Dangerous Browser Extensions Tracker
Dangerous extensions are extensions that have been hacked or broken and represent a significant threat to Enterprise Browser Security.
Understanding Dangerous Extensions in Enterprise Browser Security
The list of extensions below, once widely adopted for their productivity benefits, have increasingly become vectors for cyber attacks. Recognizing the pressing need for businesses to identify and manage these security risks, Spin.AI developed a comprehensive tool designed to list specific extensions that pose potential threats.
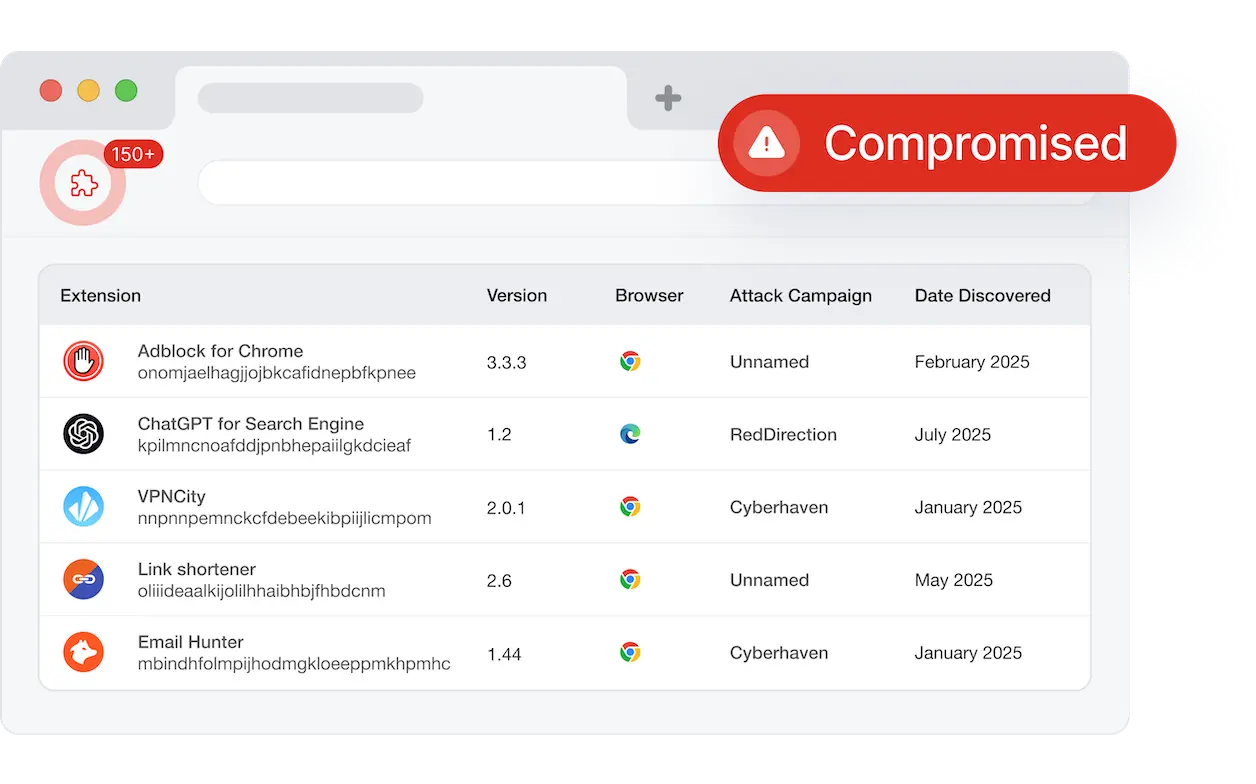
The report below aggregates and displays critical information about dangerous extensions. By providing detailed insights, it allows organizations to take timely action to protect sensitive data and maintain a secure browsing environment.
How to Read Spin.AI’s Dangerous Extensions Report
- Date Discovered: The report shows a record of when each dangerous extension was detected, helping business understand the timeline of potential exposure.
- Attack Campaign: It identifies specific attack campaigns associated with dangerous extensions, offering context on the nature and objective of the threat.
- Browser Compatibility: The report lists affected browsers, ensuring that security measures can be tailored to the specific browsing environments within an organization.
- Extension ID and Name: By providing both the unique ID and the name of each extension, the report facilitates easy identification and management of extensions in use.
- Compromised Versions: Detailing which versions of the extension are at risk, it allows IT teams to assess the necessity of updates or removal more effectively.
Related Articles
The Identity-to-Browser Attack Path: Why Your Security Stack Has a …
You’ve probably been managing identity and browser security as separate responsibilities for years. Not because…
Point-in-Time Compliance Isn’t Enough: Why Browsers Require C…
When organizations run their quarterly browser compliance audits and get a clean report, something important…
The Silent Compliance Risk in Browser Extensions
We’ve analyzed 550,000+ browser extensions across enterprise environments. The pattern we found challenges a core…
Your Browser Just Became Your Best Compliance Sensor
We’ve all spent years building compliance programs around quarterly audits, annual reviews, and point-in-time assessments….