Can Antivirus Protect Against Ransomware?
Can antivirus protect against ransomware? The short answer is it depends. In this article, we’ll talk about how antiviruses detect ransomware and their limitations. We also discuss better ways to prevent and protect your cloud against ransomware.
Understanding ransomware
Ransomware is one of the most widespread and successful tools for a cyber attack. It also pays off well. The average ransom payment has reached $812,360 and some attackers demand dozens of millions of US dollars.
In a nutshell, ransomware is a simple software that encrypts the files in an infected IT system. Without a decryption key, it can take months or even years to crack ransomware and decrypt the affected files.
With the popularity of backup solutions, many ransomware attacks began including data theft. Such attacks are called double or triple extortion. Data theft increases the chances of victims paying the ransom. In triple extortion attacks, hackers get their hands on the data of third parties (e.g., employees, clients, or partners of the targetted business). As a result, they demand ransom for this data not only from the company that they stole it from but also from the data owners.
There are several reasons why ransomware is so efficient:
- It’s easy to code and new strains appear every year.
- It’s easy to infect the target’s IT system using multiple techniques, e.g., social engineering.
- Ransomware has grown into a large multimillion-dollar business with separate roles for developers of malware and attackers.
- Double extortion techniques make the consequences of non-payment even worse for the victims.
- Certain ransomware strains can infect the cloud (e.g., Microsoft 365, or Google Workspace™).
Learn interesting and alarming ransomware facts and stats
Can antivirus protect against ransomware?
To understand the answer to this question, we must first discuss how antivirus software works. First, antivirus software is applied only to the desktop solutions. That’s why it’s helpless against ransomware that targets cloud environments.
Second, antivirus can detect ransomware in inserted devices or visited websites. Upon detection, it alerts the user about the danger. However, it’s ultimately the user’s decision to proceed with using the USB device and clicking on dangerous links. Antivirus can’t prevent a person from doing so.
Third, antivirus detection is based on the database of known ransomware strains. Antivirus developers try to keep these databases up to date. However, as mentioned above, ransomware is easy to create and dozens of new strains appear each year. Antiviruses just can’t keep up with all of them.
Finally, antivirus doesn’t stop the spread of a ransomware attack as it has begun. It doesn’t erase the ransomware from the system and doesn’t recover files. The only thing it does is warn the user about the danger. Unfortunately, in many cases, people choose to ignore the warning.
How to protect your cloud environment against ransomware
Businesses that want to protect their cloud data from ransomware infection should follow a number of ransomware prevention tactics. These include:
- employee training,
- regular cloud-to-cloud backup,
- strong password practices
- SaaS application control.
These methods will significantly reduce your chances of getting infected with ransomware and minimize its impact. However, they do not give you a 100% guarantee that your cloud environment will be safe. Humans make mistakes especially when they are under stress due to work-related or personal issues. Social engineering remains the number one attack vector for ransomware. And it is still the most successful one.
That’s why, businesses should acquire ransomware protection that is tailored specifically for the cloud solutions. Tools like SpinOne are the last line of defense against ransomware attacks in the cloud.
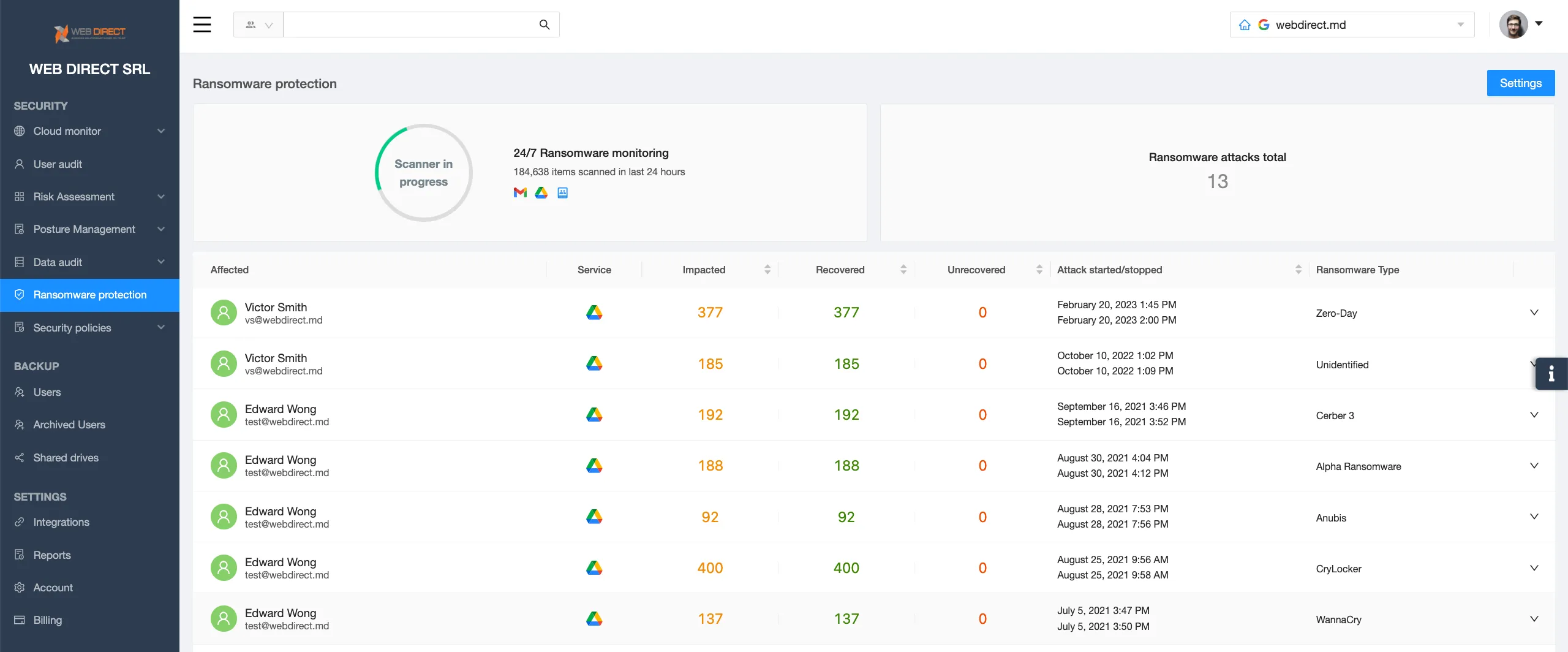
SpinOne’s AI monitors and analyzes data behavior in your cloud office suite 24/7. It learns the normal patterns of data behavior and then, when ransomware strikes, can identify the abnormal ones.
Once the tool has detected the ransomware attack, it searches for the source of this attack, i.e., ransomware disguised as a SaaS app. It then revokes the app’s access to the cloud and recovers all the encrypted files from the backup automatically.
This procedure doesn’t require human interference. In some cases, the IT security team accesses the cloud environment after the ransomware attack has been stopped and the files have been recovered.
SpinOne thereby reduces the downtime from ransomware attacks by 99%. Without this tool, the downtime can take weeks or even months. However, SpinOne does all the necessary jobs just within the hour after the attack.
Try SpinOne Ransomware Detection & Response
FAQs
What protects against ransomware?
To protect your IT system against ransomware, you need ransomware protection tools that were tailored specifically for this goal. Regular antivirus in many cases isn’t efficient.
Which antivirus is best for removing ransomware?
Antiviruses do not remove ransomware. They only warn users about ransomware danger.
Is Windows Defender enough to protect from ransomware?
No.
How is ransomware different from other malware?
Ransomware is different from other malware in several ways:
- It’s easier to develop
- It’s hard to get rid of it.
- It’s extremely hard to recover from ransomware without decryption key.










