Improve visibility into and control over all browser extensions and applications connected to your Google Workspace™
Organizations worldwide are rapidly transitioning to the cloud and SaaS applications, allowing users to access critical apps from anywhere, using only a browser or mobile apps. However, recent analysis shows up to 75% of SaaS applications pose a high or medium risk to business-critical data stored in Google Workspace™ and Microsoft 365. To help companies improve their SaaS security posture, Google has recently integrated Spin.AI and CRXcavator into the Google Workspace™ Admin console, allowing Google admins to see the risk scores for integrated SaaS extensions.
New Google integration improves SaaS security
Bad actors have created fake extensions that look legitimate but are designed to steal or damage user data or install malware on the user’s computer. Additionally, even legitimate extensions can sometimes have security vulnerabilities that hackers could exploit.
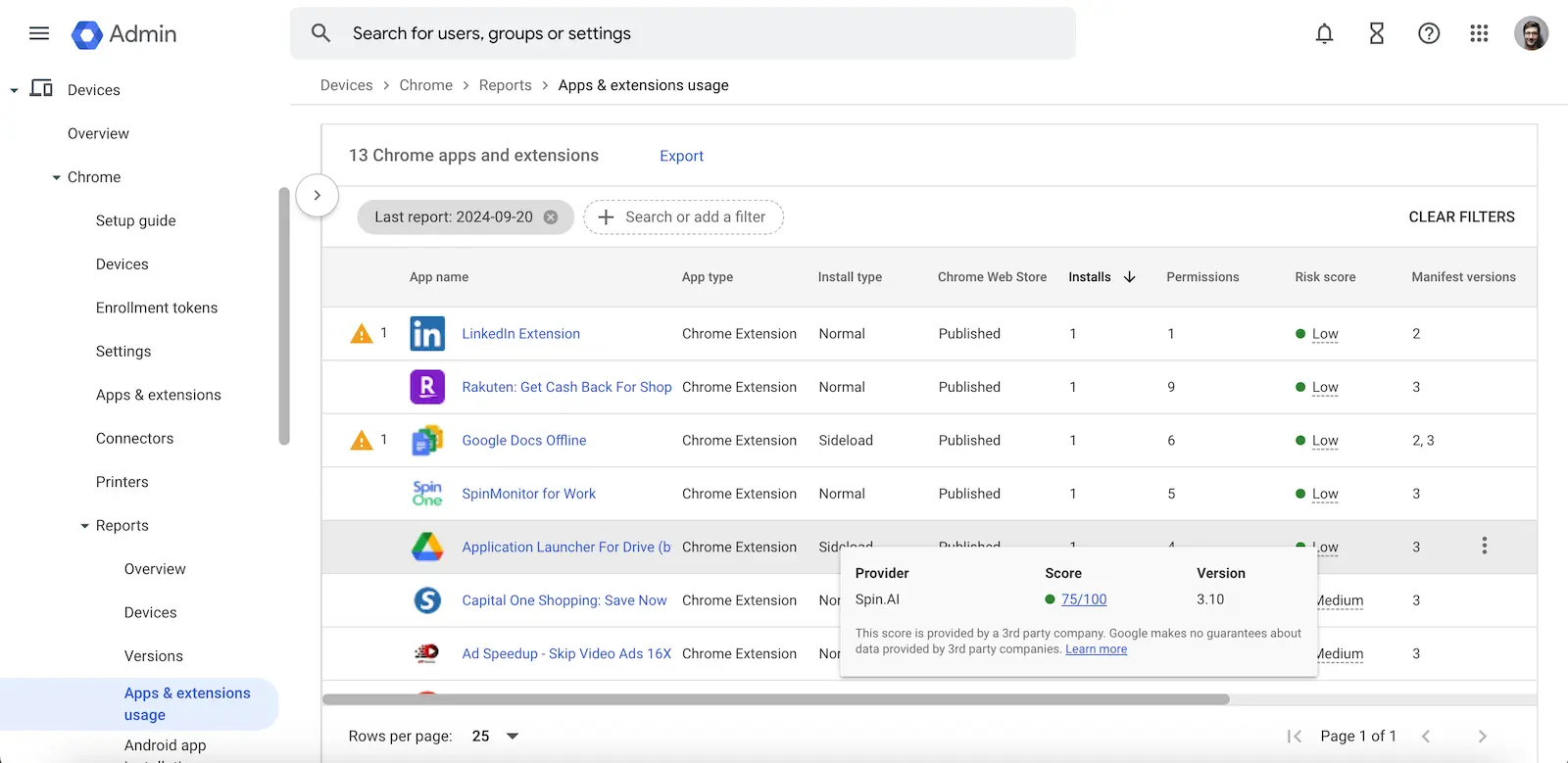
To help organizations deal with the increased risk of extensions, Google has recently integrated Spin.AI and CRXcavator, two solutions providing extension risk assessments.
It gives Google admins the tools to perform risk assessments of detected extensions. Both Spin.AI and CRXcavator provide visibility into potential risks posed by extensions. However, which risk assessment tool should you use? Let’s evaluate the use cases of each and how you can use them to help improve your security posture.
What is SpinApp Risk Assessment?
SpinApp Risk Assessment is a solution that assesses Security and Compliance risks of Browser Extensions and OAuth Apps (such as SaaS Apps, Cloud Apps, Mobile Apps), allowing admins to take control of SaaS apps and browser extensions in Google Workspace™ and Microsoft 365. In addition, Spin.AI’s integration of App Risk Assessment with Google provides powerful extension management capabilities allowing organizations to have the following capabilities:
- Extension Assessment & reporting
- Source Code Analysis
- Assessment Score and History
- Security and Compliance visibility
It reduces the risk of Shadow IT, significantly reduces the heavy lifting of Security Operations teams to inventory, provides thorough risk assessments, and sheds light on compliance risks with third-party apps. What metrics are used to scan app extensions? Note the following:
- It considers over 15+ characteristics for each detected extension
- Utilizes a unique database of over 550,000+ apps and extensions assessed by AI-algorithms
- Provides an easy-to-view assessment with the ability to drill down on each application’s possible business, security, or compliance risks
- Delivers a detailed and intuitive scoring system (from 0 to 100) for SecOps teams to zero in on the riskiest applications
SpinApp Risk Assessment allows admins to make informed, intelligent decisions based on Spin.AI’s robust machine-learning platform that continuously scans and assesses SaaS app and extension risks in the environment.
SpinApp Risk Assessment primary use cases
The new Spin.AI App Risk Assessment integration with Google Workspace™ Console allows Google admins to benefit from the risk assessment capabilities of Spin.AI. However, rather than delivering basic risk assessment, it enables administrators and SecOps teams to dive deep into an extensions’ security and compliance risks to fully understand the entire picture of risk an organization assumes when using a specific extension.
What is CRXcavator?
CRXcavator is a tool that assesses the risks associated with extensions. It is a handy tool for users and administrators who use extensions, helping determine if an extension is safe. In addition, CRXcavator is free, making it accessible to anyone who wants to ensure they’re using secure extensions.
So, what exactly is CRXcavator? It is a web-based tool that analyzes extensions for potential security risks. When an extension is submitted to CRXcavator, it scans it based on several metrics, including:
- Permissions – What permissions does the extension need
- External communications – What communications does it make to outside resources
- Vulnerability scans – Does the app extension have known vulnerabilities or software components with known vulnerabilities
CRXcavator looks for suspicious capabilities, such as collecting user data or sending it to a third party without the user’s consent. As part of the vulnerability scans, it searches for vulnerabilities in the extension’s code, which hackers could exploit.
Once the scan is complete, CRXcavator provides a report that outlines any potential risks associated with the extension. This report includes a summary of the extension’s behavior and an assessment of the extension’s risk level.
CRXcavator primary use cases
The CRXcavator tool allows administrators to have visibility to risky extensions. It provides basic risk signals to help spot risky extensions. However, its primary strength is its visibility to the extension code.
With CRXcavator, you can view Chrome app extensions’ source code and manifest files. This feature provides a research and analysis tool for developers and data scientists who want to create their own in-house app extensions.
Summary
Google has taken a tremendous step forward in helping organizations with their Chrome extension security by directly integrating Spin.AI and CRXcavator in the Google Admin console. However, which solution works best for you?
SpinApp Risk Assessment
- It primarily focuses on helping organizations have a deep understanding of security and compliance risks with apps and extensions
- It unlocks full visibility into Shadow IT operations in one dashboard
- It saves time for SecOps teams with high level of automation for risk assessment and incident response
- It shows the history of risk changes over time
- It has integration with 3rd-party vendors, such as Splunk, Jira, ServiceNow, DataDog and Slack.
Great tool for automated risk assessment, continuous reassessment, approval process, access management, and fast incident response for a large amount of Chrome Extensions and SaaS Apps within your Google Workspace™ environment.
CRXcavator
- It has a strong focus on development analysis, helping developers to have tools to audit app extension source code and manifest files
- Provides basic risk assessment capabilities
- Risk assessments are primarily based on three metrics: permissions, external communications, and vulnerability scans
- You can see history over time to track risk changes over time
- It’s FREE
Great tool for manual vulnerability research and manual risk assessment for a small amount of chrome extensions in your Google Workspace™ environment.
Speak with a Spin Solution Engineer today to learn how SpinOne helps protect your environment from malicious SaaS apps and extensions, click here to see SpinApp Risk Assessment in action.