How to Avoid Phishing Attacks
In this article we will discuss how to avoid phishing attacks in G Suite and provide phishing prevention best practices on how companies can enhance G Suite security awareness and protection against phishing scams. Cloud security concerns today are some of the most important and challenging problems that businesses have to face.
Hackers looking to steal or compromise valuable information employ many means to accomplish that goal including using malware. However, despite being quite archaic when compared to today’s advanced malware and other tools hackers use, phishing scams continue to be an effective means of stealing information from both individuals as well as organizations today.
The mass scale and the simplicity with which phishing attacks are often carried out, make them extremely difficult for organizations to entirely prevent. What is phishing and what risks are presented by phishing scams? What can organizations today do to minimize the risk presented by phishing or avoid these attacks altogether?
What are Phishing Scams? Tried and true means to steal information
What exactly is “phishing”? Phishing scams are cybercrimes that target unsuspecting end users by electronic communication that fraudulently presents itself as a known, reputable company and persuades individuals to divulge sensitive information including credit card numbers, social security numbers, and other sensitive personal information. Phishing scams come in the largest numbers via email but can be presented to an end user by other electronic means. Among the information commonly targeted by hackers using phishing scams are passwords. As an example, phishing scams posing as legitimate companies such as banking institutions, social media organizations, or online vendors may try to lure a user into disclosing or resetting their password. Unknowingly, the end user has given the hacker access to a potentially privileged account password.
How to Protect Against Phishing
There are several ways that organizations can minimize the risk of phishing scams affecting their end users. As with any security solution, there is never a “silver bullet” that is the end all to all other security mechanisms. The same holds true with protecting against or avoiding the effects of a phishing scam. To be successful, organizations must employ a multi layered approach that involves both the use of technology to prevent these attacks as well as the human factor – end user training. Let’s take a look at the following ways that organizations can help to avoid and prevent phishing.
Technology Solutions
- Have an effective SPAM solution for organization email
- Implement a firewall with UTM capabilities
- Use Antivirus and/or whitelisting software
- Make sure browsers are up to date and have malware options turned on
Human Factor
- End User Training
- Test Employees using “legitimate” phishing
G Suite Phishing Protection Best Practices
As much as technology can be used in a bad way with phishing scams, malware and other means, it can also be used to defend organizations against today’s attacks. As mentioned above, email is the common source of most phishing attacks that organizations receive. SPAM filters are designed to gauge and measure emails flowing into an organization based on known metrics characterizing SPAM and phishing emails. By filtering email through intelligent SPAM filters, organizations can drastically reduce the attack surface presented by phishing emails. Thousands of SPAM or phishing emails may flow through a SPAM solution in a single day. Many of today’s email security providers are very effective in successfully marking emails that fit SPAM or phishing metrics very accurately. Instead of thousands of phishing emails arriving in employee inboxes, that number can be reduced to only a handful.
While firewalls are considered a legacy security measure, today’s firewalls incorporate powerful Unified Threat Management or UTM features that protect against malware and other malicious attacks including phishing scams. Firewalls are a basic but rather effective measure of protecting organization’s internal networks and employees from attacks coming from the Internet. The new power of UTM devices add “layer 7” filtering and intelligence to the mix which means the firewall can scrutinize traffic all the way up to the application layer. This can add tremendous protection to potentially malicious traffic flowing through the wide area network at the application layer.
It goes without saying that organizations must be conscious of the need to protect end user devices from malicious software and threats. Any attacks that do happen to make it through the SPAM filter and edge firewall will next come down to end user devices. Having an effective antivirus solution protecting end user devices is a must. Antivirus solutions are getting more powerful and are incorporating next generation features and intelligence into malware detection and end user device protection.
A growing trend with antivirus solutions are to incorporate “whitelisting” into the protection features. Whitelisting enables organizations to specify which executables or applications are allowed to run. Any other executables or programs are disallowed from running. This is an effective means of ensuring any authorized program that an end user may attempt to run either knowingly or unknowingly will be blocked. It can prove to be very effective in combination with the other security mechanisms mentioned.
Another key mechanism to help avoid phishing scams is to ensure that end user browsers are up to date. Most of today’s browsers have security mechanisms in place in the browser itself to help identify and block phishing as well as malware coming from various sites a user may visit. Chrome for example has a setting turned on by default called “ protect you and your device from dangerous sites”. The other major browsers in use have similar features. The key for organizations is to make sure updates are continuously applied to end user applications such as browsers. Having the latest version will ensure the best protection available from phishing scams and other malicious attacks.
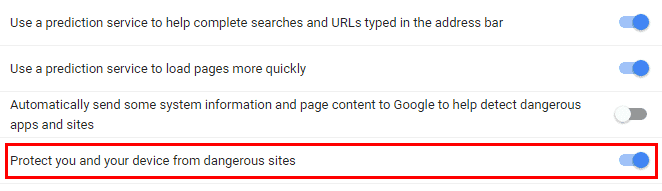
Security Settings found in Google Chrome for protecting against malware and dangerous sites
Check our for G Suite backup practices to find out more about protecting your SaaS data.
The Human Factor in Avoiding Phishing Scams
No amount of technology can replace good common sense when it comes to avoiding phishing scams. Yes, great technology mechanisms put in place can certainly reduce the potential to fall victim to phishing scams. However, no technology can completely eliminate phishing scams that come through email, browser, etc. There will always be a few that make it through the defenses. What happens when these phishing emails make it to an employee?
Employee training on cybersecurity, cyber security awareness, and insider threat control are essential in guarding against phishing scams. Employees must be trained to know what to look for when phishing emails arrive at their inbox. Untrained end users may quickly click an embedded link or send sensitive information that may be requested to what he or she thinks is a legitimate company they or the organization does business with. A few quick items to help end users identify suspicious sources:
- The email address the email came from is a different email domain than the business it claims to represent
- Closely spelled domain names that are misspelled in the from address
- An email that is requesting information that would never be requested in an email from a reputable organization such as credit card numbers or social security numbers
- Emails with suspicious embedded links
- Links to URLs that are not SSL enabled
- Reputable organizations today are utilizing SSL connections to encrypt traffic
- Emails with suspicious attachments
The above are but a few of the classic characteristics of emails that are either delivering malware payloads or are part of a phishing scam.
Organizations do well to implement mandatory training for end users on how to identify and respond to suspicious email threats . Additionally, there are third party solutions that offer online training modules for employees or who can come onsite for training sessions.
Many organizations find it beneficial to perform “legitimate” testing of end users. Either via a “roll your own” site or third-party solution, organizations can send their own phishing emails to employees and see how they respond. This can shed light on problem areas or end users who may need more training.
Takeaways
Cloud security is of utmost concern to organizations today. In fact, organizations not concerned about security will most likely not be around much longer. Hackers are using various means today to compromise information. Included in that effort, phishing scams are still a very productive means of gaining access to sensitive information from individuals and organizations. As with overall information security protocol, organizations have to take a multilayered approach to protecting and avoiding phishing scams. This includes a mix of both technology defenses including SPAM protection, firewalls, antivirus, and software updates as well as bolstering the human factor with end user training and education. Additionally, testing employee responses and behavior using “legitimate” phishing can yield positive results in shedding light on vulnerabilities in employee behaviors and responses.
Check out our Ultimate G Suite Security Guide and stay protected with Spinbackup API-based CASB!