Office 365 Phishing Email: How to Detect and How to Avoid
Hackers know it’s easier to track an organization’s employees than to break through its security systems. Phishing is one of the hacker’s trickeries, often used to infect Office 365 (or other cloud services) with ransomware. In this article, we’ll take a look at the main phishing types and how to protect against Office 365 phishing, ways to detect them, and how to avoid the potential damage they can inflict.
What is Phishing?
Phishing is a cyberattack that utilizes various social engineering methods to trick users into disclosing sensitive information, clicking a malicious link, or downloading a malicious attachment. Office 365 users are often targeted by cybercriminals because corporate data is valuable and criminals try to profit from stealing it. The main tool for phishing authors is email.
Cybercriminals use many approaches to make an Office 365 phishing email look legitimate to trick an end-user. Phishing emails may look like a customer request, message from a co-worker, newsletter, or anything else. As a common practice, hackers use email spoofing or forging an email sender identity.
Hackers constantly continue to come up with more sophisticated social engineering techniques. For example, phishing attacks may be aligned with popular events and news to lurk among normal informational emails on the breaking topic. For example, coronavirus-related phishing.
Types of Office 365 Phishing Attacks
The most common phishing types are:
- Bulk Phishing
- CEO Fraud
- Spear Phishing
- Whaling
- Filter Evasion
- PhishPoint
Each type has a somewhat different execution, but they share a similar goal: to profit from getting a hold of your data.
Bulk Phishing
Bulk phishing is a method of reaching out to as many users as possible. Bulk phishing emails are designed to be understandable and click-bait for everyone in general and no one specifically. With the quantity-over-quality approach, many users will get such emails, yet comparatively few will open them. Besides, a significant part of bulk phishing emails will be detected by native Office 365 spam filters.
CEO Fraud
CEO Fraud is a technique of impersonating C-level executives of a targeted organization. The phishing email looks like an email from the C-level sharing important news with the organization’s employees. However, this is just a fake, aimed at exploiting the trust of employees and stealing the corporate data.
To understand CEO fraud phishing better, imagine the now-common situation. You get an email from your organization’s CEO with a link to a file with anti-coronavirus measures. The purpose of such an email is understandable and everything seems fine. Would you click the link? Someone definitely would click it without hesitation—and become a victim of a phishing attack.
Spear Phishing
Spear phishing is the most advanced, and the most effective, type of phishing. This type of phishing is based on high-quality personalized emails to target specific users. This approach is very effective, making spear phishing behind 91% of cyberattacks and the resulting data breach.
Spear phishing often involves some research about the targeted company, its employees, or its partners. However, the research pays off as the probability of tricking an unsuspecting user is high.
To customize the content of a spear phishing email, attackers usually include the targeted user’s name, phone number, or other personal information that makes an email look legitimate. As an example, let’s take a look at this real-life spear phishing attack.
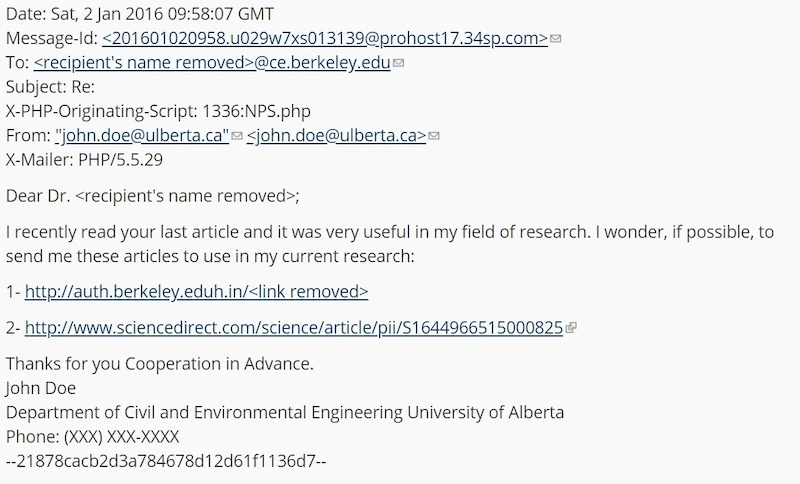
To make this email look legit, an attacker gave a link to a real research paper together with a malicious link. Nevertheless, this attack was detected. And this is how:
- The sender’s address is a misspelled address of a legit organization.
- The subject means reply. However, there was no original message and the conversation was initiated by the sender (hacker).
- The link looks very suspicious.
The spear phishing emails are designed to look as reliable as possible, and hackers often do solid research to disguise a spear phishing email. The spear phishing tactics are adapted to match a specific target. However, one thing is a fact: spear phishing is very dangerous.
Whaling
Whaling, in essence, is a kind of spear phishing aimed at targeting the top-tier users: C-level executives, business owners, investors, and such. Information in the whaling phishing email is more tailored to a high-ranking executive. Generally, whaling is related to financial, legal, or media inquiries. For example, hackers may use subpoena requests, customer complaints, contractor payment bills, and so on.
An unsuspecting senior executive may be lured into disclosing sensitive system information or other data that is valuable due to the position within the company the individual holds. Often, C-level and other executives have system access that lower-level employees do not have. If attackers can phish system-related or other information tied to high-level executives, the level of compromise can often be much greater.
Filter Evasion
Office 365 spam filtering is quite powerful, yet it can not detect 100% of malicious emails. Filter evasion is a set of techniques to avoid being detected by native phishing protection. These include:
- Using images that contain embedded malicious code
- Hiding a phishing link among legitimate links leading to websites of known organizations
- Using URL shorteners
- Creating “noise” by the excessive amount of harmless text that obfuscates the malicious code
Of course, filter evasion techniques do not work all the time, yet often they do help hackers to trick you into reading a phishing email and clicking a link/downloading a file.
PhishPoint
PhishPoint is a special type of Office 365-related phishing. Attackers insert a malicious link into a SharePoint file in an Office 365 trial. After that, the attacker tricks a user by sending an invitation to collaborate on the SharePoint file.
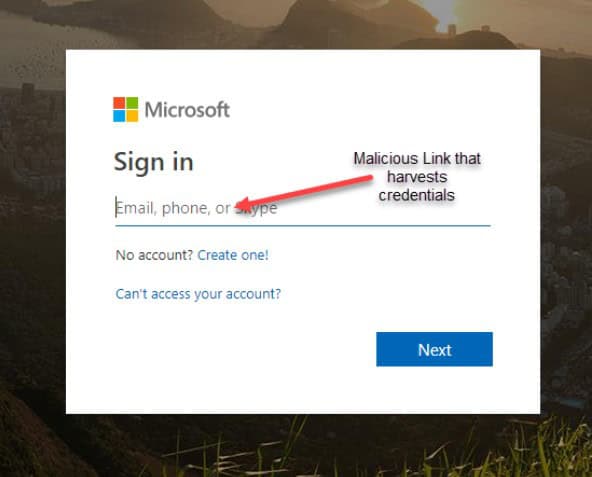
Clicking the corrupted link to the SharePoint file leads to an impersonated copy of a standard access request to a OneDrive file. The request contains a link to a malicious URL. The URL leads to another fake Office 365 login screen that harvests the user’s credentials.
How to Detect a Phishing Email?
There are several red flags that will help you to detect a suspicious email:
- Bad grammar and punctuation
- Misspellings in the organization’s name
- Misspellings in the sender’s email address
- Sense of urgency
- Call to click a link or download an attachment
- Awkward images
Phishing attacks may be more or less sophisticated, though almost all Office 365 phishing emails contain something mentioned above.
How to Avoid Phishing-Related Damage?
Unfortunately, there is no measure that completely prevents Office 365 users from being tricked with sophisticated phishing attacks. The best way is using a multi-layered approach and combining several anti-phishing measures. Some of them are:
- Check each email for the red flags mentioned above
- If an email from your colleague looks suspicious, double-check that the email is indeed from them
- Hover your mouse’s pointer over any link to check where it leads
- Carefully think before clicking any link or downloading a file
- Set up anti-phishing Office 365 policies
- Use backup and anti-ransomware software to reduce the consequences of human error
The last mentioned measure is more important than you may think. Awareness of the phishing threat will greatly decrease the chance of human error, yet it cannot eradicate it completely. Even a trained and aware user may be caught off-guard and fall for a phishing attack.
Only one click from one unsuspecting employee is enough for the whole Office 365 system to be compromised. Having your data backed up and protected by additional anti-ransomware tools is a great way to secure it from a phishing attack’s consequences.
Get Additional Layer of Office 365 Phishing Protection with SpinOne
SpinSecurity for Office 365 helps to protect from ransomware and recover the data from a backup in case of a phishing attack or other emergency. Even if your data was lost or encrypted, it can be restored from a backup, and our ransomware protection functionality prevents ransomware from spreading through the network.
SpinSecurity combines backup features with additional ransomware protection to ensure your data is secure. Features SpinSecurity offers:
- Automated daily backup
- 256-bit AES encryption for data both in-transit and at-rest
- 99.9% accurate data recovery with folder hierarchy preservation
- Multiple backup versions
- Customizable data retention
- Ransomware detection, remediation, and recovery
You can read more about our ransomware protection here. With SpinSecurity, your data is protected and can be easily recovered in case an attack happens. Though, we still recommend that you avoid clicking suspicious links.