The Complete Guide to App Risk Assessment
Most contemporary businesses, from SMBs to large enterprises, rely heavily on SaaS applications. Extensive use of SaaS applications provides users with better flexibility and productivity, yet it is risky. Here are two reasons:
- First, overreliance on SaaS applications expands the attack surface, providing criminals with more potential entry points for cyber attackers.
- Second, the chaotic installation of SaaS applications can lead to various security, operational, and compliance issues that can arise when they are adopted without proper oversight, control, or integration into an organization’s overall IT strategy.
Recent statistics on SaaS application usage prove the above considerations. According to a Cloud Security Alliance survey, malicious apps are the second most common type of SaaS security incidents in 2024, outpassed only by data leakage. At the same time, a surprising 76% of third-party apps with OAuth permissions are classified as high or medium risk. With thousands of SaaS apps connected to Google Workspace™ or Microsoft 365, businesses should constantly assess security risks related to those apps.
Automatized application risk assessment tools help determine risks associated with each third-party application within an organization’s SaaS environment and implement robust security policies to address these risks. Read our guide to application risk assessment to learn what today’s app risk assessments should entail and which automated application risk assessment tool is better to choose.
Security Risks and Vulnerabilities Associated with SaaS Applications
Cloud SaaS environments such as Google Workspace™ and Microsoft 365 allow businesses to scale rapidly without worrying about the complexities involved in running on-premises data centers. SaaS applications play an important role here as they can extend the native functionality of the cloud SaaS environment.
However, despite the tremendous capabilities that SaaS applications offer to organizations, they can be riddled with cybersecurity risks. Some of the main cybersecurity risks associated with SaaS applications include misconfigurations, shadow IT, access management, and insecure APIs.
Misconfigurations in SaaS applications
Misconfigured SaaS applications can lead to substantial security risks, primarily due to incorrect settings and inadequate controls. For instance, improper permission configurations may grant unauthorized users access to sensitive data, increasing the risk of data breaches and insider threats. Additionally, misconfigurations can leave data unprotected or exposed publicly, potentially leading to data leaks. Insecure API settings might provide attackers with vulnerabilities to exploit, manipulate data, or gain unauthorized access.
For example, in 2018, a single security misconfiguration of the JIRA collaboration tool exposed numerous Fortune 500 companies and NASA to sensitive data leaks. This vulnerability stemmed from an authorization error in JIRA’s Global Permissions settings. By default, when filters and dashboards for projects/issues were created in JIRA, their visibility was set to “All users” and “Everyone,” making internal roadmap tasks and other information publicly accessible rather than restricted to internal users.
To avoid such SaaS app misconfigurations, organizations must always check file-sharing configurations in every SaaS to ensure confidential information is not shared publicly.
Poor access controls
The above example also demonstrates the issue of insufficient access controls. When using SaaS applications, organizations face an elevated risk of user account takeovers due to the exposure of these services on the Internet. SaaS platforms typically lack geographic restrictions, allowing brute force and other credential-based attacks to be launched from anywhere. Additionally, attackers may leverage credentials obtained from the dark web to gain unauthorized access.
Insecure Application Programming Interfaces (APIs)
Some SaaS application APIs may lack adequate role-based access control and contain exploitable vulnerabilities. These insecure or absent access controls can lead to unauthorized access to sensitive data. For example, Duolingo, a SaaS-based language learning, had an API-related data breach in 2023. It was reported that data from 2.6 million Duolingo users, including names and email addresses, had been exposed on a hacking forum. The breach occurred because Duolingo’s API for accessing user accounts only required an email address, lacking adequate verification. This vulnerability allowed a hacker with an extensive email database to run a script against the API, collecting user account data whenever a matching email was found in the system.
To address the risk of insecure API should conduct an application risk assessment ito reveal possible API-related vulnerabilities. The risk assessment results may show the need to safeguard the communication endpoints by following best practices, such as implementing robust vulnerability management and restricting API access according to the need-to-know and least privilege principles.
Shadow IT
Shadow IT refers to using systems, devices, applications, and services by employees or departments without the knowledge, explicit approval, or oversight of IT, information security, or legal teams. The rise of SaaS services and applications has significantly contributed to the proliferation of Shadow IT, as 80% of company employees adopt unauthorized apps for their convenience and productivity. Consequently, departments such as legal, procurement, IT, and information security often miss the opportunity to evaluate these tools before they are used. This lack of oversight exposes the organization to significant compliance and security risks, including data breaches, malware threats, and productivity losses. To address these risks, organizations should conduct regular application risk assessments to prevent using unauthorized SaaS tools and close gaps in compliance and security.
Cybercriminals know the immense appeal of SaaS applications. Even better, they know the risks and vulnerabilities vulnerabilities associated with them. For example, when installing SaaS applications, the end-users tend to trust “application permission prompts” by simply choosing “next” through the applications’ permissions requests. Most do not scrutinize permission requests of applications asking for unlimited access to cloud storage or cloud user identities.
Why are application risk assessments critical?
SaaS marketplaces offer hundreds of third-party SaaS applications that can easily integrate with the native cloud SaaS services, adding to the extensibility and flexibility of the cloud. However, this easy access to cloud SaaS applications and third-party integrations opens a pandora’s box of risks for businesses.
With the number of third-party apps installed growing exponentially, security teams are unable to manually track all these apps or quantify the level of risk associated with them. Numerous third-party applications ask for intrusive permissions when linking to a SaaS, allowing them to read, modify, create, and delete content. Such permissions present a significant risk to the company, as malicious actors could take control of these apps and potentially steal, sell, encrypt, or disclose sensitive data.
Malicious cloud SaaS applications or browser plugins masquerade as legitimate or even sanctioned cloud applications to coax users to grant permissions to the application. After the end-user grants permission to a malicious application, it can perform malicious actions on behalf of the user. This process is due to what’s known as OAuth permissions delegation. Third-party risk mitigation is a difficult yet possible task, especially if it starts with an application security risk assessment.
An application risk assessment is a structured process used to identify, evaluate, and mitigate risks associated with a software application, including excessive permissions, misconfiguration, and other vulnerabilities. This process aims to ensure that the application is secure, reliable, and compliant with relevant regulations and standards. With the thousands of cloud SaaS applications and browser plugins available to end-users in cloud SaaS environments, it is essential to conduct application risk assessments regularly.
A Guide to Application Risk Assessment
What steps are included in a proper application risk assessment? Since an application risk assessment aims to identify any risks posed by an application to the organization’s overall cybersecurity posture, it must effectively help prevent and remediate any security risks and vulnerabilities and assess the overall risk of using the application.
Note the following components of a proper app risk assessment:
- applications inventory;
- determining how the app stores, processes, transmits and retains data;
- assessing the application’s reputation;
- assessing the app’s resiliency;
- assessing privacy and security controls in place;
- assessing certifications and security audits;
- evaluating the app’s compliance requirements compliance.
Application Inventory
A good application risk assessment should start with thoroughly discovering all apps used in the environment, who uses them, and what data these apps can access. Without this information, businesses leave themselves open to shadow IT threats, data leaks, and compliance violations. Application inventory helps to uncover the “blind spots” that may lead to sensitive data exposure.
Determining how the app stores, processes, transmits and retains data
A vital part of an application risk assessment is understanding how the app stores, processes, transmits and retains business-critical data. Protecting sensitive data is arguably one of the vital components of a modern cybersecurity strategy. After all, it is the data that attackers target and falls under compliance regulations’ purview.
Like identifying and understanding which apps are used, businesses must understand how applications integrate with critical data, store it, process it, or even share data. This understanding helps provide a complete picture of the application’s security posture and if it aligns with security and compliance requirements.
Assessing the reputation of the application
A good application risk assessment should consider the reputation of the software vendor. The higher the reputation, the more secure and reliable the vendor and its app should be. While assessing the reputation of your application, consider the following questions:
- Is the software application or cloud SaaS app from a reputable software vendor? Or is it produced by a relatively unknown company with little information or transparency?
- What behaviors are exhibited by the application?
- For example, what network connections does it make, and how does it handle your sensitive information?
Not all end-users can answer these questions, but a proper risk assessment should help answer these, and many other questions, to assess the security posture and reputation of the app vendor and application itself.
Assessing the app’s resiliency
A good application risk assessment should help determine how third-party apps handle disasters. Suppose the app is not correctly architected for high availability and resiliency. In that case, relying on the app for core critical functionality can lead to a tremendous risk to your business. Some questions to answer while addressing the app’s resiliency include:
- Can the app withstand an outage of whole cloud regions?
- How does it react to problems in specific availability zones, geographic areas, and other degraded services?
Understanding how the application handles cloud outages, disasters, and other data loss events helps understand the risks associated with using the app in your business.
Assessing the app’s privacy and security controls
Application vendors and cloud application providers should have reasonable security measures to prevent security breaches when using their software applications and cloud services. Application risk assessment should evaluate the necessary privacy and security controls.
For example, a secure and reliable SaaS app must have robust data encryption mechanisms. Ensuring that data is encrypted both in transit and at rest and verifying the strength of encryption algorithms can tell a lot about the application. Access controls are also vital. A good application risk assessment helps review the app’s authentication mechanisms (e.g., multi-factor authentication, single sign-on) and evaluate role-based access controls and the principle of least privilege. Finally, an application risk assessment should examine the app’s privacy policy and ensure the policy aligns with your organization’s privacy standards and regulations.
All in all, assessing the app’s privacy and security controls helps determine how the software vendor can handle cyberattacks on their infrastructure and, by extension, your data.
Assessing the app’s certifications and security audits
Along the same lines, knowing if third-party app vendors can produce proper security audit reports from external audits is essential. For example, secure and reliable applications and vendors generally have ISO 27001 or SOC 2 certification. Compliance with these standards testifies your application vendors protect sensitive data from unauthorized access, security incidents, and other vulnerabilities. Reputable software companies undergo external audits to determine how well the company and software align with cybersecurity and compliance best practices.
Assessing the app’s compliance requirements
As part of the app risk assessment, businesses must understand how the app aligns with their compliance requirements. Checking for compliance with relevant privacy laws and regulations such as HIPAA, GDPR, and CCPA is also necessary when working in specific industries or locations. Remember, a few third-party applications are made HIPAA or GDPR-compliant out of the box. However, most can be appropriately configured to meet regulatory requirements.
Automated SaaS App Risk Assessment
With the hundreds of SaaS applications available in popular cloud SaaS environments, how can organizations effectively identify SaaS apps and perform risk assessments on the numerous apps in SaaS app catalogs? SpinOne provides an automated cybersecurity and risk assessment app for SaaS apps, allowing businesses to leverage the power of artificial intelligence (AI) and machine learning (ML) to determine SaaS application risks effectively without manual efforts.
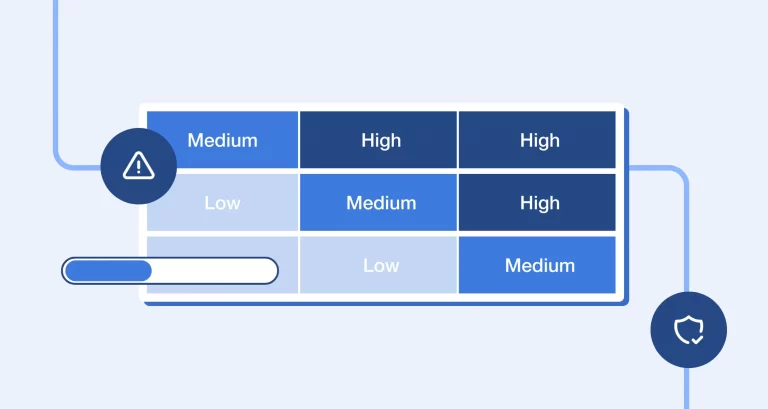
SpinAudit provides an automated assessment of third-party applications’ business, security, and compliance risks. It performs a continuous app risk analysis, user behavior analysis, and application inventory, understands how cloud data is accessed and shared, and implements necessary security policies. Besides this, SpinOne provides:
- application scoring;
- access management;
- security policies;
- zero-day mitigation;
- compliance enforcement;
- a built-in approval process for apps;
- app security visibility;
- alerts and reports.
All in all, SpinAudit allows businesses to leverage the power of automated risk assessment scoring with policy-driven automation to block or enable apps based on their risk score automatically.
If you want to speak with a Spin Solution Engineer to discuss how SpinOne can help you meet your cloud SaaS risk assessment initiatives, click here to book a demo: Request a Demo of SpinOne.