Port of San Diego Ransomware Attack. Protect Cloud Data
Organizations today must protect business-critical systems and data. It is required to maintain business continuity and SLAs. One of the tremendous threats to business-critical data today is ransomware. Ransomware attempts to extort money from businesses and individuals by holding data for ransom.
This malicious attack method has been very successful over the past few years with victims ranging from individual home users all the way up to major corporations. Recently, just a few days ago at the time of this writing, a ransomware attack resulted in the ransom of data at two ship ports – the Port of San Diego and the Port of Barcelona.
Both of these attacks serve as a vivid reminder at just how dangerous ransomware infection can be as well as the need for ensuring your data is safe. With today’s public cloud infrastructure being utilized by more and more organizations, this includes keeping your data safe in the cloud as well.
Let’s take a closer look at the recent attacks and the important considerations these attacks bring to light. We will discuss how organizations can keep their data secure on-premises and in the cloud. Additionally, we will explain how Spinbackup helps protect data in Google G Suite and Microsoft Office 365.
Recent Ransomware Attacks – What We Learn
On Tuesday September 25th, a wave of ransomware infected the Port of San Diego and the administrative computer systems at that location. Just a few days before, the Port of Barcelona in Spain was attacked by similar ransomware to the attack in San Diego.
The ransomware attack did not affect any public transportation. However, it did affect some administrative stations. In order to prevent infection, certain stations were shut down.
As of late, there seems to be a rash of attackers targeting large public transportation organizations with ransomware. The payout for these types of attacks is often very large as there can be much more incentive to pay the ransom fees, especially if services and business-critical data is affected.
This adds to an ever-growing list of organizations that have been the target of such attacks. The City of Atlanta this year was targeted by attackers and has still not paid the ransom as of yet. However, as a result, they certainly risk losing data. Colorado’s Department of Transportation paid some $2 million to retrieve critical data from the holds of ransomware.
These events and attacks are showing that organizations need to check their security, data protection, and business continuity plans. Let’s take a look at best practices across the board for protecting environments from ransomware infections and recovering from ransomware infection.
How Can Businesses Defend and Recover from Ransomware?
The defense against ransomware typically needs to involve a multi-faceted approach that involves a mix of security measures and data protection capabilities. The first line of defense is the security measures put in place to prevent ransomware infection.
The second component is a data protection solution to recover from a ransomware infection if it successfully makes it way through the security measures. Organizations often struggle to protect against ransomware and recover data and services efficiently after an attack.
Security measures are typically architected in layers that involve a multi-layer approach targeting many different aspects of the IT infrastructure. Most organizations today are typically still running perimeter defenses such as firewalls that scrutinize traffic at the point where the WAN meets the LAN.
However, even with the so-called “next-generation” firewalls, malicious traffic can still bypass the best perimeter defenses, especially due to the activities of end users. Antivirus and other anti-malware software are typically installed on workstations and other endpoints to catch any infections that make it to the endpoint.
Catching every single instance of malicious code can be very challenging even for the best malware protection solutions for endpoints. Security mechanisms are important and a key part of overall security strategy. However, they cannot fully protect important business data from threats on their own.
The only means to ensure your data is protected and available is to back it up. While often overlooked, data protection strategies ARE part of the overall security strategy. Organizations must protect their data to ensure it is recoverable.
Since no security measures are perfect, data can sometimes get corrupted by harmful code like ransomware and will require restoration. As mentioned earlier, an interesting problem arises in lieu of the hybrid technology landscape becoming ever more common among businesses today.
More organizations today are utilizing the public cloud for at least some aspect of data storage. The “cloud” has totally changed the way businesses today think about and approach IT infrastructure.
Cloud infrastructure provides definite advantages over strictly on-premises infrastructure. It has allowed organizations today to be much more agile, efficient, diverse, and able to gain access to the latest and greatest technologies much more quickly and in a cost-effective manner.
Ransomware causes problems for organizations in public cloud environments. They need to change their approach to data protection. Traditional tools simply do not work in the public cloud. In the public cloud, there is typically no central firewall filtering traffic.
Additionally, traditional virus scan and other malware utilities do not work for public cloud environments. Often, organizations synchronize files from on-premises environments to public cloud storage via tools such as Google Drive sync or Microsoft’s OneDrive.
This opens a threat vector to data that is stored both on-premises and in the public cloud. If ransomware infects files on-premises, these infected files can be easily synchronized to the cloud. How can organizations effective protect their public cloud environments?
How to Protect Public Cloud Data from Ransomware
The strategy for protecting public cloud data needs to involve many of the same concepts, however, different tooling. Protecting public cloud data should involve both security as well as data protection in the form of backups.
Organizations face challenges in ensuring security and applying policies in the public cloud. This is because traditional security devices like firewalls are not as crucial in that environment. Additionally, they need to align their security measures with their on-premises setups.
Utilizing Cloud Access Security Brokers or CASBs allow organizations to secure their public cloud-housed data and enforce policy across the board.
API based CASBs are the most powerful variant of CASB technology, allowing policies and security to be applied no matter where end point traffic is coming from. There are many additional benefits including performance, native integration with public cloud environments, infinite scaling, and no requirement for endpoints to be reconfigured for use. The API based CASB also allows using powerful technologies such as machine learning to provide intelligence to the security mechanisms utilized for securing public cloud environments.
Using API based CASBs allow organizations to have an effective and powerful means to securing the public cloud environment and business-critical data that it contains. This provides functionality that organizations today must be concerned with such as:
- Protecting against data leak
- Filtering sensitive data
- Preventing unauthorized data downloads
- Profiling user behavior
- Detecting and protecting against ransomware infection
API based CASB technology also helps organizations today to meet compliance and other regulatory concerns such as the GDPR (General Data Protection Regulation), PCI-DSS, and others. API-based CASB technology helps organizations achieve cloud security objectives that would otherwise be difficult using traditional tools and methods.
The second aspect of protecting data in the public cloud from such threats as ransomware is backing up your data. There really is no substitute for backing up business-critical data. While security mechanisms are never 100% accurate at keeping the bad guys out, when backups are performed correctly, they are always 100% able to get your data back to meet RPO SLAs.
How can organizations ensure they perform backups correctly? The best practice methodology when performing backups is the “3-2-1” rule. With the 3-2-1 rule, you need to have at least (3) copies of your data, stored on (2) different forms of media, with at least (1) copy stored offsite. Storing backups this way makes sure that even if some get lost or damaged by malware, you still have copies to use for data recovery.
Spinbackup Provides Security and Data Protection to Public Cloud
Organizations can combine CASB technology and backup technologies to protect data and ensure security in the public cloud. However, they are left with a disjointed, difficult to manage solution that does not allow a single point of management and aggregation point for both security and data protection.
There is a better solution for meeting an organization’s security and data protection needs when placing data in the public cloud. This solution provides enhanced security measures and safeguards for data. It addresses the concerns of organizations regarding the security and protection of their data in the public cloud.
Spinbackup reduced the risks of relying solely on one cloud provider. They offered a robust cybersecurity and data protection solution for Google Workspace and Microsoft 365.
Spinbackup allows organizations to have a unique solution that allows the business to choose which public cloud provider hosts the “backup” data. Spinbackup allows customers to store data either in Google’s GCP Storage or Amazon’s AWS S3 storage.
This gives businesses the opportunity to make use of a public cloud vendor they are already aligned with, or conversely, the opportunity to intentionally diversify where their data lives. For example, a customer might store backups of their data from Google’s G Suite in Amazon’s AWS S3 storage to avoid putting all their “eggs in one basket.”
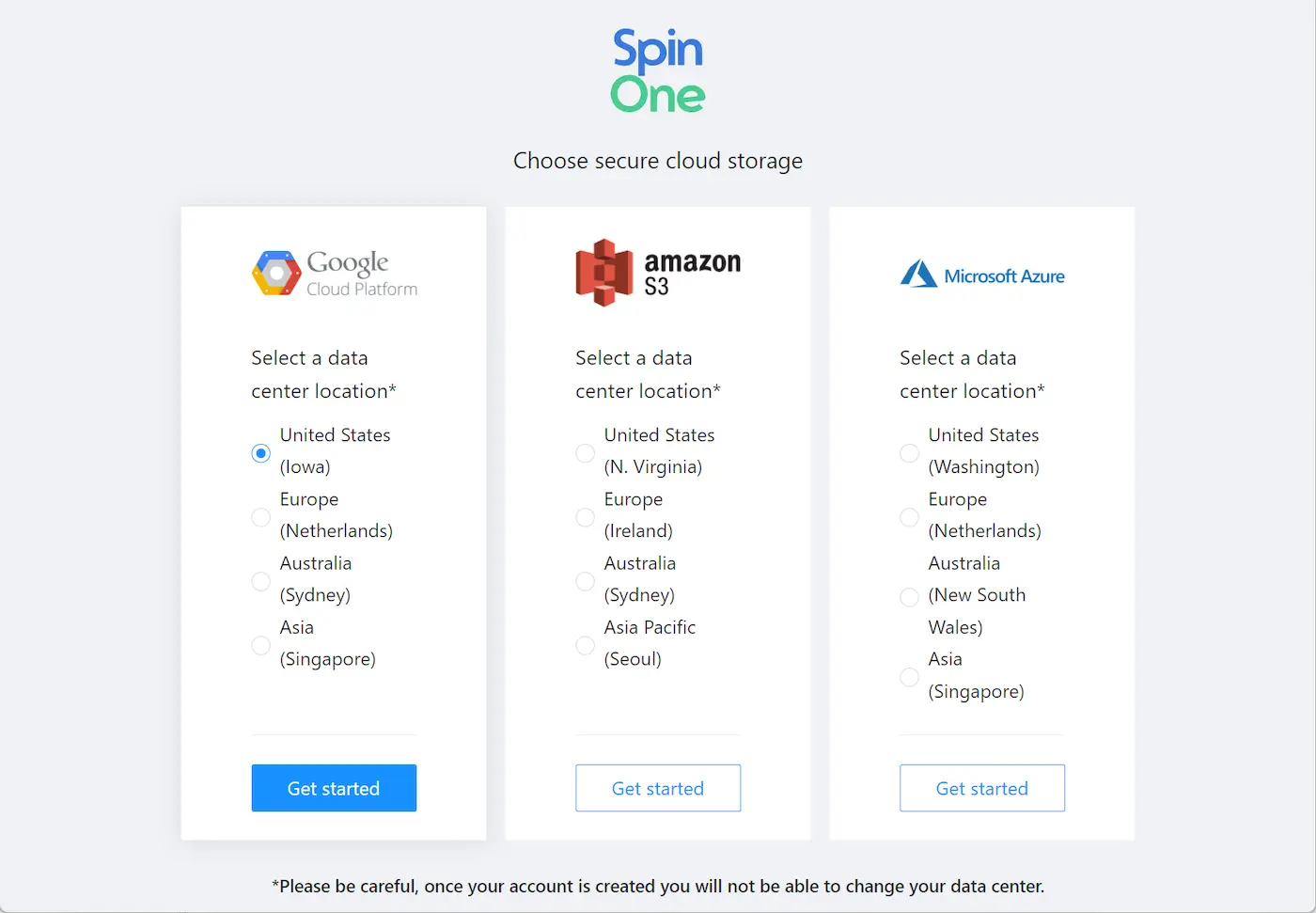
Configuring Spinbackup storage during the initial configuration
This satisfies a critical component of the backup best practice methodology of having backups stored “offsite”. By placing your public cloud backup in a completely different public cloud provider, backup data is protected by diversity.
Spinbackup allows organizations to choose data storage locations and offers powerful features to combat ransomware infections in the public cloud.
- Automated daily backups – 1x to 3x daily
- Effective versioning
- Ransomware Protection and automated remediation
- API based CASB technology that incorporates powerful Machine Learning
- Risky Third-party Apps Control
- Automated alerting
- Domain audit dashboard
Automated daily backups – 1x to 3x daily
Spinbackup provides an automated platform that automatically backs up data in either Google G Suite or Microsoft Office 365. The backup process takes place 1 or 3 times daily, giving organizations multiple restore points each day to revert back to. In addition, the powerful file versioning system included with Spinbackup allows recovering files prior to loss or corruption as a result of ransomware.
Ransomware Protection of Cloud Data
Spinbackup includes a world class mechanism for detecting and remediating ransomware infection. Utilizing the API based CASB Machine Learning, Spinbackup constantly watches your environment 24x7x365 to detect and alert on any process that starts performing encryption on the data in the public cloud. As soon as the infection is detected, the process is blocked, and any files that were affected can be automatically recovered using Spinbackup’s automated recovery mechanism in the cloud Ransomware Protection module.
Risky Third-party Apps Protection
By profiling and noting the behavior of third-party apps that have access to business-critical data, Spinbackup can note if a third-party app performs risky behavior or attempts to do something with data that it shouldn’t do. The third-party app access can be revoked and prevented from accessing the environment. This is crucial protection as end users can unintentionally grant access to data they have permissions to access and potentially compromise business-critical or sensitive data.
Alerting and Reporting
Spinbackup provides automated alerting on security events. When the Ransomware Protection module detects a ransomware infection, Spinbackup alerts administrators of the event. Additionally, other security events and risky behavior coming from end users can trigger alerts so administrators can be proactive instead of reactive when triaging and dealing with security events.
The domain audit dashboard provides a high-level overview of the environment, allowing administrators to “drill down” on events of interest. This type of visibility is key to administrators being able to trend potential security events and other behaviors worth noting. This functionality along with Spinbackup’s automated intelligence gives administrators the advantage needed in today’s complex hybrid cloud environments.
Takeaways
Ransomware is a growing threat to businesses today. The threat of ransomware will only continue to get worse and more sophisticated. Complicating matters is the diverse IT landscape that makes up today’s business-critical infrastructure.
With organizations today moving quickly to the public cloud, they must have a strategy to both secure their data and back that data up to combat the ransomware threat. Using traditional means to secure and backup data in the public cloud is simply not possible.
Organizations can also piece together solutions that may do one or the other and have a disjointed solution that has to be managed from multiple management consoles and logins.
Spinbackup solves the traditional issues that organizations face with backing up public cloud environments by providing a multifaceted solution that allows choosing where backup data is stored, securing the environment with powerful cloud security mechanisms including ransomware protection, and backing data up multiple times a day along with file versioning.
Spinbackup’s solution also allows effectively having visibility to both security and backup telemetry, providing real-time alerts and visibility public cloud environment events. By utilizing Spinbackup’s automated security and backup intelligence, organizations can proactively take charge in the face of ransomware threats.
Was this helpful?
How Can You Maximize SaaS Security Benefits?
Let's get started with a live demo
Latest blog posts
6 Common Mistakes in Google Workspace Backup
Google Workspace is a set of productivity apps, including Gmail, Drive, Docs, Meet, and Calendar...
Backup Microsoft: Securing Critical Business Data Across Microsoft ...
We all know Microsoft is a behemoth with all types of critical products used by...
Microsoft 365 Backup vs. 3rd Party Cloud Backup
As organizations increasingly adopt and become dependent on cloud-based services like Microsoft 365 to run...