing tools and processes to effectively combat the evolving and persistent cybersecurity threats.
When do these rules go into effect?
The new SEC rules were announced in mid-2023 and implemented in late-2023. While these rules have been known for some months, investors have just begun to see how publicly traded companies are reacting to these new rules. Last week, major technology companies – Alphabet (Google), Amazon, Meta, and Microsoft – released their annual earnings report, which complied with the new SEC rules. How did they respond?
Each company complied to the new SEC rules by providing an overview of their cybersecurity-related risk management and strategy. However, some were notably more detailed and transparent than others for the two new SEC rules. For example, in compliance with Item 1.05 – Disclosing material cybersecurity incidents, Microsoft revealed an incident involving a nation-state threat actor who used a password spray attack to compromise a legacy test account and gain unauthorized access to email accounts. For another example, in compliance with Item 106 – Risk Management and Strategy, Meta shared its third-party assessment (TPA) process, which assesses potential cybersecurity risks by collecting security controls from Meta’s major contractors who have privileged data and system access.
How can SpinOne help?
As an all-in-one SaaS security solution, SpinOne helps prevent and manage cybersecurity incidents within mission-critical applications. SpinOne provides complete visibility and context of cybersecurity incidents related to ransomware, data leak, and data loss to help customers evaluate the materiality of these incidents.
The most notable element of the new SEC rules is the shift in culture around cybersecurity. Placing a spotlight on the importance of cybersecurity shifts companies into an essential mindset that is both aware of potential threats and urgently prioritizes a holistic cybersecurity strategy. Learn more here about how SpinOne can help.