Microsoft 365 Ransomware Protection
Fully automated ransomware protection for Exchange Online, OneDrive and Sharepoint. 100% automated. No human involvement required.
Achieve Near-Zero Downtime with SpinOne
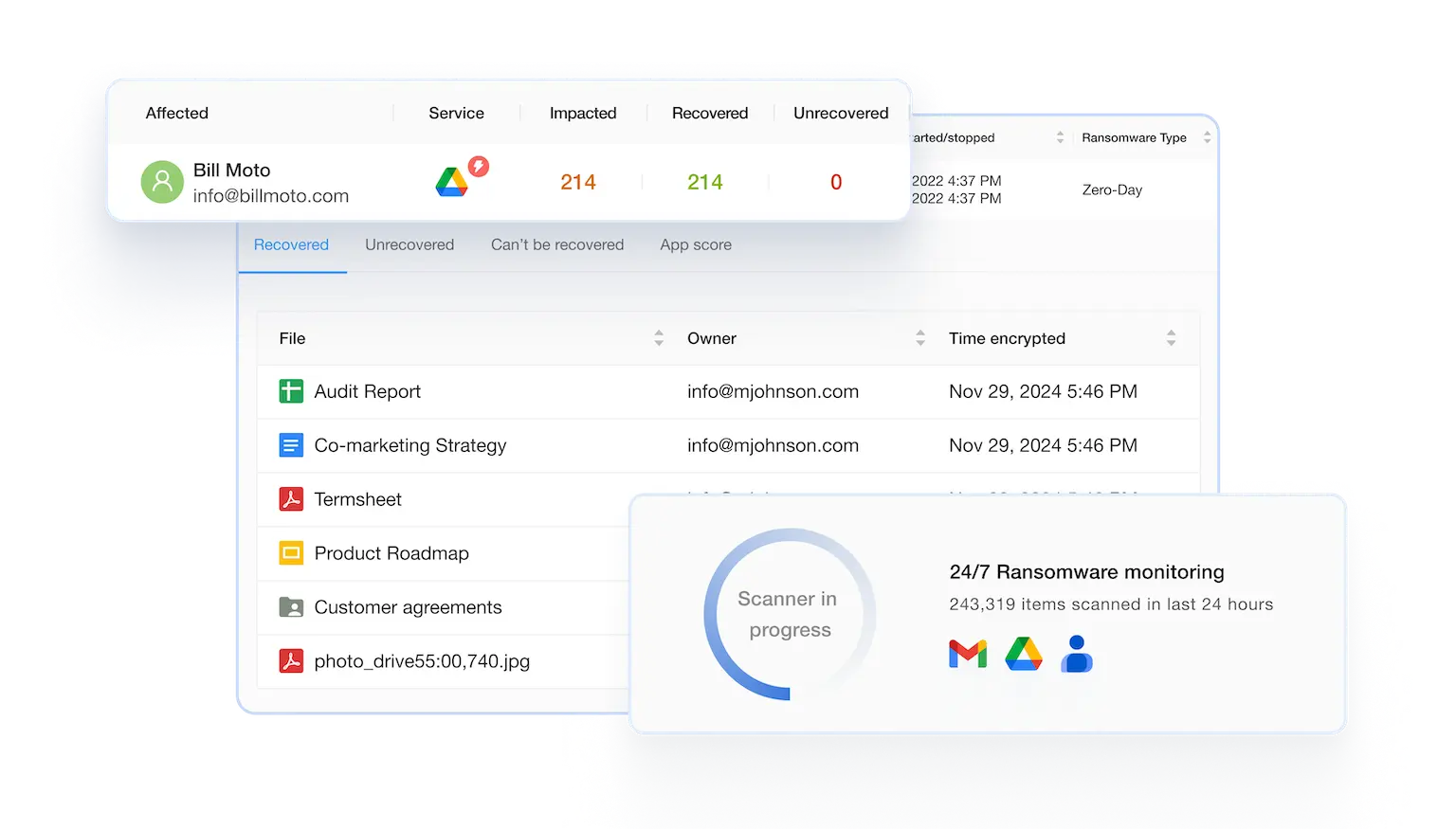
SpinOne helps quickly and safely restore your Microsoft 365 data in the event of a ransomware attack. You’ll get ultimate and instant visibility into the scope of the damage. SpinOne can automatically recover your SaaS data, reducing potential downtime from 21 day to just 2 hours.
Microsoft 365 Ransomware Protection for Business Continuity and Compliance
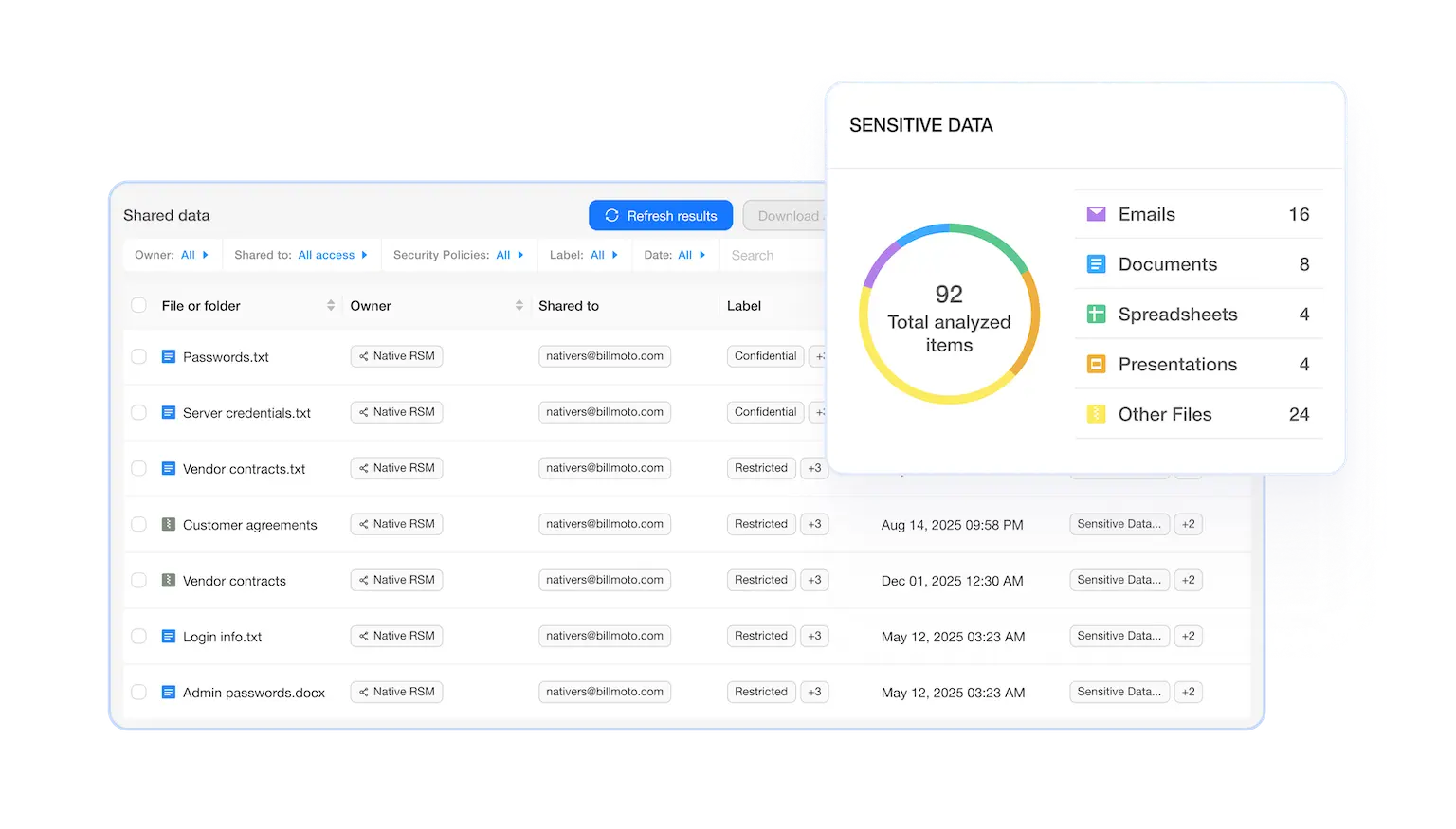
SpinOne can help your company avoid the pain and cost of a cloud ransomware attack. SpinOne provides 24/7 ransomware monitoring and immediately alerts Microsoft 365 admins of any incidents.
SpinOne can automatically identify encrypted files, initiate automated granular recovery of damaged assets without human intervention, ensuring business continuity and protecting you against compliance breaches.
Ransomware Protection
SpinOne is the only solution to integrate pro-active ransomware protection with 24/7 domain monitoring, cloud backup, and flawless restore.
SpinOne combats ransomware, prevents data leak, and can restore your Microsoft 365 data to the most recent version in hours, ensuring that there’s no downtime or data loss.



Book a Demo with Spin.AI
Schedule a 30-minute personalized demo with one of our security engineers.
Award-Winning Solution

3x Recognition by
Global Infosec Awards
- Market Innovator Data Recovery
- Market Leader SaaS/Cloud Security
- Visionary Secure SaaS Backups


From SMBs to Fortune 500s, Here’s Why Businesses Choose SpinOne
Related Resources
Frequently Asked Questions
Learn more from our FAQ section or contact our support team
Why should I backup my SaaS data?
Google Workspace™ applies shared responsibility model for data protection. It prevents data loss due to technical malfunction or attacks. However, Google place responsibility for the human error exclusively on its users.
I am looking for a solution to archive the Gmail™ accounts of former employees and retain their emails. Can you help?
SpinOne have a special offer for archived users. You can safely delete their Google Workspace™ account and store all the data in our storage. Please connect with one of our sales team members for more information and pricing: info@spintech.ai
What is the 3-2-1 rule?
It’s a backup practice recommended by security experts. You should have 3 copies of your data stored on 2 different media one being stored in a remote location.
Is SpinOne safe?
Yes. Our solution takes necessary measures to protect your data, including secure storage on AWS, GCP or Azure, as well as encrypting your data in use, at transit, and at rest.
What types of Microsoft 365 data does SpinOne back up?
All types of files stored on your Google Drive™, emails, contacts & calendar entries, as well as meta data (file hierarchy, email folders, permissions).
How does Spin.AI handle ransomware attacks on SaaS data in Microsoft 365?
Here’s how SpinRDR responds upon detecting ransomware:
- blocks the source of a ransomware attack to immediately stop the spread and reduce the impact of a ransomware attack
- isolates damaged files once a ransomware attack is detected, preventing any further encryption of your SaaS data
- recovers any affected files from the last successfully backed-up version
- sends immediate security alerts while automated protection is taking place
Does SpinRDR identify and patch vulnerabilities in Microsoft 365 configurations to prevent ransomware attacks?
SpinRDR is a ransomware detection and response solution. Its main functionality is to detect ransomware, block its source, isolate the encrypted files, and recover affected files from the last backups.
I fell victim to a ransomware attack. Can Spin.AI assist in the forensic analysis and investigation of the incident?
In addition to detecting, remediating, and recovering from the ransomware attack, SpinOne provides insight into the incident, such as when the attack started/stopped, how the ransomware entered the SaaS environment, and the ransomware type.









