Compliance Guide: SaaS Data Backup & Recovery
Outside of ransomware, there is another word that IT admins and business stakeholders never want to hear – data loss. When it comes to business-impacting events, data loss generally ranks number one. When you consider the damage that ransomware causes, it is the data loss that impacts the business significantly. Data availability is one of the requirements of modern compliance regulations. So, organizations must ensure they have the capabilities in place to recover data in the event it is lost. This requirement extends over to cloud SaaS environments. Businesses are heavily using cloud SaaS, and these have become mission-critical. Let’s see why SaaS data backup for achieving compliance is crucial.
Why SaaS data backup is vital
Businesses are attracted to cloud SaaS environments today as these help to meet the growing pressure for modern services, availability, access flexibility, communication, and collaboration. In addition, since the onset of the global pandemic early in 2020, companies began to accelerate cloud migrations as these were crucial in dealing with the immediate needs of remote workers.
However, as companies migrate business-critical data to cloud SaaS environments, new security and compliance challenges quickly came to light around protecting and securing data. Traditional legacy security and backup solutions are no longer effective in backing up cloud-hosted data. Businesses need cloud-to-cloud backup solutions.
Many organizations also mistakenly assume the data loss and security challenges of on-premises environments no longer apply to their cloud SaaS environment. However, contrary to this mistaken assumption, data loss can and does happen in cloud SaaS environments due to many of the same reasons as on-premises data disasters, including human error, ransomware, and infrastructure failures.
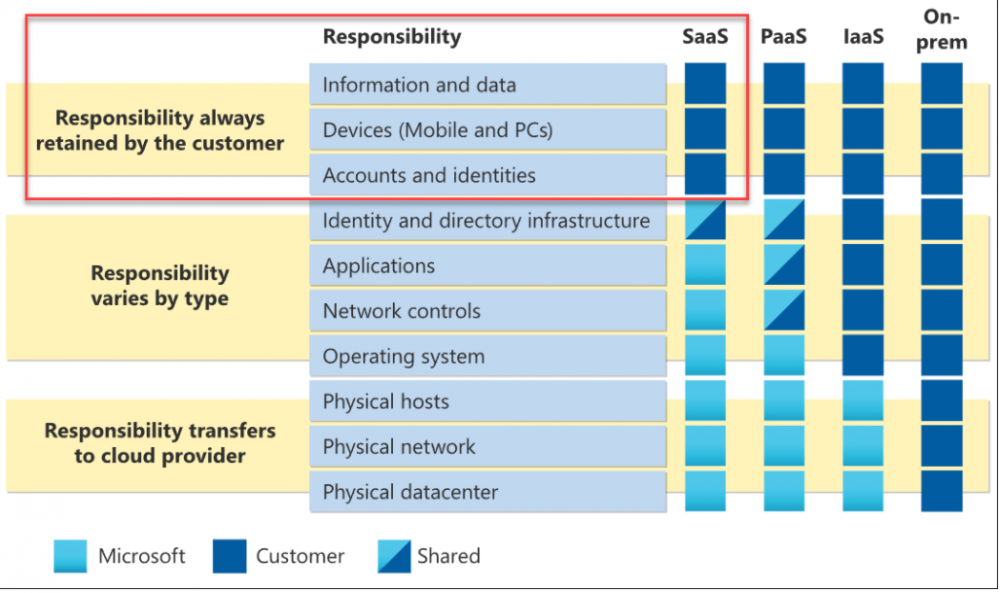
In addition, cloud service providers today, such as Amazon, Google, and Microsoft, all operate under a “shared responsibility model.” It means that the cloud service provider is responsible for certain critical aspects of the cloud infrastructure. However, it also means the customer is also responsible for crucial aspects of their overall data security, availability, and compliance.
As an example of this customer responsibility, note the infographic provided by Microsoft detailing customer responsibilities with SaaS, PaaS, IaaS, and on-premises.
With SaaS services, the customer is responsible for:
- Information and data
- Devices (Mobile and PCs)
- Accounts and identities
Included in the list above is the bulk of the data security, protection, and compliance burden. It means customers are ultimately responsible for any data loss that happens in cloud SaaS environments.
Backing up your cloud SaaS data is essential to ensuring that you can recover from the data loss event if your cloud SaaS environment experiences a data disaster. What are the common causes of data loss in cloud SaaS environments?
Cloud SaaS data loss – why it happens
There are many reasons why data loss can happen in cloud SaaS environments. These include many of the same culprits as experienced on-premises. Let’s consider:
- Human error
- Ransomware
- Infrastructure failure
Human error
Human error is generally the most common reason for data loss, both on-premises and in the cloud. It means that an end-user mistakenly performs an action that leads to data being deleted, updated, modified, or otherwise changed so that information is lost.
Age-old end-user actions such as performing a “Save” instead of a “Save As” or deleting the wrong document from cloud storage can lead to business continuity disruptions. Shared cloud storage resources such as files and folders may be used by groups of tens or even hundreds of users. A single user who deletes the wrong data can cause an outage in business processes and workflows for many users.
When thinking about compliance, particularly dealing with sensitive data, human error accounts for a large percentage of data loss incidents.
Security Magazine online, covering a report from StorageCraft, cited:
“Among survey respondents, 61 percent reported that their company had suffered a data loss over the last two years. More striking is that 67 percent of respondents said human error—everyday mistakes made by employees—was the primary reason for data loss and system outages.”
Accidents do happen with production data. A notable example happened on January 31, 2017 for GitLab. GitLab experienced a major production outage when an employee deleted production data from a primary database server. It led to the service being unavailable for many hours, and ultimately, in unrecoverable data for the company. You can read about the incident and post mortem here.
Another notable example of human error leading to tremendous data loss happened many years ago with the filming of the movie Toy Story 2. An animator working on the project accidentally entered a “delete” command at the wrong level of the folder structure, resulting in over 90% of the production files being deleted.
COVID-19 and remote work leading to more data loss
With millions of employees now working remotely since the beginning of the global pandemic in early 2020, the probability of data loss in business-critical environments has gone up. In addition, employees are no longer located in the secure office environment and may work on less reliable, less secure, and less stable end-user clients and networks.
Working from less secure home environments can lead to more data loss challenges for organizations. The cost of remote work data loss and leak challenges has been captured in the latest IBM Cost of a Data Breach 2021 Report. Remote working and digital transformation due to the COVID-19 pandemic increased the average total cost of a data breach. The report states:
“The average cost was $1.07 million higher in breaches where remote work was a factor in causing the breach, compared to those where remote work was not a factor.”
While the report focuses mainly on data breach statistics, it helps to highlight the increased risks and challenges associated with remote work from a data perspective. Cloud SaaS environments accessed by remote workers incur the same elevated risks for business-critical data as those on-premises.
Ransomware
There is arguably no greater risk or threat to business-critical data than ransomware. Ransomware has evolved and transitioned from a threat to individual PCs to a cybersecurity phenomenon that can shut down major enterprise organizations and disrupt critical services for the masses.
The attack on Colonial Pipeline illustrates the danger posed by ransomware. In May 2021, Colonial Pipeline was hit with ransomware, shutting down critical operations for the company for many days. Colonial is a major supplier of fuel resources to the Eastern Seaboard in the United States. Due to the ransomware attack, Colonial shut down over 5,500 miles of the pipeline supplying the Northeast, causing fuel shortages, price hikes, and other disruptions for weeks after.
When thinking about SaaS backup for achieving compliance and ensuring data is available, ransomware is your worst enemy. Having effective backups of your cloud SaaS data is absolutely required for recovery from ransomware. Without backups, organizations are relegated to either paying the ransom demanded by ransomware gangs or trying to find a decryptor tool if one exists for the specific variant that locked up the data.
As outlined in the Microsoft Digital Defense Report FY21, backups play a key role in the post-breach response, when ransomware is involved.
“Once a ransomware gang locks a victims’ network, exfiltrates data, and holds the network and data for ransom, an incident response team will investigate the root cause of the breach and drive remediation efforts depending on the victim’s level of preparedness prior to the attack. If the victim has sufficient backups of its data or data has not been stolen, often the incident response team will work to remove the threat actor from the victim’s system, restore business operations, and apply future mitigation measures.”
How can ransomware affect cloud SaaS environments?
There are generally two ways this happens:
- File synchronization
- Malicious cloud SaaS applications
File synchronization
Ransomware can attack cloud SaaS data indirectly by means of file synchronization tools like Google Drive™ and OneDrive for Business. An end-user PC is infected with ransomware. Once ransomware begins encrypting files, it triggers synchronization with cloud storage. Any users connected to the shared cloud SaaS storage location will then see good copies of files replaced with ransomware-encrypted files.
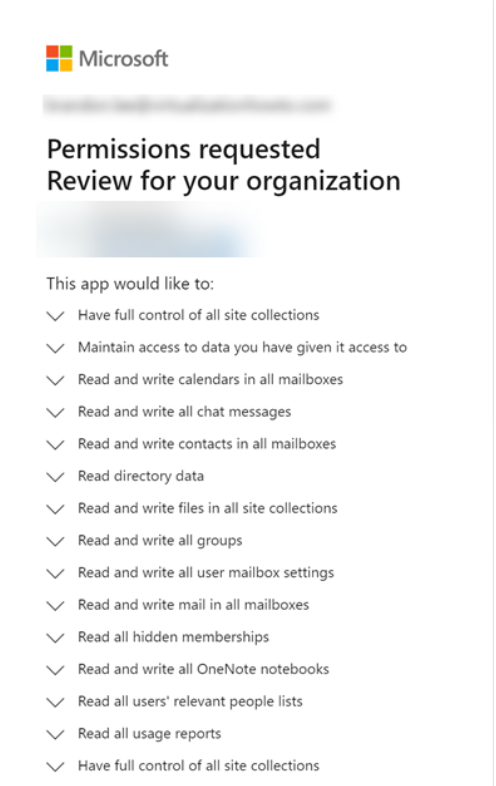
Malicious cloud SaaS applications
Cloud SaaS applications use something called OAuth authorization to gain access to cloud SaaS resources. When a user clicks to allow a permissions request from a cloud application, an OAuth token is granted to the cloud application. This token allows the cloud application to operate on behalf of the user without knowing the user’s password.
Attackers can use the capabilities of OAuth by masquerading a malicious application housing ransomware as a legitimate, safe application. An attacker might prompt the user to install a “security update” to their cloud SaaS application with the proper branding and imagery making it appear from Google or Microsoft. All the while, the application is ransomware in disguise.
Once the user grants the OAuth token to a malicious ransomware application, it has everything it needs to start encrypting data. It can then encrypt any data the user has access to in the cloud SaaS environment, such as their email inbox and cloud SaaS storage. It can also include SharePoint storage in Microsoft 365.
Relying on file versioning is risky
After migrating to cloud SaaS environments, many organizations may reason they can rely on the “file versioning” provided in cloud SaaS file storage as an effective recovery solution for data loss. However, this can be riskly. If you note the fine print very closely with the file versioning provided, neither Google nor Microsoft advertises this as a means of “backup and recovery.” Instead, it is a tool used for light cases of data loss, such as overwriting a file or updating the wrong file.
However, it lacks many features and capabilities of actual enterprise backup solutions. In addition, both Google and Microsoft place limits on file versioning by default. They only keep file versions for a finite number of days. After that, these versions of your data begin rolling off and are deleted. If data loss is not discovered immediately, it is possible only to find the affected data after this period has elapsed, so data is lost permanently.
Proper backups store data “outside” the production environment and not part of a file versioning system that relies on available production infrastructure. As a result, organizations will be in a much better position and have options when restoring data affected by ransomware when they have proper data backups.
Infrastructure failure
Data loss in the cloud can also happen due to infrastructure failures in cloud data centers. But, wait, infrastructure failures in the cloud never happen. Right? Wrong. Cloud service providers have had major infrastructure failures leading to data loss.
In 2019, Amazon AWS suffered a cascading failure in one of their data centers due to a power failure and subsequent generator failure. As a result, over 1 TB of Amazon’s cloud-hosted Elastic Block Store (EBS) disappeared and was not recoverable.
Even if data is not lost, it can often become inaccessible due to cloud service provider outages. Just yesterday, at the time of this writing, Google experienced a network outage that took down major Internet services such as Spotify, Discord, Snap, and Google Cloud. You can read about the root cause of the Google outage here:
It helps to appreciate that organizations hosting their data and services with hyper scale cloud service providers like Amazon, Google, and Microsoft will experience outages and even the possibility of data loss.
Effective SaaS data backup for achieving compliance
As mentioned at the outset, current compliance regulations such as GDPR, HIPAA, and others mandate data is available at all times. Thus, it underscores the need to build highly available and robust data architectures that include effective backups for data protection.
Even when data and services are housed in robust cloud SaaS environments, such as Google Workspace™ and Microsoft 365, businesses must take data backups seriously as part of the shared responsibility model. SpinOne is a powerful SaaS backup and SaaS security solution that secures and protects data using AI-based cybersecurity and automated backups, helping to solve the compliance challenges of data loss resulting from end-user mistakes, ransomware, and cloud outages.
SpinBackup features include
- Automated daily backups
- Diversity in data storage locations
- Restore in time capabilities
- Migration of data between user accounts
- Easy to use admin panel
- Advanced search for items contained in backups
- Encryption of backups at-rest and in-flight
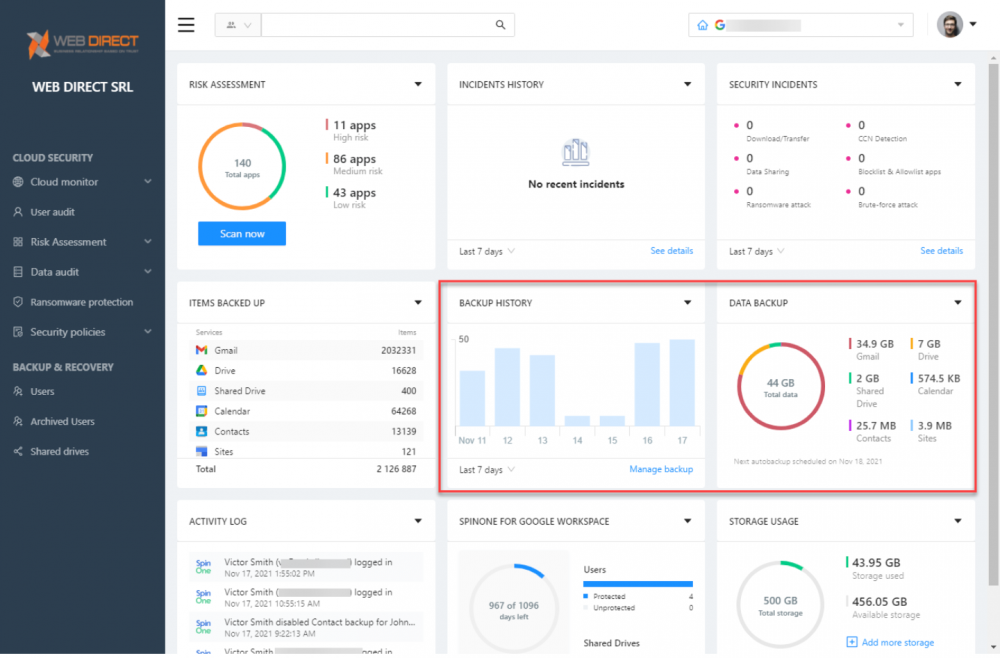
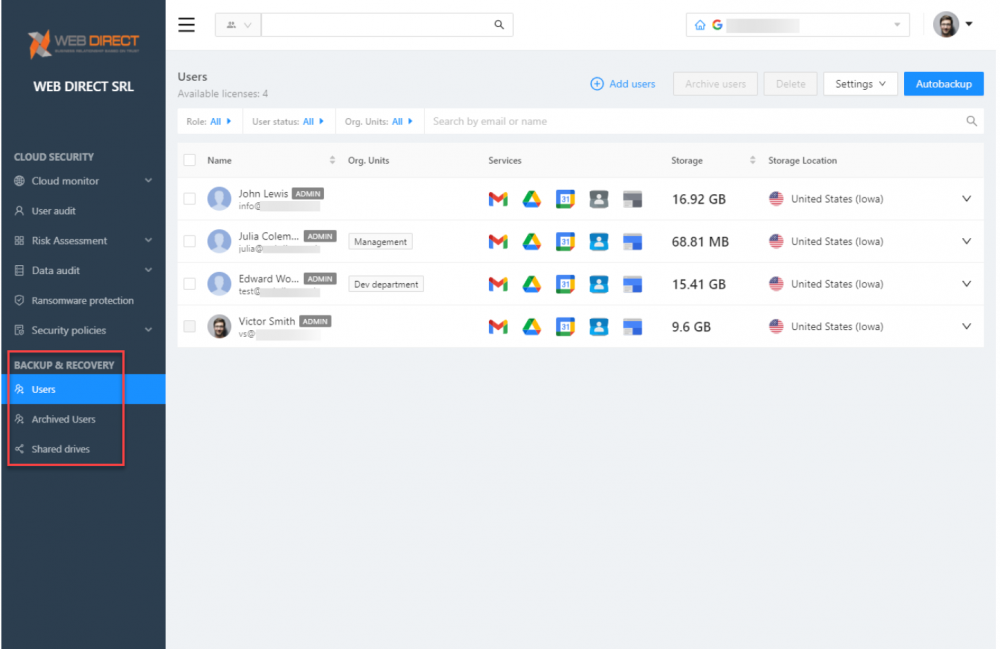
You can view the cloud SaaS user accounts backed up using the solution, services backed up, storage, and storage locations.
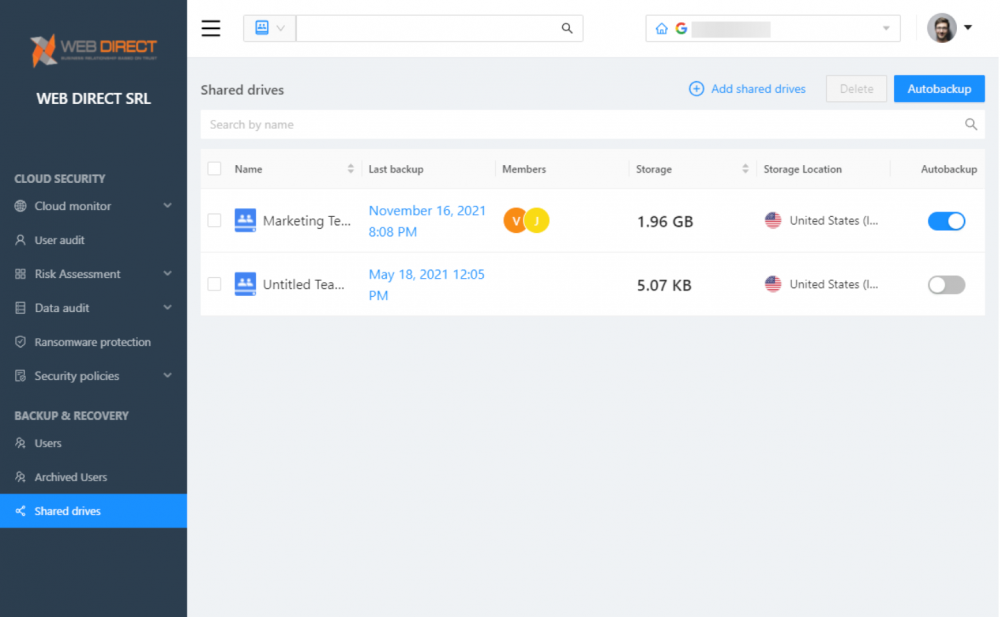
View Shared Drive™ that are backed up using SpinOne.
SpinOne provides a robust SaaS backup solution for meeting the challenges of compliance demands and data availability. It uses effective automation to seamlessly backup data in an automated way and leverages automatic backups to recover your data when needed. SpinOne’s Ransomware Protection module uses the data backups to recover your cloud SaaS environment from a ransoware attack proactively.